Email Access Online is a browser extension published by Polarity Technologies Ltd. That offers users quick and easy access to emails and weather reports. While this might sound interesting and useful, there is nothing this extension offers that cannot be solved with a few simple bookmarks.
While installed Email Access Online monitors the user's browser activity and records visited websites, clicked links, and bought products, this data is later used to serve partner ads if the user looks for the covered categories, additionally, it will hijack your new tab page, changing your search engine to Yahoo to allow easier ad placement.
Browsing the internet with this extension enabled will result in additional ad placement, pop-up ads, and sponsored links throughout your browsing sessions.
Upon further investigation, it was discovered that this extension is a repack of MyEmailXP, which was a repack of Fast Email Checker. Due to its suspicious delivery methods and information gathering, several anti-virus scanners have marked this extension as a browser hijacker and it is recommended to remove it from your computer.
About Browser Hijackers
Browser hijacking means that a malicious code has taken control over and modified the settings of your web browser, without your consent. Browser hijacker malware is designed for many different reasons. The idea is to force users to visit specific websites which are aiming to increase their visitor traffic and generate higher advertisement income. It may appear naive, but the majority of such websites are not legitimate and can present a significant risk to your online safety. In a worst-case scenario, your internet browser could be hi-jacked to download malicious software that can do a lot of damage to your PC.
Major signs that your internet browser has been highjacked
There are many signs that could indicate a browser hijacking:
1. the home page of the web browser is changed suddenly
2. you observe new unwanted bookmarks or favorites added, usually directed to ad-filled or porn websites
3. the default search engine is changed and the web browser security settings have been brought down without your knowledge
4. you see unwanted new toolbars added
5. your internet browser will display constant pop-up windows
6. your web browser starts running sluggishly or presents frequent errors
7. Inability to navigate to particular sites, especially anti-malware and other computer security software websites.
So how does a computer get infected with a browser hijacker
There are a number of ways your computer can get infected by a browser hijacker. They usually arrive through spam e-mail, via file sharing websites, or by a drive-by-download. They could also come from add-on software, also referred to as browser helper objects (BHO), web browser extensions, or toolbars. Browser hijackers sneak to your computer in addition to free software application downloads that you unintentionally install along with the original.
The presence of any browser hijacker on your system could substantially diminish the web browsing experience, monitor your internet activities that lead to critical privacy concerns, create system stability problems and finally cause your PC to slow down or to a practically unusable condition.
How to repair a browser hijack
Certain kinds of browser hijackers can be effortlessly removed from your PC by deleting malicious software programs or any other recently installed shareware. However, most hijacking codes are certainly not very easy to remove manually, as they go deeper into your operating system. And there’s no denying the very fact that manual repairs and removal methods can certainly be a difficult job for an inexperienced PC user. Besides, there are several risks connected with fiddling around with the system registry files.
Anti-malware program is incredibly effective when it comes to discovering and removing browser hijackers that regular anti-virus application has missed. To get rid of any kind of browser hijacker from your computer, you can download the following certified malware removal application – SafeBytes Anti-Malware.
What you can do if Virus Stops You From Downloading Antivirus?
Practically all malware is bad, but certain kinds of malicious software do much more damage to your PC than others. Some malware goes to great lengths to stop you from downloading or installing anything on your personal computer, especially anti-malware software. If you are reading this right now, you’ve probably realized that virus infection is the reason behind your blocked net traffic. So what to do when you want to install an anti-malware application such as Safebytes? There are a few actions you can take to circumvent this issue.
Make use of Safe Mode to fix the issue
If the malware is set to run automatically when Windows starts, getting into safe mode may block this attempt. Since only the bare minimum programs and services start-up in “Safe Mode”, there are rarely any reasons for conflicts to happen. You will need to do the following to remove malware in Safe mode.
1) At power on/start-up, tap the F8 key in one-second intervals. This will bring up the Advanced Boot Options menu.
2) Use the arrow keys to choose Safe Mode with Networking and press ENTER.
3) When you are into this mode, you will have access to the internet again. Now, use your internet browser normally and navigate to https://safebytes.com/products/anti-malware/ to download Safebytes Anti-Malware.
4) Once the software is installed, let the diagnostic scan run to remove viruses and other threats automatically.
Obtain the antivirus software in an alternate browser
Certain viruses may target vulnerabilities of a particular web browser that obstruct the downloading process. If you seem to have a virus attached to Internet Explorer, then switch to an alternate browser with built-in safety features, such as Firefox or Chrome, to download your favorite antivirus program – Safebytes.
Run anti-virus from a pen drive
Here’s yet another solution which is using a portable USB anti-malware software package that can scan your computer for viruses without needing installation. Follow these steps to run the anti-malware on the infected PC.
1) Make use of another virus-free computer to download Safebytes Anti-Malware.
2) Plug the Flash drive into the uninfected computer.
3) Double-click on the downloaded file to run the installation wizard.
4) Choose the drive letter of the USB drive as the location when the wizard asks you exactly where you want to install the anti-virus. Follow activation instructions.
5) Now, insert the USB drive into the infected system.
6) Double click the Safebytes Anti-malware icon on the thumb drive to run the software.
7) Click on “Scan Now” to run a complete scan on the infected computer for malware.
Let's Talk About SafeBytes Anti-Malware!
Nowadays, anti-malware software can protect your PC from different forms of internet threats. But wait, how to select the right one among plenty of malware protection application that is available on the market? As you may be aware, there are numerous anti-malware companies and tools for you to consider. Some of them are good, some are ok types, while some will affect your computer themselves! When looking for an antivirus program, select one which gives solid, efficient, and full protection against all known computer viruses and malware. On the list of the recommended tool by industry experts is SafeBytes Anti-Malware, well-known security software for Microsoft Windows.
SafeBytes anti-malware is really a powerful, highly effective protection software intended to help end-users of all levels of IT literacy in identifying and removing malicious threats from their computers. Once you have installed this tool, SafeBytes advanced protection system will ensure that absolutely no viruses or malware can seep through your personal computer.
SafeBytes possesses a plethora of amazing features that can help you protect your computer from malware attacks and damage. The following are some of the great features included in the application.
Real-time Active Protection: SafeBytes offers a totally hands-free active protection and is set to observe, prevent and wipe out all threats at its first encounter. It’ll constantly monitor your pc for hacker activity and also gives users superior firewall protection.
Anti-Malware Protection: Using its advanced and sophisticated algorithm, this malware removal tool can detect and remove the malware threats hiding in your PC effectively.
High-Speed Malware Scanning Engine: This computer software has got one of the fastest and most efficient virus scanning engines in the industry. The scans are extremely accurate and take a short amount of time to complete.
Web Security: SafeBytes gives an instant safety rating on the pages you are about to check out, automatically blocking risky sites and making sure that you’re certain of your online safety while browsing the web.
Lowest Memory/CPU Usage: SafeBytes gives you complete protection from online threats at a fraction of the CPU load due to its enhanced detection engine and algorithms.
Fantastic Tech Support Team: For any technical inquiries or product guidance, you could get 24/7 expert assistance through chat and email.
SafeBytes will keep your personal computer protected from most advanced malware threats automatically, thus keeping your online experience safe and secure. You now may know that this particular software does more than just scan and delete threats on your computer. If you want advanced forms of protection features and threat detections, buying SafeBytes Anti-Malware could be well worth the dollars!
Technical Details and Manual Removal (Advanced Users)
To remove Email Access Online manually, navigate to the Add/Remove programs list in the Windows Control Panel and choose the program you want to remove. For browser plug-ins, go to your browser’s Addon/Extension manager and choose the plug-in you want to remove or disable. You will probably also want to reset your internet browser.
To make sure of complete removal, find the following Windows registry entries on your system and eliminate it or reset the values accordingly. However, this is a difficult task and only computer professionals can perform it safely. Additionally, certain malware is capable of replicating itself or preventing deletion. You’re suggested to do this process in Windows Safe Mode.



 1. File-infecting Virus
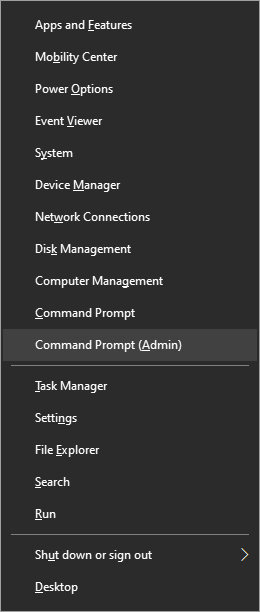
1. File-infecting Virus From the menu choose command prompt (admin)
From the menu choose command prompt (admin)
 In command prompt type sfc /scannow and press ENTER
Leave the computer for the operation to be completed and Reboot your computer
In command prompt type sfc /scannow and press ENTER
Leave the computer for the operation to be completed and Reboot your computer