Error Code 0xC1900101, 0x4000D - What Is It?
Error Code 0xC1900101, 0x4000D is not very common among the many error codes emerging when updating to Windows 10. It is specific to Windows 7 users who try to upgrade to Windows 10 system.
This error hinders Windows 7 users to install the Windows 10 update. Once the update is launched, the process will go smoothly until a certain percentage (normally upon hitting 70% or more) and then it gets stuck. The user will then see a notification stating: “The installation failed in the SECOND_BOOT phase with an error during MIGRATE_DATA operation.”
You’ll be able to get past the error after a while. The error message will disappear and continue with the configuration process. But, not for long as it will reoccur at around 90% of installation with another error message saying: “The installation failed in the SECOND_BOOT phase with an error during PRE_OOBE operation.”
Solution
 Error Causes
Error Causes
You’re most likely to encounter Error Code 0xC1900101 – 0x4000D when you upgrade to Windows 10 using a USB drive. There are several reasons why this update-related error happens such as wrong update, incompatibility with an antivirus program, or incompatibilities with some software.
Further Information and Manual Repair
In attempting to fix error code-related problems, it is best to do manual repair methods. Employing repair methods manually can help users pinpoint the root causes of the issues they are encountering and apply permanent solutions to fix the problem.
While every Windows user can do most manual repair methods, there are certain cases where help from a Windows expert is needed. If you’re not confident in employing the manual repair methods yourself, you can always consider seeking help from a professional Windows technician who is equipped with enough knowledge to address any issues you are facing or you can just simply use a powerful automated tool.
In fixing Error Code 0xC1900101 – 0x4000D, you can try doing any of the following manual repair methods:
Method One: Disable Background Applications
Error Code 0xC1900101-0x4000D probably occurs when there are programs running in the background of the system as you are in the process of updating. On that note, you must ensure that any programs running in the background must be disabled through Task Manager.
- Press Ctrl+Alt+Del then choose Task Manager.
- Right-click on all background applications then chooses End Task to close the apps.
NOTE: If there are any processes you are unfamiliar with, you can always right-click that process then “search online.” Be careful not to end “Windows process” tasks under the “Type” column as it might cause further problems.
- Restart your device then proceed to Windows 10 system upgrading.
Method Two: Uninstall Anti-Malware Tools
Anti-malware tools normally trigger problems since they consist of files that are possibly incompatible with some software. If Error Code 0xc1900101-0x4000d is caused by incompatibility with an antivirus program, follow the following steps:
- Open the Control Panel then choose System and Security.
- Select Windows Solution Center.
- Click Security to locate your antivirus.
- Once you’ve located your antivirus, click on it then choose
- Restart your device then check if it eliminates the problem.
Method Three: Install System Updates
- Click on the Start menu then select System and Security – Windows Updates.
- Choose Check for updates.
- If there are any required updates detected by the system, select them all then choose Install Updates.
- Restart your device.
Method Four: Check System For Any Incompatibilities
In doing this method, you need to use the System Readiness tool.
- Download System Update Readiness Tool for Windows 7 for x64-based Systems (KB947821).
- Once the download is finished, open Windows 6.1-KB947821-v34-x64.msu
- Run the program to check for any incompatibilities in your system.
NOTE: The process might take a while depending on the speed of your device.
- If there are no results found, you can now try updating again to Windows 10. However, if there are any issues found, you need to have them fixed first.
Method Five: Download A Powerful Automated Tool
Can’t seem to put up with the long and technical manual repair process? You can still fix this error by downloading and installing a powerful automated tool that will surely get the job done in a jiffy!
 Error Causes
Error Causes This is the second large game company acquisition by Microsoft, Acquiring Bethesda first and a big hit to Sony since Xbox will now have more games in its catalog and as exclusives.
This is the second large game company acquisition by Microsoft, Acquiring Bethesda first and a big hit to Sony since Xbox will now have more games in its catalog and as exclusives.
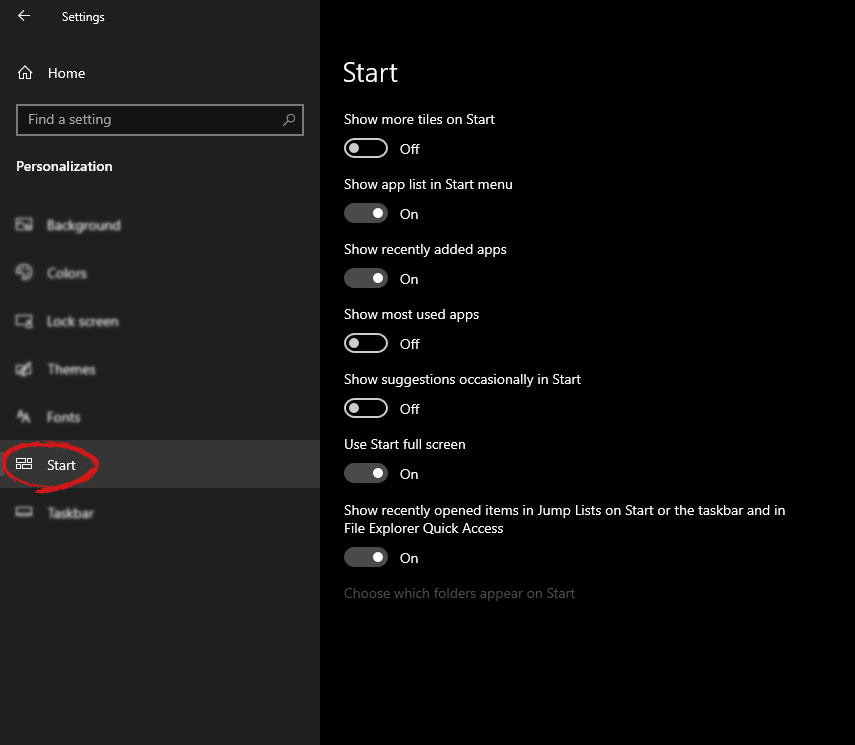
 Under personalization options click on START.
Under personalization options click on START.
 And then on the right part click on the button under Use Start full screen to turn it ON
And then on the right part click on the button under Use Start full screen to turn it ON
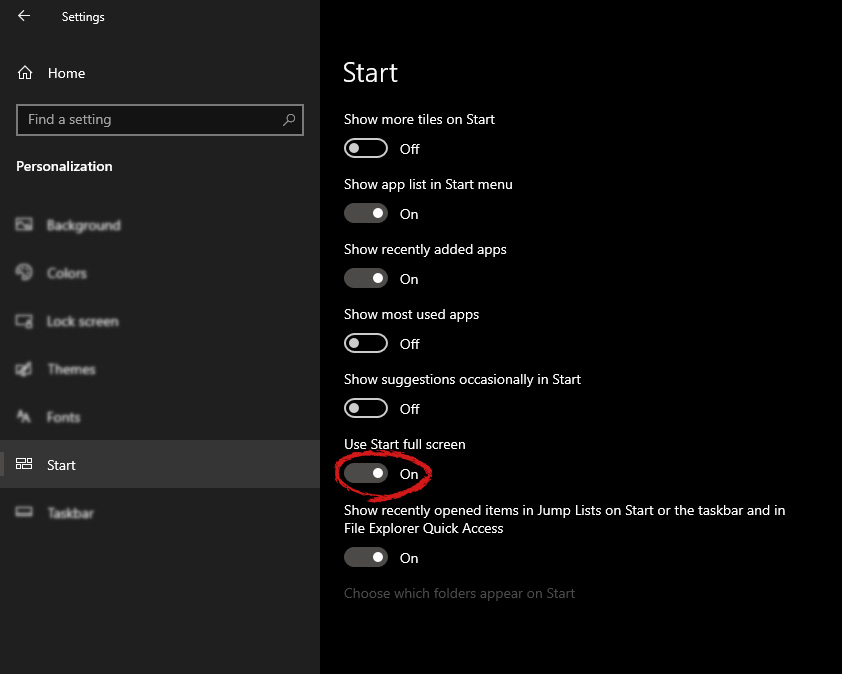 That's it, your start menu is now full screen.
That's it, your start menu is now full screen.  Following are proven solutions that will resolve the issue and provide you with a working device.
Following are proven solutions that will resolve the issue and provide you with a working device.
