Daily Bible Guide is a browser extension developed by Mindspark Inc. for Google Chrome Browser. This extension offers users a fast and easy way to find Bible passages, view daily verses, study the Bible and view the current weather. When installed, this extension changes your default search engine and your home page to MyWay.
When installed this extension gathers user browsing information such as visited websites, search queries, clicked links, and other information. This information is later used to better target ads.
While active, you may encounter additional unwanted ads and sponsored links throughout your browsing sessions.
Daily Bible Guide was marked as a Browser Hijacker by several anti-virus scanners, and due to its information mining behavior, it is considered a security risk and it is not recommended to keep on your computer; being flagged for optional removal.
About Browser Hijackers
Browser hijackers (sometimes known as hijackware) are a kind of malware that alters internet browser settings without the computer owner’s knowledge or approval. These kinds of hijacks are rising at a worrying rate around the globe, and it could be actually nefarious and sometimes dangerous too. There are plenty of reasons why you might experience an internet browser hijack; but commercial, advertising, and marketing are definitely the key reasons for their creation. Generally, the idea would be to force users to visit particular sites which are looking to improve their site visitor traffic and produce higher advertisement revenue. While it might seem harmless, these tools were created by malicious individuals who always attempt to take full advantage of you, so that they could make money from your naivety and distraction. Furthermore, hijackers can make the entire infected system vulnerable – other destructive malware and viruses will grab these opportunities to intrude into your computer effortlessly.
Signs of browser hijacker infection
The typical symptoms that signify having this malware on your computer are: home page is modified; you find new unwanted favorites or bookmarks added, typically directed to ad-filled or porn websites; the default search engine is modified; discover new toolbars which you did not add; you may see random pop-ups start occurring frequently; your internet browser has instability issues or exhibits frequent errors; you cannot visit specific websites like home pages of antivirus software.
So how does a PC get infected with a browser hijacker?
Browser hijackers attack computer systems via malicious email attachments, downloaded infected files, or by visiting infected sites. They sometimes are included with toolbars, add-ons, BHO, plugins, or browser extensions. A browser hijacker can also come bundled up with some free application that you inadvertently download to your computer, compromising your internet security. A good example of a popular browser hijacker is the most recent Chinese malware named “Fireball”, which has infected 250 million PCs throughout the world. It works as a hijacker but could be changed into a fully functioning malware downloader afterward.
Browser hijackers will interrupt the user’s browsing experience significantly, keep track of the websites frequented by users and steal private information, cause difficulty in connecting to the net, and ultimately create stability problems, causing software programs and computers to crash.
Browser Hijacker Malware – Removal
Certain browser hijacking can be quite easily reversed by identifying and removing the corresponding malware program through your control panel. However, the majority of hijackers are extremely tenacious and need specialized tools to eradicate them. Additionally, manual removals require deep system knowledge and thus can be quite a difficult task for inexperienced computer users.
Installing and running anti-malware programs on the affected computer could automatically delete browser hijackers and other malicious programs. Safebytes Anti-Malware features a cutting-edge anti-malware engine that will help you prevent browser hijacking in the first place, and clean up any pre-existing issues. In addition to anti-malware, a PC optimizer software, for example, Total System Care, will help you fix Windows registry errors, remove unwanted toolbars, secure online privacy, and stabilize software programs installed on the computer.
Malware Blocking Internet And All Antivirus Software? Do This!
Malware can cause a lot of damage to your PC. Some malware variants modify internet browser settings by including a proxy server or change the PC’s DNS settings. When this happens, you will be unable to visit some or all of the websites, and therefore not able to download or install the necessary security software to clear out the infection. If you’re reading this right now, you’ve perhaps recognized that virus infection is a reason behind your blocked internet connectivity. So how to proceed when you want to download and install an anti-malware program like Safebytes? Although this sort of issue will be difficult to get around, there are some steps you can take.
Install in Safe Mode
If the malware is set to run at Windows startup, then booting in safe mode should avoid it. Only minimal required programs and services are loaded when you start your PC into Safe Mode. You will have to do the following to remove malware in Safe mode.
1) At power-on/startup, press the F8 key in 1-second intervals. This will invoke the Advanced Boot Options menu.
2) Choose Safe Mode with Networking with arrow keys and press Enter.
3) As soon as this mode loads, you should have an internet connection. Now, obtain the malware removal program you want by using the browser. To install the software, follow the directions within the installation wizard.
4) Once the software is installed, let the scan run to eliminate viruses and other malware automatically.
Switch over to some other web browser
Web-based viruses could be environment-specific, aiming for a specific web browser or attacking particular versions of the web browser. If you are not able to download the security software using Internet Explorer, it means the virus may be targeting IE’s vulnerabilities. Here, you should switch to an alternate internet browser such as Chrome or Firefox to download the Safebytes application.
Create a portable USB antivirus for removing viruses
To effectively remove the malware, you should approach the issue of running an anti-malware program on the affected computer from a different perspective. To run anti-malware using a USB flash drive, follow these simple steps:
1) Download the anti-malware on a virus-free PC.
2) Mount the USB drive onto the same system.
3) Double-click the Setup icon of the anti-malware program to run the Installation Wizard.
4) Choose the drive letter of the USB drive as the location when the wizard asks you exactly where you would like to install the anti-virus. Do as instructed on the screen to finish off the installation process.
5) Now, transfer the flash drive to the infected PC.
6) Double click the Safebytes Anti-malware icon on the USB drive to run the application.
7) Run Full System Scan to detect and clean-up up all types of malware.
SafeBytes Anti-Malware - More Protection For You Personally
These days, an anti-malware tool can protect your computer from different kinds of online threats. But exactly how to select the best one among plenty of malware protection software that’s available on the market? You may be aware, there are many anti-malware companies and tools for you to consider. Some are worth your money, but many aren’t. You must be careful not to choose the wrong application, especially if you purchase a paid program. While thinking about the highly regarded software programs, Safebytes AntiMalware is undoubtedly the strongly recommended one.
SafeBytes anti-malware is a powerful, very effective protection application designed to assist users of all levels of computer literacy in detecting and eliminating harmful threats out of their PC. Once you’ve got installed this tool, SafeByte's state-of-the-art protection system will make sure that absolutely no viruses or malware can seep through your computer.
SafeBytes anti-malware takes computer protection to a whole new level with its advanced features. Listed below are some of the great ones:
Anti-Malware Protection: This deep-cleaning anti-malware software goes much deeper than most antivirus tools to clean out your personal computer. Its critically acclaimed virus engine finds and disables hard to remove malware that hides deep inside your computer.
Real-time Threat Response: Malware programs attempting to get into the computer are identified and stopped as and when detected by the SafeBytes real-time protection shields. It’ll inspect your personal computer for suspicious activity regularly and its unparalleled firewall shields your PC from illegal access by the outside world.
“Fast Scan” Features: SafeBytes’s virus scan engine is among the fastest and most efficient in the industry. It's targeted scanning highly increases the catch rate for viruses which is embedded in various PC files.
Web Protection: SafeBytes gives an instant safety rating to the web pages you are going to visit, automatically blocking dangerous sites and ensuring that you are certain of your safety while browsing the world wide web.
Light-weight: SafeBytes is a lightweight and user-friendly antivirus and antimalware solution. As it uses very little computer resources, this tool leaves the computer’s power exactly where it belongs to: with you.
24/7 Guidance: SafeBytes provides 24/7 technical support, automatic maintenance, and software upgrades for the best user experience.
To sum it up all, SafeBytes Anti-Malware offers great protection combined with very low system resource usage with both great malware prevention and detection. Malware trouble will become a thing of the past when you put this application to use. If you’re looking for the very best malware removal application out there, and when you don’t mind shelling out some money for it, opt for SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
If you’d like to manually remove Daily Bible Guide without using an automated tool, it might be possible to do so by deleting the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and uninstalling it. You will probably also want to reset your internet browser.
If you choose to manually remove the system files and Windows registry entries, utilize the following list to ensure that you know exactly what files to remove before performing any actions. Please remember that only experienced users should try to manually edit the system files simply because removing any single critical registry entry results in a major problem or even a PC crash. In addition, certain malicious programs have the capability to defend against its removal. It is advisable that you carry out the removal process in Safe Mode.
Files:
Search and Delete:
2vauxstb.dll
2vbar.dll
2vbarsvc.exe
2vbprtct.dll
2vbrmon.exe
2vbrstub.dll
2vdatact.dll
2vdlghk.dll
2vdyn.dll
2vfeedmg.dll
2vhighin.exe
2vhkstub.dll
2vhtmlmu.dll
2vhttpct.dll
2vidle.dll
2vieovr.dll
2vimpipe.exe
2vmedint.exe
2vmlbtn.dll
2vmsg.dll
2vPlugin.dll
2vradio.dll
2vregfft.dll
2vreghk.dll
2vregiet.dll
2vscript.dll
2vskin.dll
2vsknlcr.dll
2vskplay.exe
2vSrcAs.dll
2vSrchMn.exe
2vtpinst.dll
2vuabtn.dll
AppIntegrator64.exe
AppIntegratorStub64.dll
BOOTSTRAP.JS
2vffxtbr.jar
CHROME.MANIFEST
CREXT.DLL
CrExtP2v.exe
DPNMNGR.DLL
EXEMANAGER.DLL
Hpg64.dll
LOGO.BMP
NP2vStub.dll
T8EXTEX.DLL
T8EXTPEX.DLL
T8HTML.DLL
T8RES.DLL
T8TICKER.DLL
VERIFY.DLL
s_pid.dat
2vEIPlug.dll
2vEZSETP.dll
NP2vEISb.dll
00082350.exe
files.ini
Folders:
%APPDATA%\DailyBibleGuide\
%PROGRAMFILES%\DailyBibleGuide\
%PROGRAMFILES%\DailyBibleGuideEI\
Registry:
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\ Value: DailyBibleGuide Browser Plugin Loader
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\ Value: DailyBibleGuide Search Scope Monitor
Key HKCU\Software\DailyBibleGuide
Key HKLM\SOFTWARE\DailyBibleGuide
Key HKLM\SOFTWARE\MozillaPlugins\@DailyBibleGuide.com/Plugin
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DailyBibleGuidebar Uninstall Internet Explorer
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DailyBibleGuidebar Uninstall Firefox
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\beea7fa9-d1f4-49a2-9b1f-6fb7a2d9bc2a
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\0631bff0-6846-48ca-982d-d62d7f376e97
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.XMLSessionPlugin
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.UrlAlertButton
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.ToolbarProtector
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.ThirdPartyInstaller
Key HKHKLM\SOFTWARE\Classes\DailyBibleGuide.SkinLauncherSettings
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.SkinLauncher
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.SettingsPlugin
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.ScriptButton
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.RadioSettings
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.Radio
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.PseudoTransparentPlugin
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.MultipleButton
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.HTMLPanel
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.HTMLMenu
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.FeedManager
Key HKLM\SOFTWARE\Classes\DailyBibleGuide.DynamicBarButton


 I going to admit right here that I am a big fan of Cooler Master PC cases, I like them and they are always one of the things that I consider when building a new PC, overall I like their ideas and quality so personal for me it was quite a surprise to see that they are one that is making a new generation gaming chair.
Now truth to be told Orb X is not your typical gaming chair as you can clearly see from the pictures. The chair itself will come in two colors: white or black and RGB lighting looks to be prominently featured throughout.
I going to admit right here that I am a big fan of Cooler Master PC cases, I like them and they are always one of the things that I consider when building a new PC, overall I like their ideas and quality so personal for me it was quite a surprise to see that they are one that is making a new generation gaming chair.
Now truth to be told Orb X is not your typical gaming chair as you can clearly see from the pictures. The chair itself will come in two colors: white or black and RGB lighting looks to be prominently featured throughout.
 The chair itself is advertised as both meant and aimed for professional and gaming crowds but I believe the gaming crowd is in general more interested in this hardware piece.
Hardware is enclosed in a fully motorized shuttle dome which aims to maximize your privacy, it supports a single 49inch display or three 27inch monitors along with surround speakers if you do not wish to use headphones.
The chair itself is advertised as both meant and aimed for professional and gaming crowds but I believe the gaming crowd is in general more interested in this hardware piece.
Hardware is enclosed in a fully motorized shuttle dome which aims to maximize your privacy, it supports a single 49inch display or three 27inch monitors along with surround speakers if you do not wish to use headphones.
 It offers an adjustable headrest, lumbar support, and footrest so you can spend some time in it and be comfortable. Controls on the chair itself allow you to raise or lower the dome for easier getting in and out of it.
Orb X also has a compartment in its backside, it folds out and has a sliding tray designed to hold your PC or console. Everything is enclosed so wiring is not the issue.
Overall Orb X seems really like the computer chair of the future, Cooler Master expects to release the Orb X by December 2021, priced around $12,000-$14,000.
It offers an adjustable headrest, lumbar support, and footrest so you can spend some time in it and be comfortable. Controls on the chair itself allow you to raise or lower the dome for easier getting in and out of it.
Orb X also has a compartment in its backside, it folds out and has a sliding tray designed to hold your PC or console. Everything is enclosed so wiring is not the issue.
Overall Orb X seems really like the computer chair of the future, Cooler Master expects to release the Orb X by December 2021, priced around $12,000-$14,000.  In this article we are going to go through the best Stock Photo sites BUT, we will focus on ones that give you royalty-free Photos, so no paying stuff here, just the best of the free world.
In this article we are going to go through the best Stock Photo sites BUT, we will focus on ones that give you royalty-free Photos, so no paying stuff here, just the best of the free world.
 EVE Online is one of the earliest MMO games out there but since its release, it is still actively developed and is receiving updates. This science-fiction Sandbox will offer space lovers everything they need and more. Large scale PvP, mining, pirating, etc. It can be daunting and complex for beginners but take your time to get familiar with its systems and you will be rewarded greatly with an immersive and complex game worth the time. Open PvP in some zones might not be everyone’s cup of tea and seeing only your ship might be a turn-off for some players, but if you do not mind these things give it a go. It is free to play with an item shop.
EVE Online is one of the earliest MMO games out there but since its release, it is still actively developed and is receiving updates. This science-fiction Sandbox will offer space lovers everything they need and more. Large scale PvP, mining, pirating, etc. It can be daunting and complex for beginners but take your time to get familiar with its systems and you will be rewarded greatly with an immersive and complex game worth the time. Open PvP in some zones might not be everyone’s cup of tea and seeing only your ship might be a turn-off for some players, but if you do not mind these things give it a go. It is free to play with an item shop.
 FF14 had a tough start, so tough that it was scrapped and destroyed and has been remade again and that idea was great. The game now is better than ever and at this time it is experiencing large players from other games surging into it. This on the rails fantasy MMO will offer you a great story and great leveling experience. It has a free trial where you can play the whole original game for free but if you wish to continue playing you will have to buy the expansion and pay a monthly subscription but the content is well worth the money.
FF14 had a tough start, so tough that it was scrapped and destroyed and has been remade again and that idea was great. The game now is better than ever and at this time it is experiencing large players from other games surging into it. This on the rails fantasy MMO will offer you a great story and great leveling experience. It has a free trial where you can play the whole original game for free but if you wish to continue playing you will have to buy the expansion and pay a monthly subscription but the content is well worth the money.
 Let’s be honest, not a single list of MMO games cannot be without a once greatest and most successful MMO ever made, World of Warcraft. But instead of me praising the game why it was the greatest and why you should play it and how great it is I am going to take a little different approach. I am going to recommend you World of Warcraft classic, yup, you read it correctly, classic. Now World of Warcraft is a retail game with a subscription service but with that one subscription you will be able to access three games in the World of Warcraft universe: World of Warcraft retail (standard game), World of Warcraft Classic (vanilla WOW without expansions offering you experience as it once was when it was released) and World of Warcraft the Burning Crusade classic (same as WOW classic but with the first expansion the Burning Crusade). Among all solutions, I would really urge you to play either WOW classic or WOW TBC classic simply for reason that they are far superior games in comparison to typical retail ones, but if you like easier game go for retail, it is included in the sub anyway.
Let’s be honest, not a single list of MMO games cannot be without a once greatest and most successful MMO ever made, World of Warcraft. But instead of me praising the game why it was the greatest and why you should play it and how great it is I am going to take a little different approach. I am going to recommend you World of Warcraft classic, yup, you read it correctly, classic. Now World of Warcraft is a retail game with a subscription service but with that one subscription you will be able to access three games in the World of Warcraft universe: World of Warcraft retail (standard game), World of Warcraft Classic (vanilla WOW without expansions offering you experience as it once was when it was released) and World of Warcraft the Burning Crusade classic (same as WOW classic but with the first expansion the Burning Crusade). Among all solutions, I would really urge you to play either WOW classic or WOW TBC classic simply for reason that they are far superior games in comparison to typical retail ones, but if you like easier game go for retail, it is included in the sub anyway.
 Guild Wars 1 was one of my favorite games and I sank a lot of times in it and once Guild Wars 2 came I must admit I was pleasantly surprised with it and I would recommend it highly. The base game is completely free to play with only expansion to be purchased and it is buy to play model without monthly fees. It has specific mechanics different from other games and interesting classes to try. The living world is a great feature of the game and it is still very strong with its player base.
Guild Wars 1 was one of my favorite games and I sank a lot of times in it and once Guild Wars 2 came I must admit I was pleasantly surprised with it and I would recommend it highly. The base game is completely free to play with only expansion to be purchased and it is buy to play model without monthly fees. It has specific mechanics different from other games and interesting classes to try. The living world is a great feature of the game and it is still very strong with its player base.
 This game is made for people who enjoy, love, and like Star Wars. Mechanically besides being able to have henchmen with you and space battles (which I do not really like how they are done) game itself does not offer anything special. Where it shines is in the story and overall Star Wars experience. If you look at this game as a single-player game with multiplayer dungeons you will have a great time, since the story is really good but sadly end game lacks in comparison.
This game is made for people who enjoy, love, and like Star Wars. Mechanically besides being able to have henchmen with you and space battles (which I do not really like how they are done) game itself does not offer anything special. Where it shines is in the story and overall Star Wars experience. If you look at this game as a single-player game with multiplayer dungeons you will have a great time, since the story is really good but sadly end game lacks in comparison.
 I am going to admit something here, I was not fond of the idea to make the beloved Elder Scrolls series into MMO, but in time I gave it a go and I am really glad I did. This game is great and it is getting better and better as time progresses. It is buy to play without monthly fees and basic game free, same as FF14 but without fees. It has a decent community and offers a really good Elder Scrolls experience and now it is packing Morrowind expansions and other great areas. Highly recommended for any Elder Scrolls fan.
I am going to admit something here, I was not fond of the idea to make the beloved Elder Scrolls series into MMO, but in time I gave it a go and I am really glad I did. This game is great and it is getting better and better as time progresses. It is buy to play without monthly fees and basic game free, same as FF14 but without fees. It has a decent community and offers a really good Elder Scrolls experience and now it is packing Morrowind expansions and other great areas. Highly recommended for any Elder Scrolls fan.
 This one is troublesome to recommend, on one side you have free to play games deeply inside Tolkien Lord of the Rings lore, on the other side, you have outdated graphics and some stupid item shop decisions like buys specific classes. But if you look past stupid item shop decisions and can live with playing free class in the game you will be pleasantly surprised. The game itself is surprisingly good, the story is great as expected from the game infused with lore taken from one of the best books series ever written, and the feeling when visiting iconic landscape is epic. But if I need to be real as I should, I would recommend this one to people appreciate good story and lore and ones that are fans of Lord of the Rings itself.
This one is troublesome to recommend, on one side you have free to play games deeply inside Tolkien Lord of the Rings lore, on the other side, you have outdated graphics and some stupid item shop decisions like buys specific classes. But if you look past stupid item shop decisions and can live with playing free class in the game you will be pleasantly surprised. The game itself is surprisingly good, the story is great as expected from the game infused with lore taken from one of the best books series ever written, and the feeling when visiting iconic landscape is epic. But if I need to be real as I should, I would recommend this one to people appreciate good story and lore and ones that are fans of Lord of the Rings itself.
 Neverwinter is a premium and licensed D&D MMO game and it is well strange. The free-to-play model of the game will let you enjoy it until you hit the end game, then you will have to shell real money if you want to be competitive but the journey until then is great. I would recommend it to D&D lovers and people that love to try other people's maps, yup you read it correctly. Neverwinter has a map editor making it one of a kind MMO game where you can create your own dungeons and post them for other players to play, this user-generated content makes it a very specific beast in this list, and for that feature alone it has my recommendation.
Neverwinter is a premium and licensed D&D MMO game and it is well strange. The free-to-play model of the game will let you enjoy it until you hit the end game, then you will have to shell real money if you want to be competitive but the journey until then is great. I would recommend it to D&D lovers and people that love to try other people's maps, yup you read it correctly. Neverwinter has a map editor making it one of a kind MMO game where you can create your own dungeons and post them for other players to play, this user-generated content makes it a very specific beast in this list, and for that feature alone it has my recommendation.
 Another one of the older titles, Tera will offer you nor depth nor anything new in terms of leveling, quests, or end game except… the COMBAT. This is maybe the greatest MMO Combat game ever created and it is quite fascinating that even after so many years no other game has managed to create a better combat system than one of Tera. If you enjoy action combat and like some specific aesthetics Tera is a game for you.
Another one of the older titles, Tera will offer you nor depth nor anything new in terms of leveling, quests, or end game except… the COMBAT. This is maybe the greatest MMO Combat game ever created and it is quite fascinating that even after so many years no other game has managed to create a better combat system than one of Tera. If you enjoy action combat and like some specific aesthetics Tera is a game for you.
 Albion is a sandbox game with open-world PvP and building mechanics where you can build your own forest, house, etc. You know, sandbox stuff, including a lot of crafting and well, other sandbox stuff. If you want great quests and some occasional play then skip Albion, this game is made for a more hardcore player base not being afraid to die and spend some time crafting and going through the economy. The best comparison might be with EVE but in fantasy settings.
Albion is a sandbox game with open-world PvP and building mechanics where you can build your own forest, house, etc. You know, sandbox stuff, including a lot of crafting and well, other sandbox stuff. If you want great quests and some occasional play then skip Albion, this game is made for a more hardcore player base not being afraid to die and spend some time crafting and going through the economy. The best comparison might be with EVE but in fantasy settings.
 Black Desert is also a sandbox game but different from Albion, here you can organize and hire a workforce and send them to different nodes on a map to harvest resources and build an economy while you are on some epic adventure. Housing is also included but you can buy already made houses instead of making your own in the world. Combat is a game that comes very close to Tera combat and it is very enjoyable. The end game is money sink and PvP based so be careful when choosing this one.
Black Desert is also a sandbox game but different from Albion, here you can organize and hire a workforce and send them to different nodes on a map to harvest resources and build an economy while you are on some epic adventure. Housing is also included but you can buy already made houses instead of making your own in the world. Combat is a game that comes very close to Tera combat and it is very enjoyable. The end game is money sink and PvP based so be careful when choosing this one.
 If you like occult and supernatural with new world order themes and conspiracy theories, Secret World Legends is the game for you. Somewhat little clunky its setting and story really set it apart in many many ways. It has semi-action combat and it is free to play with item shop but all the content can be experienced for free. Recommended for fans of deeper gameplay and horror lore.
If you like occult and supernatural with new world order themes and conspiracy theories, Secret World Legends is the game for you. Somewhat little clunky its setting and story really set it apart in many many ways. It has semi-action combat and it is free to play with item shop but all the content can be experienced for free. Recommended for fans of deeper gameplay and horror lore.
 When I said no MMO list can be without World of Warcraft, it also cannot be without Runescape, one of the oldest games it was revamped with newer mechanics and graphics, free to play all the way and you can also pick old school Runescape if you really want to go all the way on a nostalgia trip. I would recommend a newer one for newer players, the game offers a great story and unusual quests infused with puzzles and interesting storylines. If you like really good quest design without fetch and grind quests along with interesting story this is a game for you.
When I said no MMO list can be without World of Warcraft, it also cannot be without Runescape, one of the oldest games it was revamped with newer mechanics and graphics, free to play all the way and you can also pick old school Runescape if you really want to go all the way on a nostalgia trip. I would recommend a newer one for newer players, the game offers a great story and unusual quests infused with puzzles and interesting storylines. If you like really good quest design without fetch and grind quests along with interesting story this is a game for you.
 Last on my list would be AION, a very interesting game made also a long way back, but the fact that is completely free with the cosmetic shop will make it as one to recommend since you can experience the whole game for free. It has some limited flying mechanics in it and later game zone are open PvP zones, story is interesting and leveling process is enjoyable. Also game itself is not really easy and if not careful you can get yourself in danger quite quickly. Recommended for old-school feeling.
Last on my list would be AION, a very interesting game made also a long way back, but the fact that is completely free with the cosmetic shop will make it as one to recommend since you can experience the whole game for free. It has some limited flying mechanics in it and later game zone are open PvP zones, story is interesting and leveling process is enjoyable. Also game itself is not really easy and if not careful you can get yourself in danger quite quickly. Recommended for old-school feeling.
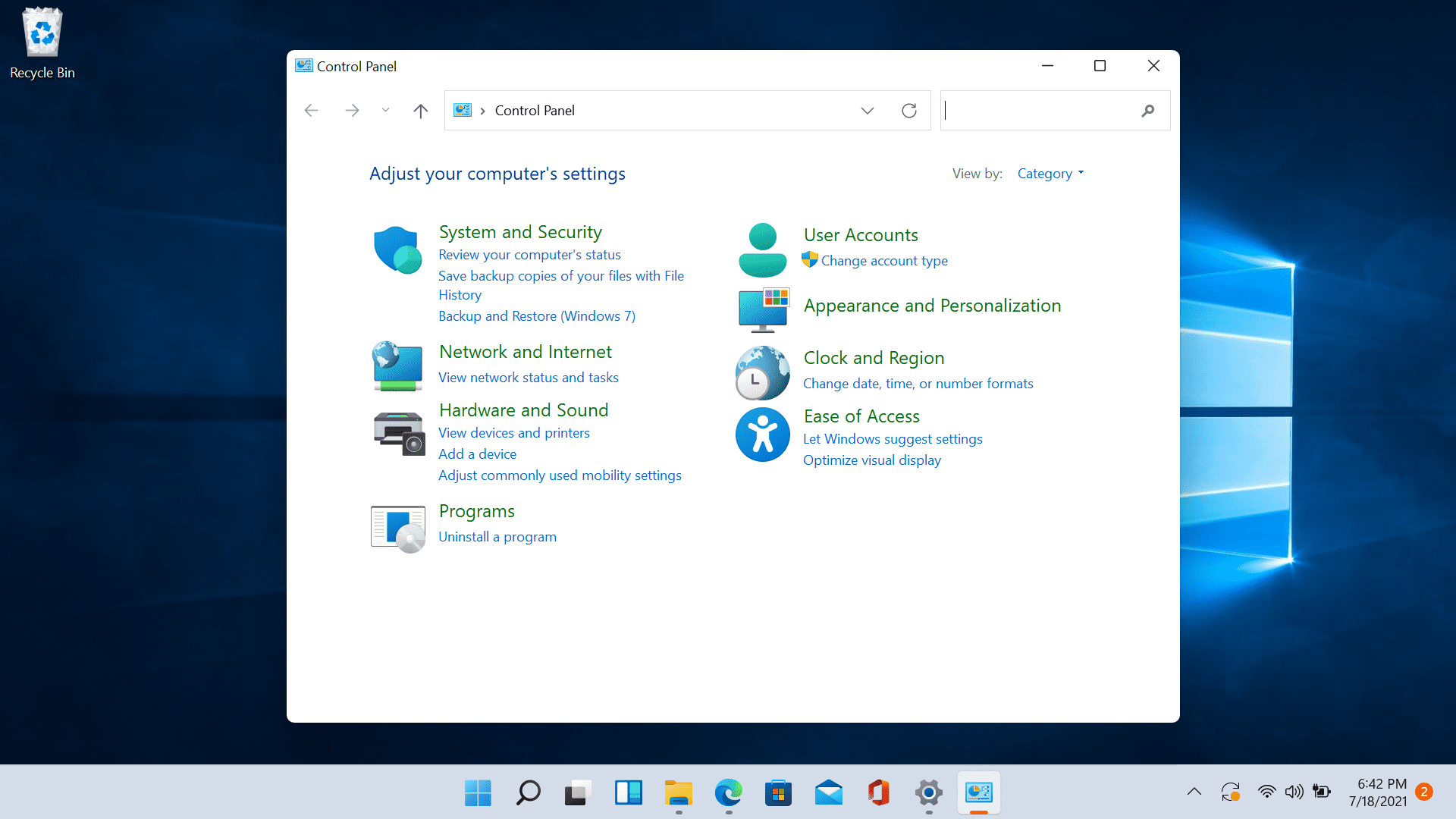 Since the Control Panel icon itself is somewhat not right away once clicked on the start button we are presenting you a couple of ways to open it so you can change each detail you want.
Since the Control Panel icon itself is somewhat not right away once clicked on the start button we are presenting you a couple of ways to open it so you can change each detail you want.
