There are various components that take part during a Windows Upgrade process such as the CPU, Disk, Network, and many more. This is why the process of upgrading your Windows 10 computer can be quite complex and due to its complexity, there are times when you might encounter some errors like the Windows Upgrade error 0x800701E3.
If you encounter this kind of error then it has something to do with the “disk” part of the whole upgrade process which could be due to a conflict with the storage of your Windows 10 computer. When you receive this error, you will see the following error message on your screen:
“Windows cannot install required files. Make sure all files required for installation are available and restart the installation. Error code: 0x800701e3.”
To fix this Windows Upgrade error, here are some suggestions that might help.
Option 1 – Delete Files from Software Distribution Folder & Catroot2 folders
The downloaded Windows Updates are placed in a folder called “SoftwareDistribution”. The files downloaded in this folder are automatically deleted once the installation is completed. However, if the files are not clean up or if the installation is still pending, you can delete all the files in this folder after you pause the Windows Update service. For complete instructions, refer to the steps below.
- Open the WinX Menu.
- From there, open Command Prompt as admin.
- Then type in the following command – don’t forget to hit Enter right after typing each one of them.
net stop wuauserv
net start cryptSvc
net start bits
net start msiserver
- After entering these commands, it will stop the Windows Update Service, Background Intelligent Transfer Service (BITS), Cryptographic, and the MSI Installer
- Next, go to the C:/Windows/SoftwareDistribution folder and get rid of all the folders and files thereby tapping the Ctrl + A keys to select them all and then click on Delete. Note that if the files are in use, you won’t be able to delete them.
After resetting the SoftwareDistribution folder, you need to reset the Catroot2 folder to restart the services you just stopped. To do that, follow these steps:
- Type each one of the following commands.
net start wuauserv
net start cryptSvc
net start bits
net start msiserver
- After that, exit Command Prompt and restart your computer, and then try to run Windows Update once more.
Option 2 – Try running the DISM tool
You can try running the Deployment Imaging and Servicing Management or DISM tool to fix the Windows Upgrade problem. Using this built-in tool, you have various options such as the “/ScanHealth”, “/CheckHealth”, and “/RestoreHealth”.
- Open the Command Prompt with admin privileges.
- Then type in the following commands and make sure to hit Enter right after you type each one of them:
- Dism /Online /Cleanup-Image /CheckHealth
- Dism /Online /Cleanup-Image /ScanHealth
- exe /Online /Cleanup-image /Restorehealth
- Do not close the window if the process takes a while as it will probably take a few minutes to finish.
Option 3 – Run the System File Checker Scan
System File Checker or SFC is a built-in command utility that helps in restoring corrupted files as well as missing files. It replaces bad and corrupted system files with good system files. To run the SFC command, follow the steps given below.
- Tap Win + R to launch Run.
- Type in cmd in the field and tap Enter.
- After opening Command Prompt, type in sfc /scannow
The command will start a system scan which will take a few whiles before it finishes. Once it’s done, you could get the following results:
- Windows Resource Protection did not find any integrity violations.
- Windows Resource Protection found corrupt files and successfully repaired them.
- Windows Resource Protection found corrupt files but was unable to fix some of them.
Option 4 – Try running the ChkDsk utility
You can also run the ChkDsk utility to fix the Windows Upgrade error 0x800701E3.
- First, open This PC and right-click on your operating system partition for Windows.
- Next, click on Properties and navigate to the Tools tab.
- Then click on Check under the Error Checking section.
- After that, a new mini window will be opened and from there click on Scan drive and let it scan your disk drive partition for any errors and then restart your computer.
Option 5 – Run the Windows Update Troubleshooter
Running the built-in Windows Update troubleshooter is one of the things you can first check out as it is known to automatically resolve any Windows Update or upgrade errors like error code 0x800701E3. To run it, go to Settings and then select Troubleshoot from the options. From there, click on Windows Update and then click the “Run the troubleshooter” button. After that, follow the next on-screen instructions and you should be good to go.
Option 6 – Run Microsoft’s online troubleshooter
Running Microsoft’s online troubleshooter might also help you fix the Windows Upgrade error code 0x800701E3. This online troubleshooter is known to help in fixing Windows Update errors, it scans your computer for issues that might be causing the problem and then fixes them automatically.


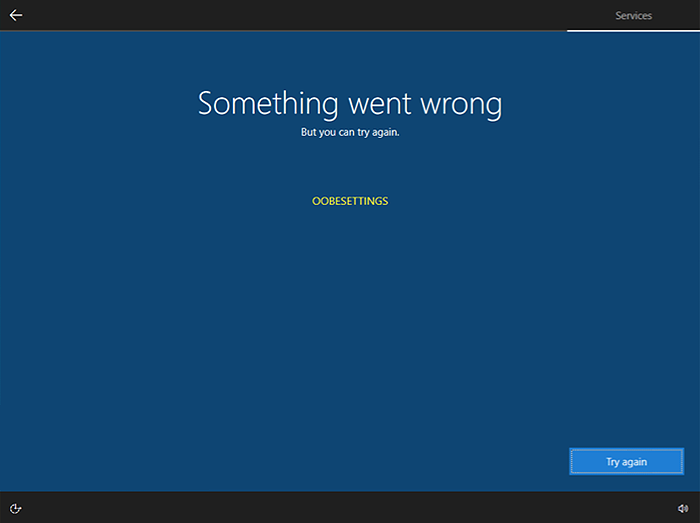 Oobesttings error is the blue screen of death error caused by some faulty settings inside the Windows registry. The good news is that this is not a hard error to fix and if by any chance you are one of the unfortunate people getting this dreaded annoying error, please do keep reading because we have several things that you can do in order to eliminate this issue from your computer.
Oobesttings error is the blue screen of death error caused by some faulty settings inside the Windows registry. The good news is that this is not a hard error to fix and if by any chance you are one of the unfortunate people getting this dreaded annoying error, please do keep reading because we have several things that you can do in order to eliminate this issue from your computer.
