SysPlayer is a potentially unwanted ad-supported media application from Goobzo.com. It can display targeted ads, hijack browser search results, and can display pop-up ads. This player gathers information about your visited websites, the number of clicks on each website, and cookie information containing sensitive data, that it occasionally sends back to the server.
Multiple Anti-virus programs detect SysPlayer as malicious or potentially unwanted as of the time of publication of this video. It has been associated in bundles with iWebar, which is also flagged by many AVs.
From the publisher:
SysPlayer is an extremely lightweight free Media Player with built-in codecs, which supports the most popular video and audio formats, as well as DVD, audio CD, Webcams, and other devices. It lets you play your video files, and watch images.
About Potentially Unwanted Applications
People have experienced it – you download and install a piece of free software, next you see some unwanted programs on your computer system, find a strange toolbar on your web browser, or find your default search engine has been changed. You did not set them up, so how did they appear? A Potentially Unwanted Program, also known as PUP, in short, is actually software that contains adware, installs toolbars, or has other hidden goals. These types of programs are almost always bundled up with free software which you download via the internet or may also be bundled inside the custom installers of many download sites.
Despite being considered very destructive, PUPs aren’t necessarily computer viruses or malware The main reason for this is the fact that the majority of PUPs get into users’ PC’s not because they exploit security weaknesses, for example, but because the users give consent to download and install it – unknowingly in general. On the other hand, there is no doubt that PUPs are still bad news for PC users as they can be incredibly dangerous to the computer in many ways.
What do PUPs do on your computer, really?
Unwanted programs can be found in many forms. More often, they can be found in adware bundlers which are known to use aggressive and misleading advertising. The majority of bundlers install many adware applications from several companies, each of which possesses its own EULA policy. Total System Care entirely eliminates this threat and protects your computer against unwanted programs or malware infection. PUPs that come as browser add-ons and toolbars are readily recognizable. They’ll modify web browser settings, change default search provider, substitute the default home page with their very own websites, decelerate internet speed, and can ruin your system also.
They may look innocent but PUPs are usually spyware. They could include things like information gathering code which could gather and send your private information to organizations. Even if the PUPs really aren’t inherently malicious, these programs still do practically nothing good on your computer – they’ll take valuable system resources, slow down your computer, weaken your computer security, and make your system more vulnerable to trojans.
Protect yourself from PUPs
• Read the terms and conditions so that the end-user license agreement (EULA) you’re accepting is only for the program you actually intend to download.
• Pick the “custom” install whenever installing a software program. Particularly, pay attention to those tiny boxes that have been checked by default, where you might ‘agree’ to receive advertising or install software bundlers.
• Have a top-notch anti-virus program like Total System Care which will protect your personal machine from PUPs. Once you install this software, protection from viruses and PUPs is already switched on.
• Avoid installing a freeware program you will not use. Prior to adding a toolbar or browser extension, think of whether it is really needed.
• Always download programs from the original website. The majority of PUPs find their way to your computer system is through download portals, so stay away from it entirely.
What To Do If You Cannot Install Any Anti-virus?
Practically all malware is bad, but certain kinds of malicious software do a lot more damage to your computer or laptop than others. Some malware variants modify web browser settings by including a proxy server or modify the PC’s DNS configuration settings. In these instances, you’ll be unable to visit certain or all of the sites, and therefore not able to download or install the necessary security software to eliminate the malware. If you are reading this article, you probably have got affected by malware that stops you from installing security software such as Safebytes Anti-Malware. Even though this sort of issue will be harder to get around, there are some steps you can take.
Eliminate viruses in Safe Mode
The Windows operating system includes a special mode known as “Safe Mode” in which just the bare minimum required applications and services are loaded. If the malware is obstructing access to the internet and affecting your computer, launching it in Safe Mode allows you to download anti-virus and run a diagnostic scan while limiting possible damage. In order to enter into Safe Mode or Safe Mode with Networking, press F8 while the computer is starting up or run MSCONFIG and look for the “Safe Boot” options in the “Boot” tab. Once you restart into Safe Mode with Networking, you could download, install, and update the anti-malware program from there. At this point, you are able to run the antivirus scan to get rid of computer viruses and malware without hindrance from another application.
Use an alternate web browser to download an anti-malware program
Some malware only targets certain internet browsers. If this is your case, employ another web browser as it can circumvent the computer virus. If you’re not able to download the anti-virus application using Internet Explorer, this means the virus may be targeting IE’s vulnerabilities. Here, you should switch over to a different internet browser like Firefox or Chrome to download the Safebytes Anti-malware program.
Create a portable USB antivirus for removing malware
Another option would be to make a portable antivirus program on your USB thumb drive. Follow these steps to employ a USB drive to clean your corrupted system.
1) On a virus-free PC, download and install Safebytes Anti-Malware.
2) Plug the USB drive into the uninfected computer.
3) Double-click on the downloaded file to open the installation wizard.
4) Pick thumb drive as the location when the wizard asks you exactly where you would like to install the software. Follow the activation instructions.
5) Transfer the USB drive from the uninfected PC to the infected computer.
6) Double-click the EXE file to run the Safebytes tool right from the thumb drive.
7) Click the “Scan” button to run a full computer scan and remove malware automatically.
SafeBytes Anti-Malware: Light-weight Malware Protection for Windows Computer
If you’re looking to buy anti-malware for your computer system, there are many brands and applications for you to consider. A few of them do a good job in eliminating threats while many will harm your computer themselves. It is important to opt for a company that creates industry-best antimalware and has achieved a reputation as reliable. When considering trustworthy applications, Safebytes AntiMalware is certainly the highly recommended one.
SafeBytes can be described as a powerful, real-time antivirus application that is created to assist the everyday computer end user in safeguarding their PC from malicious threats. Once you have installed this software program, SafeBytes superior protection system will make sure that absolutely no viruses or malicious software can seep through your PC.
SafeBytes anti-malware takes computer protection to a whole new level with its advanced features. The following are some of the great features included in the product.
World-class AntiMalware Protection: This deep-cleaning antimalware program goes much deeper than most anti-virus tools to clean out your personal computer. Its critically acclaimed virus engine finds and disables hard-to-remove malware that hides deep within your computer.
Active Protection: SafeBytes gives real-time active supervision and protection from all of known viruses and malware. They’re extremely effective in screening and getting rid of numerous threats because they’re regularly improved with new updates and alerts.
Quick Multi-threaded Scanning: Safebytes Anti-Malware, with its advanced scanning engine, provides extremely fast scanning which will quickly target any active online threat.
Web Protection: SafeBytes checks and provides a unique safety ranking to every single site you visit and block access to web pages known to be phishing sites, thus safeguarding you from identity theft, or known to contain malware.
Light-weight Utility: SafeBytes provides complete protection from online threats at a fraction of the CPU load due to its enhanced detection engine and algorithms.
24/7 Premium Support: Support service is accessible 24 x 7 x 365 days through chat and email to answer your concerns.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove SysPlayer without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by SysPlayer
Files:
Search and Delete: SysPlayer.lnk
Search and Delete: sysp.exe
Search and Delete: AccDownload.dll
Search and Delete: SysPlayer.lnk
Search and Delete: SysPlayerMenu.dll
Search and Delete: SysPlayerMenu64.dll
Search and Delete: imageformatsqjpeg4.dll
Search and Delete: libvlc.dll
Search and Delete: libvlccore.dll
Search and Delete: msvcp100.dll
Search and Delete: msvcr100.dll
Search and Delete: QtCore4.dll
Search and Delete: QtGui4.dll
Search and Delete: QtNetwork4.dll
Search and Delete: QtSql4.dll
Search and Delete: QtXml4.dll
Search and Delete: sqldriversqsqlite4.dll
Search and Delete: SysPlayer.exe
Search and Delete: uninstall.exe
Search and Delete: Updater.exe
Search and Delete: SPMupdate1.job
Search and Delete: SysPlayerUpd.job
Registry:
Key HKCUSoftwareTrolltechOrganizationDefaultsQt Plugin Cache 4.8.false
Key HKCUSoftwareTrolltechOrganizationDefaultsQt Factory Cache 4.8
Key HKLMSOFTWARESysPlayer
Key HKLMSOFTWAREMicrosoftWindowsCurrentVersionUninstallSysPlayer
Key HKLMSOFTWAREClassesSysPlayerFile
Key HKLMSOFTWAREClassesFoldershellexContextMenuHandlersSysPlayerMenuExt
Key HKLMSOFTWAREClassesDirectoryshellexContextMenuHandlersSysPlayerMenuExt
Key HKLMSOFTWAREClassesAppIDSysMenu.DLL
Key HKLMSOFTWAREClasses*shellexContextMenuHandlersSysPlayerMenuExt

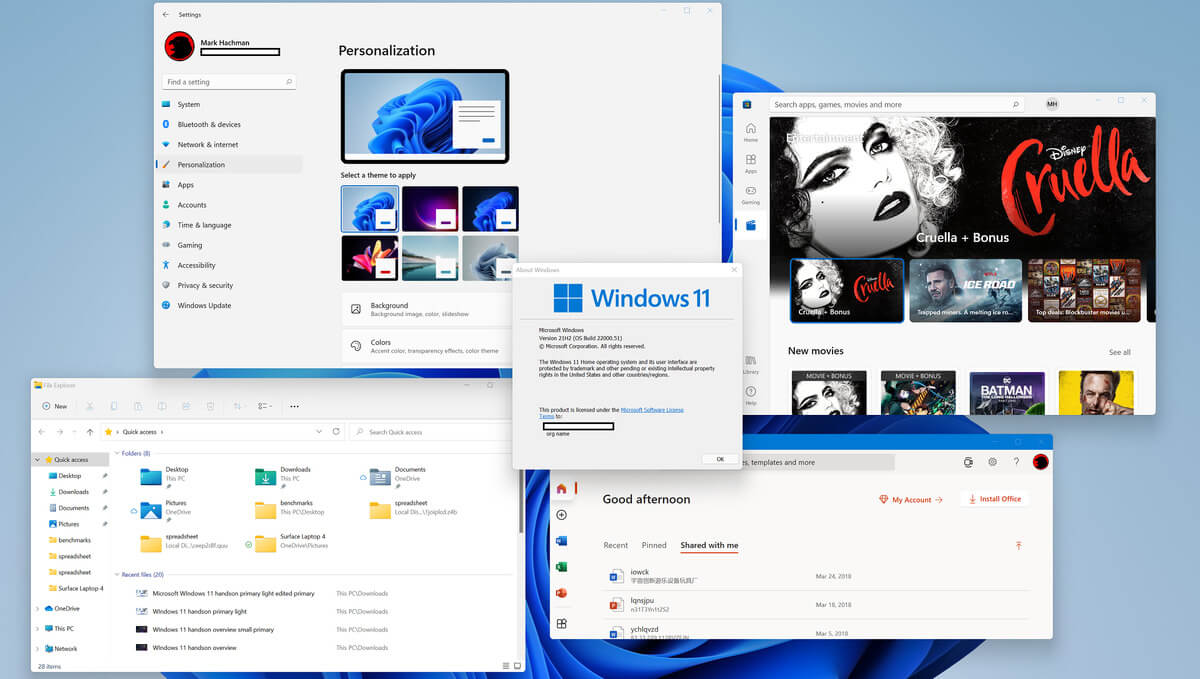 So far we probably all know what are good new and exciting features that W11 is bringing to the table, let’s talk now about features that will be removed and are not there but we had them in W10
So far we probably all know what are good new and exciting features that W11 is bringing to the table, let’s talk now about features that will be removed and are not there but we had them in W10

