There are times when you install a Windows update to your Windows 10 computer but you only got an error message saying, “The update isn’t applicable to your computer”. This is unusual as Windows was the one that downloaded them in the first place. To understand the reason behind this error, read on as this post will also give you a couple of suggestions you can try to fix the problem.
One of the main reasons why this error occurs is that your computer might not have the required installed updates and many more. Other reasons include:
To fix the problem, here are some suggestions that might help.
As pointed out earlier, updates are made according to the Windows versions. Thus, if one of the updates failed to install, you need to check if it’s applicable or not. The best way to do that is by searching the Windows update name on the official website of Windows.
It could be that the Processor Architecture is not compatible with the Windows Update you are trying to install. If you have an X86-based processor, you can’t install x64-based installations of Windows and vice-versa. This usually happens when you’ve downloaded the update manually and then tried installing it.
The issue might be because you are trying to install an old Windows update which is why it didn’t work. To check, go to Settings > Update and Security > View Update history. From there, you can look for the update.
To verify the update, just go to the Windows Update history once more as you did in option 2, and then see if the update is already installed or not.
AS mentioned earlier, there are some updates that depend on other updates before they get installed on your computer. The best way to verify is by checking the Microsoft Knowledge Base (KB). And to verify if the prerequisite updates are installed or not, just run the command below in PowerShell:
get-hotfix KB1111111, KB2222222, KB3333333
Note: In the command given above, you need to replace “KB1111111, KB2222222, KB3333333” with the actual update KB numbers.
As you know, Windows 10 has various auto-repair built-in tools to help users fix small issues which used to get fixed manually. And in this case, you will need the Windows Update Troubleshooter to fix the issue.

“D3dx9_43.DLL Not Found" "The file d3dx9_43.dll is missing" "File d3dx9_43.dll not found" "D3dx9_43.dll not found. Reinstalling might help fix this."
 Error Causes
Error Causes
 I do not know about you, but I prefer to set my Windows to be more to my liking and not how Microsoft thinks it should be. Let’s face it, not all users feel comfortable whit Microsoft settings and idea how things should be.
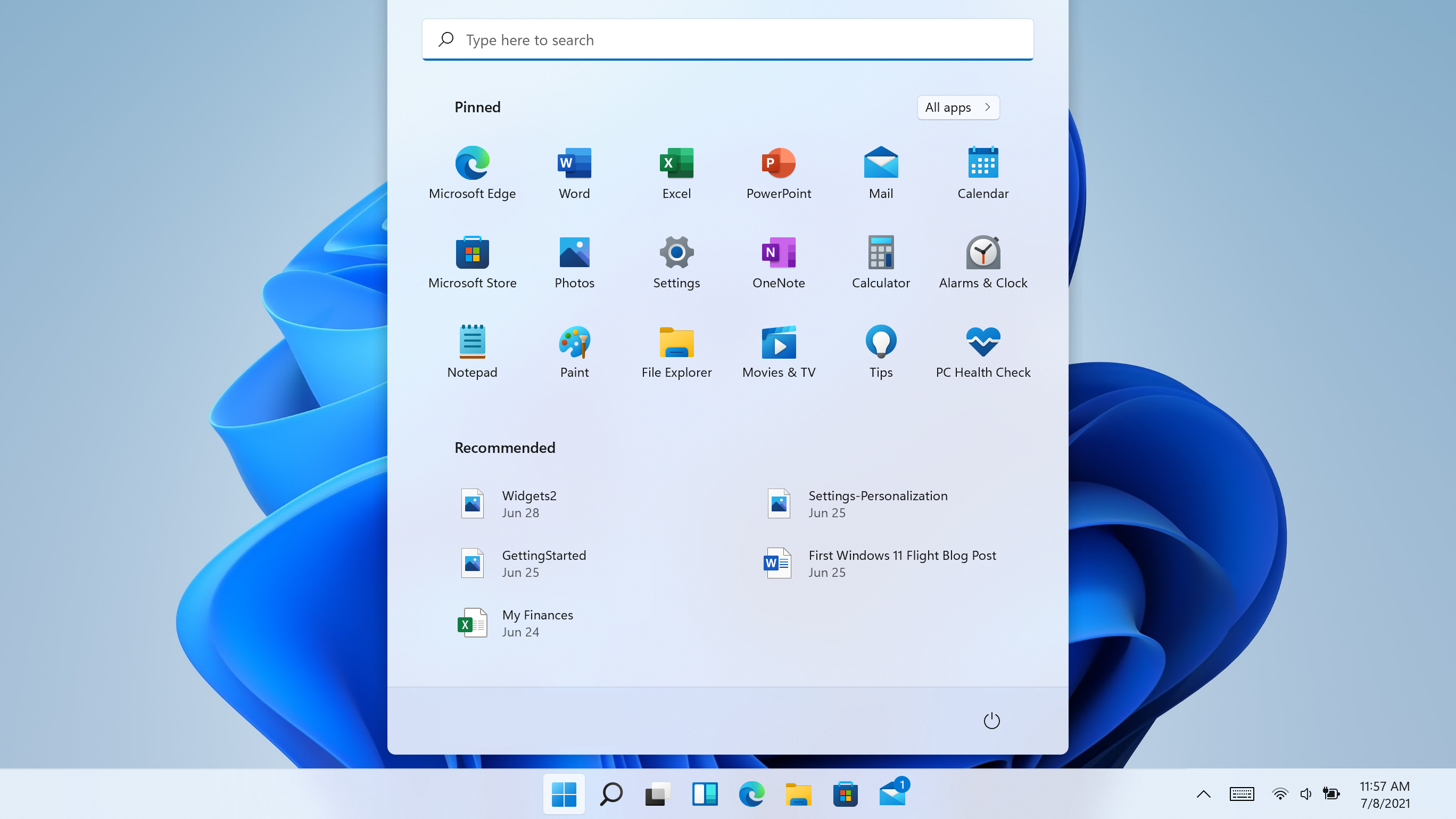
One of the things I particularly did not like even in Windows 10 is icons that come by default on my taskbar, now so far, well until the latest Windows 11 update you could remove default taskbar icons the same way as in Windows 10, just right-click on them and unpin, sadly with latest update build on Windows 11 this option has been removed.
In order to remove default icons from the taskbar, one must go now to Windows 11 settings and choose from there which one you would like to be placed on it. Of course, this is nothing game-breaking but it still feels strange why the standard option has been removed, it just makes no sense but lately not many things that come from Microsoft do.
I do not know about you, but I prefer to set my Windows to be more to my liking and not how Microsoft thinks it should be. Let’s face it, not all users feel comfortable whit Microsoft settings and idea how things should be.
One of the things I particularly did not like even in Windows 10 is icons that come by default on my taskbar, now so far, well until the latest Windows 11 update you could remove default taskbar icons the same way as in Windows 10, just right-click on them and unpin, sadly with latest update build on Windows 11 this option has been removed.
In order to remove default icons from the taskbar, one must go now to Windows 11 settings and choose from there which one you would like to be placed on it. Of course, this is nothing game-breaking but it still feels strange why the standard option has been removed, it just makes no sense but lately not many things that come from Microsoft do.
I do not know about you, but I prefer to set my Windows to be more to my liking and not how Microsoft thinks it should be. Let’s face it, not all users feel comfortable whit Microsoft settings and idea how things should be.
One of the things I particularly did not like even in Windows 10 is icons that come by default on my taskbar, now so far, well until the latest Windows 11 update you could remove default taskbar icons the same way as in Windows 10, just right-click on them and unpin, sadly with latest update build on Windows 11 this option has been removed.
In order to remove default icons from the taskbar, one must go now to Windows 11 settings and choose from there which one you would like to be placed on it. Of course, this is nothing game-breaking but it still feels strange why the standard option has been removed, it just makes no sense but lately not many things that come from Microsoft do.
I do not know about you, but I prefer to set my Windows to be more to my liking and not how Microsoft thinks it should be. Let’s face it, not all users feel comfortable whit Microsoft settings and idea how things should be.
One of the things I particularly did not like even in Windows 10 is icons that come by default on my taskbar, now so far, well until the latest Windows 11 update you could remove default taskbar icons the same way as in Windows 10, just right-click on them and unpin, sadly with latest update build on Windows 11 this option has been removed.
In order to remove default icons from the taskbar, one must go now to Windows 11 settings and choose from there which one you would like to be placed on it. Of course, this is nothing game-breaking but it still feels strange why the standard option has been removed, it just makes no sense but lately not many things that come from Microsoft do. “ehshell.exe – Common Language Runtime Debugging Services Application has generated an exception that could not be handled. Process id=0xa18 (2584), Thread id=0xa24 (2596).”
 Error Causes
Error Causes“Info: An error occurred while attempting to read the boot configuration data.” with File: as “BootBCD” “File: Windowssystem32configsystem Info: Windows failed to load because the system registry file is missing or is corrupt” “Info: The Boot Configuration Data for your PC is missing or contains errors.”To fix the error code 0xc000014C when booting your computer, you can check out the suggestions provided below.
C:/Windows/System32/config/RegBack