FormFetcherPro.com is a Browser Extension for Google Chrome developed by Mindspark Inc. This extension offers users quick and easy access to various forms required for visas and other documents. While this may seem appealing, all this extension does is point you to the most popular websites online that can easily be found by searching.
When installed it hijacks your new tab page and changes it to search.myway.com, enabling it to better target ads.
While browsing the internet with this extension enabled you will see additional sponsored content, additional ads, and sometimes even pop-up ads displaying throughout your browsing sessions.
Several anti-virus programs have marked this extension as Potentially Unwanted and as a Browser Hijacker and are therefore recommended to remove it from your computer.
About Browser Hijackers
Browser hijacking means a malicious code has taken control over and altered the settings of your web browser, without your permission. Browser hijackers are capable of doing more than just changing home pages. Usually, hijackers will force hits to internet sites of their preference either to increase targeted traffic generating higher ad earnings, or to obtain a commission for every user visiting there. Many people believe that these types of sites are legitimate and harmless but that is incorrect. Nearly all browser hijackers pose an actual threat to your online safety and it is necessary to classify them under privacy dangers. Browser hijackers can even let other destructive programs without your knowledge further damage your computer.
Key signs that your web browser has been highjacked
When your web browser is hijacked, the following could happen: you find unauthorized changes to your web browser’s home page; your internet browser is constantly being redirected to adult sites; the default browser configurations have been changed, and/or your default search engine is altered; you see many toolbars on your internet browser; you’ll find random pop-ups start showing regularly; your web browser starts running slowly or exhibits frequent errors; Inability to navigate to certain sites, especially antivirus and other security software websites.
How it infects the computer
Browser hijackers can enter a PC in some way or other, for example via file sharing, downloads, and email as well. They sometimes are included with toolbars, add-ons, BHO, plugins, or browser extensions. Browser hijackers sneak into your pc in addition to free software application downloads also that you unwittingly install alongside the original. Common examples of browser hijackers include CoolWebSearch, Conduit, RocketTab, OneWebSearch, Coupon Server, Delta Search, Searchult.com, and Snap.do.
How you can fix a browser hijack
Some types of browser hijackers can be removed from the computer by uninstalling malicious software or any other recently added shareware. Having said that, the majority of hijackers are really tenacious and require specialized applications to eliminate them. Also, browser hijackers might modify the Windows registry so that it can be very tough to restore all the values manually, particularly when you are not a very tech-savvy individual.
Anti-malware software is very efficient when it comes to catching and removing browser hijackers that regular anti-virus software has missed. SafeBytes Anti-Malware will counter relentless browser hijackers and provide you active PC protection against all types of malware. Utilize a pc optimizer (such as Total System Care) together with your anti-malware to repair various registry issues, eliminate system vulnerabilities, and improve your computer performance.
How To Install Safebytes Anti-Malware On An Infected Computer system
Practically all malware is bad, but certain kinds of malware do more damage to your computer or laptop than others. Some malware sits in between your PC and your internet connection and blocks some or all sites that you would like to check out. It would also prevent you from the installation of anything on your PC, especially antivirus software. If you are reading this article right now, you’ve perhaps realized that a malware infection is a reason for your blocked internet traffic. So what to do if you want to install an anti-virus program like Safebytes? There are a few actions you can take to get around this issue.
Use Safe Mode to resolve the issue
In Safe Mode, you can modify Windows settings, un-install or install some software, and eradicate hard-to-delete malware. In case the malicious software is set to load automatically when the PC starts, shifting to this particular mode can prevent it from doing so. In order to get into Safe Mode or Safe Mode with Networking, press F8 while the system is booting up or run MSConfig and locate the “Safe Boot” options in the “Boot” tab. Once you restart the PC into Safe Mode with Networking, you could download, install, and update anti-malware software from there. Now, you are able to run the anti-virus scan to remove viruses and malware without interference from another malicious application.
Switch to a different internet browser
Some malware mainly targets certain web browsers. If this is your case, utilize another browser as it could circumvent the malware. If you suspect that your Internet Explorer has been hijacked by a trojan or otherwise compromised by cybercriminals, the best course of action would be to switch over to a different internet browser like Google Chrome, Mozilla Firefox, or Apple Safari to download your chosen security program – Safebytes Anti-Malware.
Make a bootable USB anti-virus drive
Another approach is to download and transfer an anti-malware application from a clean computer to run a scan on the affected computer. To run anti-virus from a USB pen drive, follow these simple steps:
1) Use another virus-free PC to download Safebytes Anti-Malware.
2) Mount the pen drive on the same computer.
3) Double-click on the downloaded file to open the installation wizard.
4) When asked, select the location of the pen drive as the place in which you would like to store the software files. Do as instructed on the screen to finish off the installation process.
5) Unplug the flash drive. Now you can use this portable anti-virus on the infected computer.
6) Double-click the EXE file to open the Safebytes tool right from the thumb drive.
7) Click on “Scan Now” to run a complete scan on the affected computer for viruses.
SafeBytes Anti-Malware Overview
If you are planning to buy anti-malware for your PC, there are many brands and utilities for you to consider. Some are very good ones, some are ok types, while some are simply just fake anti-malware software that can harm your personal computer themselves! When looking for anti-malware software, select one that gives reliable, efficient, and comprehensive protection against all known computer viruses and malware. On the list of strongly recommended software by industry, analysts are SafeBytes Anti-Malware, popular security software for Microsoft Windows.
SafeBytes anti-malware is a powerful, highly effective protection software designed to help end-users of all levels of computer literacy in finding and removing harmful threats out of their computer. When you have installed this program, SafeByte's state-of-the-art protection system will ensure that no viruses or malware can seep through your PC.
SafeBytes has outstanding features when compared with other anti-malware programs. Listed below are some of the features you will like in SafeBytes.
Most effective AntiMalware Protection: This deep-cleaning antimalware program goes much deeper than most antivirus tools to clean your personal computer. Its critically acclaimed virus engine detects and disables hard to remove malware that hides deep inside your PC.
Real-time Active Protection: SafeBytes provides complete and real-time security for your personal machine. This tool will continuously keep track of your computer for any suspicious activity and updates itself continuously to keep current with the constantly changing threat scenarios.
Internet Security: Through its unique safety score, SafeBytes tells you whether a website is safe or not to visit it. This will ensure that you’re always certain of your safety when browsing the internet.
Minimal CPU and RAM Usage: This application is not “heavy” on your computer’s resources, so you’ll not find any performance troubles when SafeBytes is working in the background.
Premium Support: For any technical inquiries or product guidance, you may get 24/7 professional assistance through chat and email.
SafeBytes can keep your computer protected from the latest malware threats automatically, thereby keeping your web experience safe and secure. Malware trouble can become a thing of the past once you put this tool to use. So if you’re searching for the best malware removal tool out there, and when you don’t mind spending some money for it, go for SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
To get rid of FormFetcherPro manually, go to the Add/Remove programs list in the Control Panel and select the program you want to get rid of. For browser plug-ins, go to your browser’s Addon/Extension manager and select the add-on you intend to disable or remove. You will most probably also want to reset your web browser to its default settings.
To make sure of complete removal, find the following registry entries on your computer and delete it or reset the values accordingly. However, this is a tough task and only computer professionals can carry it out safely. In addition, some malware is capable of replicating or preventing removal. Carrying out this in Safe Mode is recommended.

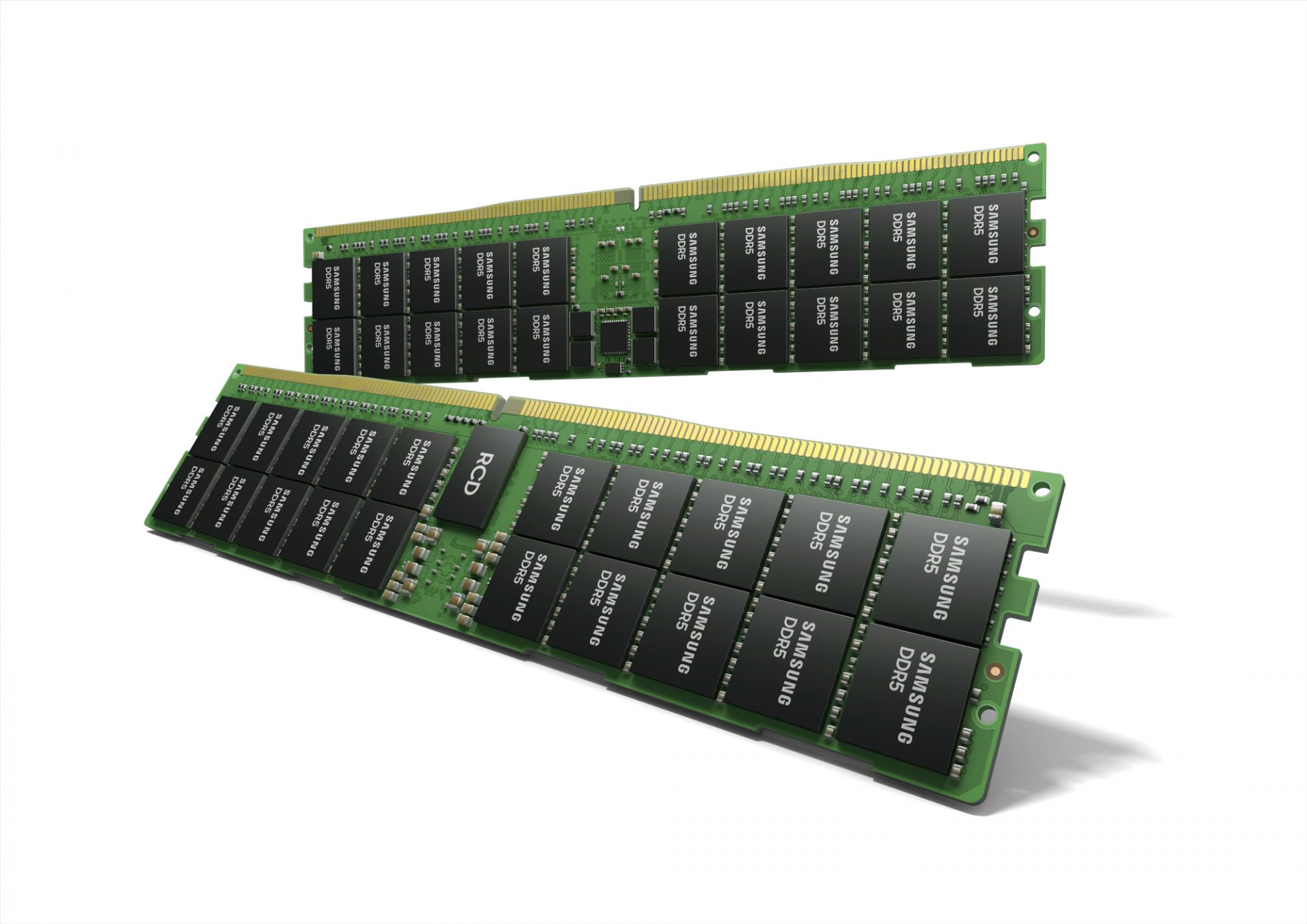 Next-generation of RAM, DDR5 supposed to hit shelves around late summer or fall in 2021if everything goes as planned.
Its goal is to increase speed and efficiency, wants to pack more memory in a single stick, and have better power management.
Next-generation of RAM, DDR5 supposed to hit shelves around late summer or fall in 2021if everything goes as planned.
Its goal is to increase speed and efficiency, wants to pack more memory in a single stick, and have better power management.