Error Code 44 – What is it?
Error Code 44 is a device driver error that users encounter when using Windows 2000 operating system and later versions.
It is when the peripheral device that is connected to the computer, such as a printer or a fax machine, cannot be accessed as the programs required for operation interfere with other software on the computer. The error code will pop up with the following message:
“An application or service has shut down this hardware device. (Code 44)”
Solution
 Error Causes
Error Causes
Error Code 44 is caused when the program that you are using shuts down the peripheral device installed on your system. It is triggered by the following:
- Corrupted system registry entries
- Device driver files are outdated
- Device driver files are missing
It is critical to fix the Error Code 44 as it can pose serious risks to the wellbeing of your PC.
Further Information and Manual Repair
While bothersome, like other error codes, error code 44 to is relatively easy to fix. Here are ways to help resolve the error.
Method 1 – Restart your PC
The easiest method you can use to solve your PC error code is to simply run a restart of your Windows system. It may be that the error prompted upon connecting the device you have connected is merely a temporary problem, and upon restart, will resume functioning smoothly.
Method 2 – Run the Troubleshooting Wizard
If restarting your PC does not help, you will have to find the exact nature of the problem by running the troubleshooting wizard for the device and address the problem accordingly. To do this, proceed with the following steps:
- Run Device Manager on your PC
- Click on the program under the installed programs that are creating problems for you
- Click on the ‘General’ Tab
- Click ‘Troubleshoot’
- Upon opening, the Troubleshooting Wizard will ask a series of questions regarding the error. Answer the questions and follow its directions for solving the error code.
After following the directions of the Troubleshooting wizard, make sure to restart your PC for the changes to take effect. Then check if your device is still causing problems.
Method 3 – Manually uninstall and reinstall the device driver
If troubleshooting does not work, you may have to resort to manually uninstalling and then reinstalling the device driver causing the problem.
This would be necessary since the remaining incomplete files due to a partial removal or installation of programs is what contributes to the error code. A fresh install, after uninstallation of the previous drivers, would lead to the completion of the files.
You can do this by firstly logging in as Administrator and opening Device Manager. Select the device that is causing the problem and double click it and make sure that the peripheral is connected properly to the PC.
Upon opening, click on the ‘Driver’ tab and then select ‘Update Driver’. Make sure to refer to the system documentation that you received with your PC or computer to check for the motherboard details and driver specifics.
Method 4 – Use software to automatically download the driver
Manually uninstalling and reinstalling the driver will do the trick, however, it may be time-consuming especially when you would have to resort to your hardware user manual.
Therefore, using a program such as DriverFIX can save you a lot of time and frustration in having your device work properly on your computer.
Driver Assist, with its user-friendly approach to help you fix your PC issues, comes with an integrated database that detects which drivers you need to reconfigure within just a few seconds and downloads it automatically.
It further ensures that your drivers are installed in their entirety leaving no room for any incomplete files to remain that create Error Code 38.
It also has the added advantage of being able to backup and restores your files should there be the slightest possibility of system file damage. DriverFIX is the answer to fixing your PC error codes accurately and quickly.
Click here to download DriverFIX to fix Error Code 44 quickly and effectively!
 Update Windows 11
Update Windows 11

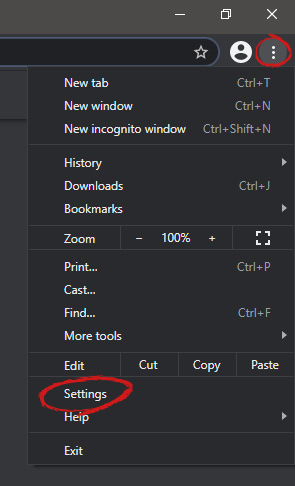 When you are in settings, on the left side move toward the bottom until you run into a tab that says On Startup and click on it. On right, a new section will open, click on Open a specific page or set of pages.
When you are in settings, on the left side move toward the bottom until you run into a tab that says On Startup and click on it. On right, a new section will open, click on Open a specific page or set of pages.
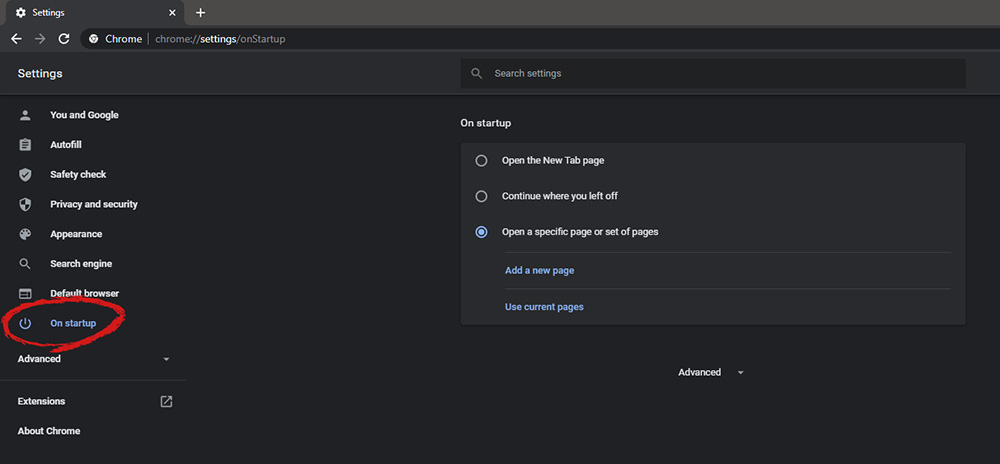 You will be presented with the option to add a new page by typing its URL or getting it from bookmarks or using a specific opened one. You can repeat this process until you have added all pages that you wish to be automatically opened once Chrome is opened for the first time.
You will be presented with the option to add a new page by typing its URL or getting it from bookmarks or using a specific opened one. You can repeat this process until you have added all pages that you wish to be automatically opened once Chrome is opened for the first time.


