 Today most people have Facebook accounts where they keep in touch with friends and family. But large Facebook network of users is also very interesting to another party as well, hackers.
Today most people have Facebook accounts where they keep in touch with friends and family. But large Facebook network of users is also very interesting to another party as well, hackers.
There are many ways hackers can steal your data via direct hacks, trickery, and social engineering in order to get your credentials, emails, and many other things using them to wreak further havoc.
Once a hacker has needed information it is very difficult to minimize impact and all of your information could be compromised from a list of friends to credit card numbers. Keep on reading to learn how can you protect yourself against these attacks and learn about common practices that hackers use in order to steal your data.
Stealing Facebook data via email
A couple of years ago there was a lot of talk about not opening suspicious emails. Well, it still holds today. The difference is that today’s fake emails have become very difficult to differentiate from official ones since hackers put the effort into creating them copying fonts and layout, making them identical to original ones.
So if emails look and feel like original ones how do you know if it is fake? Very simple, you do not click anything in it. If Facebook or for that matter any company wants to contact you they will do via their platform.
Clicking inside a hacker's email will lead you probably to a fake Facebook website replica where you will have to type in your username and password providing an attacker with your login credentials, etc.
If you receive this kind of mail where there are threats about terminating an account, missing payments, etc. it is always the best thing to go directly to Facebook and see if you have any kind of notifications there. Do not trust any emails that ask for account information, request money, or threaten to suspend your account.
Phishing attacks
As stated previously if you click on the link inside fake mail it will probably lead you to a website replica of the original.
Although hackers can pretty much copy all things from an original website like layout, fonts, colors, etc. There is one thing that he cannot, web address. Take a good look into your browser address bar to see if there is a typo or anything strange in the address of a website.
Also, make sure to check for the secure icon in the web address before signing in.
Fake Facebook buttons
If by any chance and for whatever reason, you end up on a fake Facebook site be vary careful about like and other buttons since buttons themselves behave and act like links inside your browser.
IF when you click on like you get a prompt to sign in, it is almost 100% that you ended up on a phishing fake website.
Password brute force attack
Having complex and long passwords is a must. If your Facebook password is 12345 there is a very high chance that if a hacker wants he can easily guess it via trying out the most used and simple passwords via simple guessing.
To avoid being hacked just for having poor passwords try to think of something longer, combine letters and numerical characters, place special characters inside it or just simply as the best solution use a password manager and create passwords with it.
Password grab outside Facebook
If you use the same password for multiple accounts which is a big no-no and you should not do it then hackers can use passwords from other services and login into your Facebook in order to steal data.
Avoid these situations by having different passwords for different accounts or use a password manager to keep everything in order.
Hacking via key logger
Some time ago we have made an article which explained in detail everything you need to know about key loggers here: https://errortools.com/windows/how-to-know-if-you-have-keylogger-in-windows/
Anyway, this is a more advanced hacking technique in order for hackers to steal your data and it includes placing malicious applications into your system that records your keystrokes and sends them directly to hackers.
Since this is an application best protection against this type of attack is to have a security suite installed and active on your PC or device you use to go to Facebook.
Connecting and surfing on an unsecured network
Using no password and unsecured WI FI or any other type of network is risky at least. You can have all protection installed on your device and have a strong password but hackers also logged in to the same network can track all outgoing stuff going through mentioned network leaving you again exposed to attacks.
It is better to connect to your mobile operator network than on free WI FI, at least there is some level of security in your operator network while free WI FI is completely unsecured.
Getting a virtual private network or VPN is also one thing you could think about for protection since almost all VPN services will encrypt your data thus providing you with a security layer even on unsecured Wi-FI.
Conclusion
Hacking and stealing have come a long way from their infant stages and in today’s world when we use a lot of gadgets and have plenty of online presence taking some steps for security is a must.
I hope that you have found anything here informational and helpful so you can avoid getting your data compromised.
 Error Causes
Error Causes Today most people have Facebook accounts where they keep in touch with friends and family. But large Facebook network of users is also very interesting to another party as well, hackers.
Today most people have Facebook accounts where they keep in touch with friends and family. But large Facebook network of users is also very interesting to another party as well, hackers.
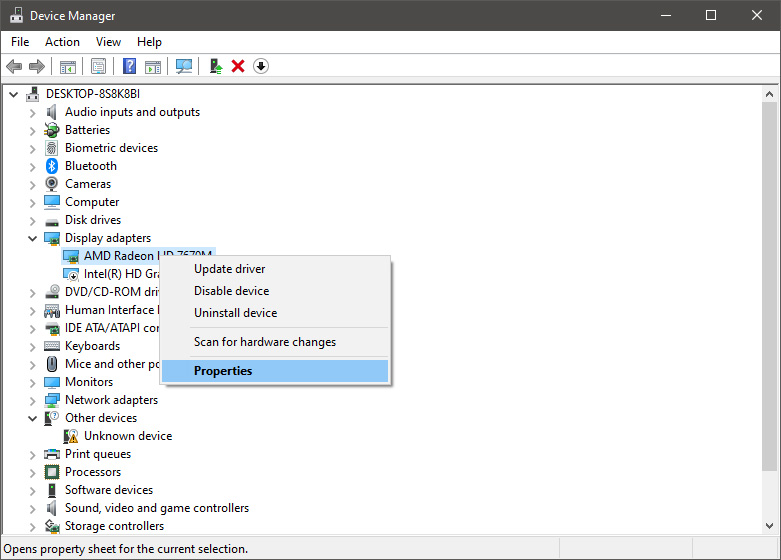
 From the Device Manager choose the troublesome device and right-click on it, choose properties.
From the Device Manager choose the troublesome device and right-click on it, choose properties.
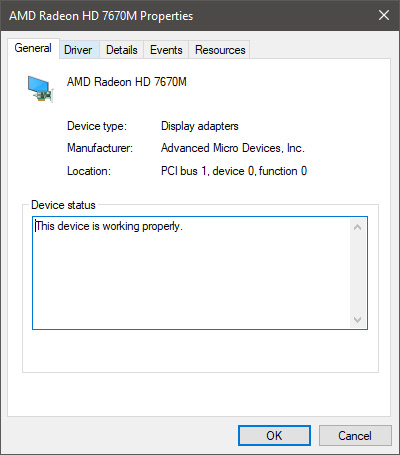
 Device properties floating Window will appear.
Device properties floating Window will appear.
 Click on the top tab which says, Driver. From the Driver tab, click on Roll Back Driver.
Click on the top tab which says, Driver. From the Driver tab, click on Roll Back Driver.
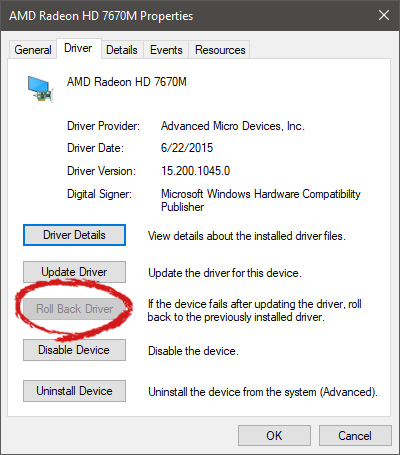 Note that if the device is working properly, the Roll Back Driver button will be greyed out and you will not be able to click on it meaning that chosen device is not the issue. If the device is not working properly and you can click on Roll Back driver, do it, choose the previous version, and reboot your computer.
You can use this method to get back to the previous driver version for any device that is causing issues in your computer.
Note that if the device is working properly, the Roll Back Driver button will be greyed out and you will not be able to click on it meaning that chosen device is not the issue. If the device is not working properly and you can click on Roll Back driver, do it, choose the previous version, and reboot your computer.
You can use this method to get back to the previous driver version for any device that is causing issues in your computer.  Check the Epic Games Status page
Check the Epic Games Status page
