Error Code 0x8007041d - What is It?
Error Code 0x8007041d is an error that arises during the Windows 10 Update process. In some cases, this error code can also arise during the Windows 10 Activation process. It is an error code that has been present in multiple versions of the software but usually arises when antivirus or registry issues interfere with the Windows Update or Activation software.
Common symptoms include:
- Inability to download the needed Windows 10 updates
- Inability to complete the Windows 10 Update process
If you are experiencing the Error Code 0x8007041d on your machine, there are several methods that you can use to attempt to resolve the problem. Several of the steps that are most successful for the resolution of this error require familiarity with registry and antivirus tools, so if you are unsure of your ability to complete these steps on your own, contact a qualified computer repair technician to assist you.
Solution
 Error Causes
Error Causes
In most cases, Error Code 0x8007041d arises when there is a conflict between multiple antivirus or malware tools on the computer, if there is an issue in the Windows registry, or if your Windows Defender software is out of date. During the Windows Update process, the system checks to ensure that there are not any factors that are present that could introduce viruses to the system, so if there are any indicators that could present issues to the software, Error Code 0x8007041d will often arise.
Further Information and Manual Repair
For users who experience Error Code 0x8007041d, there are several steps that can be taken to resolve the issue. If the following methods are not successful for you or if you are unsure of your ability to undertake them on your own, contact a qualified Windows 10 computer technician.
Here are the best ways to attempt to fix Error Code 0x8007041d on your computer:
Method 1: Remove Additional Security Software Apart from Windows Defender
In some cases, having multiple versions of malware or antivirus software installed on your computer can cause the Windows system to create conflicts between them, which can interfere with your ability to update. During the update process, the system may attempt to determine if there is any malware present, and having multiple kinds of antivirus software present on the same machine may return mixed results.
If you currently are running antivirus software that is separate from Windows Defender, consider removing it from your computer prior to running the update software. This may allow you to successfully complete your update process without conflict. Additional software can be reinstalled after the update is complete, but make sure to keep both sets of software up to date in order to lessen the chances of encountering this error code again during future updates.
Method 2: Update Your Windows Defender Software
If you currently have Windows Defender as your primary antivirus software, check to see whether it is fully up to date. Out of date antivirus software can cause conflicts with the Windows Update process since the update to Windows 10 will not be able to be completed unless the system is free from viruses or malware.
If you are unsure of whether or not your Windows Defender is up to date, open it and run the process to check for updates, then re-attempt to run Windows Update. In some cases, you may want to restart your computer before running the Windows 10 Update process a second time.
Method 3: Run the Registry Repair Tool
Another issue that could cause Error Code 0x8007041d is a problem in the system registry. If you believe that this may be the case, run the Windows Registry Repair Tool on your machine to check for and resolve any issues. This is a fairly simple and straightforward tool to use, but it can help you to resolve any number of problems that may interfere with your ability to update your Windows 10 software.
If you have taken the steps listed above, restart your computer before attempting to proceed with the Windows Update process. If the three methods listed above are not successful in completely resolving Error Code 0x8007041d on your machine or if you are not comfortable in your ability to implement these steps on your own, contact a qualified Windows repair technician who is familiar with the Windows Update process to assist you.
If you wish to always have at your disposal a utility tool to fix these Windows 10 and other related issues when they do arise, download and install a powerful automated tool.



 Intel announced that Pat Gelsinger (CEO) and Dr. Ann Kelleher (technology Department head) will discuss Intel’s process and packaging innovations on an upcoming webcast that will happen on July 26th.
The spokesman will talk and provide a deeper look at the process and packaging roadmaps for Intel. As we know Intel is planning to expand its production capabilities, outsource some of its technologies and offer foundry services to other chip design companies.
The strategy will also include a shift to a 7nm process and Intel’s effort to set itself again as leader of CPU performance by 2024.
There is also a chance that we will hear exact plans for Intel in the next three or four years.
Intel didn't reveal much else about what Gelsinger and Kelleher plan to discuss during the webcast. The event will be streamed on July 26 at 2 pm PT via the
Intel announced that Pat Gelsinger (CEO) and Dr. Ann Kelleher (technology Department head) will discuss Intel’s process and packaging innovations on an upcoming webcast that will happen on July 26th.
The spokesman will talk and provide a deeper look at the process and packaging roadmaps for Intel. As we know Intel is planning to expand its production capabilities, outsource some of its technologies and offer foundry services to other chip design companies.
The strategy will also include a shift to a 7nm process and Intel’s effort to set itself again as leader of CPU performance by 2024.
There is also a chance that we will hear exact plans for Intel in the next three or four years.
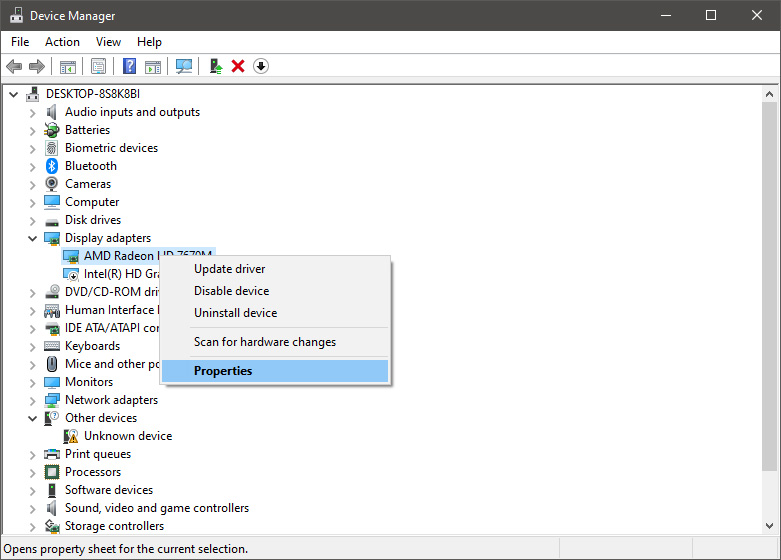
Intel didn't reveal much else about what Gelsinger and Kelleher plan to discuss during the webcast. The event will be streamed on July 26 at 2 pm PT via the  From the Device Manager choose the troublesome device and right-click on it, choose properties.
From the Device Manager choose the troublesome device and right-click on it, choose properties.
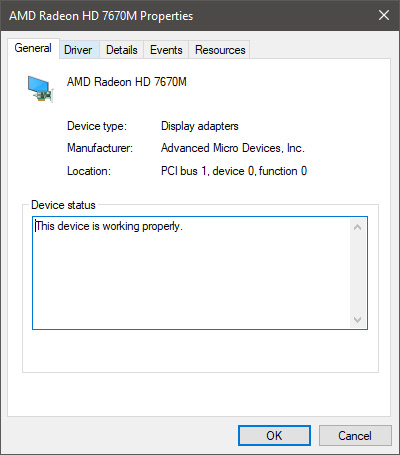
 Device properties floating Window will appear.
Device properties floating Window will appear.
 Click on the top tab which says, Driver. From the Driver tab, click on Roll Back Driver.
Click on the top tab which says, Driver. From the Driver tab, click on Roll Back Driver.
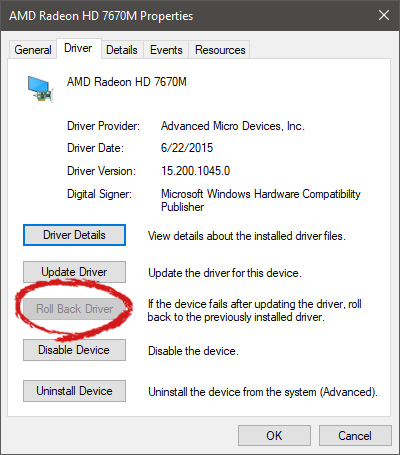 Note that if the device is working properly, the Roll Back Driver button will be greyed out and you will not be able to click on it meaning that chosen device is not the issue. If the device is not working properly and you can click on Roll Back driver, do it, choose the previous version, and reboot your computer.
You can use this method to get back to the previous driver version for any device that is causing issues in your computer.
Note that if the device is working properly, the Roll Back Driver button will be greyed out and you will not be able to click on it meaning that chosen device is not the issue. If the device is not working properly and you can click on Roll Back driver, do it, choose the previous version, and reboot your computer.
You can use this method to get back to the previous driver version for any device that is causing issues in your computer. 
