iLivid is a video download manager for YouTube and other third-party video-hosted websites. iLivid download manager has powerful features that make it the fastest and easiest way to download hosted files. iLivid includes XBMC plug-ins that let you play almost all popular audio and video formats, in any available protocol and in any media type: streaming, CDs, DVDs, and RAR and archived files from your hard drive.
Livid is a program developed by Bandoo Media Inc. Upon installation, it defines an auto-start registry entry which allows the program to run on each boot for the user who installed it. A scheduled task is added to Windows Task Scheduler in order to launch the program at various scheduled times. The software is designed to connect to the Internet and adds a Windows Firewall exception in order to do so without being interfered with.
Multiple Anti-Virus scanners have detected iLivid as a possible Malware and are therefore not recommended.
About Potentially Unwanted Applications
Have you ever discovered an unwanted program running on your computer system and wondered how the heck it got there? These unwanted programs, which are referred to as Potentially Unwanted Programs, or PUP briefly, typically tag along as a software package when downloading the program and could cause serious problems for computer users.
The term PUP was actually coined to identify this downloadable crapware as something other than malicious software. The primary reason for this is the fact that the majority of PUPs get into users’ computers not because they exploit security weaknesses, for instance, but mainly because the users grant consent to install it – unwittingly in many instances. However, it is obvious that PUPs continue to be bad news for PC users as they could be really detrimental to your computer in numerous ways.
How does unwanted software affect you?
PUPs come in various forms; having said that, many are classified as adware, which always displays irritating ads and advertising banners on internet pages that you’re exploring. Additionally, they come in the form of web browser extension add-ons and toolbars. Not only they entirely fill up space on your computer screen, but toolbars could also manipulate search engine results, monitor your web browsing activities, decrease your web browser’s efficiency, and slow down your web connection to a crawl.
PUPs load up a nasty bite if left unchecked. Some PUPs carry keyloggers, dialers, and other software to gather your personal details which might lead to identity theft. Often, such software will turn off security protections and settings to take control over your computer, making that computer susceptible to online hackers and data thieves. At a minimum, PUPs slow your PC down with every added program.
Preventing unwanted programs
• When installing anything on your desktop, always study the fine print, including the EULA. Don’t accept terms of use that are for bundled programs.
• Choose the “custom” install whenever installing an application. In particular, focus on those tiny boxes that have been checked as default, where you may ‘agree’ to get advertisements or install software bundlers.
• Use an advert blocker/pop-up blocker; Deploy anti-malware products such as Safebytes Anti-malware. These software programs will establish a wall between your computer and cybercriminals.
• Avoid installing applications you don’t really need. Do not ever install software programs that appear suspicious or malicious.
• Don’t download programs from popups, internet advertising, file sharing sites, and also other unreliable sources; be cautious about any preset, unwanted options when downloading software. Avoid going to weblogs and sites that promote pirated software.
Can't Install Safebytes Anti-malware because of a Virus? Do This!
Malware could potentially cause a lot of damage to your personal computer. Some malware is designed to interfere with or prevent things that you wish to do on your computer. It may not allow you to download anything from the net or it will stop you from accessing some or all of the internet sites, particularly the anti-virus websites. If you’re reading this article, chances are you’re stuck with a virus infection that is preventing you to download and/or install the Safebytes Anti-Malware program on your computer system. There are a few solutions you could try to get around with this issue.
Download the software in Safe Mode with Networking
If the malware is set to load automatically when Microsoft Windows starts, getting into Safe Mode may block the attempt. Since just the bare minimum programs and services launch in safe mode, there are hardly any reasons for conflicts to take place. Below are the steps you have to follow to boot into the Safe Mode of your Windows XP, Vista, or 7 computers (visit Microsoft site for directions on Windows 8 and 10 PCs).
1) After switching on the computer, hit the F8 key while the Windows splash screen begins to load. This should bring up the Advanced Boot Options menu.
2) Choose Safe Mode with Networking with arrow keys and press Enter.
3) Once this mode loads, you will have the internet. Now, make use of your web browser to download and install Safebytes Anti-malware.
4) Immediately after installation, run a full scan and allow the software program to get rid of the threats it finds.
Switch to an alternate browser
Web-based malware could be environment-specific, targeting a particular internet browser or attacking particular versions of the browser. If you seem to have malware attached to Internet Explorer, then switch to a different internet browser with built-in safety features, such as Chrome or Firefox, to download your preferred antivirus program – Safebytes.
Run anti-virus from your USB drive
Another option is to save and run an anti-malware software tool entirely from a Pen drive. Follow these steps to use a USB drive to fix your corrupted computer.
1) On a virus-free computer, install Safebytes Anti-Malware.
2) Put the USB drive into the uninfected computer.
3) Double-click the Setup icon of the anti-malware software package to run the Installation Wizard.
4) Select the drive letter of the flash drive as the place when the wizard asks you where you want to install the antivirus. Follow the on-screen instructions to complete the installation process.
5) Unplug the USB drive. Now you can use this portable anti-malware on the infected computer system.
6) Double-click the antivirus program EXE file on the pen drive.
7) Run Full System Scan to identify and clean-up up all kinds of malware.
Let's Talk About SafeBytes Security Suite!
If you’re looking to download an anti-malware application for your computer, there are various tools in the market to consider nonetheless, you should not trust blindly anyone, no matter whether it is a free or paid program. Some of them are excellent, some are decent, while some will ruin your computer themselves! You have to select a company that creates industry-best anti-malware and has earned a reputation as reliable. Among few good programs, SafeBytes Anti-Malware is the highly recommended tool for the security-conscious individual.
Safebytes is one of the well-established PC solutions companies, which offer this complete anti-malware application. This software program could easily identify, eliminate, and protect your PC from the most advanced malware attacks such as spyware, adware, trojan horses, ransomware, worms, PUPs, and other possibly damaging software applications.
There are lots of amazing features you will get with this security product. Here are some popular features present in this software:
Real-time Threat Response: SafeBytes gives complete and real-time security for your personal machine. It will check your personal computer for suspicious activity at all times and safeguards your personal computer from unauthorized access.
Anti-Malware Protection: This deep-cleaning anti-malware application goes much deeper than most anti-virus tools to clean your computer. Its critically acclaimed virus engine detects and disables hard-to-remove malware that conceals deep inside your PC.
Web Security: Through its unique safety score, SafeBytes informs you whether a site is safe or not to access it. This will make sure that you’re always certain of your online safety when browsing the net.
High-Speed Malware Scanning Engine: Safebytes Anti-Malware, with its advanced scanning engine, offers super-fast scanning that can promptly target any active online threat.
Lowest CPU/Memory Usage: SafeBytes gives you complete protection from online threats at a fraction of the CPU load due to its enhanced detection engine and algorithms.
24/7 Online Technical Support: You will get 24/7 technical support to quickly resolve any problem with your security application.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually get rid of iLivid without using an automated tool, it may be possible to do so by deleting the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browser’s AddOn/Extension manager and uninstalling it. It is also recommended to factory reset your browser to its default condition to fix corrupt settings.
If you decide to manually remove the system files and registry entries, utilize the following list to ensure that you know exactly what files to remove before executing any actions. However, editing the registry is really a complicated job that only advanced computer users and professionals should try to fix the problem. Moreover, certain malicious programs are capable to defend against its deletion. It is recommended that you do the removal process in Windows Safe Mode.


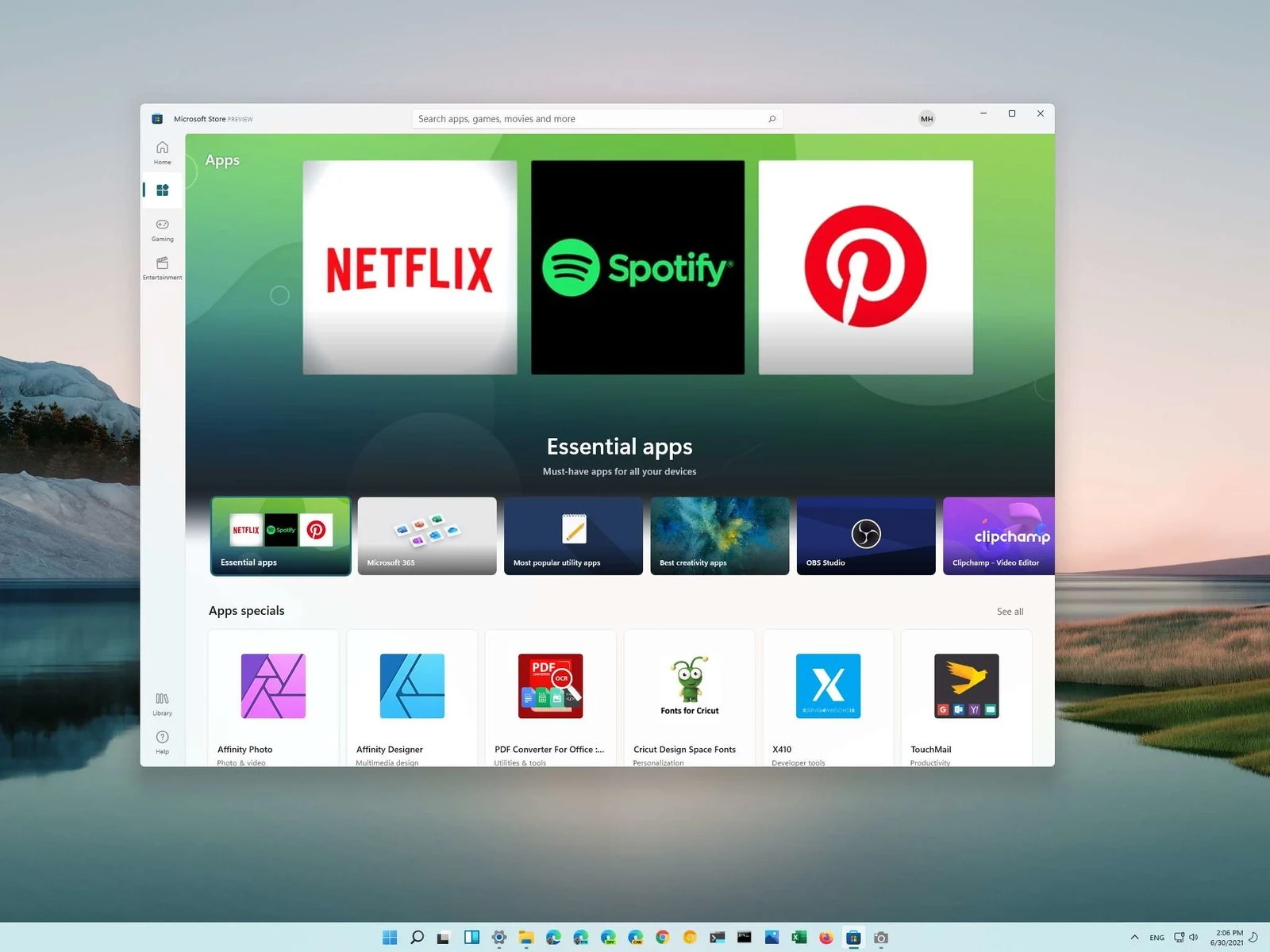 You can prevent starting of app installations files if they have not come from the MS store inside Windows 11.
This can make your PC more secure because all apps in the store will have to be digitally signed and overall it can provide you with more control over what will be installed.
Follow the guide below to find out how can you easily turn this feature ON.
You can prevent starting of app installations files if they have not come from the MS store inside Windows 11.
This can make your PC more secure because all apps in the store will have to be digitally signed and overall it can provide you with more control over what will be installed.
Follow the guide below to find out how can you easily turn this feature ON.
