What is Babylon?
Babylon is a self-published computer dictionary and translation program. Babylon is a tool used for translation and conversion of currencies, measurements, and time, and for obtaining other contextual information. The program also uses a text-to-speech agent so users hear the proper pronunciation of words and text.
Babylon’s translation software adds the Babylon toolbar identified as a browser hijacker. This toolbar may modify the homepage of the browser. It adds a Scheduled Task, Startup file, and Registry Keys that allow it to run at any time. A Windows Firewall exception is also added for the software, allowing it to connect to the internet without content.
About Browser Hijackers
Browser hijacking is actually a type of unwanted software program, commonly a browser add-on or extension, which causes modifications in browser settings. Browser hijackers will do a number of things on your computer. Often, hijackers will force hits to internet sites of their choice either to increase targeted traffic generating higher ad revenue, or to obtain a commission for each and every user visiting there. It could seem harmless, but the majority of these websites aren’t legitimate and can present a significant risk to your online safety. Additionally, hijackers can make the entire infected system fragile – other harmful malware and viruses will take hold of these opportunities to get into your PC effortlessly.
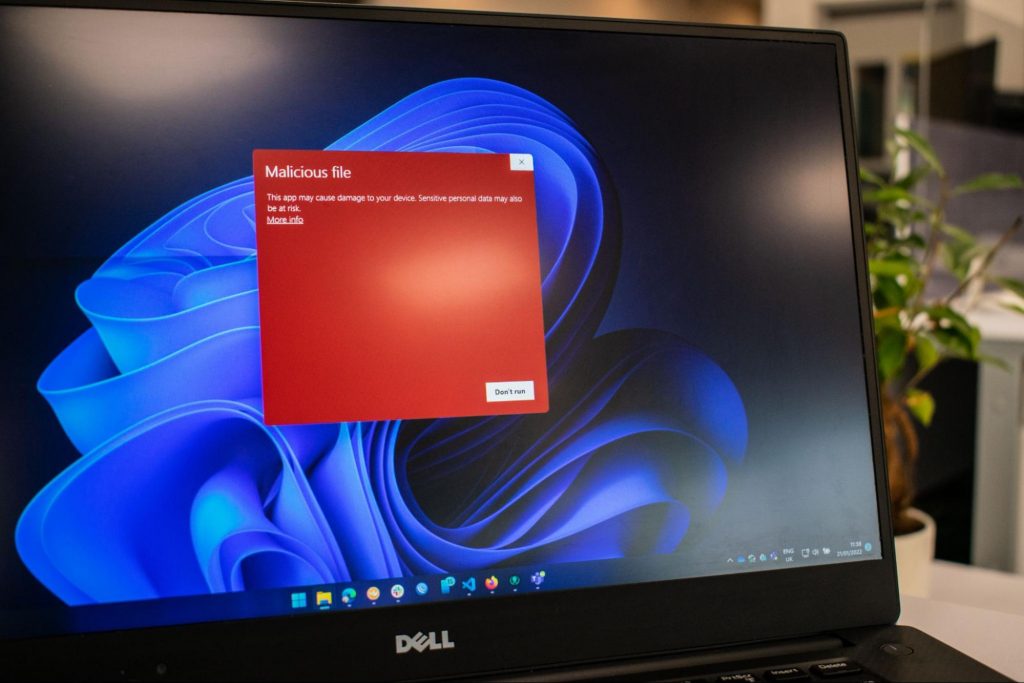
Signs of browser hijacker malware
There are several symptoms of browser hijacking. Here are a few of them: the home page of your browser is changed all of a sudden; new bookmarks pointing to porn websites are added to your favorite pages; the default browser settings have been modified and/or your default search engine is altered; unsolicited new toolbars are added to your internet browser; you notice a lot of pop-ups on your computer screen; your web browser gets sluggish, buggy, crashes frequently; you cannot go to certain sites such as homepages of anti-malware software.
How it infects your computer
Browser hijackers may use drive-by downloads or file-sharing networks or perhaps an email attachment in order to reach a targeted computer system. They may also originate from any BHO, browser extension, toolbar, add-on, or plug-in with malicious intent. Sometimes you might have accidentally accepted a browser hijacker as part of a software bundle (usually freeware or shareware). Examples of well-known browser hijackers include Fireball, GoSave, Ask Toolbar, CoolWebSearch, Babylon Toolbar, and RocketTab.
The existence of any browser hijacker on your system will considerably diminish the browsing experience, monitor your online activities that lead to troublesome privacy issues, produce system stability issues and finally cause your PC to slow down or to a nearly unusable state.
Browser hijacker removal tips
Some hijackers can be easily removed by deleting the free software they were included with or by eliminating any add-ons you’ve recently added to your computer system. Sadly, most of the software packages used to hijack a web browser are intentionally designed to be hard to eliminate or detect. And there’s no denying the fact that manual fixes and removal can be quite a difficult task for an inexperienced PC user. Besides, there are numerous risks associated with fiddling around with the pc registry files.
Anti-malware application is extremely efficient when it comes to picking up and eliminating browser hijackers that regular anti-virus program has overlooked. To get rid of any kind of browser hijacker from your PC, you could download this top-notch malware removal tool – Safebytes Anti-Malware.
What To Do If You Cannot Install Safebytes Anti-Malware?
Practically all malware is inherently unsafe, but certain types of malicious software do much more damage to your computer than others. Certain malware types alter browser settings by adding a proxy server or modify the PC’s DNS configurations. In such cases, you will be unable to visit some or all websites, and thus unable to download or install the required security software to clear out the infection. So what you should do if malware prevents you from downloading or installing Anti-Malware? Even though this sort of problem can be tougher to get around, there are some actions you can take.
Boot Windows in Safe Mode
If the malware is set to run at Windows start-up, then booting in Safe Mode should prevent it. Just the minimum required applications and services are loaded when you start your laptop or computer into Safe Mode. To launch your Windows XP, Vista, or 7 computers in Safe Mode with Networking, follow the instructions below.
1) After switching on the computer, hit the F8 key before the Windows splash screen begins to load. This should bring up the Advanced Boot Options menu.
2) Use the arrow keys to select Safe Mode with Networking and press ENTER.
3) Once this mode loads, you should have the internet. Now, make use of your internet browser normally and navigate to https://safebytes.com/products/anti-malware/ to download Safebytes Anti-Malware.
4) Immediately after installation, do a full scan and allow the software to delete the threats it detects.
Obtain the antivirus software using a different browser
Certain malware may target vulnerabilities of a particular browser that obstruct the downloading process. The best way to overcome this problem is to opt for a web browser that is well known for its security measures. Firefox comprises built-in Phishing and Malware Protection to help keep you secure online.
Install security software on a flash drive
Another option is to store and run an antivirus program completely from a Thumb drive. Try these simple actions to clear up your affected computer using a portable antivirus.
1) Use another virus-free computer to download Safebytes Anti-Malware.
2) Mount the USB drive onto the same PC.
3) Double-click the exe file to run the installation wizard.
4) When asked, choose the location of the pen drive as the place in which you would like to store the software files. Do as instructed on the screen to finish up the installation process.
5) Remove the flash drive. You may now utilize this portable anti-malware on the infected computer.
6) Double-click the antivirus software EXE file on the pen drive.
7) Press the “Scan Now” button to start the virus scan.
If all the previously mentioned methods are not able to help you in downloading and installing the anti-malware, then you have no option but to reinstall the computer’s operating system to wipe out all of the data, including the harmful programs which are obstructing the anti-malware installation. If you are unclear regarding which method works best for you, simply call 1-844-377-4107 to speak to our computer professionals who can walk you through the process to fix your infected computer system.
SafeBytes AntiMalware Overview
Today an anti-malware program can protect your PC from different kinds of internet threats. But how to decide on the best one among countless malware protection application that is available in the market? You may be aware, there are several anti-malware companies and products for you to consider. A few of them do a good job in eradicating malware threats while many will harm your computer themselves. While looking for an anti-malware program, pick one which provides dependable, efficient, and total protection against all known computer viruses and malware. With regards to commercial application options, many people select popular brands, like SafeBytes, and they are quite happy with it.
Safebytes is among the well-established computer solutions firms, which offer this all-inclusive anti-malware program. When you have installed this software, SafeBytes' sophisticated protection system will make sure that no viruses or malware can seep through your PC.
SafeBytes anti-malware provides a myriad of enhanced features which set it apart from all others. The following are some of the great features included in the tool.
Optimum AntiMalware Protection: With its enhanced and sophisticated algorithm, this malware removal tool can detect and remove the malware threats hiding within your computer system effectively.
Real-time Active Protection: SafeBytes offers entirely hands-free real-time protection and is set to monitor, block, and destroy all computer threats at its very first encounter. They’re highly efficient in screening and getting rid of numerous threats because they’re regularly revised with new updates and safety measures.
Web Filtering: Through its unique safety score, SafeBytes notifies you whether a site is safe or not to visit it. This will ensure that you’re always certain of your online safety when browsing the world wide web.
Light-weight: This program is not “heavy” on the computer’s resources, so you’ll not notice any performance difficulties when SafeBytes is operating in the background.
24/7 Guidance: You can obtain totally free 24/7 technical assistance from their IT experts on any product queries or PC security concerns.
SafeBytes has put together an excellent anti-malware solution to help you conquer the latest computer threats and virus attacks. There is no doubt that your computer system will be protected in real-time as soon as you put this software to use. So if you’re trying to find a comprehensive antivirus program that’s still easy to use, SafeBytes Anti-Malware is exactly what you need!
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove Babylon without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by Babylon


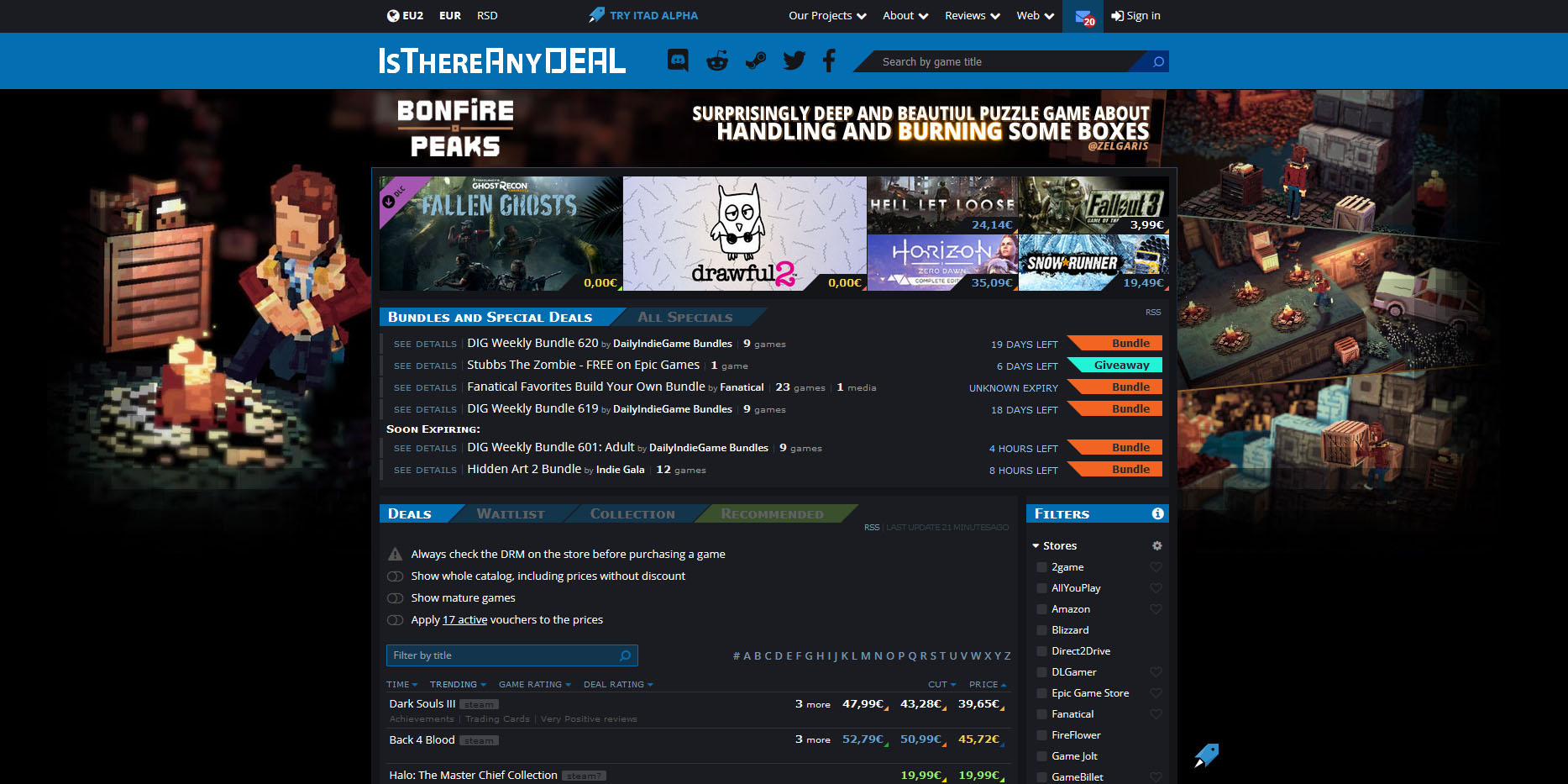 Is There Any Deal
Is There Any Deal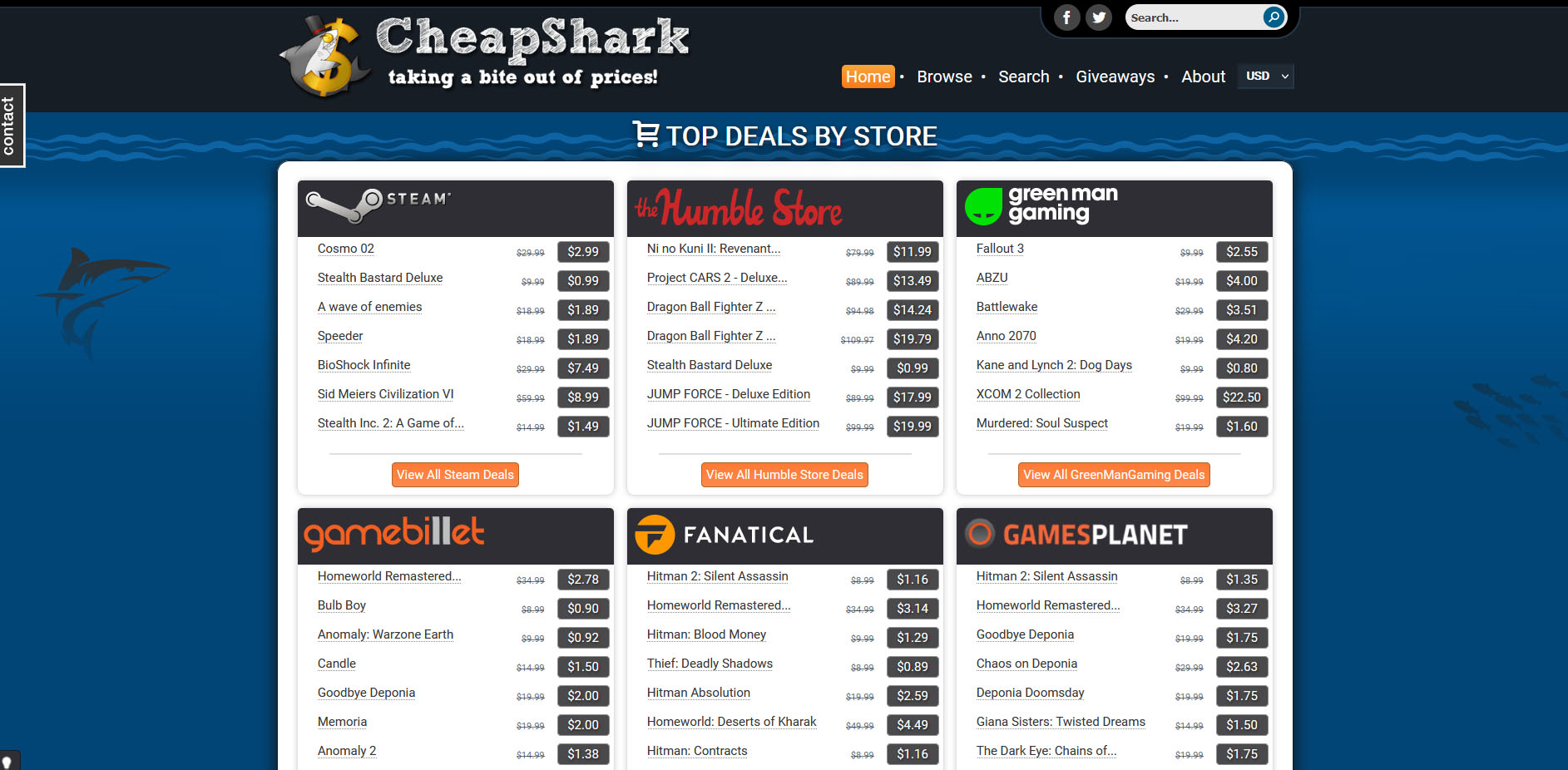 Cheap Shark
Cheap Shark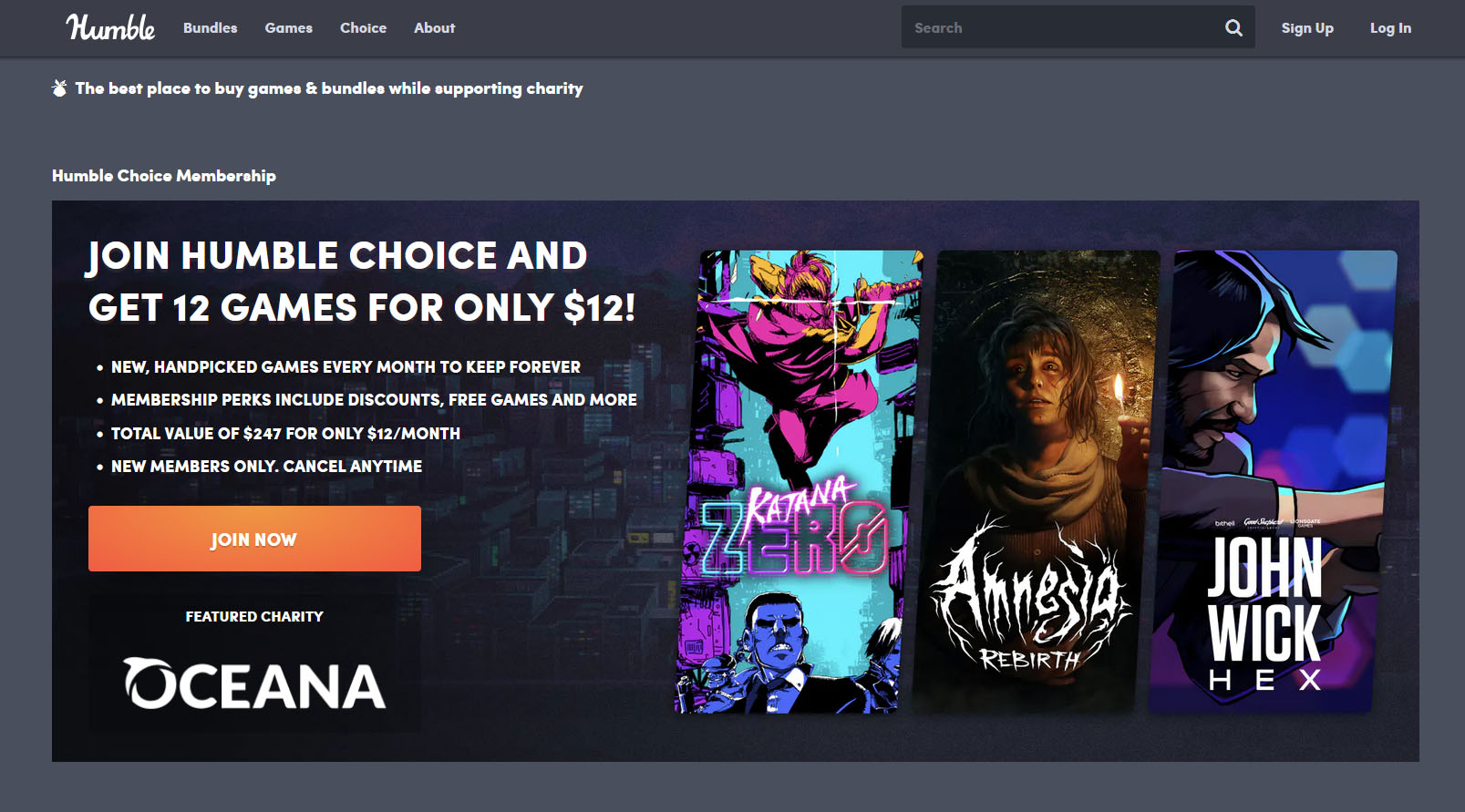 Humble Bundle
Humble Bundle Fanatical
Fanatical Slick Deals
Slick Deals Green Man Gaming
Green Man Gaming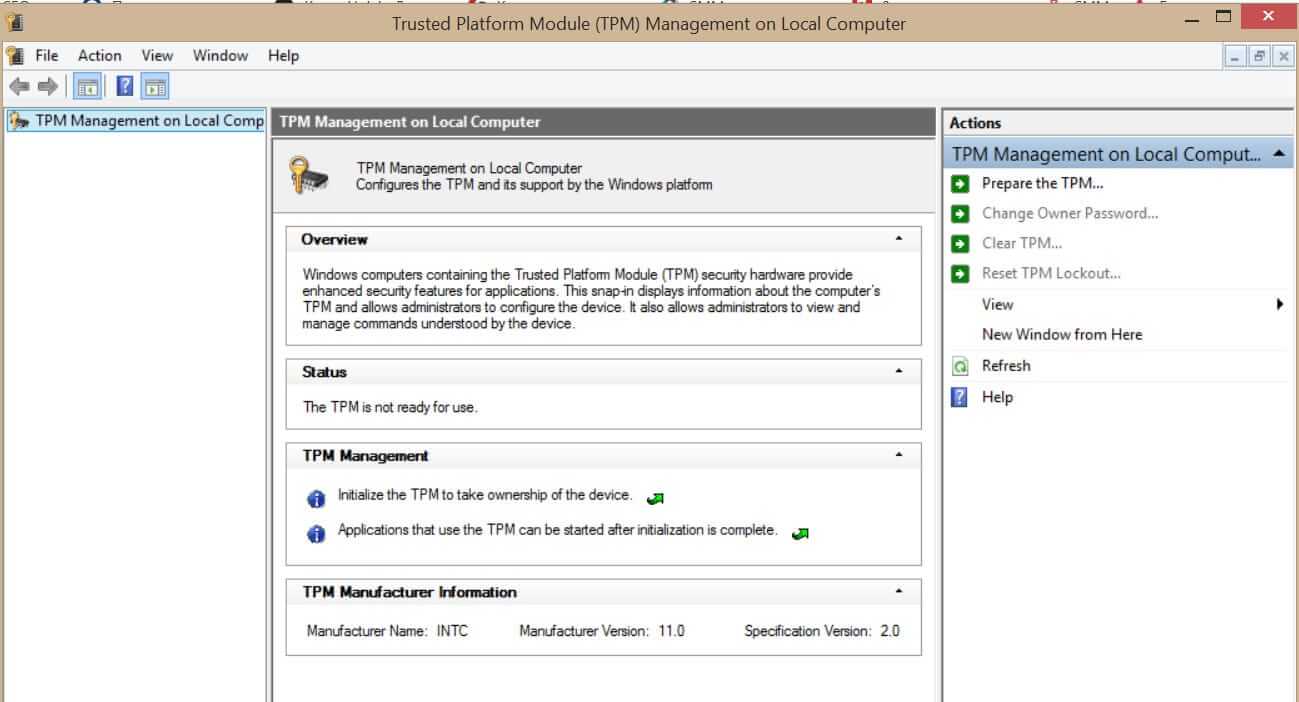 What exactly is TPM?
What exactly is TPM?