In this post, we will discuss what the “ bootres.dll ” file is in the Windows 10 operating system and where it’s also located. In addition, you will also be guided on how you can replace or fix a corrupt bootres.dll file which may prevent you from booting to your Windows desktop and will display an error message instead saying, “Boot critical file resourcescustombootres.dll is corrupt”. There are times when this error might also boot your PC to the Automatic Repair screen.
DLL files, also known as Dynamic Link Libraries are external parts of applications that run on Windows as well as other operating systems. Almost all applications are not complete in themselves and store code in different files so if there is a need for the code, the related file being called by a certain application is loaded into memory and used. If the software or the operating system is unable to find the concerned DLL file or if the DLL file ends up getting corrupted, you will most likely get an error message.
In case you don’t know, the bootres.dll file is a critical system OS file, size 90KB, and can be found in the Windows folder. It is a part of the Boot Resource Library and portrays an important role in making sure that your PC boots properly. So if it ends up getting corrupted, your PC may fail to boot correctly and you’ll get an error message instead. To resolve this problem, here are some suggestions that might help.
If your PC automatically boots to the Automatic Repair screen, you need to click on that option to run the Automatic Repair. If it doesn’t work, you have to boot into the Advanced Startup options to manually access and run the Automatic Repair. Once you’re in the Advanced Options, you will be able to:
- Run Automatic Repair
- Use System Restore
- Start Windows from an external device
- Access Command Prompt
- And use the System Image Recovery to restore Windows from a Factory image.
If the Automatic Repair fails to fix the problem, you may have to use System Restore or the Command Prompt to carry out further troubleshooting steps. Refer to the guide below to use these tools.
Option 1 – Try running the System File Checker in Safe Mode
Running the System File Checker is the safest way to fix DLL file missing or corrupted errors are thrown up by the Windows operating system as it could give you better results.
System File Checker or SFC is a built-in command utility that helps in restoring corrupted files as well as missing files. It replaces bad and corrupted system files with good system files that might be causing the Machine Check Exception BSOD error. To run the SFC command, follow the steps given below.
- Boot your PC into Safe Mode.
- Tap Win + R to launch Run.
- Type in cmd in the field and tap Enter.
- After opening Command Prompt, type in sfc /scannow
The command will start a system scan which will take a few whiles before it finishes. Once it’s done, you could get the following results:
- Windows Resource Protection did not find any integrity violations.
- Windows Resource Protection found corrupt files and successfully repaired them.
- Windows Resource Protection found corrupt files but was unable to fix some of them.
Option 2 – Try running the DISM tool to repair the System Image
To repair the System Image, you need to use the DISM or Deployment Imaging and Servicing Management tool. The DISM tool is another command-line tool in the Windows operating system that could help users fix various corrupted system files. To use it, follow these steps:
- Open the Command Prompt as admin.
- Then type in this command: Dism /Online /Cleanup-Image /RestoreHealth
- Do not close the window if the process takes a while as it will probably take a few minutes to finish.
Note: The command you executed will check for Windows component store corruption and will restore its good health. The scan might take up to 15 minutes. Once it is done, you have to restart your computer.
Option 3 – Try to repair the MBR and rebuild BCD
To repair the MBR and rebuild BCD, follow these steps:
The problem might boil down to the Master Boot Records since the previous case has already been isolated. There are times when the Master Boot Records can get corrupted and even though it is a serious issue, it can still be rectified by repairing the Master Boot Record.
- Tao the F8 key while booting the system to go into the Windows Recovery Menu.
- Next, click on Troubleshoot.
- Then click on the Advanced options to get into the Automatic Repair menu.
- After that, you have to use the bootrex.exe tool, so click on the command prompt and type in the following commands, one after the other:
- bootrec /RebuildBcd
- bootrec /fixMbr
- bootrec /fixboot
- Exit and then go ahead and restart your PC.
Option 4 – Try running the ChkDsk utility
One of the best options you must try is running chkdsk as it will check the disk for any errors and repair them automatically. To use it, follow these steps:
- Boot your PC to the Advanced Options menu and click on Command Prompt.
- Once you’ve opened an elevated Command Prompt, type in the following command and tap Enter to execute it:
chkdsk C: /f /x /r
Note: “C” is the drive root drive so it could be changed if you’re using a different one.
Option 5 – Try resetting your PC
Go to the Advanced Options > Troubleshoot > and select the Reset This PC option from the menu and then select Keep my files.


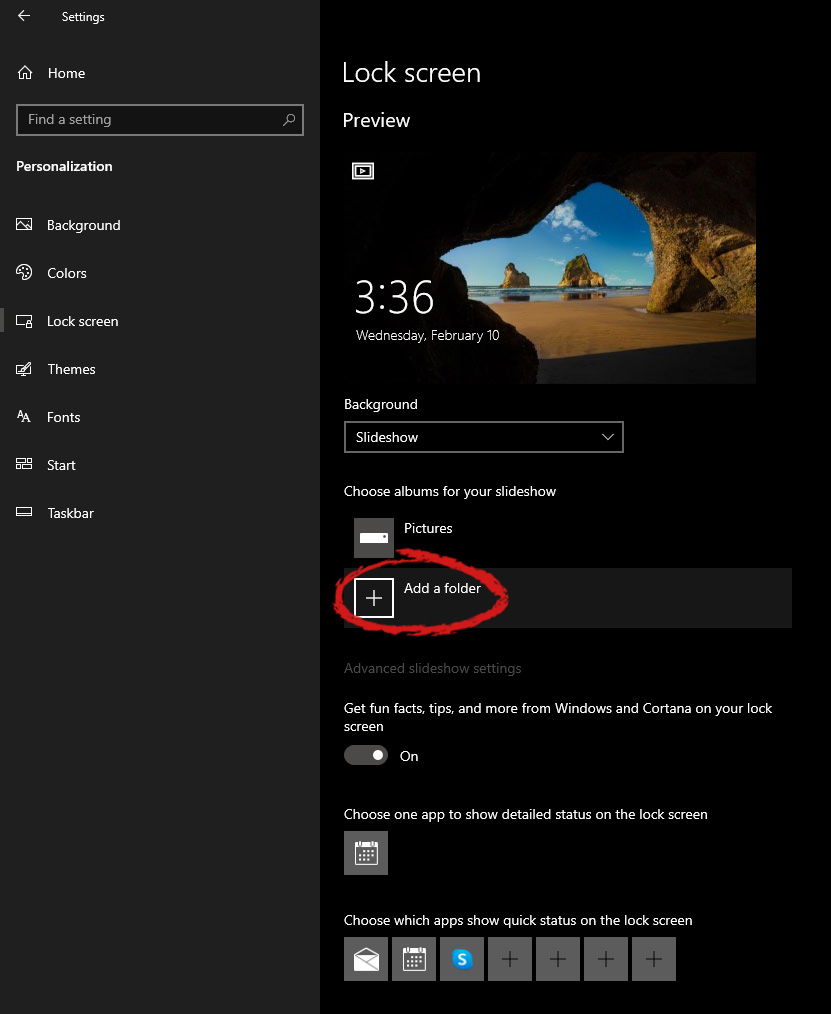
 Inside personalization, click on the Lock Screen tab.
Inside personalization, click on the Lock Screen tab.
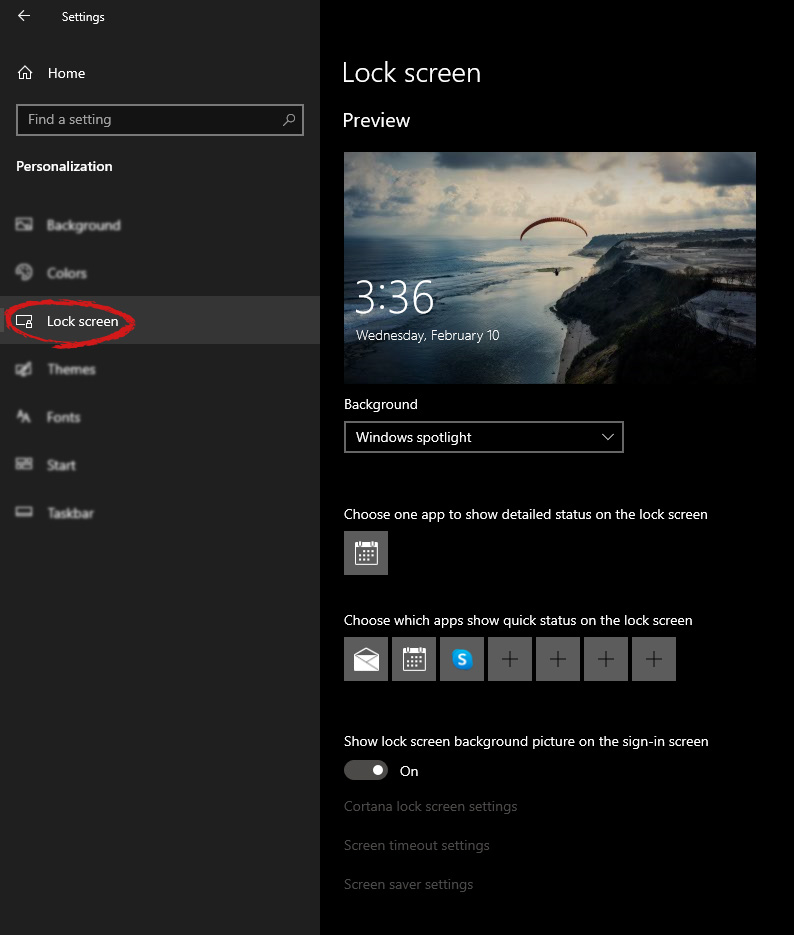 On the right screen, under the picture, you will find Windows spotlight, click on it to bring a drop-down menu up.
On the right screen, under the picture, you will find Windows spotlight, click on it to bring a drop-down menu up.
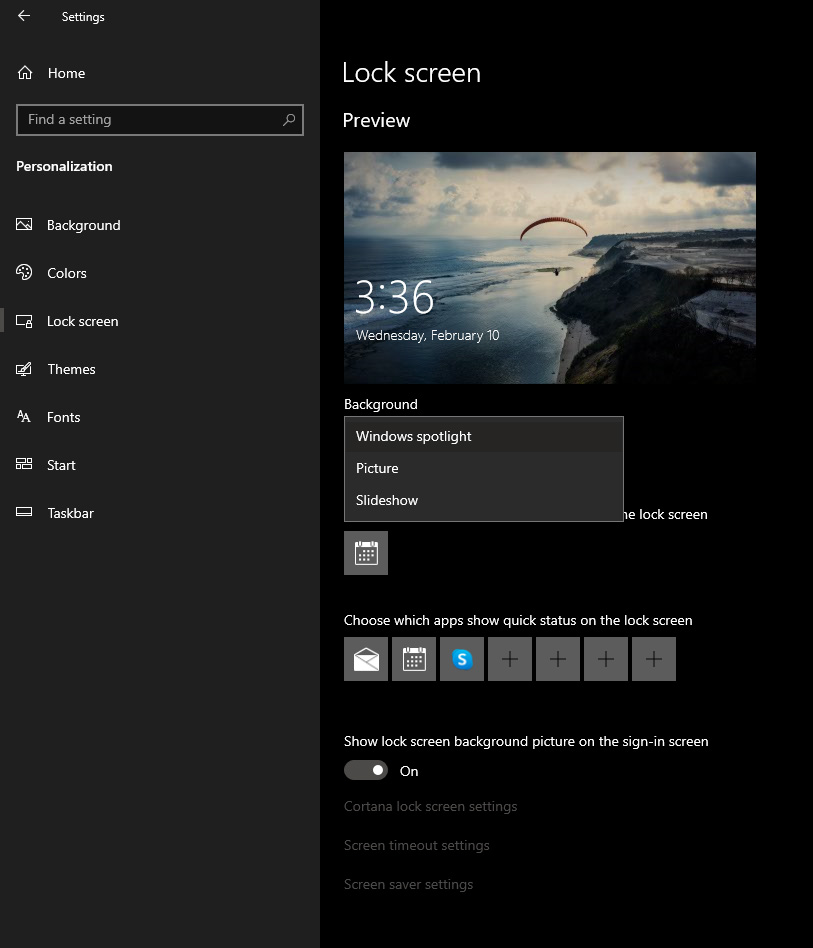 Your choice is presented as a single picture for background or slideshow, a series of pictures that are going to be looped in a given time interval.
If you would like just a single picture for your background, choose that and click on it.
Your choice is presented as a single picture for background or slideshow, a series of pictures that are going to be looped in a given time interval.
If you would like just a single picture for your background, choose that and click on it.
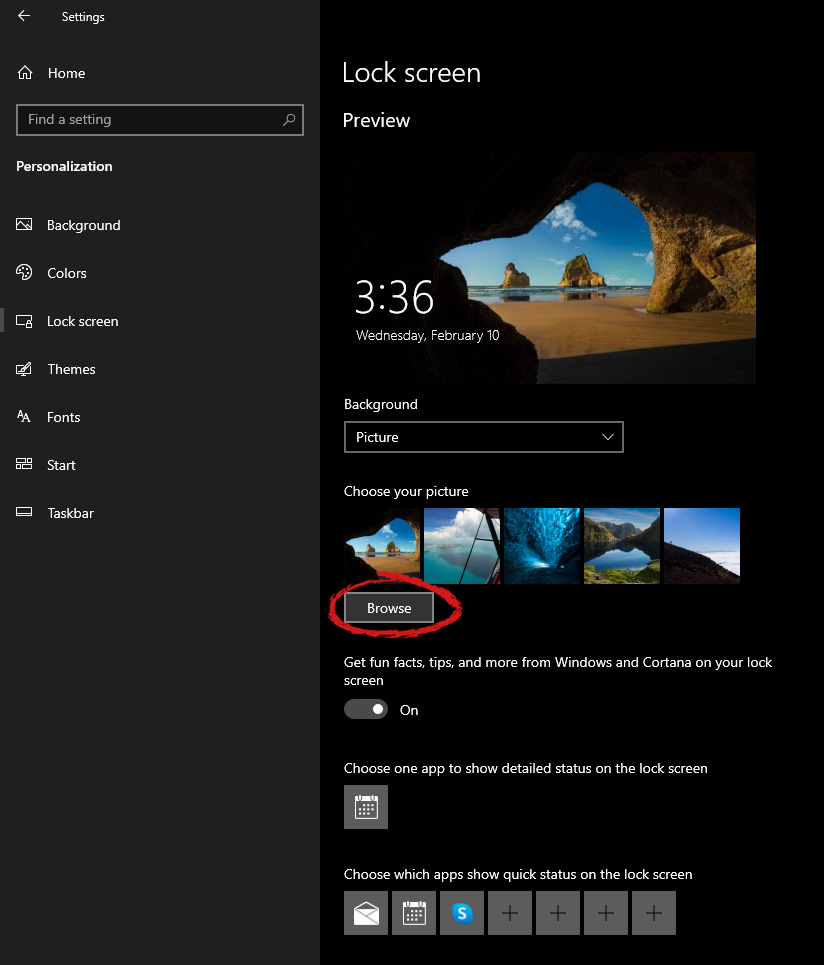 Once you are in choose picture dialog, click on the browse button and navigate to the picture on your storage which you would like to have as a background.
If however, you fancy slideshow as your lock screen background, click on the background drop-down menu and choose the slideshow. Next, click on add a folder and navigate to a folder where you have pictures that you would like to have as a slideshow for your Windows lock screen.
Once you are in choose picture dialog, click on the browse button and navigate to the picture on your storage which you would like to have as a background.
If however, you fancy slideshow as your lock screen background, click on the background drop-down menu and choose the slideshow. Next, click on add a folder and navigate to a folder where you have pictures that you would like to have as a slideshow for your Windows lock screen.

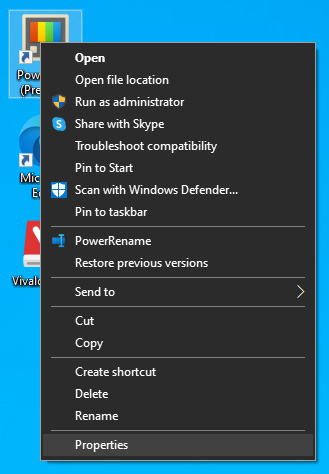 The application settings screen will open, in upper tabs locate Compatibility and left-click on it.
The application settings screen will open, in upper tabs locate Compatibility and left-click on it.
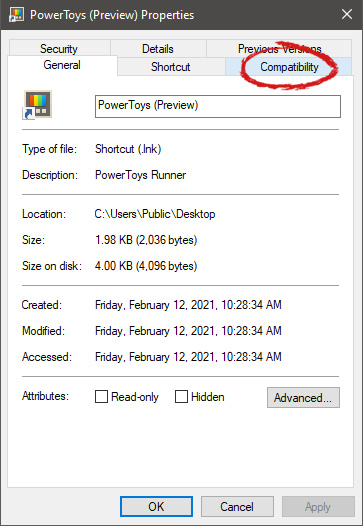 After the click, you will find yourself in application compatibility settings.
After the click, you will find yourself in application compatibility settings.
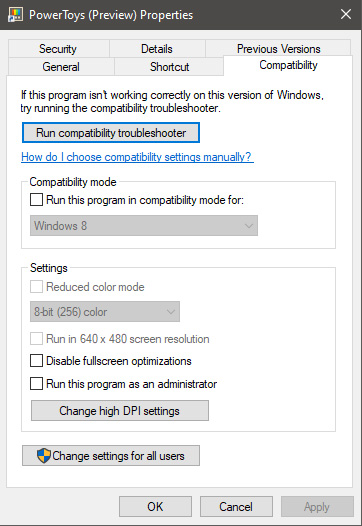 In this window, you will face different options to run the chosen application in various modes in order to make it run. How settings are self-explanatory and different applications will need different settings sadly we can not cover them all but your safest bet is to run them in an environment where they have worked.
For example, if the application was working fine in Windows XP and required administrator privileges, check Run this program as an administrator and Run this program in compatibility mode for Windows XP.
In this window, you will face different options to run the chosen application in various modes in order to make it run. How settings are self-explanatory and different applications will need different settings sadly we can not cover them all but your safest bet is to run them in an environment where they have worked.
For example, if the application was working fine in Windows XP and required administrator privileges, check Run this program as an administrator and Run this program in compatibility mode for Windows XP. 