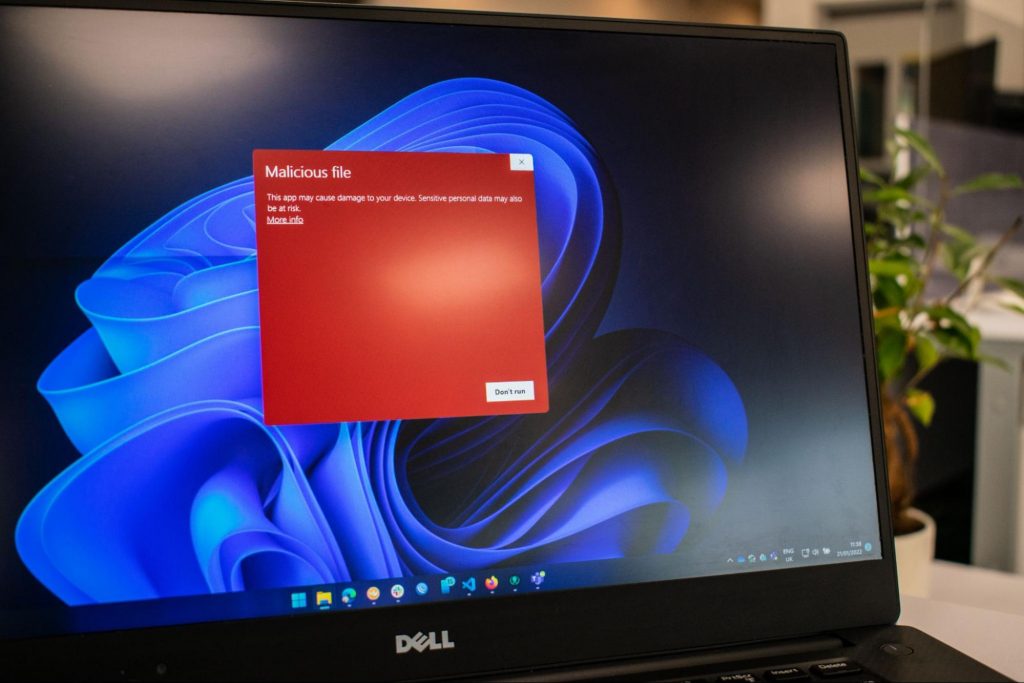
Afraid of the growing threats online? As you should be. But we’re here to show you what kinds of malware are out there and what you can do to keep them at bay.
Malware comes from the term malicious software. It’s software designed to attack and exploit devices and networks to the advantage of the hacker who made it.
Malware can be transmitted in different ways. Most commonly this happens via infected USB drives, downloadable files or malicious websites. Depending on the type and ultimate goal, the consequences of a malware attack can range from negligible to catastrophic.
A virus is typically spread via infected files, websites or links. It’s one of the oldest malware types and one of the most difficult to get rid of. That’s because, once activated, it replicates itself - hence the name.
It can perform different kinds of attacks, depending on what the creator wants to achieve. The main characteristic of a virus is that it really doesn’t show itself until you activate the host. So that’s a scary thought for sure.
Sometimes an ad blocker isn’t enough to fight off unwanted ads. And some of them can, unfortunately, be malicious. They may redirect you to infected sites or prompt downloads of risky files. Even just opening a malicious site can lead to data theft.
So, definitely be careful when clicking around. Even if an ad seems completely legitimate, you can never be too sure.
Through ransomware, cybercriminals gain access to a user’s data and use it to extort them for money. Basically, the user is threatened with data deletion or even exposure if a ransom isn’t paid by a specific deadline.
This is a particularly nerve-wracking type of malware. If it targets an individual, it preys upon their sense of anxiety, fear, guilt and even shame. If it targets a business (which is a lot more common), it preys upon not only that business’s profit but also every single one of their customers and their data.
This type of malware disguises itself very well as a legitimate-looking program. Once you download it, hackers can get full access and control of your device, data and network. They can even be hidden in games, apps and attachments. They cannot self-replicate, though, so we guess that’s… good news?
Worms can replicate, just like viruses, but you don’t need to actually activate the infected program for them to get going. They can be used for various purposes, ranging from data deletion to file encryption to support a ransomware attack.

Spyware refers to malicious software that stays hidden on your computer and monitors your activity. The best-known type is keyloggers. This can be used to steal sensitive data like passwords and banking information.
Rootkits are among the most dangerous types of malware. They allow administrative access and full control of a device, which lets hackers continue hijacking all your data and monitoring your activity without your knowledge.
Botnets are networks made up of bots - computers that cybercriminals have infected with malicious software. Bots and botnets give hackers remote access to users’ devices and allow them to spy on your camera, take screenshots, memorize passwords and launch Distributed Denial of Service attacks. This one truly makes your hair stand on end.
You know the old adage - better safe than sorry. And trust us, malware attacks are such a pain in the you-know-what that you really don’t want to be sorry.
Luckily, there are simple solutions that can shield you from most digital threats these days. What you want to be looking at is a solid antivirus program. Well, technically, you need an antimalware program, but since the latter evolved from the former, we still mostly refer to them as antivirus software.
The majority of antimalware programs these days don’t just shield you from potential risks online, but include additional features as well. For example, some Bitdefender antivirus packages also include parental control and a VPN. And Bitdefender is not just for PCs either - it offers protection for your beloved iPhone or Android as well. You can throw in a password manager in there too, for an additional layer of security.

If you aren’t too concerned about all these various threats or feel like you don’t need extra security, you can at least take a step to protect your information from being exposed to lurking cybercriminals as you’re browsing. This can be done through a good VPN like Surfshark, which hides your identity in the digital space and prevents your data from being tracked.
Choosing the right protective software is especially important if you have children with access to the Internet, since they’re unfortunately even more vulnerable to malicious attacks. If you aren’t sure what the right kind of antimalware program is right for you, you can reach out to us and we’ll be happy to help keep your entire household or office digitally secure.
The truth is that there’s no way to be 100% protected in the online world. Hackers are constantly coming up with new ways to infiltrate our devices. But malware-battling software evolves along with them and there’s still plenty you can do to keep risks away. Stay safe!

There is a lot of software on the market today, but from time to time we discover something extraordinary and unique worth sharing and today we have a threat for you. Ventoy is a tool that will help you with system reinstallations and system maintenance once and for all.
If you are a computer user that has multiple operating systems or you are installing and maintaining different hardware via different OS there is a high chance that you have multiple USB sticks with different operating systems on them.
Now the problem with that is that there are probably too many unlabeled sticks around or you do not have enough so you keep making system USBs depending on which one you might need.

Ventoy solves all of these problems by letting you have as many operating systems images as your USB has capacity. The only thing you need to do is get the software here: https://www.ventoy.net/en/index.html and make a USB with it, then you can freely just copy your ISO images onto the USB and once it is inserted into the computer you will be given a menu to choose which one you would like to start with, simple as that.
“The boot configuration data store could not be opened”while you try to carry out any command on the bcedit.exe, then you’ve come to the right place as this post will guide you on how you can fix this error in Windows 10. This kind of error could pop up if the system is not able to locate the specified file. It is also possible that the requested system device can’t be found or that the boot configuration data store could not be opened. In addition, when you open the System Configuration or MSConfig, you might notice that there is no Boot data, and according to the reports, is that when you try to dual boot the computer, the installer will replace the default bootloader.
0xC1900101 – 0x20017, The installation failed in the SAFE_OS phase error during Replicate_OC operationTo fix this issue, you need to follow the given options below. But before you do, you need to create a System Restore point first so that if anything goes wrong, you can always undo the changes you’ve made.
dism /Mount-Image /ImageFile:H:sourcesboot.wim /index:1 /MountDir:C:UsersUserDesktopmount
C:UsersUserDesktopmountWindowsSystem32mcupdate_GenuineIntel.dll
dism /Unmount-Image /MountDir:C:UsersUserDesktopmount /commit
Stable Diffusion is a machine learning model developed by Stability AI to generate digital images from natural language descriptions. The model can be used for different tasks like generating image-to-image translations guided by text prompts and upscaling images.
Unlike competing models like DALL-E, Stable Diffusion is open source and does not artificially limit the images it produces. Stable diffusion was trained on a subset of the LAION-Aesthetics V2 data set. It can run on most consumer hardware equipped with a modest GPU and was hailed by PC World as "the next killer app for your PC".

Since Stable Diffusion is run locally and not in the cloud, as mentioned there is no limit to the number of images that you can produce but in order to use it you will have to get down a little dirty with setting your PC environment for it since it is not really an application, it is a command line text based descriptor that will use python to generate your images, so there is no install nor GUI.
In this guide, we will show you how to both install and run Stable Diffusion on your local PC so you can start producing some cool images all by yourself.
Make no mistake, Stable Diffusion will not run on a potato PC, in order to harvest the power of AI-generated imagery this is what you will need:
For this tutorial, we are covering the installation and running of Stable Diffusion on Windows PC. The steps presented here are presented in a way that installation can be performed on any operating system but precise instructions will be for Windows OS.
The first thing to do is to install GIT. It is a tool that will let you easily maintain and install repos from the internet. to install it go to: https://git-scm.com/ and click on download. Follow the instructions for your version of the operating system. If you are a developer you are familiar with GIT and if you already have it installed you can skip this step.
One thing that is important when installing GIT locally is to select to use it via the command line (the second option that says "Git from the command line and also from 3rd-party software").
Now when we have GIT installed, next thing is to use Miniconda3 to install python and all required libraries that are needed. Get the installer at: https://docs.conda.io/en/latest/miniconda.html
Miniconda3 is basically an easy installer so you do not have to install tons of stuff manually from different websites and sources, it is nicely packaged in the installer that will take care of everything.
After the previous two steps, we are ready now to actually install Stable Diffusion. Go to https://huggingface.co/CompVis/stable-diffusion#model-access and install the latest library (as of the writing of this article currently it is stable-diffusion-v1-4-original, the last one on the right), the library is almost 5GB in size so be prepared for big download.
After installing stable diffusion's latest library it is time to update it to the newest version. You can download ZIP from GIT HUB https://github.com/CompVis/stable-diffusion
Once downloaded click on the Windows start button and type in Miniconda3 and click on open. Create a folder and name it how you want on a drive of your choice. For this example, we will install it all in disk C under folder AI_art, follow the instructions below but use your own names and destination instead. Do not close Minicoda3 after typing commands!!!
cd c:/
mkdir AI_art
cd AI_art Extract GitHub files that you have downloaded into your new folder and get back to Minicoda3 and type the next commands:
cd C:\AI_art\stable-diffusion-main
conda env create -f environment.yaml
conda activate ldm
mkdir models\ldm\stable-diffusion-v1Let the whole process finish, some files are large and it might take a while. After the whole process is finished and completed, copy the checkpoint file that you have downloaded into: C:\AI_art\stable-diffusion-main\models\ldm\stable-diffusion-v1
After the file is copied rename it to model.ckpt and you are finished.
The created environment is needed in order to actually use Stable Diffusion to create images. Each time you want to use it you will have to run it, so go into Miniconda3, and inside it type:
conda activate ldm
cd C:\AI_art\stable-diffusion-mainafter we are inside the folder call the script with the parameters:
python scripts/txt2img.py --prompt "TXT DESCRIPTION OF IMAGE THAT YOU WANT TO CREATE" --plms --n_iter 5 --n_samples 1and that's it, your image is created and it is located in C:\AI_art\stable-diffusion-main\outputs\txt2img-samples\samples
 BigTech platforms Google and Facebook were hit with a series of antitrust lawsuits by the US federal government and states on charges they are operating monopolies and abusing their power.
Below is the status of the cases, as well as government probes of Apple and Amazon in their current states
BigTech platforms Google and Facebook were hit with a series of antitrust lawsuits by the US federal government and states on charges they are operating monopolies and abusing their power.
Below is the status of the cases, as well as government probes of Apple and Amazon in their current states
“The last product key you entered can’t be used on this copy of Windows (0xc03f6506).”This particular error tends to occur when you go on to activate Windows 10 although it can also appear during the upgrade process. In such cases, you will see the following error message:
“Unable to upgrade your edition, We can’t upgrade your edition of Windows. Try upgrading your edition of Windows again. (0xc03f6506).”To fix the Activation Error Code 0xc03f6506 in Windows 10, use the options provided below as references but before you proceed, make sure that you create a System Restore point first.
setup.exe /auto upgrade /pkey <YOUR WINDOWS 10 PRO EDITION PRODUCT KEY>After entering the command, check if it was able to fix the Windows Upgrade or Activation error 0xc03f6506. If not, refer to the next given option below.