FoxTab Toolbar is a browser hijacking toolbar add-on for IE, Firefox, Chrome, and Opera browsers that claims that it allows you to access your favorite sites faster, and improving your overall search and browsing experience. 1-click access to search results, most popular websites, and web services directly from our Foxtab browser toolbar.
Fox tab will integrate itself into your browser, modifying the search engine, welcome page, and new tab. This toolbar may change some browser settings, display unwanted ads, and sometimes displays additional ads from its ad sponsor. Some of the settings that this toolbar changes can lower the security of your browser.
Upon installation the toolbar ads scheduled tasks in Windows, allowing it to run with your browser every time, and to automatically update itself. Several anti-virus programs have flagged this software as Malware and therefore it is classified as a browser hijacker and recommended for optional removal.
About Browser Hijackers
Browser hijackers (sometimes called hijackware) are a type of malicious software that modifies internet browser settings without the user’s knowledge or approval. These types of hijacks are rising at an astonishing rate across the world, and they can be actually nefarious and sometimes dangerous too. They are created to interfere with web browser programs for many different reasons. Often, hijackers will force hits to internet sites of their choice either to increase targeted traffic generating higher ad revenue, or to gain a commission for every user visiting there. Although it might appear harmless, these tools are made by malicious people who always try to take full advantage of you, so that hackers can earn money from your naivety and distraction. What’s more, hijackers can make the whole infected system fragile – other destructive malware and viruses will take hold of these opportunities to get into your computer system effortlessly.
How to know whether the browser is hijacked?
Symptoms that your internet browser is hijacked include:
1. your home page has been reset to some unknown webpage
2. bookmark and the new tab are also changed
3. default web engine is changed
4. you see unwanted new toolbars added
5. you’ll notice random pop-ups start showing regularly
6. your web browser starts running sluggishly or exhibits frequent glitches
7. Inability to navigate to particular sites, particularly anti-malware as well as other computer security software webpages.
How it infects your PC
Browser hijackers infect PCs in numerous ways, including via a file-share, a drive-by download, or an infected email. They can also be deployed via the installation of an internet browser toolbar, extension, or add-on. Also, certain shareware and freeware can put the hijacker in your PC through “bundling”.
Browser hijackers can record user keystrokes to collect potentially invaluable information that leads to privacy issues, cause instability on systems, drastically disrupt the user experience, and ultimately slow down the PC to a point where it becomes unusable.
Tips on how to get rid of browser hijackers
Certain kinds of browser hijackers can be removed from your computer by deleting malicious applications or any other recently added freeware. Often, it can be a tough task to find and eliminate the malicious component because the associated file might be running as part of the operating system process. Also, manual removals require in-depth system understanding and thus can be a very difficult task for beginner computer users.
Professionals always suggest users remove any malicious software including browser hijacker by using an automatic removal tool, which is easier, safer, and quicker than the manual removal process. Safebytes Anti-Malware detects all kinds of hijackers – including FoxTab – and eliminates every trace efficiently and quickly. Employ a pc optimizer along with your antivirus software to solve various computer registry problems, eliminate system vulnerabilities, and boost your computer performance.
Malware Blocking Access To Safebytes Website And Anti-Malware Downloads - What You Should Do?
Malware may cause many different types of damage to computer systems, networks, and data. Some malware is meant to interfere with or prevent things that you wish to do on your PC. It may well not permit you to download anything from the internet or prevent you from accessing some or all of the sites, particularly the anti-malware sites. If you’re reading this, you may have affected by a virus that stops you from downloading a computer security program like Safebytes Anti-Malware. There are a few steps you can take to get around this problem.
Download the software in Safe Mode with Networking
If any virus is set to load automatically when Microsoft Windows starts, getting into Safe Mode could very well block the attempt. Just the minimum required programs and services are loaded when you start your PC in Safe Mode. To start your Windows XP, Vista, or 7 computers in Safe Mode with Networking, please do as instructed below.
1) Tap the F8 key repeatedly as soon as your system boots, but before the large windows logo comes up. This would conjure up the Advanced Boot Options menu.
2) Choose Safe Mode with Networking using arrow keys and hit ENTER.
3) When this mode loads, you will have the internet. Now, get the virus removal software you want by utilizing the internet browser. To install the software, follow the guidelines within the setup wizard.
4) Immediately after installation, do a complete scan and let the program remove the threats it finds.
Download the antivirus program in a different web browser
Some malware mainly targets particular browsers. If this is your situation, employ another web browser as it could circumvent the computer virus. In the event you suspect that your Internet Explorer has been hijacked by malware or otherwise compromised by online hackers, the ideal course of action would be to switch over to a different browser like Chrome, Firefox, or Safari to download your favorite computer security application – Safebytes Anti-Malware.
Create a bootable USB anti-virus drive
Another option is to make a portable anti-malware program onto your USB flash drive. Try these simple measures to clean up your infected PC using a portable antivirus.
1) Make use of another virus-free computer to download Safebytes Anti-Malware.
2) Insert the pen drive into the clean PC.
3) Double-click the Setup icon of the antivirus software to run the Installation Wizard.
4) When asked, choose the location of the USB drive as the place in which you would like to store the software files. Follow the on-screen instructions to finish the installation.
5) Disconnect the USB drive. You may now utilize this portable anti-virus on the affected computer system.
6) Run the Safebytes Anti-malware directly from the thumb drive by double-clicking the icon.
7) Hit the “Scan Now” button to start the malware scan.
Protect Your PC and Privacy With SafeBytes Anti-Malware
Do you want to install the best anti-malware software for your computer? There are plenty of applications on the market that comes in free and paid versions for Windows computers. Some are very good ones, some are decent, and some are simply just bogus anti-malware software that will damage your PC themselves! You need to be very careful not to pick the wrong product, particularly if you buy a paid application. On the list of recommended software programs is SafeBytes AntiMalware. SafeBytes has a very good reputation for excellent service, and clients seem to be happy with it.
SafeBytes anti-malware is a trusted tool that not only protects your computer system permanently but is also quite easy to use for people of all skill levels. After you have installed this application, SafeBytes' superior protection system will make sure that absolutely no viruses or malware can seep through your computer.
SafeBytes has great features when compared with other anti-malware programs. Below are some of the great features included in the application.
Active Protection: SafeBytes offers real-time active monitoring service and protection against all known viruses and malware. It’ll monitor your computer system for suspicious activity regularly and its unparalleled firewall guards your PC against illegal access by the outside world.
World-class AntiMalware Protection: Built on a highly acclaimed anti-virus engine, this malware removal tool is able to detect and remove numerous obstinate malware threats such as browser hijackers, potentially unwanted programs, and ransomware that other common antivirus software will miss.
Safe Browsing: SafeBytes checks and provides a unique safety rating to every single site you visit and block access to web pages known to be phishing sites, thus protecting you from identity theft, or known to contain malicious software.
Low Memory/CPU Usage: This software is lightweight and will run quietly in the background, and that does not have an effect on your PC efficiency.
24/7 Online Technical Support: SafeBytes provides you with 24/7 technical support, automatic maintenance, and updates for the best user experience.
Overall, SafeBytes Anti-Malware is a solid program since it has plenty of features and can detect and remove any potential threats. There is no doubt that your computer will be protected in real-time as soon as you put this software program to use. If you’re looking for the absolute best malware removal tool out there, and if you don’t mind shelling out some money for it, go for SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove FoxTab without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by FoxTab
[/section][/vc_column_text][/vc_column][/vc_row][/vc_section]
 Skinning of applications is not new to PC users, but did you knew you could skin Steam?
With skin, you can customize the UI and style of the client to what you want making it more personal and to your liking. First thing is to find the skin that you would like to install. There are a lot of sites where you could find custom made Steam skins but we would recommend steamskins.org
The site itself is organized in tabs with different sections, once you click on the tab you will get a list of skins available for chosen section. If you click on the skin you will be taken to skin page detail where you can find what skin is aiming for, its legibility, a record of how the skin has been altered over time, or some mix of these aspects.
Note that some skins might have issues like some buttons might be missing from big picture mode but so far none of the skins has any kind of client breaking feature, only functionality one.
Skinning of applications is not new to PC users, but did you knew you could skin Steam?
With skin, you can customize the UI and style of the client to what you want making it more personal and to your liking. First thing is to find the skin that you would like to install. There are a lot of sites where you could find custom made Steam skins but we would recommend steamskins.org
The site itself is organized in tabs with different sections, once you click on the tab you will get a list of skins available for chosen section. If you click on the skin you will be taken to skin page detail where you can find what skin is aiming for, its legibility, a record of how the skin has been altered over time, or some mix of these aspects.
Note that some skins might have issues like some buttons might be missing from big picture mode but so far none of the skins has any kind of client breaking feature, only functionality one.


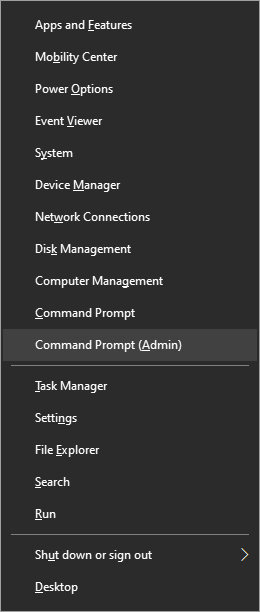
 From the menu choose command prompt (admin)
From the menu choose command prompt (admin)
 In command prompt type sfc /scannow and press ENTER
Leave the computer for the operation to be completed and Reboot your computer
In command prompt type sfc /scannow and press ENTER
Leave the computer for the operation to be completed and Reboot your computer