nslookup is a command-line tool that helps in finding the DNS records of a website. It sends a name server query to the DNS and obtains the corresponding IP address. Aside from that, it can also perform some complex functionality such as finding details about FTP server, Mail server and many more but most of them are used by administrators. The best thing about nslookup is that it queries the DNS server directly and it does not rely on the cache.
On the other hand, there is another tool called PING that is used to verify connectivity. PING sends a packet of information to the IP address or Domain and gets back a response in the form of packets. So if everything goes well, all packets are received but if not, it will help you find out where the delay in the network exactly is. However, the ping command does not always attempt a DNS lookup which means that it might be using the DNS cache and use the IP address available in that table.
Although both nslookup and PING help you in identifying the host or IP address, however, they don’t always work and sometimes fail. So if your nslookup works but ping fails on your Windows 10 PC when querying the IP address of a website then it could be caused by many reasons. It could be that the nslookup queries work for you but when you try to use PING, it fails. For instance, if you open the abc.com website, here’s how it will look like:
nslookup xyz.com
Server: dns.company.com
Address: 192.168.1.38
C:> ping xyz.com
Ping request could not find host xyz.com. Please check the name and try again.
The domain is converted into an IP address and then data is sent to that IP address when you use PING. So when a reply comes back it means that the data is going back and forth to that domain without any problem. However, if the DNS fails to resolve the IP address of the website or if your PC does not attempt a DNS lookup, you will receive a similar error message that says, “Could not find host” and so on. To resolve this issue, here are some options that might help.
Option 1 – Reset Winsock, TCP/IP & Flush DNS
Resetting Winsock, TCP/IP, and flushing DNS might help you resolve the issue with nslookup and PING. To do so, follow these steps:
- Right-click on the Start button and click on Command Prompt (administrator) so you can pull up an elevated Command Prompt.
- After that, execute each one of the commands listed below. And after you typed in one after the other, you have to hit Enter.
- netsh winsock reset – type in this command to reset Winsock
- netsh int ip reset resettcpip.txt – type in this command to reset TCP/IP
- ipconfig /flushdns – type in this command to flush the DNS cache
- Next, restart your PC and check if the problem’s fixed.
Option 2 – Force Windows to do a DNS lookup using FQDN
- Go to Settings > Network & Internet > Status > Change adapter options.
- From there, right-click on the network and select Properties.
- Next, in case you’re using IPv6, from the list of connections available in the list, select Internet Protocol Version 4.
- Then click on Properties and click Advanced.
- After that, switch to the DNS tab and select “Append these DNS suffixes (in order)” and click on the Add button and then add “.” as a suffix so that each time you query using PING and another tool, it will add a “.” at the end and will force the lookup.
Option 3 – Make sure that there is only one default gateway
If your computer has more than one NIC connected and there are multiple default gateways, then it will most likely create confusion which is why you need to remove the default gateway from the configuration of all NICs and make sure that there is only one default gateway.
Option 4 – Use the Google Public DNS
You might want to change your DNS to Google Public DNS as it could also help you in fixing the nslookup and PING issues. To do so, follow the steps below.
- The first thing you have to do is right-click on the network icon in the Taskbar and select Network and Sharing Center.
- Next, click on the “Change Adapter Settings” option.
- After that, search for the network connection that you are using to connect to the internet. Note that the option might be “Wireless Connection” or “Local Area Connection”.
- Right-click on your network connection and click on Properties.
- Then select the new window to choose the “Internet Protocol 4 (TCP/IPv4)” option.
- After that, click on the Properties button and click the checkbox in the new window for the option “Use the following DNS server addresses”.
- Type in “8.8.8.8” and “8.8.4.4” and click OK and exit.
Option 5 – Check the Windows Host file
You can also try to cross-check the Windows Hosts file to find out if the website you are trying to open has been blocked, because if it is, then it’s no wonder why PING fails even when nslookup works. There are instances when some third-party application modifies the file and adds some websites to the blocklists. So if the website is indeed blocked, you need to remove it from the list.
Option 6 – Delete the WLAN Profiles
Deleting the WLAN Profiles might be a good idea if you are not able to connect to the internet on your computer and if you’re using Wi-Fi. It could be that the networks that were connected previously have gone rogue which is why it is not connecting properly. And so deleting the WLAN profiles might help you in fixing the issue with nslookup and PING.
Option 7 – Reinstall the Network Adapter Drivers
- Tap the Win + R keys to launch the Run window and then type in the “msc” command and hit Enter to open the Device Manager window.
- Under the Device Manager, you will see a list of drivers. From there, look for the Network Adapters and expand it.
- Then right-click on each one of the Network drivers and select “Uninstall device”.
- Restart your PC.
 In the menu choose device manager and click on it.
In the menu choose device manager and click on it.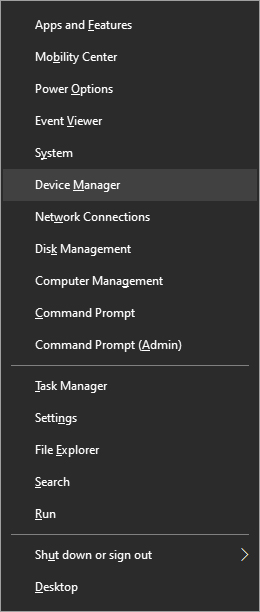 When the device manager opens, expand the Imaging devices or Cameras section.
When the device manager opens, expand the Imaging devices or Cameras section.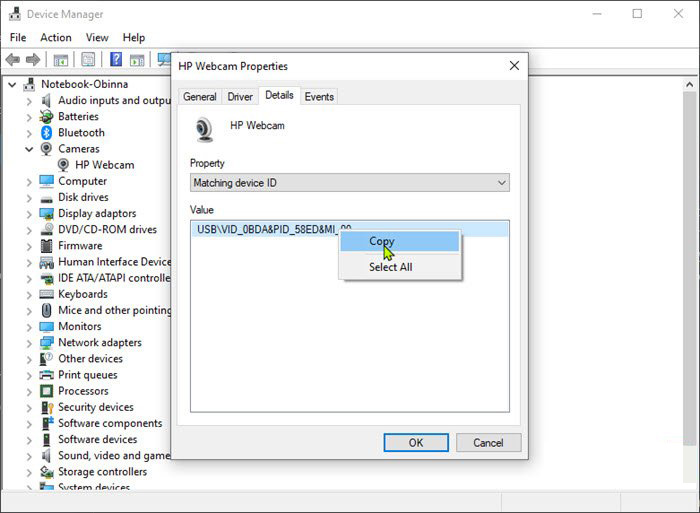 The next step is to download and install
The next step is to download and install 
 Antivirus software has become the kind of a must-have in every computer in this day and age. When you think about it, our systems are connected to the internet most of the time if not always, and therefore kind placed in from the line of various cyber-attacks. Here antivirus software comes into focus, especially because it has evolved long from just a simple virus removal tool to full security suites.
We will be going through the best of these applications in order to present both their good and bad sides and hope that we will help you in picking the right one for you. Remember, picking either one of the presented solutions is way better than not having one at all. The list is made from best down in our opinion so number one is highly recommended.
Antivirus software has become the kind of a must-have in every computer in this day and age. When you think about it, our systems are connected to the internet most of the time if not always, and therefore kind placed in from the line of various cyber-attacks. Here antivirus software comes into focus, especially because it has evolved long from just a simple virus removal tool to full security suites.
We will be going through the best of these applications in order to present both their good and bad sides and hope that we will help you in picking the right one for you. Remember, picking either one of the presented solutions is way better than not having one at all. The list is made from best down in our opinion so number one is highly recommended.
 California's Department of Fair Employment & Housing has widened its anti-discrimination lawsuit against Activision Blizzard and claims the publisher has been shredding vital documents relevant to the ongoing investigation.
A recent report from Kotaku described the department as offering poorly paid, highly insecure positions, with a culture of hostility towards LGBTQ+ testers. The DFEH's rewording of "employees" to "workers" now hopes to take these contractors' experiences into account.
"As a contract employee, I feel there's a lot of pressure to excel, impress, and move through the ranks as fast as you can before your contract ends and you're forced to go 3 months without income or find another job," Axios reports one worker saying. "I take pride in what I do, but it feels like it's never enough."
Activision's contentious hiring of union-busting third-party law firm WilmerHale "directly interferes" with its own investigation, it says. By going to WilmerHale, Activision appears to be claiming that all work related to the investigation is privileged and can't be shared with DFEH.
The suit also claims that Activision HR shredded documents related to "investigations and complaints", against its legal obligation to retain them during the investigation. The relevant parts of the updated lawsuit were shared by Axios reporters Stephen Totilo and Megan Farokhmanesh, the former also noting that the DFEH "fixed their misspelling of Bill Cosby's name".
"DFEH is also informed and aware that documents and records have not been maintained as required by law or by the DFEH's Document Retention Notice," the complaint reads, "including but not limited to documents related to investigations and complaints were shredded by human resource personnel and emails are deleted thirty days after an employees separation."
California's Department of Fair Employment & Housing has widened its anti-discrimination lawsuit against Activision Blizzard and claims the publisher has been shredding vital documents relevant to the ongoing investigation.
A recent report from Kotaku described the department as offering poorly paid, highly insecure positions, with a culture of hostility towards LGBTQ+ testers. The DFEH's rewording of "employees" to "workers" now hopes to take these contractors' experiences into account.
"As a contract employee, I feel there's a lot of pressure to excel, impress, and move through the ranks as fast as you can before your contract ends and you're forced to go 3 months without income or find another job," Axios reports one worker saying. "I take pride in what I do, but it feels like it's never enough."
Activision's contentious hiring of union-busting third-party law firm WilmerHale "directly interferes" with its own investigation, it says. By going to WilmerHale, Activision appears to be claiming that all work related to the investigation is privileged and can't be shared with DFEH.
The suit also claims that Activision HR shredded documents related to "investigations and complaints", against its legal obligation to retain them during the investigation. The relevant parts of the updated lawsuit were shared by Axios reporters Stephen Totilo and Megan Farokhmanesh, the former also noting that the DFEH "fixed their misspelling of Bill Cosby's name".
"DFEH is also informed and aware that documents and records have not been maintained as required by law or by the DFEH's Document Retention Notice," the complaint reads, "including but not limited to documents related to investigations and complaints were shredded by human resource personnel and emails are deleted thirty days after an employees separation."
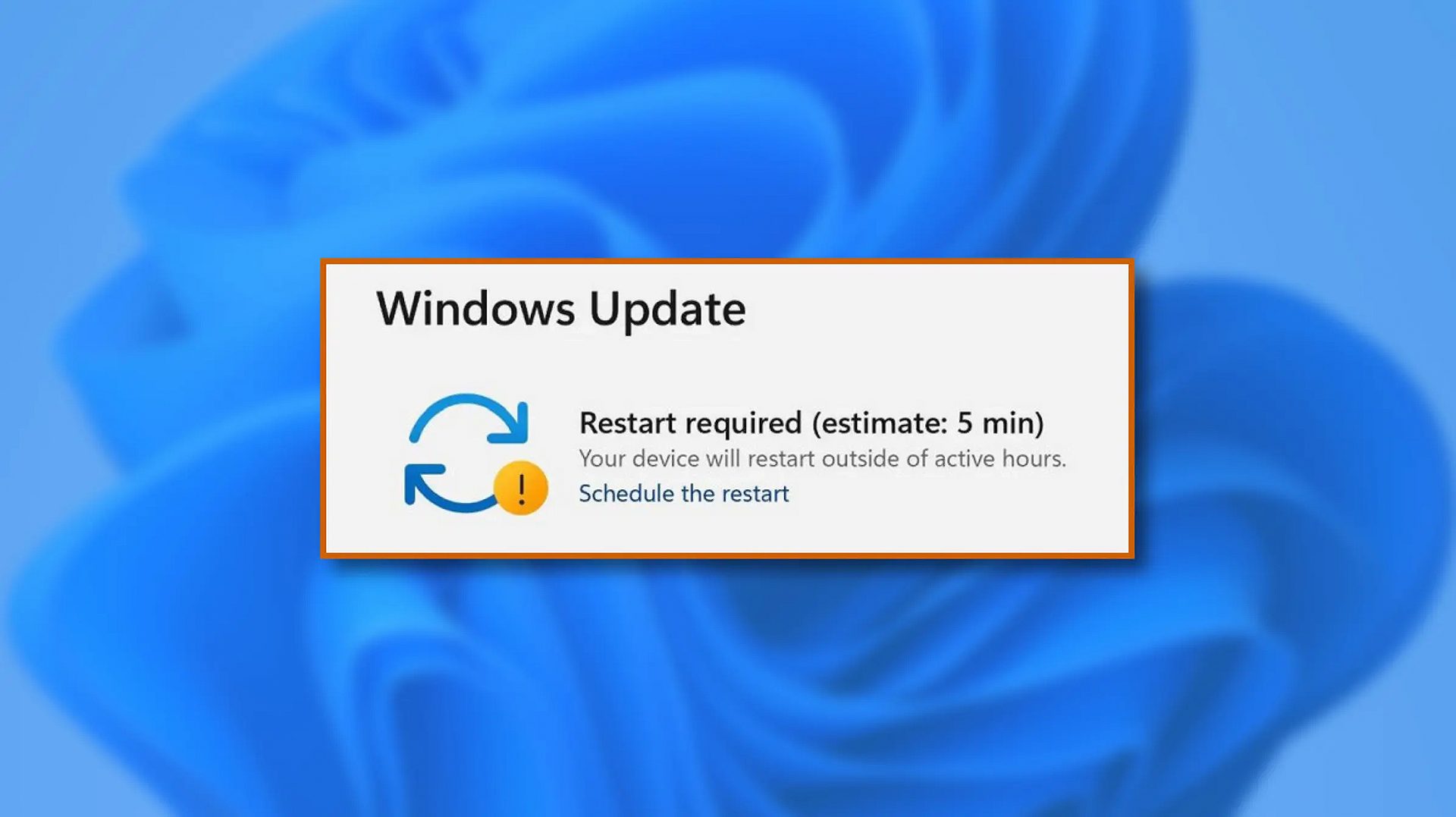 When Windows 11 update is available but you do not wish to restart right away because you are in the middle of using a computer, you can schedule a restart for up to 7 days. It is very easy and we will show you how to do it.
When Windows 11 update is available but you do not wish to restart right away because you are in the middle of using a computer, you can schedule a restart for up to 7 days. It is very easy and we will show you how to do it.
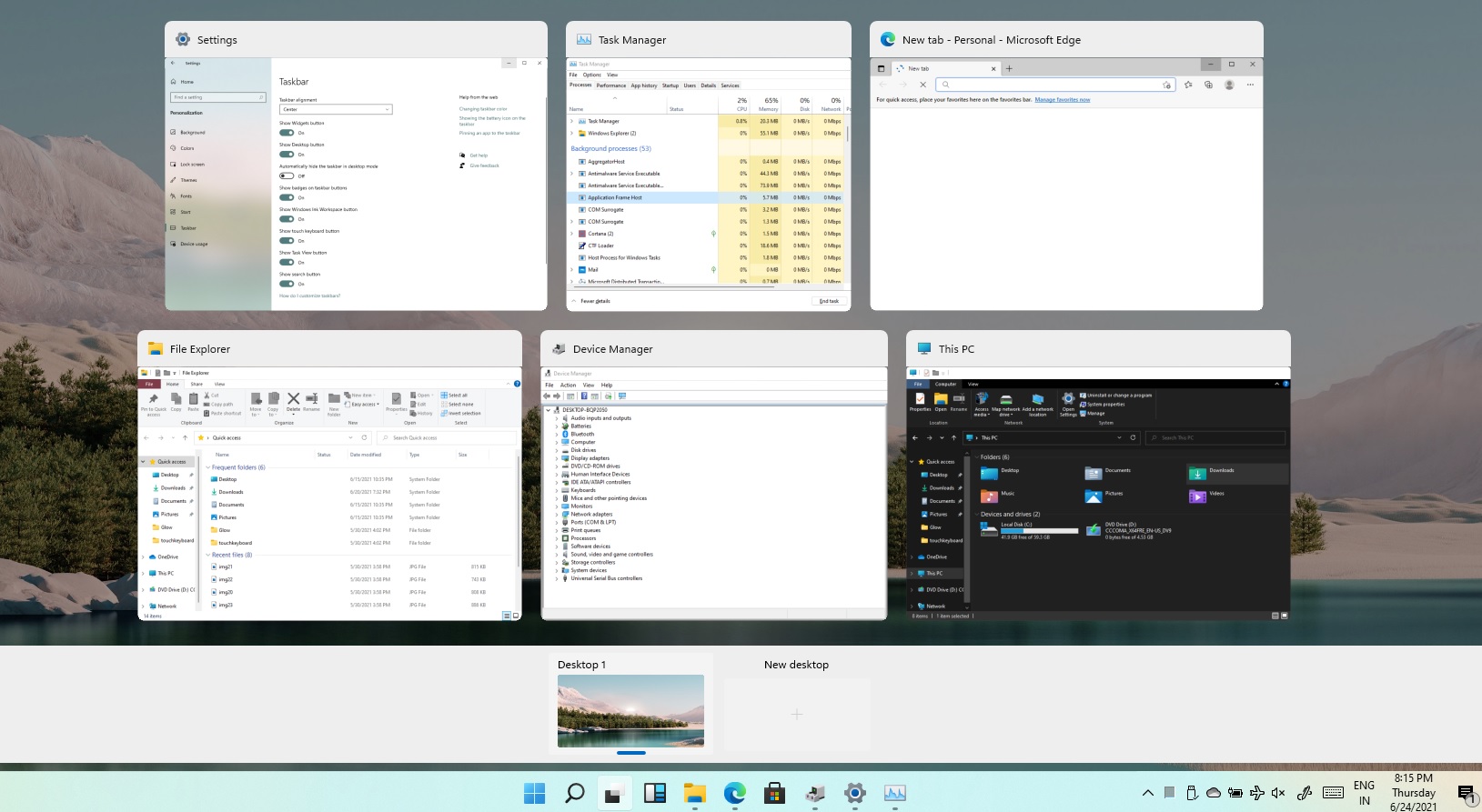 Task View feature inside Windows 11 is actually a great feature, letting you quickly view open windows and virtual desktops. How Task view itself could be reached with keyboard shortcut combination of ⊞ WINDOWS + TAB some users will prefer this way of using it and thus button on the taskbar is something you do not want or need.
There is a very easy way to remove mentioned button and I will show you how to do it.
Right-click the taskbar button itself and click on Hide From Taskbar.
That’s it, you have done it.
Now in order for you to bring it back if you change your mind, you will have to do some extra steps but it is nothing difficult.
Right-click on the taskbar and click on Taskbar settings, you will be lead to Personalization > Taskbar.
Inside locate Taskbar Items and switch Task View to ON, you will see the Task View button right away showing itself again.
Task View feature inside Windows 11 is actually a great feature, letting you quickly view open windows and virtual desktops. How Task view itself could be reached with keyboard shortcut combination of ⊞ WINDOWS + TAB some users will prefer this way of using it and thus button on the taskbar is something you do not want or need.
There is a very easy way to remove mentioned button and I will show you how to do it.
Right-click the taskbar button itself and click on Hide From Taskbar.
That’s it, you have done it.
Now in order for you to bring it back if you change your mind, you will have to do some extra steps but it is nothing difficult.
Right-click on the taskbar and click on Taskbar settings, you will be lead to Personalization > Taskbar.
Inside locate Taskbar Items and switch Task View to ON, you will see the Task View button right away showing itself again. 