ShopAtHome Toolbar is a browser extension. This extension tracks information when you visit a website, whether typing in the URL or clicking a link, the Browser App recognizes whether the URL is that of an Affiliate Store, and, if so, may redirect you through the affiliate network site to the Affiliate Store’s website, at which time, a tracking cookie will be placed in your browser. This cookie is the tracking mechanism that will follow your transaction with the Affiliate Store.
During installation, the Browser App may automatically change the default search engine used by your Web browser, whether via a built-in search box or otherwise, to our search engine. Upon installation and setup, it defines an auto-start registry entry which makes this program run on each Windows boot for all user logins. A scheduled task is added to Windows Task Scheduler in order to launch the program at various scheduled times.
Multiple anti-virus scanners have detected possible malware in ShopAtHome.com Helper and are therefore classified as potentially unwanted and flagged for optional removal.
About Browser Hijackers
Browser hijacking is actually a form of an unwanted program, often a web browser add-on or extension, which then causes modifications in the browser’s settings. Browser hijackers can do a variety of things on your PC. The idea would be to force users to visit certain sites that are looking to increase their visitor traffic and generate higher ad income. A lot of people assume that these kinds of sites are legitimate and harmless but that is incorrect. Almost every browser hijacker poses an actual threat to your online safety and it is important to classify them under privacy risks. They do not just screw up your web browsers, but browser hijackers could also modify the system registry, leaving your computer or laptop susceptible to other forms of hacking.
Browser hijacking signs and symptoms
Signs that your web browser is hi-jacked include:
1. the home page of your web browser is changed suddenly
2. you find yourself regularly directed to some other web page than the one you actually meant
3. The default search page of the browser is changed
4. you find many toolbars in your web browser
5. you see a lot of pop-ups on your computer screen
6. your internet browser starts running sluggishly or displays frequent glitches
7. Inability to navigate to particular sites, particularly anti-malware as well as other security software sites.
How browser hijacker infects PCs
Browser hijackers infect computers through malicious email attachments, downloaded infected documents, or by checking out infected internet sites. They also come from add-on programs, also called browser helper objects (BHO), web browser extensions, or toolbars. Other times you may have unintentionally accepted a browser hijacker as part of a software program package (generally freeware or shareware). Popular examples of browser hijackers include Conduit, CoolWebSearch, Coupon Server, OneWebSearch, RocketTab, Delta Search, Searchult.com, and Snap.do.
The best ways to get rid of browser hijackers
Some hijackers could be removed simply by uninstalling the related freeware or add-ons from the Add or Remove Programs in the Microsoft Windows Control Panel. Sadly, the majority of the software packages utilized to hijack a web browser are deliberately designed to be hard to detect or remove. Besides, browser hijackers can modify the Windows registry so it can be very difficult to fix manually, particularly if you are not a very tech-savvy person.
Help! Malware Preventing Anti-virus Installation And Access To The Web
All malware is inherently dangerous, but certain kinds of malware do a lot more damage to your computer or laptop than others. Some malware sits in between the computer and the net connection and blocks some or all websites that you would like to visit. It might also block you from adding anything on your PC, especially anti-malware applications. If you’re reading this, odds are you’re stuck with a virus infection that is preventing you to download and/or install Safebytes Anti-Malware software on your PC. Do as instructed below to get rid of the malware by alternate methods.
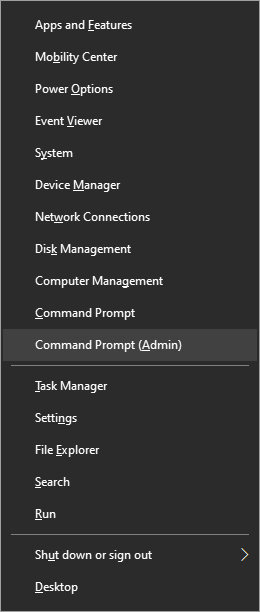
Boot your PC in Safe Mode
In the event the malware is set to load at Windows startup, then booting in Safe Mode should avoid it. Just the minimum required applications and services are loaded when you boot your personal computer in Safe Mode. To launch your Windows XP, Vista, or 7 PCs in Safe Mode with Networking, please do as instructed below.
1) Press the F8 key repeatedly as soon as your PC boots, but before the big Windows logo shows up. This will conjure up the “Advanced Boot Options” menu.
2) Make use of the arrow keys to choose Safe Mode with Networking and press ENTER.
3) Once you get into this mode, you should have online access again. Now, obtain the virus removal application you need by utilizing the browser. To install the application, follow the guidelines in the installation wizard.
4) Right after installation, do a full scan and let the software delete the threats it detects.
Use an alternate web browser to download a security program
Malicious program code can exploit vulnerabilities in a particular browser and block access to all antivirus software websites. The best solution to avoid this problem is to choose a browser that is well known for its security features. Firefox contains built-in Phishing and Malware Protection to keep you secure online.
Install and run anti-virus from a USB drive
Here’s another solution which is using a portable USB anti-virus software package that can check your system for viruses without the need for installation. Try these simple actions to clean up your affected computer by using portable anti-malware.
1) Make use of another virus-free computer system to download Safebytes Anti-Malware.
2) Put the USB drive into the clean PC.
3) Double click on the downloaded file to run the installation wizard.
4) When asked, choose the location of the USB drive as the place where you would like to store the software files. Follow the on-screen instructions to finish the installation.
5) Now, plug the thumb drive into the corrupted system.
6) Run the Safebytes Anti-malware directly from the pen drive by double-clicking the icon.
7) Run Full System Scan to identify and clean-up up all types of malware.
SafeBytes Anti-Malware Features
If you’re planning to purchase anti-malware for your computer system, there are many brands and utilities for you to consider. Some are very good ones, some are ok types, while some are simply just fake anti-malware software that could harm your PC themselves! While looking for an antimalware tool, pick one that provides reliable, efficient, and total protection against all known computer viruses and malware. While considering the dependable software programs, Safebytes AntiMalware is undoubtedly the highly recommended one.
Safebytes is among the well-established computer solutions firms, which provide this complete anti-malware tool. With its cutting-edge technology, this application can help you remove multiples types of malware including computer viruses, worms, PUPs, trojans, adware, ransomware, and browser hijackers.
SafeBytes anti-malware takes computer protection to a totally new level with its enhanced features. Here are a few popular features found in this program:
Antimalware Protection: With a critically acclaimed anti-malware engine, SafeBytes offers multilayered protection that is intended to find and get rid of viruses and malware that are hidden deep inside your computer’s operating system.
Live Protection: SafeBytes provides complete and real-time security for your PC. It’ll continuously monitor your pc for hacker activity and also gives users sophisticated firewall protection.
Extremely Speed Scanning: SafeBytes Anti-Malware has got a multi-thread scan algorithm that works up to 5x faster than any other anti-malware software.
Web Filtering: SafeBytes provides an instant safety rating on the pages you are about to check out, automatically blocking harmful sites and make sure that you’re certain of your online safety while browsing the net.
Lightweight Application: This software program is not “heavy” on the computer’s resources, so you will not find any overall performance troubles when SafeBytes is operating in the background.
24/7 Customer Service: Skilled technicians are at your disposal 24/7! They will quickly fix any technical issues you might be encountering with your security software.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove ShopAtHome without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by ShopAtHome
Files:
File %PROGRAMFILESSelectRebatsToolbarShopAtHomeToolbar.dll.
File %WINDIRDownloaded Program Filesinstall.inf.
File %WINDIRDownloaded Program Filessahagent-cdt1004.exe.
File %LOCALSETTINGSTempsahagent-cdt1004.exe.
File %LOCALSETTINGSTempcdt1004.sah.
File %LOCALSETTINGSTempsetup4002b.cab.
File %LOCALSETTINGSTempsetup4002b.ini.
File %SYSDIRap9h4qmo.ini.
Search and Delete: ap9h4qmo.ini.
File %SYSDIRap9h4qmo.exe.
File %SYSDIRBundleLite_westfrontier1001.exe.
File %SYSDIRap9h4qmo.ini.
File %WINDIRa95kfrhe.exe.
File %SYSDIRa95kfrhe.ini.
File %SYSDIRa95kfrhe.ini.
File %SYSDIRq17i9a4j.ini.
Search and Delete: ap9h4qmo.ini.
Directory %LOCALSETTINGSTempSahUpdate.
Registry:
Key 759C257C-F750-4F52-AB58-FB8A7B8770FE at HKEY_CLASSES_ROOTTypeLib.
Key HKEY_CLASSES_ROOT named GRInstall7.Installer
Key HKEY_CLASSES_ROOT named GRInstall7.Installer.1


 That being said, now when services are back we stopped and reflected on the platform itself and on its users. If Facebook is vulnerable so are its users, but sometimes users themselves are responsible for being a target. We step back and take a look at posts that manifest on Facebook and have come with some advice on what things you should never post on Facebook and on other social platforms.
That being said, now when services are back we stopped and reflected on the platform itself and on its users. If Facebook is vulnerable so are its users, but sometimes users themselves are responsible for being a target. We step back and take a look at posts that manifest on Facebook and have come with some advice on what things you should never post on Facebook and on other social platforms.









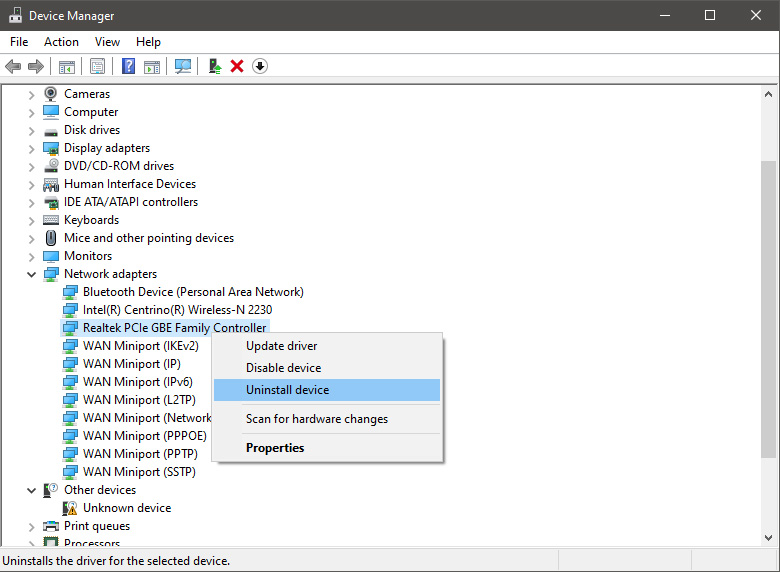
 In the Device Manager expand Network adapters, choose adapter, right-click on it and choose Uninstall.
In the Device Manager expand Network adapters, choose adapter, right-click on it and choose Uninstall.
 Install latest driver or reboot so Windows will install the driver automatically
Install latest driver or reboot so Windows will install the driver automatically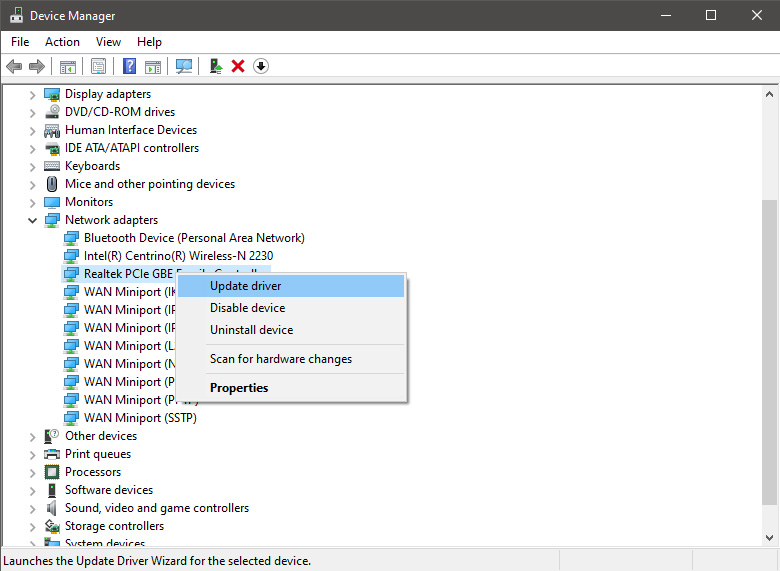
 In command prompt type next line and press ENTERDEL /F /S /Q /A “C:\Windows\System32\drivers\mfewfpk.sys
Reboot the system
In command prompt type next line and press ENTERDEL /F /S /Q /A “C:\Windows\System32\drivers\mfewfpk.sys
Reboot the system