If you are trying to update your Windows 10 computer but encounter the Windows update error 0x80244019 instead, read on as this post will help provide you some possible fixes to resolve the problem. This kind of Windows Update error is usually caused by your Windows Update settings or the Windows Update components. Many users who encountered this error reported that the update fails with the said error which keeps them from enjoying the latest features that the Windows Update brings.
In such cases, some of the common culprits for this Windows Update error are the Windows Update settings, Windows Update configuration, third-party antivirus programs, and so on. To resolve this error, you can check out the options provided below.
Option 1 – Restart your computer and try installing the Updates again
You can restart your computer and then try installing the updates once again. There are instances when a simple restart resolves Windows Update errors. Aside from that, it would also be better if you make sure that your internet connection is working and that it’s stable. And so after you restart your computer, check for updates once again and see if you’re still getting the error or not.
Option 2 – Try to change the Windows Update settings
You might also want to try tweaking the Windows Update settings. This will prevent other Microsoft products from being updated and besides, you can always turn the option back on afterward. To change Windows Update settings, follow these steps:
- Tap the Win + I keys to open Settings.
- Next, go to Updates and Security and click on the Advanced Options.
- From there, turn off the “Get me updates for other Microsoft products when I update Windows” option.
Option 3 – Run the Windows Update Troubleshooter
Running the built-in Windows Update troubleshooter is one of the things you can first check out as it is known to automatically resolve any Windows Update errors like error code 0x80244019. To run it, Refer to these steps:
- Tap the Win + I keys to open Settings.
- From there, click Update and Security and go to the Troubleshoot section.
- Next, select Windows Update and click the “Run the troubleshooter” button and wait until it’s finished, and then try to run Windows Update again.
Option 4 – Try to disable the third-party antivirus program
Disabling the antivirus program or any security software installed in your computer is always a good idea you can try when the Windows Update process does not go smoothly. There are times when you encounter Windows Update errors like 0x80244019 due to interference of third party antivirus programs. So before you try updating your computer again, make sure to disable the antivirus or security program and once the Windows Update is done, don’t forget to enable the antivirus program back again.
Option 5 – Try to manually install the Windows Updates
Windows Update Error 0x80244019 might be due to a Windows Update that has failed. So if it is not a feature update and only a cumulative update, you can download the Windows Update and install it manually. But first, you need to find out which update has failed, and to do so, refer to the following steps:
- Go to Settings and from there go to Update and Security > View Update History.
- Next, check which particular update has failed. Note that Updates that have failed to install will be displayed under the Status column which has a label of “Failed”.
- After that, go to the Microsoft Download Center and look for that update using its KB number and once you find it, download and then install it manually.
Note: You can also use the Microsoft Update Catalog, a service from Microsoft that provides a list of software updates that can be distributed over a corporate network. With the help of this service, it can be easier for you to find Microsoft software updates, drivers as well as fixes.
Option 6 – Restart some Windows Update services
The first thing you have to do is to restart Windows Update-related services. Refer to the steps below to do so.
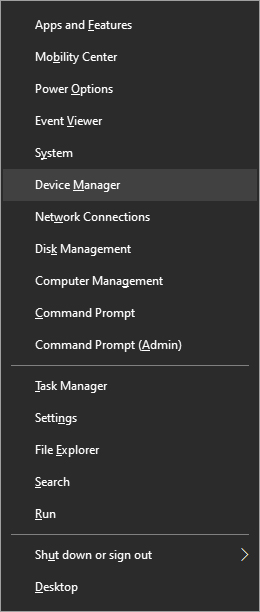
- Open the WinX Menu.
- From there, open Command Prompt as admin.
- Then type in the following command – don’t forget to hit Enter right after typing each one of them.
net stop wuauserv
net stop bits
- After entering these commands, it will stop the Windows Update Service and the Background Intelligent Transfer Service.
- Next, go to the C:/Windows/SoftwareDistribution folder and get rid of all the folders and files thereby tapping the Ctrl + A keys to select them all and then click on Delete. Note that if the files are in use, you won’t be able to delete them.
- Once all the contents in the Software Distribution folder are deleted, restart your PC and then go back to Command Prompt and input the following commands again.
net start wuauserv
net start bits
Since the folder has already been flushed, it will be populated afresh the instant your restart your computer and open Windows Update. Now try to update your computer again and see if the error is fixed or not.
 In Windows 11 by default inside the Start menu, there is recommended section that contains recently opened folders, documents, and files. If you do not wish this section and do not want recent items in your Start menu there is an easy way to turn it off.
In Windows 11 by default inside the Start menu, there is recommended section that contains recently opened folders, documents, and files. If you do not wish this section and do not want recent items in your Start menu there is an easy way to turn it off.
 Intel says that the remedy to the issue for these games is the scroll lock fix which can be done so by enabling Legacy Game Compatibility mode from the BIOS of your motherboard. When running the said games, you can press scroll lock to park the E-cores on Intel's Alder Lake Desktop CPUs to get rid of DRM issues.
Certain motherboard manufacturers such as MSI and Gigabyte have made this even easier through software tools with which you don't have to access the BIOS. All you need to do is select a button in the tool which works on both Windows 11 and Windows 10 operating systems and you will enable compatibility mode.
Intel says that the remedy to the issue for these games is the scroll lock fix which can be done so by enabling Legacy Game Compatibility mode from the BIOS of your motherboard. When running the said games, you can press scroll lock to park the E-cores on Intel's Alder Lake Desktop CPUs to get rid of DRM issues.
Certain motherboard manufacturers such as MSI and Gigabyte have made this even easier through software tools with which you don't have to access the BIOS. All you need to do is select a button in the tool which works on both Windows 11 and Windows 10 operating systems and you will enable compatibility mode. 
 In the menu choose device manager and click on it.
In the menu choose device manager and click on it.
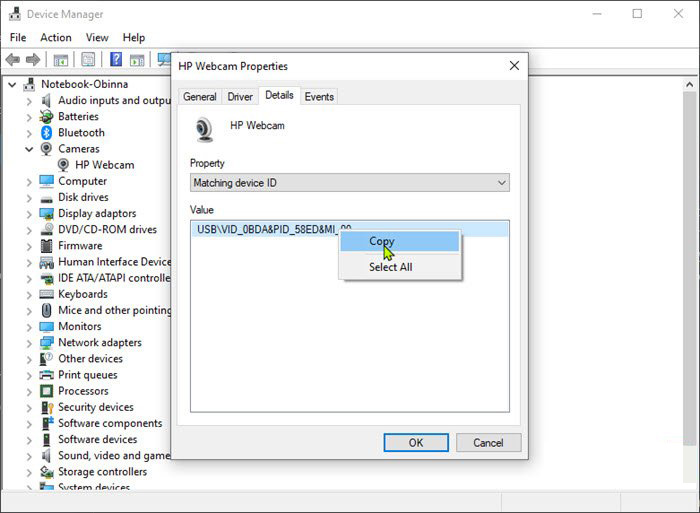
 When the device manager opens, expand the Imaging devices or Cameras section.
Right-click Integrated Camera or the primary webcam, and click Properties.
Go to the Details tab.
Under the Property section, click to select Matching device ID from the drop-down.
Right-click the value and select Copy
When the device manager opens, expand the Imaging devices or Cameras section.
Right-click Integrated Camera or the primary webcam, and click Properties.
Go to the Details tab.
Under the Property section, click to select Matching device ID from the drop-down.
Right-click the value and select Copy
 The next step is to download and install
The next step is to download and install 