FindWide is a browser add-on for Internet Explorer. This addon Hijacks your home page and internet search provider changing it to search.findwide.com. Alternate versions change the homepage to search.us.com.
This addon monitors your user activity while you are surfing the web. It collects user and browsing data, that it uses to better display targeted ads. While browsing with this addon enabled you will see additional ads, sponsored links, and even sometimes pop-up ads displaying throughout your browsing sessions.
Several anti-virus programs have marked this addon as a Browser Hijacker and is therefore not recommended to keep on your computer.
From the Author: Each search engine has its own method of searching and each will return different results. Findwide.com looks at all of them, decides which are most relevant to your search, eliminates duplicates, and reveals them to you. In the end, you get a list of results more complete than using any one search engine alone.
Help! Malware Blocking Antivirus Installation And Access To The Internet
Viruses could cause plenty of damage to your computer. Some malware is meant to restrict or block things that you wish to do on your personal computer. It may well not permit you to download anything from the net or it will stop you from accessing some or all websites, especially the anti-malware websites. If you’re reading this, you probably have got infected by a virus that prevents you from installing a computer security program like Safebytes Antimalware on your PC. Even though this kind of problem can be tougher to get around, there are some steps you can take.
Download the application in Safe Mode with Networking
If any virus is set to run automatically when Microsoft Windows starts, entering Safe Mode could block the attempt. Since only the bare minimum applications and services launch in safe mode, there are seldom any reasons for conflicts to take place. To launch your Windows XP, Vista, or 7 PCs in Safe Mode with Networking, follow the instructions below.
1) Press the F8 key continuously as soon as your computer boots, but before the big Windows logo comes up. This will bring up the Advanced Boot Options menu.
2) Choose Safe Mode with Networking using arrow keys and press ENTER.
3) When you are into this mode, you will have online access again. Now, utilize your browser to download and install Safebytes.
4) Following installation, do a full scan and let the software get rid of the threats it discovers.
Switch over to an alternate web browser
Certain malware might target vulnerabilities of a specific web browser that obstruct the downloading process. In the event you suspect that your Internet Explorer has been hijacked by malware or otherwise compromised by hackers, the best course of action is to switch over to an alternate internet browser such as Chrome, Firefox, or Safari to download your chosen computer security application – Safebytes Anti-Malware.
Install antivirus on a USB drive
Here’s another solution which is using portable USB anti-malware software that can scan your computer for malicious software without needing installation. Follow these steps to run the anti-malware on the affected computer system.
1) Download Safebytes Anti-Malware or MS Windows Defender Offline onto a clean computer.
2) Plug the Flash drive into the uninfected computer.
3) Double-click the exe file to open the installation wizard.
4) When asked, select the location of the pen drive as the place in which you want to put the software files. Follow the directions to complete the installation process.
5) Transfer the USB drive from the clean PC to the infected PC.
6) Double-click the anti-malware software EXE file on the thumb drive.
7) Press the “Scan” button to run a full computer scan and remove malware automatically.
Protect Your PC & Privacy With SafeBytes Anti-Malware
To help protect your computer or laptop from various internet-based threats, it is very important to install anti-malware software on your computer system. However, with countless numbers of antimalware companies in the marketplace, nowadays it is actually challenging to decide which one you should obtain for your laptop. A few are good ones, some are decent, while some are simply just fake anti-malware software that will harm your PC themselves! You must be careful not to choose the wrong product, especially if you buy a premium program. Among few good applications, SafeBytes Anti-Malware is the highly recommended program for security-conscious people.
SafeBytes anti-malware is a trustworthy tool that not only protects your PC completely but is also very easy to use for people of all skill levels. With its cutting-edge technology, this application can help you eliminate multiples types of malware like computer viruses, trojans, PUPs, worms, ransomware, adware, and browser hijackers.
SafeBytes anti-malware offers an array of advanced features which sets it apart from all others. The following are some typical features present in this computer software:
Real-time Threat Response: Malware programs attempting to enter the system are discovered and stopped as and when detected by the SafeBytes active protection shields. This tool will always monitor your PC for any suspicious activity and updates itself continuously to keep current with the latest threats.
Robust Anti-malware Protection: By using a critically acclaimed anti-malware engine, SafeBytes offers multilayered protection that is made to catch and eliminate threats that are concealed deep inside your computer.
Web Filtering: Through its unique safety score, SafeBytes alerts you whether a website is safe or not to visit it. This will assure that you’re always certain of your safety when browsing the net.
Lowest CPU/Memory Usage: SafeBytes is well-known for its low effect on computer resources and great detection rate of countless threats. It runs quietly and efficiently in the background so you are free to use your computer at full power all the time.
Fantastic Technical Support: Support service is accessible 24 x 7 x 365 days via chat and email to answer your queries.
To conclude, SafeBytes Anti-Malware is really great for securing your computer against all sorts of malware threats. Once you’ve installed SafeBytes Anti-Malware, you will no longer have to bother about malware or other security concerns. If you’re searching for a comprehensive antivirus program that’s still easy to use, SafeBytes Anti-Malware is just what you need!
Technical Details and Manual Removal (Advanced Users)
If you do not wish to use an automated tool and like to eliminate FindWide manually, you could possibly do so by going to the Windows Add/Remove Programs menu in the Control Panel and deleting the offending program; in cases of browser plug-ins, you can uninstall it by visiting the browser’s Add-on/Extension manager. You might also want to reset your home page and search engine providers and also clear your browser cache and cookies.
Finally, examine your hard disk for all of the following and clean your Windows registry manually to remove leftover application entries following uninstalls. But bear in mind, this is often a complicated task and only computer professionals could perform it safely. In addition, some malware is capable of replicating or preventing removal. Carrying out this malware-removal process in Safe Mode is suggested.
Files:
C:\Documents and Settings\%USERNAME%\Local Settings\Application Data\TNT2.0.0.1599\Autorun.inf
C:\Documents and Settings\%USERNAME%\Local Settings\Application Data\TNT2.0.0.1599\crx.tar
C:\Documents and Settings\%USERNAME%\Local Settings\Application Data\TNT2.0.0.1599\ffassist.1.dll
C:\Documents and Settings\%USERNAME%\Local Settings\Application Data\TNT2.0.0.1599\GLOBALUNINSTALL.TNT
C:\Documents and Settings\%USERNAME%\Local Settings\Application Data\TNT2.0.0.1599\hmac.1.dll
C:\Documents and Settings\%USERNAME%\Local Settings\Application Data\TNT2.0.0.1599\iehpr.1.dll
C:\Documents and Settings\%USERNAME%\Local Settings\Application Data\TNT2.0.0.1599\iestage2.1.dll
C:\Documents and Settings\%USERNAME%\Local Settings\Application Data\TNT2.0.0.1599\IEToolbar.dll
C:\Documents and Settings\%USERNAME%\Local Settings\Application Data\TNT2.0.0.1599\IEToolbar64.dll
C:\Documents and Settings\%USERNAME%\Local Settings\Application Data\TNT2.0.0.1599\INSTALL.TNT
 One of the first things that everyone saw when Microsoft has unveiled Windows 11 is its Start menu. Funny enough this is what has caused most of the divide among users, some find it interesting, and some do not like it. Truth is, it is different, and it is centered in the middle instead of the lower left part of the screen.
It has been confirmed however that the Start menu can be moved to any part of the screen so if you want, you could place it on the lower left as it has always been.
Live tiles do not longer exist in the Start menu, instead, we have styled simple icons.
One of the first things that everyone saw when Microsoft has unveiled Windows 11 is its Start menu. Funny enough this is what has caused most of the divide among users, some find it interesting, and some do not like it. Truth is, it is different, and it is centered in the middle instead of the lower left part of the screen.
It has been confirmed however that the Start menu can be moved to any part of the screen so if you want, you could place it on the lower left as it has always been.
Live tiles do not longer exist in the Start menu, instead, we have styled simple icons.
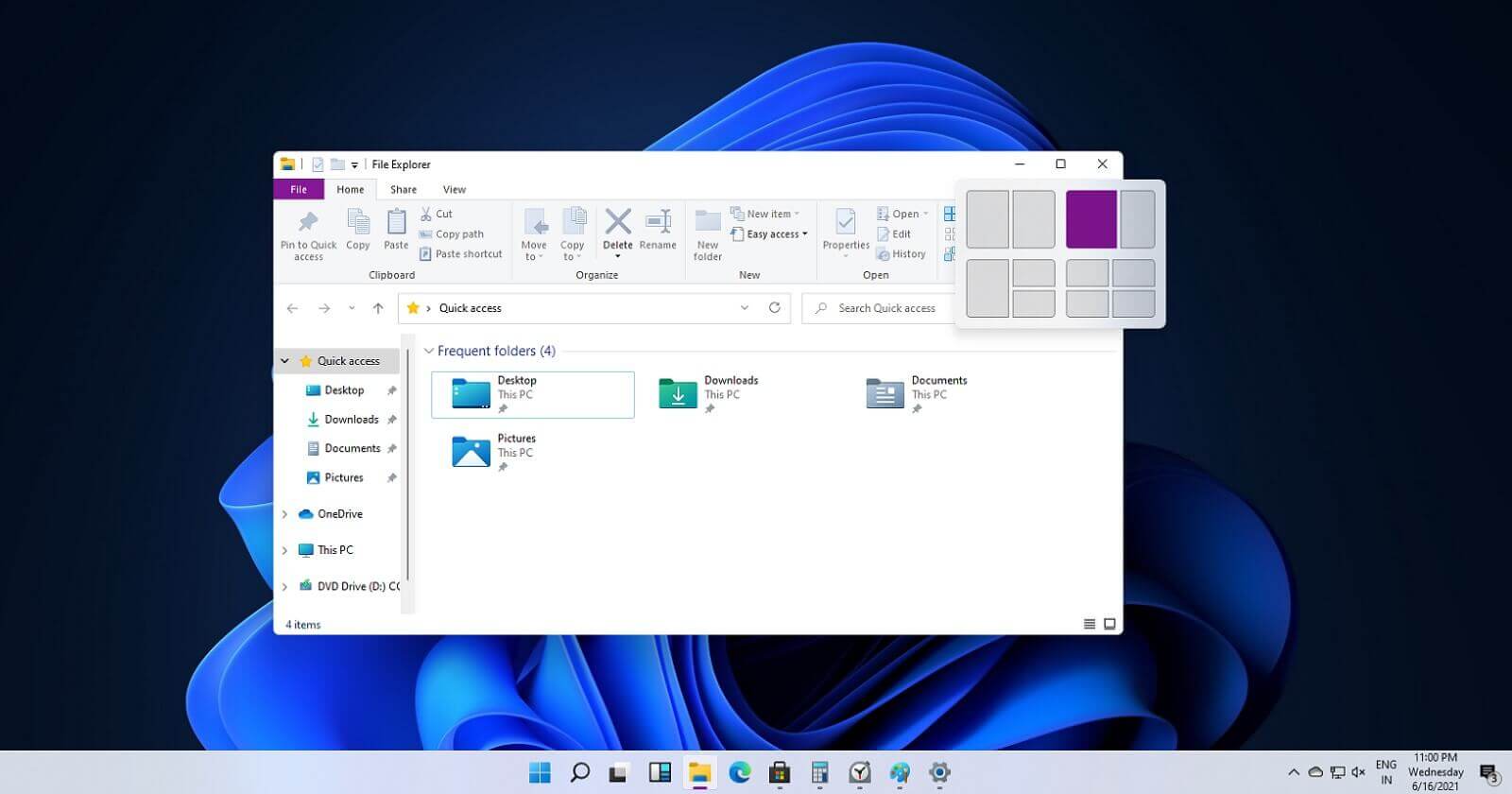 If you have used the cascade option in previous Windows versions then it is most likely that you will like the new Snap controls.
You can quickly snap windows side by side, or arrange them in sections on your desktop just by hovering over maximize button on the title bar.
If you have used the cascade option in previous Windows versions then it is most likely that you will like the new Snap controls.
You can quickly snap windows side by side, or arrange them in sections on your desktop just by hovering over maximize button on the title bar.
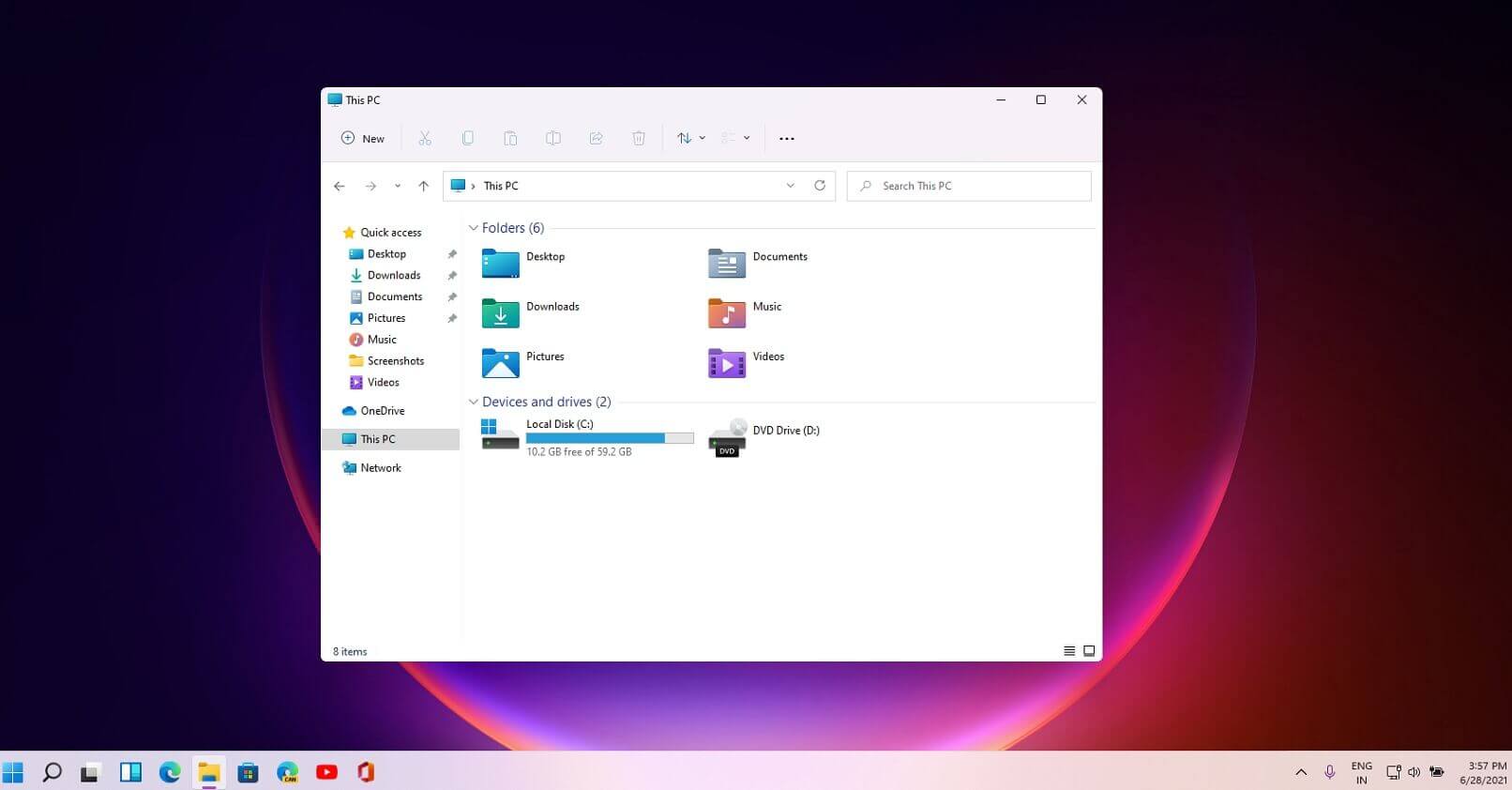 File explorer has gone through some visual and design changes, the ribbon on top has been completely removed and replaced with a header-like feature with a slick and clean design.
The header contains a nice organized and designed single row of icons like cut, paste, copy, rename, delete, and new folder icons.
File explorer has gone through some visual and design changes, the ribbon on top has been completely removed and replaced with a header-like feature with a slick and clean design.
The header contains a nice organized and designed single row of icons like cut, paste, copy, rename, delete, and new folder icons.
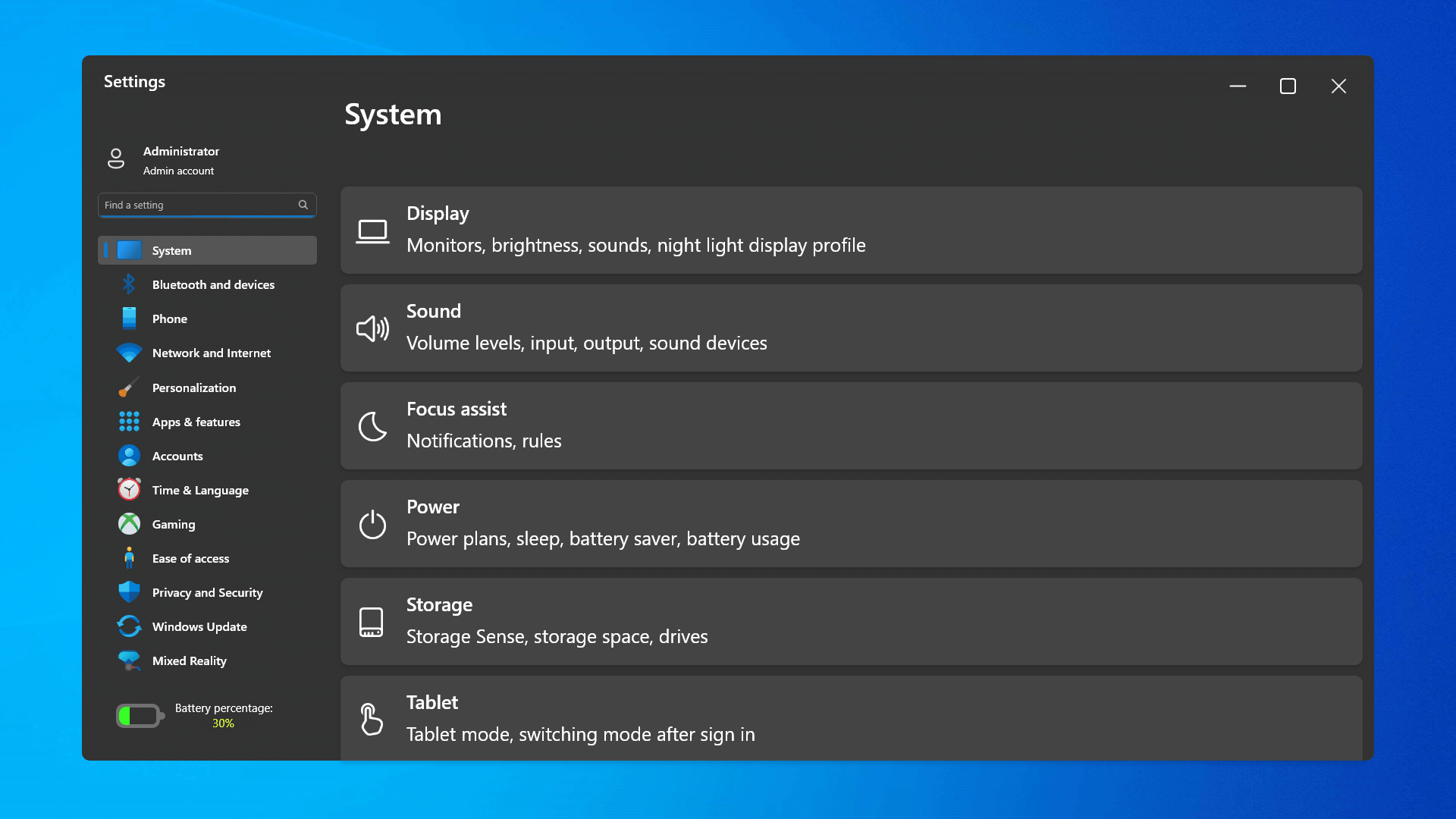 The settings app also has gone through visual and design changes. It has a new design that is very visually appealing and navigation has been simplified and more organized. Finding the right and desired setting is much faster and clearer now.
The settings app also has gone through visual and design changes. It has a new design that is very visually appealing and navigation has been simplified and more organized. Finding the right and desired setting is much faster and clearer now.
 Yes, widgets are back but not like you remember them.
Instead of being all-time present at your desktop like once they used to be, now there is a button on the taskbar which brings the widget bar up that contains desired widgets. This way they are easily accessible and do not clutter desktops.
So far we have weather, news, calendar, and stocks widget but we will see how development on these goes. I expect to have community-made widgets like in old days for all of our needs.
Yes, widgets are back but not like you remember them.
Instead of being all-time present at your desktop like once they used to be, now there is a button on the taskbar which brings the widget bar up that contains desired widgets. This way they are easily accessible and do not clutter desktops.
So far we have weather, news, calendar, and stocks widget but we will see how development on these goes. I expect to have community-made widgets like in old days for all of our needs.
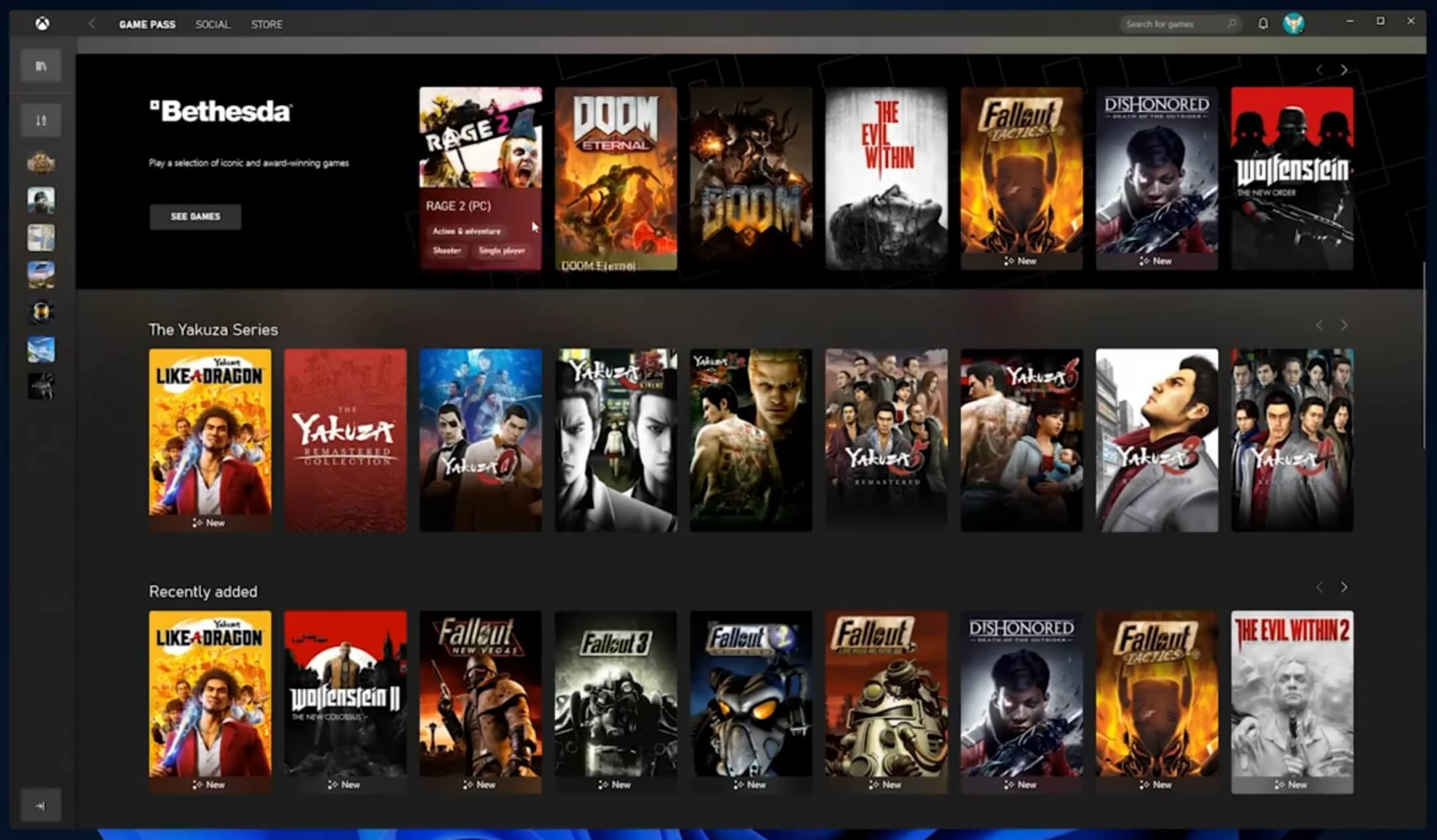 The new Xbox app is now integrated into Windows 11, offering quick access to Xbox Game Pass games, the social parts of the Xbox network, and the Xbox store.
The new Xbox app is now integrated into Windows 11, offering quick access to Xbox Game Pass games, the social parts of the Xbox network, and the Xbox store.
 As widely known by now Windows 11 will require you to have a TPM 2.0 module capable CPU in order to install it.
This system requirement has caused a lot of controversies but essentially it seems that MS's goal is to protect your personal data by using this module.
The upside of course is that your data will be protected much more than in previous Windows versions, the downside, of course, will be that you will need newer hardware to run OS on it.
and that is essentially it, keep on tuned on more Windows 11 information and overall articles tied to PC and technology here at errortools.com
As widely known by now Windows 11 will require you to have a TPM 2.0 module capable CPU in order to install it.
This system requirement has caused a lot of controversies but essentially it seems that MS's goal is to protect your personal data by using this module.
The upside of course is that your data will be protected much more than in previous Windows versions, the downside, of course, will be that you will need newer hardware to run OS on it.
and that is essentially it, keep on tuned on more Windows 11 information and overall articles tied to PC and technology here at errortools.com 
