 Many times we were talking and writing here on Errortools.com about security, privacy, hacking, identity theft, etc. We tried to raise important security questions and I hope I have managed to at least shed some light and change maybe some bad behaviors for some, helping them embrace better routines about their security on their PC.
Many times we were talking and writing here on Errortools.com about security, privacy, hacking, identity theft, etc. We tried to raise important security questions and I hope I have managed to at least shed some light and change maybe some bad behaviors for some, helping them embrace better routines about their security on their PC.
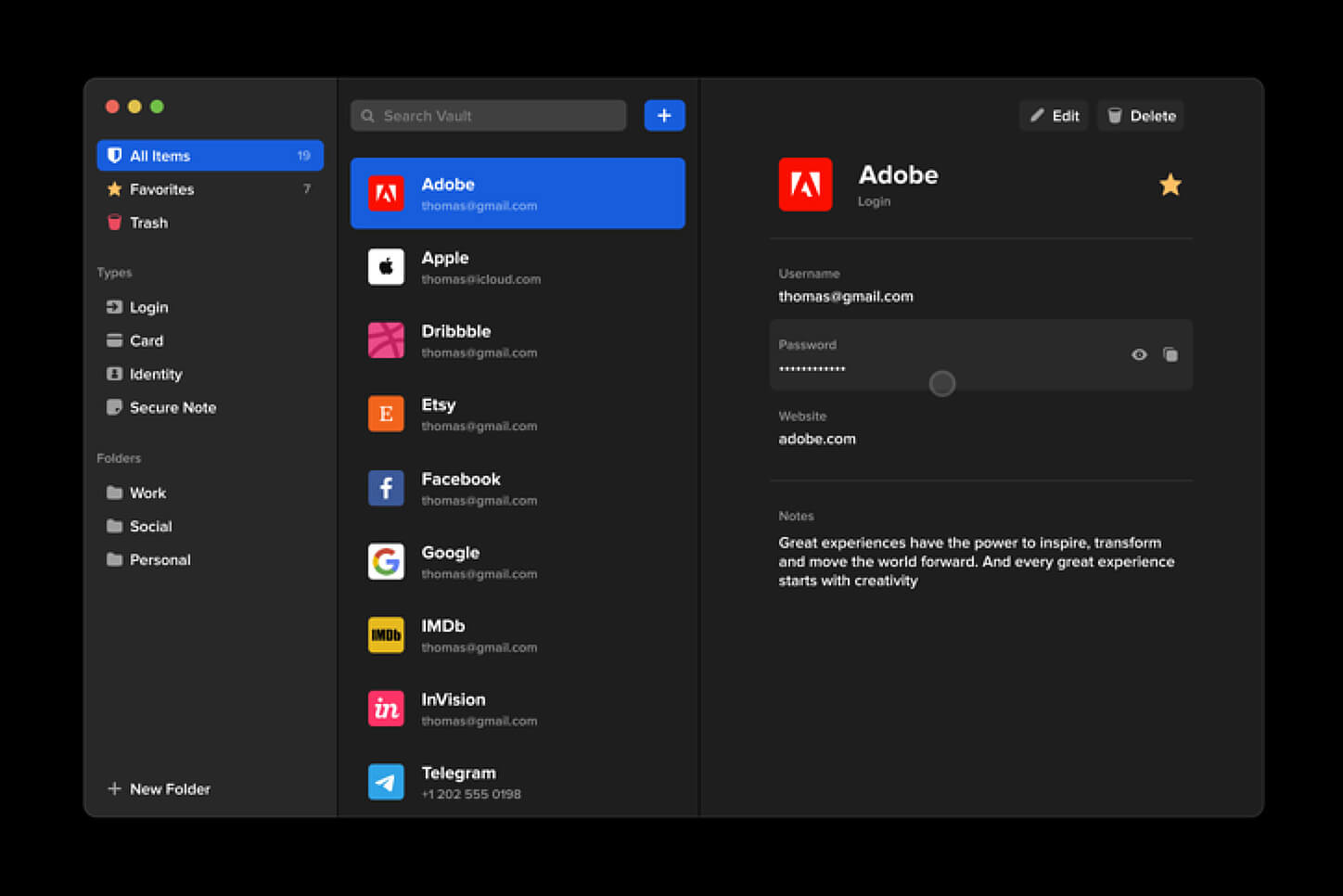
In this light, I will today present you with one neat and awesome piece of software, a password manager worth your time and money (if you want premium features): BitWarden.
What BitWarden offers?
The first thing that it offers is the completely free basic plan, granted BitWarden is not an open-source project nor completely free but it has an unlimited free basic plan that will cover 90% of user needs. There is also a free basic unlimited plan for Organizations letting you and one more user share files and other stuff via BitWarden making it a cool option if you need it.
Premium features offer you encrypted sharing of files, two-step login, 1GB file attachments (encrypted), Bitwarden Authenticator (TOTP), Vault Health Reports, Emergency Access, and Priority Support. The cost for all of these additional features is 10 USD per year for an individual plan or 40 USD per year for organizations where you will get an increase of maximum users from 2 to 6. Yes, you read that correctly, only 10 USD per YEAR for the whole set of features. Granted if you do not need any of them, enjoy the free version forever.
Besides very low premium cost BitWarden will offer you compatibility with all major browsers and devices including both Android and iOS platforms making it a great cross-platform solution to login and maintain your passwords anywhere with just one click.
Once installed all you need to do is set one master password and be very careful not to lose or forget this one, if you do all of your other generated passwords will be lost forever.
Features
Secure Password Sharing
Share your encrypted data quickly and easily, and only with the users or teams who need access
Cross-Platform Accessibility
Access critical data in your Bitwarden vault from any location, browser, and device
Cloud-Based or Self-Host
Get up and running in minutes in the cloud or you can self-host Bitwarden for complete data control
Security Audit & Compliance
Open source and third-party audited, Bitwarden complies with Privacy Shield, GDPR, CCPA regulations
Vault Health Reports
Access insightful reports to reveal weak, reused passwords, and other helpful data security metrics
Directory Sync
Our powerful Directory Connector streamlines user and group onboarding and keeps them in sync
Always-On Support
Our Customer Success agents are available to support you around the clock
Detailed Event Logs
Bitwarden creates audit trails to help you keep track of user and group access to sensitive data
Flexible Integrations
Unite your existing systems with Bitwarden using SSO authentication, Directory services, or powerful APIs
Conclusion
There are many password managers out there but via recommendation I have tried BitWarden and truth to be told, I really never felt the need to try anything else, it is great at what it does and it is moving forward with features and it is constantly updated and maintained.
 Error Causes
Error Causes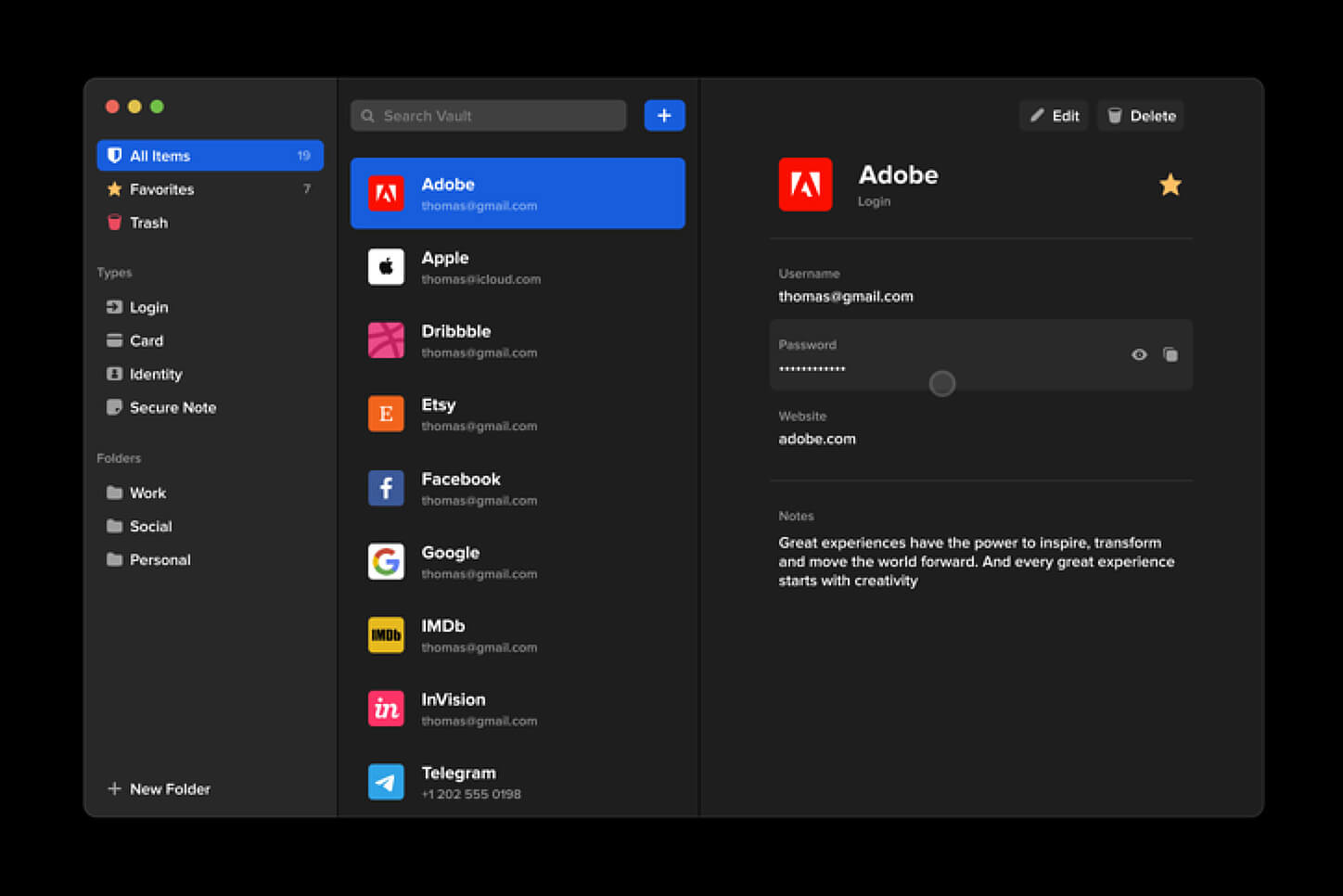 Many times we were talking and writing here on Errortools.com about security, privacy, hacking, identity theft, etc. We tried to raise important security questions and I hope I have managed to at least shed some light and change maybe some bad behaviors for some, helping them embrace better routines about their security on their PC.
Many times we were talking and writing here on Errortools.com about security, privacy, hacking, identity theft, etc. We tried to raise important security questions and I hope I have managed to at least shed some light and change maybe some bad behaviors for some, helping them embrace better routines about their security on their PC.
