If you are using Google Chrome browser in surfing the web, you might have experienced a situation where you’re trying to connect to a website but were unable to since Chrome failed to fetch the website to the browser and throws an error that says, This webpage is not available – Err Connection Timed Out. Aside from an issue with the network connection, there are also other reasons why this error suddenly shows up, read on to fix it.
There are times when the Windows computer is responsible for this kind of issue. And it can happen not just to Google Chrome but to other browsers as well. To resolve this issue, here are some suggestions that might be of help.
Option 1 – Try checking the network cables and then restart your router and reconnect
The first thing you can do is to check if all the network cables are properly connected be it to your computer or to the router. And if your computer is connected via Wi-Fi, you need to restart your router once. And of course, you can always opt to forget the Wi-Fi details and then reconnect again just make sure that you know the password.
Option 2 – Check the Windows Host file
You can also try to cross-check the Windows Hosts file to find out if the website you are trying to open has been blocked because if it is, then it’s no wonder why you’re getting the ERR CONNECTION TIMED OUT error in Chrome. There are instances when some third-party application modifies the file and adds some websites to the blocklists. So if the website is indeed blocked, you need to remove it from the list.
Option 3 – Try removing Proxy
Removing the Proxy might also help you in fixing the ERR CONNECTION TIMED OUT error. Here’s how you can do it:
- Tap the Win + R keys to open the Run dialog box.
- Then type “inetcpl.cpl” in the field and hit Enter to pull up the Internet Properties.
- After that, go to the Connections tab and select the LAN settings.
- From there. Uncheck the “Use a Proxy Server” option for your LAN and then make sure that the “Automatically detect settings” option is checked.
- Now click the OK and the Apply buttons.
- Restart your PC.
Note: If you are using a third-party proxy service, you have to disable it.
Option 4 – Try to clear the browsing data of Google Chrome
If your browsing data in Chrome hasn’t been cleared for some time now then that might be the reason why you’re suddenly getting the ERR CONNECTION TIMED OUT error when you browse the web. To fix this error, you need to clear your web browsing data. Refer to the following steps to do so.
- Tap the Ctrl + Shift + Delete buttons to go to the Clear browsing data section in Chrome.
- Next, set the time range to “All time” and tick all the boxes and then click on the Clear data button.
- After that, restart the Chrome browser and try to open the website you were trying to open earlier.
Option 5 – Flush the DNS and reset TCP/IP
You might also want to flush the DNS and reset TCP/IP as it could help in fixing the ERR CONNECTION TIMED OUT error. To do so, refer to these steps:
- Click the Start button and type in “command prompt” in the field.
- From the search results that appear, right-click on Command Prompt and select the “Run as administrator” option.
- After opening Command Prompt, you have to type each one of the commands listed below. Just make sure that after you type each command, you hit Enter
- ipconfig /release
- ipconfig /all
- ipconfig /flushdns
- ipconfig /renew
- netsh int ip set dns
- netsh winsock reset
After you key in the commands listed above, the DNS cache will be flushed and the Winsock, as well as the TCP/IP, will reset.
- Now restart your computer and open Google Chrome then try opening the website you were trying to open earlier.
Option 6 – Run the built-in Malware Scanner and Cleanup Tool in Chrome
In case you don’t know, there is actually a built-in malware scanner and cleanup tool in Chrome that helps you get rid of any unwanted ads, pop-ups, and even malware, as well as unusual startup pages, toolbars, and other things that could affect the performance of the browser.
Option 7 – Reset Chrome
Resetting Chrome can also help you get rid of the ERR CONNECTION TIMED OUT error. Resetting Chrome means restoring its default settings, disabling all the extensions, add-ons, and themes. Aside from that, the content settings will be reset as well and the cookies, cache, and site data will also be deleted. To reset Chrome, here’s what you have to do:
- Open Google Chrome, then tap the Alt + F keys.
- After that, click on Settings.
- Next, scroll down until you see the Advanced option, once you see it, click on it.
- After clicking the Advanced option, go to the “Restore and clean up the option and click on the “Restore settings to their original defaults” option to reset Google Chrome.
- Now restart Google Chrome.


 From the Device Manager choose the troublesome device and right-click on it, choose properties.
From the Device Manager choose the troublesome device and right-click on it, choose properties.
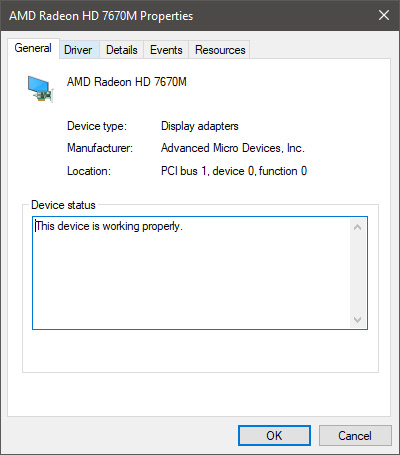
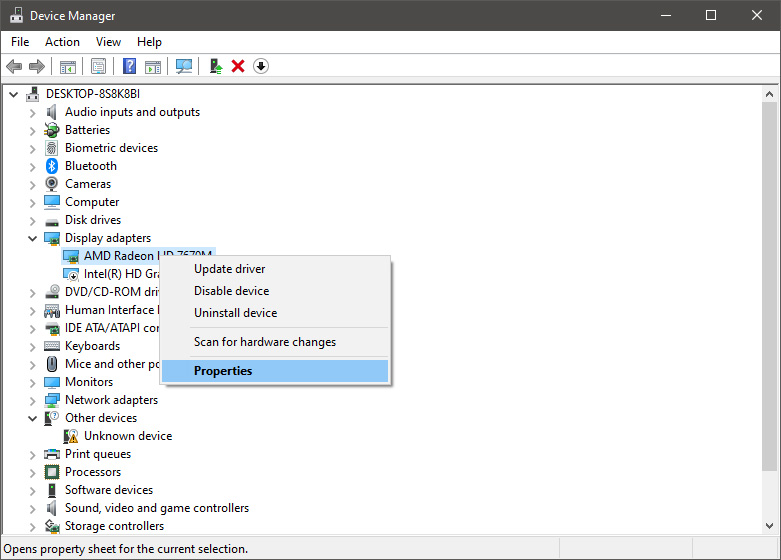 Device properties floating Window will appear.
Device properties floating Window will appear.
 Click on the top tab which says, Driver. From the Driver tab, click on Roll Back Driver.
Click on the top tab which says, Driver. From the Driver tab, click on Roll Back Driver.
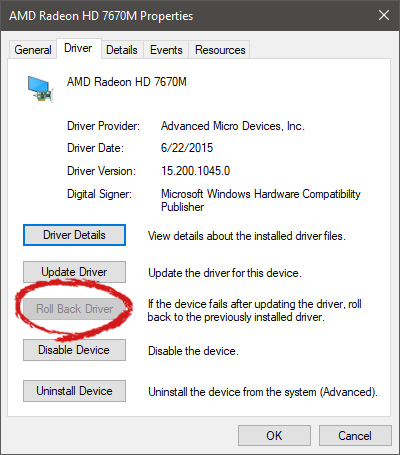 Note that if the device is working properly, the Roll Back Driver button will be greyed out and you will not be able to click on it meaning that chosen device is not the issue. If the device is not working properly and you can click on Roll Back driver, do it, choose the previous version, and reboot your computer.
You can use this method to get back to the previous driver version for any device that is causing issues in your computer.
Note that if the device is working properly, the Roll Back Driver button will be greyed out and you will not be able to click on it meaning that chosen device is not the issue. If the device is not working properly and you can click on Roll Back driver, do it, choose the previous version, and reboot your computer.
You can use this method to get back to the previous driver version for any device that is causing issues in your computer. 
