Still sitting on the fence about upgrading to Windows 11 because you don’t know what to expect? Interestingly, the new edition somehow manages to be both a total revamp and still very similar to its predecessor in many ways. It’s really something to experience for yourself.
We do want to give you a sneak peek, though. So here’s an overview of the biggest changes Windows 11 brings to the table.
What’s different in Windows 11?
1. Visual changes
The first thing anyone will notice after switching to Windows 11 is the striking visual difference. The entire interface is smoother, cleaner and more minimalistic than on Windows 10, even resembling the macOS in some instances.
Perhaps the most obvious change in appearance is the Start menu and Taskbar location, which is now at the bottom center. It’s actually very neat, but if you’re someone who loves familiarity, don’t worry, you can move it back to the left.
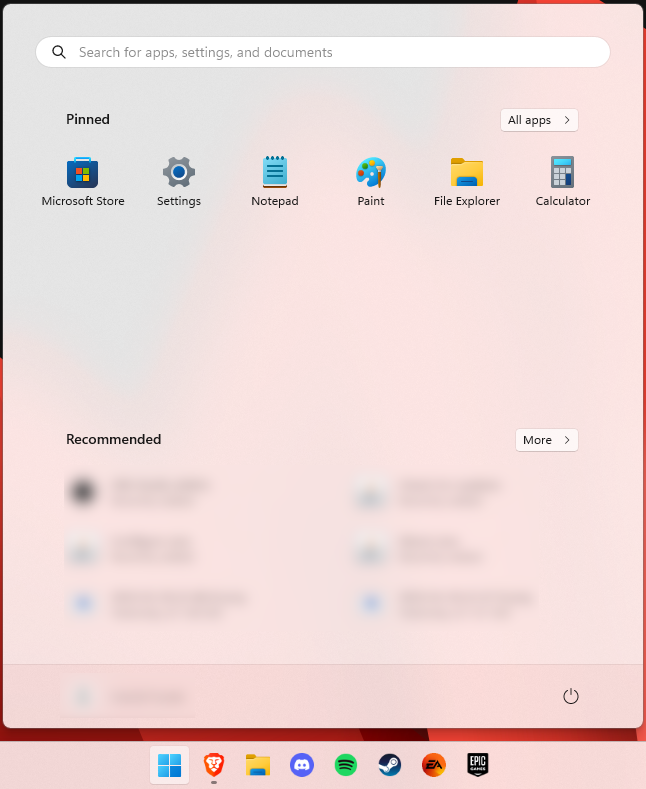
Moreover, you’ll notice that the Taskbar includes a Microsoft Teams icon by default (which you can, of course, remove) and that Live Tiles are gone. The News and Interests section has also been removed - or, shall we say, replaced. As opposed to Windows 10, news, weather forecasts and other information are now displayed as widgets.
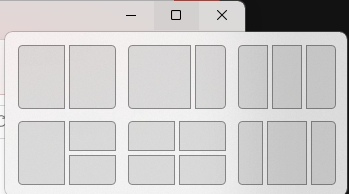
To add to the cleanliness of the UI, Microsoft also enhanced the ‘Snap Layouts’ feature to help you better organize your windows and maximize screen real estate. It’s similar to app grouping on your smartphone. In Windows 10 this feature is slightly restricted, as it requires some manual resizing and dragging. In Windows 11, you can just hover over the minimize/maximize option on a window, select a layout and throw the windows in there.
2. New accessibility features
Microsoft has certainly paid attention to accessibility with Windows 10, but Windows 11 takes this to a whole new level.
One of the ways Windows 11 has taken things up a notch is by adding the long-awaited ‘Live Captions’ feature and advanced Narrator options.
Live Captions apply both to media played on your PC as well as your own speech when you’re using the microphone. Keep in mind that, as with almost all kinds of subtitles, you have to be prepared for a potential delay. However, it’s barely noticeable and doesn’t take away from the usefulness of this awesome new feature whatsoever.
As for the Narrator, there are three new voice packs to choose from. Microsoft has tried to put emphasis on a more natural voice than we are used to. So, now you can choose between Aria, Jenny and Guy, who will read pretty much anything off your screen out loud. Aside from this, Microsoft has also expanded the list of braille displays supported by the Narrator feature.
For users with anxiety or trouble concentrating, a welcomed addition is the Focus app, which is no longer part of the Clock app. It’s now separate and called ‘Focus Sessions’, automatically triggering the Do Not Disturb mode when activated. It blocks all pop-ups and flashes and lets you work in peace until you’re ready to switch it off.
3. Android apps
Android users may rejoice! Windows 11 supports the use of your favorite applications now.
Microsoft has done this by integrating the Amazon Appstore to the Windows 11 Microsoft Store. From there, you can download your favorite Android apps and use them on your PC in a smartphone-like window.
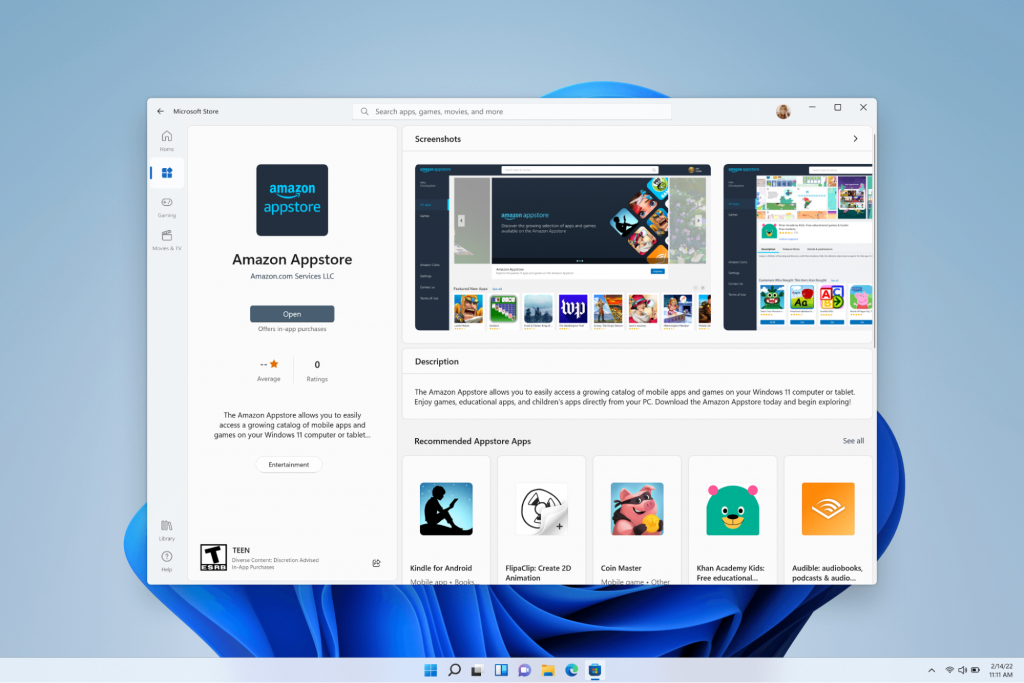
Unfortunately not too many apps are supported at this time, but Microsoft is working on making the emulation possible for many more. Also, the option is only available in specific regions at this moment - check out if you’re one of the lucky ones.
4. Improved gaming performance
Avid gamers will be happy to hear that Microsoft has put some effort into streamlining Windows 11 for their gaming needs.
To give gamers a supreme visual experience, Windows 11 offers the ‘Auto HDR’ feature. As long as your monitor is HDR-compatible, this feature will automatically adjust the colors, brightness and contrast of games without any input from you.
Another update is DirectStorage, which we were introduced to in Windows 10 already. In Windows 11, it’s been improved to tweak loading times and overall gaming performance efficiency even better. The predisposition for it to work optimally is that your device has an NVMe SSD.
The Xbox Game Bar also helps gamers towards a smoother experience. It allows in-game screenshots, viewing processes that are running (similar to the Task Manager), monitoring the CPU and GPU performance and frame rate, integrating the Xbox App and more. There’s also a number of widgets you can now use with the Game Bar, for example the Spotify widget.
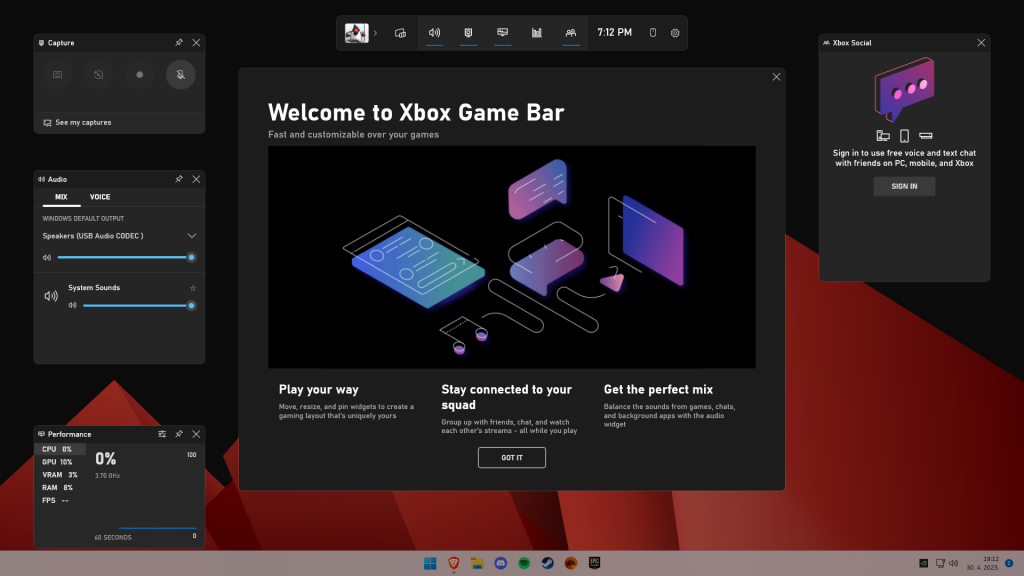
Another cool addition is the Xbox Game Pass, which unlocks hundreds of games to play on your Xbox App, with new additions coming in every month.
5. Smart App Control
Aside from a sleek new look and better accessibility for all users, Windows 11 also comes with a security power-up. Bear in mind that this feature is only available on clean Windows 11 installs.
Smart App Control (SAC) is an AI-powered new feature designed to protect your PC from potential threats. It blocks untrustworthy apps and adware and helps detect potentially unwanted apps, maintaining your PC’s performance and keeping your system safe.
It comes with an ‘Evaluation’ mode, which you should definitely select when running SAC for the first time. That way, the app monitors your usage and assesses whether you’re a candidate for SAC. Some users need it to be on all the time, for others it might be too distracting. Evaluation mode will turn SAC on or off based on your usage.
Don’t disable SAC again unless you’re absolutely sure you don’t need it, since reenabling it will require a fresh install. We recommend you don’t turn it off, as it is a neat feature protecting your data and files from malware at all times.
Summary
Have we piqued your interest in trying Microsoft’s latest OS? It’s a pretty exciting new iteration, but we’ll let you find out for yourself. We hope you like it!
 The first new feature that was slid in is Always on top utility. With this cool utility, you can keep the window as the name suggests, always on top of other windows. To enable this cool feature all you have to do is press the key combination of ⊞ WINDOWS + CTRL + T and an active window will be now always on top of all other windows. To reverse and unlock this window from being always on top just press key combination again.
The first new feature that was slid in is Always on top utility. With this cool utility, you can keep the window as the name suggests, always on top of other windows. To enable this cool feature all you have to do is press the key combination of ⊞ WINDOWS + CTRL + T and an active window will be now always on top of all other windows. To reverse and unlock this window from being always on top just press key combination again.


