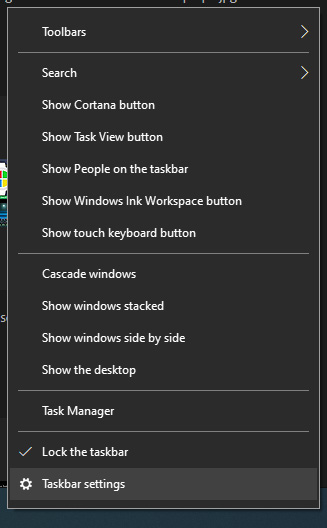
 in the menu, on the bottom choose taskbar settings. Once the settings dialog opens, on the right side locate the taskbar location on screen.
in the menu, on the bottom choose taskbar settings. Once the settings dialog opens, on the right side locate the taskbar location on screen.
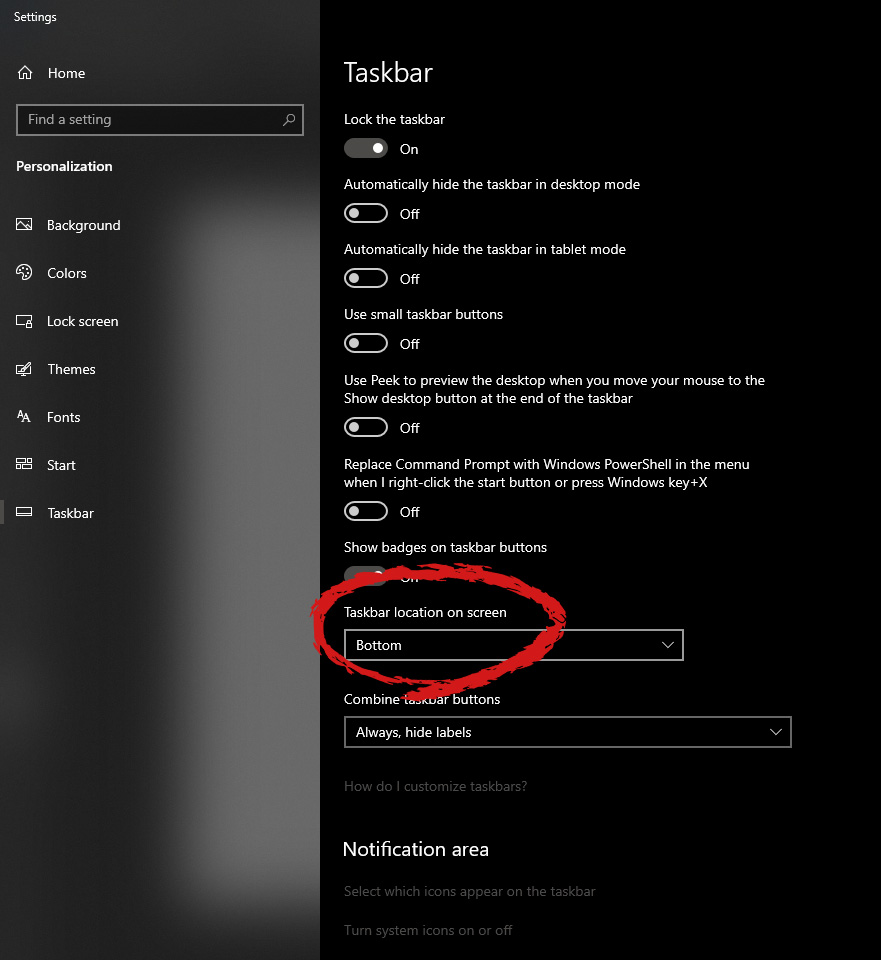 Click on the dropdown menu and choose the desired location for the taskbar.
Click on the dropdown menu and choose the desired location for the taskbar. Each time you connect to a Wi-Fi network your PC saves that network password. If for any reason you need to see this password or passwords there are ways you can do it and we are here to show you how.
 Hello and welcome to error tools where we aim to help you with all of your Windows problems and issues, where we offer our insight on various topics and sometimes go offroad and write something crazy. This time we will offer you a way on how to easily and quickly see how can you find out your memorized Wi-Fi password.
Hello and welcome to error tools where we aim to help you with all of your Windows problems and issues, where we offer our insight on various topics and sometimes go offroad and write something crazy. This time we will offer you a way on how to easily and quickly see how can you find out your memorized Wi-Fi password.

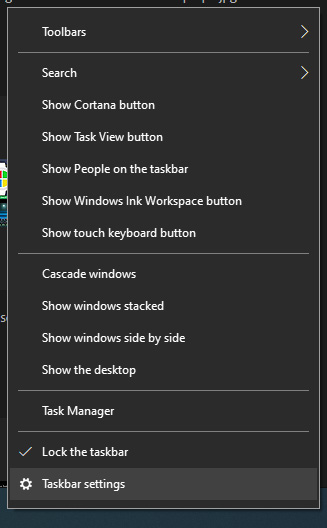 in the menu, on the bottom choose taskbar settings. Once the settings dialog opens, on the right side locate the taskbar location on screen.
in the menu, on the bottom choose taskbar settings. Once the settings dialog opens, on the right side locate the taskbar location on screen.
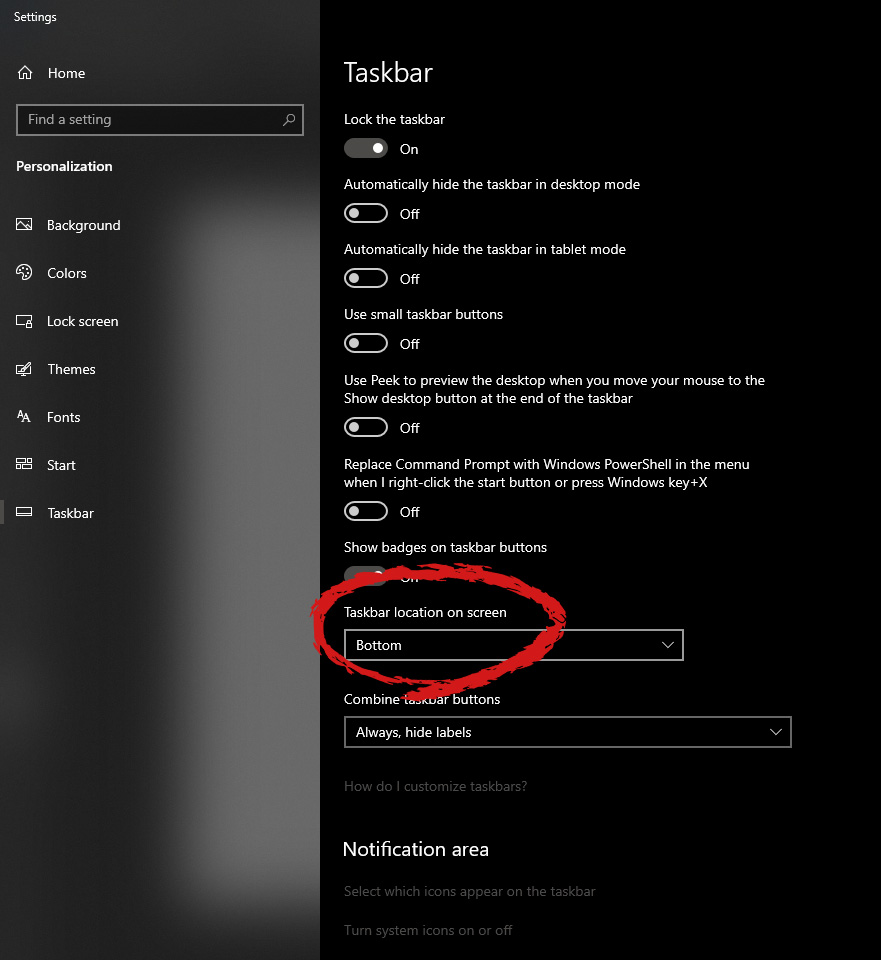 Click on the dropdown menu and choose the desired location for the taskbar.
Click on the dropdown menu and choose the desired location for the taskbar. PowerShell -ExecutionPolicy Unrestricted -Command "& {$manifest = (Get-AppxPackage Microsoft.<YOUR APP ID HERE>).InstallLocation + 'AppxManifest.xml' ; Add-AppxPackage -DisableDevelopmentMode -Register $manifest}"
 If you consider yourself a power user or you value your privacy then firefox is the browser for you. It is open source and is packed with great features like reporting when your email has been used for a known data breach, it stops annoying pop-up notifications, stops browser fingerprinting, and many more. Firefox is also a cross-platform browser making it a great choice if you want to transfer and use your data across multiple devices with one account. The downside of firefox however is its speed, this browser is the slowest on this list, I guess features and advantages took their tool in the speed department, but if that is not a concern for you and you feel like the positives outweigh some slower speed, grab it here.
If you consider yourself a power user or you value your privacy then firefox is the browser for you. It is open source and is packed with great features like reporting when your email has been used for a known data breach, it stops annoying pop-up notifications, stops browser fingerprinting, and many more. Firefox is also a cross-platform browser making it a great choice if you want to transfer and use your data across multiple devices with one account. The downside of firefox however is its speed, this browser is the slowest on this list, I guess features and advantages took their tool in the speed department, but if that is not a concern for you and you feel like the positives outweigh some slower speed, grab it here. Chrome browser has been a game-changer when it was released and even today some of its features are still great and needed. It is packed with some great features like tab freezing, for example, it is cross-platform meaning that also as firefox you can change data between browsers on different devices. it is a very expandable browser with tons of extensions and its speed performance is very very good. The downside of Chrome are two things sadly, one of them is its hunger for RAM, the browser takes a big chunk of RAM once it is active and on some older computer with limited RAM it performs slowly, another is telemetry which its sending, in other words, other browsers don’t come with the lingering fear that Google’s just a little bit too involved in all of our lives. But if downsides do not trouble you and you have a decent amount of RAM in your system chrome might be the best solution for you, grab it here and check it out.
Chrome browser has been a game-changer when it was released and even today some of its features are still great and needed. It is packed with some great features like tab freezing, for example, it is cross-platform meaning that also as firefox you can change data between browsers on different devices. it is a very expandable browser with tons of extensions and its speed performance is very very good. The downside of Chrome are two things sadly, one of them is its hunger for RAM, the browser takes a big chunk of RAM once it is active and on some older computer with limited RAM it performs slowly, another is telemetry which its sending, in other words, other browsers don’t come with the lingering fear that Google’s just a little bit too involved in all of our lives. But if downsides do not trouble you and you have a decent amount of RAM in your system chrome might be the best solution for you, grab it here and check it out. Or should I say Microsoft edge 2.0 since this new Edge is completely recoded and rethought, a completely new browser based on chromium. The first version of the edge was an inhouse attempt from Microsoft and it was a disaster, I guess the lesson was learned, and this new edge we have today is a great Browser, it is lightning fast and packed with some great features with one among them standing out I just love, that is the ability to save web pages as applications and truth to be told you have to try this in order to see al great advantages it offers. A very interesting feature is that edge itself wins the speed race from all of the 5 contestants here which is a great surprise. Of course, the downside of annoying Microsoft pushing it to be your default is, well it's Microsoft, as chrome is tied to Google so is edge tied to Microsoft, and the same dreaded feeling that big MS is watching you. If however, you do not concern yourself with these kinds of things, since it is already part of Windows 10, give it a spin and try it, I am sure you will at least love its blazing speed.
Or should I say Microsoft edge 2.0 since this new Edge is completely recoded and rethought, a completely new browser based on chromium. The first version of the edge was an inhouse attempt from Microsoft and it was a disaster, I guess the lesson was learned, and this new edge we have today is a great Browser, it is lightning fast and packed with some great features with one among them standing out I just love, that is the ability to save web pages as applications and truth to be told you have to try this in order to see al great advantages it offers. A very interesting feature is that edge itself wins the speed race from all of the 5 contestants here which is a great surprise. Of course, the downside of annoying Microsoft pushing it to be your default is, well it's Microsoft, as chrome is tied to Google so is edge tied to Microsoft, and the same dreaded feeling that big MS is watching you. If however, you do not concern yourself with these kinds of things, since it is already part of Windows 10, give it a spin and try it, I am sure you will at least love its blazing speed.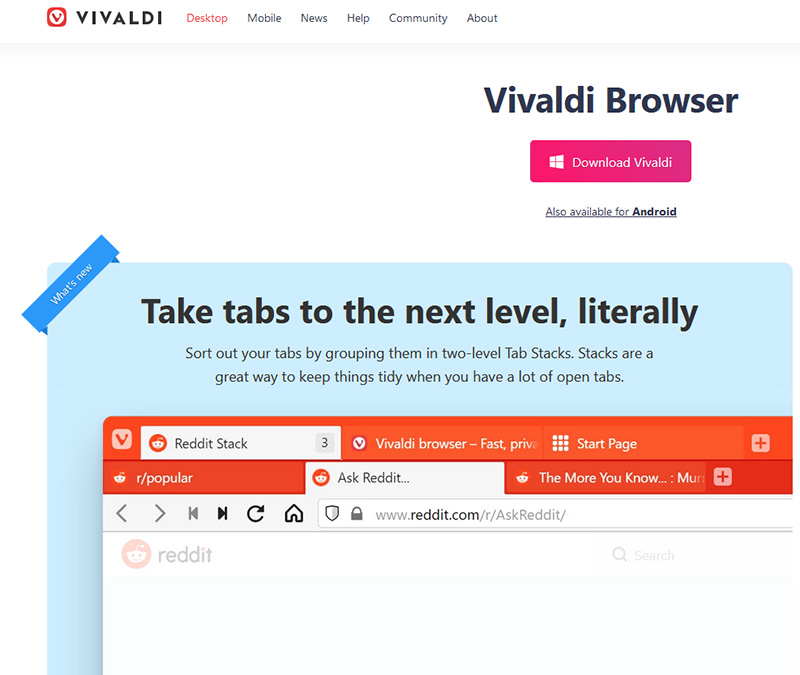 A new kid on the block, relatively unknown Browser Vivaldi offers some great customizable features no other one on this list offers, a very unique and down to each detail customization option, you can literally tweak each and every aspect of this browser making it best customizable and personal browser ever. How it is also based o chromium, every chrome extension works in it naturally. It is very good in speed and constantly updated and developed. The downside, well if you are anything like me, you could spend ages trying to customize it, ages, it has tons of features, and making it really feel and tick as you want can consume a really lot of time. If this thing does not bother you at all, grab Vivaldi here.
A new kid on the block, relatively unknown Browser Vivaldi offers some great customizable features no other one on this list offers, a very unique and down to each detail customization option, you can literally tweak each and every aspect of this browser making it best customizable and personal browser ever. How it is also based o chromium, every chrome extension works in it naturally. It is very good in speed and constantly updated and developed. The downside, well if you are anything like me, you could spend ages trying to customize it, ages, it has tons of features, and making it really feel and tick as you want can consume a really lot of time. If this thing does not bother you at all, grab Vivaldi here. Last but not least, we have another relic of the old browser age, the Opera browser. Packed with great security and great in-house features like a built-in VPN, built-in ad blocker, built-in crypto wallet, etc this browser seems like a swiss army knife. Opera is full of features and it shows once you start using it. The downside of opera is that its look and feel are specifically tailored to a certain type of user and not everyone will find that appealing or attractive, add some great but hidden and hard to come by features and it may go unnoticed. However, I think you should really give it a go since it definitely deserves more attention than it gets. Grab it here and check it out.
Last but not least, we have another relic of the old browser age, the Opera browser. Packed with great security and great in-house features like a built-in VPN, built-in ad blocker, built-in crypto wallet, etc this browser seems like a swiss army knife. Opera is full of features and it shows once you start using it. The downside of opera is that its look and feel are specifically tailored to a certain type of user and not everyone will find that appealing or attractive, add some great but hidden and hard to come by features and it may go unnoticed. However, I think you should really give it a go since it definitely deserves more attention than it gets. Grab it here and check it out.iWin is a self-published games platform that offers users to download and play free games. It is classified as potentially unwanted, primarily because it often comes bundled with the iWin Toolbar, which is an adware supported browser extension by Conduit. The iWin Toolbar is heavily flagged as malware or unwanted by numerous Antiviruses. iWin Games is not malicious in itself, though due to its bundling and common inclusion of the toolbar, many users wish to remove it.
powercfg –lastwakeOnce you enter the command given above, it will show you the last device that woke your PC up. After that, you need to type in the next command:
powercfg –devicequery wake_armedAfter entering the command, it will show you a list of all the devices that could wake your PC up. The goal in running these commands is to understand the reason what’s really causing your PC to turn on and see the reason is on the hardware level or not. Here are a couple of options you can try if your Windows 10 PC turns on by itself.
 Following are proven solutions that will resolve the issue and provide you with a working device.
Following are proven solutions that will resolve the issue and provide you with a working device.