FindGoFind is a browser extension for Google Chrome.Developers present findgofind.com as an improved Internet search engine that supposedly enhances the Internet browsing experience by generating better search results. These claims often trick users into believing that findgofind.com is legitimate and useful. In fact, developers promote this site using deceptive software download/installation set-ups that hijack web browsers and modify various options without permission. Furthermore, findgofind.co continually records various data relating to users’ Internet browsing activity.
While this extension is installed, users will see additional unwanted ads throughout their browsing sessions. Furthermore, this extension changed the default search engine to FindGoFind to easier display Sponsored content.
About Browser Hijackers
Browser hijackers (also known as hijackware) are a type of malicious software that modifies web browser configuration settings without the computer owner’s knowledge or approval. These hijacks are raising at an astonishing rate across the world, and they can be truly nefarious and sometimes harmful too. Browser hijackers can do a variety of things on your computer. These are typically used to force hits to a specific site, manipulating web traffic to earn ad revenue. Many people believe that the browser hijacker is just a harmless website but that is incorrect. Almost every browser hijacker poses an actual threat to your online safety and it’s vital to categorize them under privacy risks. When the malware attacks your computer, it begins to mess things up a whole lot that slows your PC down to a crawl. In the worse case, you will be pushed to tackle serious malware threats too.
How one can know if your browser is hijacked
The typical signs that signify having this malicious software on your PC are:
1. the home page of the browser is changed all of a sudden
2. you see new unwanted favorites or bookmarks added, usually directed to advertisement-filled or porn websites
3. the default browser configurations are changed and/or your default web engine is altered
4. you’ll see multiple toolbars in your internet browser
5. you see lots of pop-ups on your screen
6. your internet browser has become unstable or starts running slowly
7. you can’t navigate to certain websites, like security software-related sites.
Exactly how they infect computer systems
Browser hijackers may use drive-by downloads or file-sharing websites or even an e-mail attachment to reach a targeted computer. They also come from add-on programs, also known as browser helper objects (BHO), web browser plug-ins, or toolbars. Also, certain freeware and shareware can put the hijacker in your PC through “bundling”. Some of the most well-known hijackers are FindGoFind, Babylon Toolbar, Conduit Search, Sweet Page, OneWebSearch, and CoolWebSearch.
How you can get rid of a browser hijacker
Some hijackers can be simply removed by uninstalling the free software they came with or by deleting any add-ons you have recently added to your system. In some cases, it can be a difficult job to find and delete the malicious program because the associated file might be running as part of the operating system process. Apart from that, manual removal expects you to perform several time-consuming and complicated actions that are tough to do for new computer users.
Industry experts always recommend users to eliminate any malware including browser hijacker with an automatic malware removal tool, which is easier, safer and faster than the manual removal method. SafeBytes Anti-Malware can counter relentless hijackers and provide you with proactive PC protection against all kinds of malware.
What you can do if Virus Prevents You From Downloading Anti-virus?
Malware may cause several kinds of damage to computers, networks, and data. Some malware sits in between the computer and your net connection and blocks a few or all internet sites that you want to visit. It will also block you from adding anything to your system, particularly the anti-virus program. So what to do if malicious software keeps you from downloading or installing Anti-Malware? There are a few actions you can take to get around this issue.
Download the application in Safe Mode with Networking
If the malware is set to load at Windows startup, then booting in Safe Mode should prevent it. Just the minimum required programs and services are loaded when you start your computer in Safe Mode. To start your Windows XP, Vista, or 7 computers in Safe Mode with Networking, do as instructed below.
1) At power on/start-up, hit the F8 key in one-second intervals. This will conjure up the Advanced Boot Options menu.
2) Select Safe Mode with Networking with arrow keys and press Enter.
3) When this mode loads, you will have the internet. Now, use your browser to download and install Safebytes Anti-malware.
4) Following installation, run a complete scan and let the software delete the threats it detects.
Use an alternate web browser to download an antivirus application
Some malware may target vulnerabilities of a particular browser that obstruct the downloading process. If you’re not able to download the anti-malware software program using Internet Explorer, it means the virus is targeting IE’s vulnerabilities. Here, you need to switch over to a different browser like Firefox or Chrome to download Safebytes Anti-malware software.
Make a bootable USB anti-virus drive
Another option would be to make a portable antivirus program onto your USB thumb drive. Adopt these measures to use a flash drive to fix your infected computer system.
1) Download the anti-malware program on a virus-free PC.
2) Connect the USB flash drive to a USB port on the uninfected computer.
3) Double click on the downloaded file to run the installation wizard.
4) Pick a USB flash drive as the place when the wizard asks you exactly where you intend to install the application. Follow the activation instructions.
5) Transfer the pen drive from the clean PC to the infected PC.
6) Run the Safebytes Anti-malware directly from the pen drive by double-clicking the icon.
7) Hit the “Scan” button to run a full computer scan and remove viruses automatically.
Protect your PC against Malware With SafeBytes Security Suite
If you are looking to download an anti-malware application for your PC, there are several tools out there to consider nonetheless, you should not trust blindly anyone, no matter whether it is free or paid software. A few are good ones, some are decent, and some are merely fake anti-malware software that will harm your PC themselves! You need to be very careful not to select the wrong product, particularly if you buy a paid application. When considering commercial application options, the majority of people select well-known brands, like SafeBytes, and are very happy with them.
SafeBytes anti-malware is trustworthy software that not only secures your PC permanently but is also very easy to use for people of all ability levels. Once you have installed this software, SafeByte's sophisticated protection system will ensure that no viruses or malicious software can seep through your personal computer.
SafeBytes has excellent features when compared to other anti-malware programs. Listed below are some of the features you may like in SafeBytes.
Robust Anti-malware Protection: With a critically acclaimed anti-malware engine, SafeBytes offers multilayered protection which is made to find and get rid of viruses and malware that are hidden deep in your computer’s operating system.
Real-Time Protection: SafeBytes gives complete and real-time security for your PC. It’ll inspect your personal computer for suspicious activity at all times and its unparalleled firewall protects your PC from illegal access by the outside world.
High-Speed Malware Scanning Engine: SafeBytes Anti-Malware has got a multi-thread scan algorithm that works up to 5 times faster than any other antivirus software.
Safe Web Browsing: SafeBytes provides an instant safety rating on the web pages you are going to check out, automatically blocking unsafe sites and making sure that you’re certain of your online safety while browsing the web.
Lightweight: The program is lightweight and can run silently in the background, and that does not impact your PC efficiency.
Premium Support: For any technical queries or product guidance, you can obtain 24/7 professional assistance through chat and e-mail.
To sum it up, SafeBytes has created a meaningful anti-malware solution that is aimed to protect your computer against all manner of malware. There is no doubt that your PC will be protected in real-time as soon as you put this software program to use. You’ll get the best all-around protection for the money you pay on SafeBytes Anti-Malware subscription, there’s no question about it.
Technical Details and Manual Removal (Advanced Users)
If you wish to carry out the removal of FindGoFind manually instead of employing an automated tool, you may follow these simple steps: Navigate to the Windows Control Panel, click the “Add or Remove Programs” and there, select the offending program to remove. In case of suspicious versions of browser plug-ins, you can actually remove it via your browser’s extension manager. You’ll likely also want to reset your browser.
If you opt to manually delete the system files and Windows registry entries, use the following list to make sure you know precisely what files to remove before performing any actions. Please remember that this is for experienced users only and might be challenging, with wrong file removal resulting in additional system errors. In addition, some malicious programs have the capability to defend against its deletion. Doing this malware-removal process in Safe Mode is recommended.
Registry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\FindGoFind.comTT0-F49X-LPA01-3150QB
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\FindGoFind.comWG9-L33B-ZSH05-1418OI
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Shell\FindGoFind.comRegistry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\FindGoFind.comTT0-F49X-LPA01-3150QB
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\FindGoFind.comWG9-L33B-ZSH05-1418OI
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Shell\FindGoFind.com%#MANIFEST#%PH1-S39W-JGS29-6268LL
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run [random].exe
HKEY_CURRENT_USER\Software\AppDataLow\Software\FindGoFind.com
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ FindGoFind.com
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\BrowserHelperObjects\[random numbers]PH1-S39W-JGS29-6268LL
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run [random].exe
HKEY_CURRENT_USER\Software\AppDataLow\Software\FindGoFind.com
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ FindGoFind.com
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\BrowserHelperObjects\[random numbers]

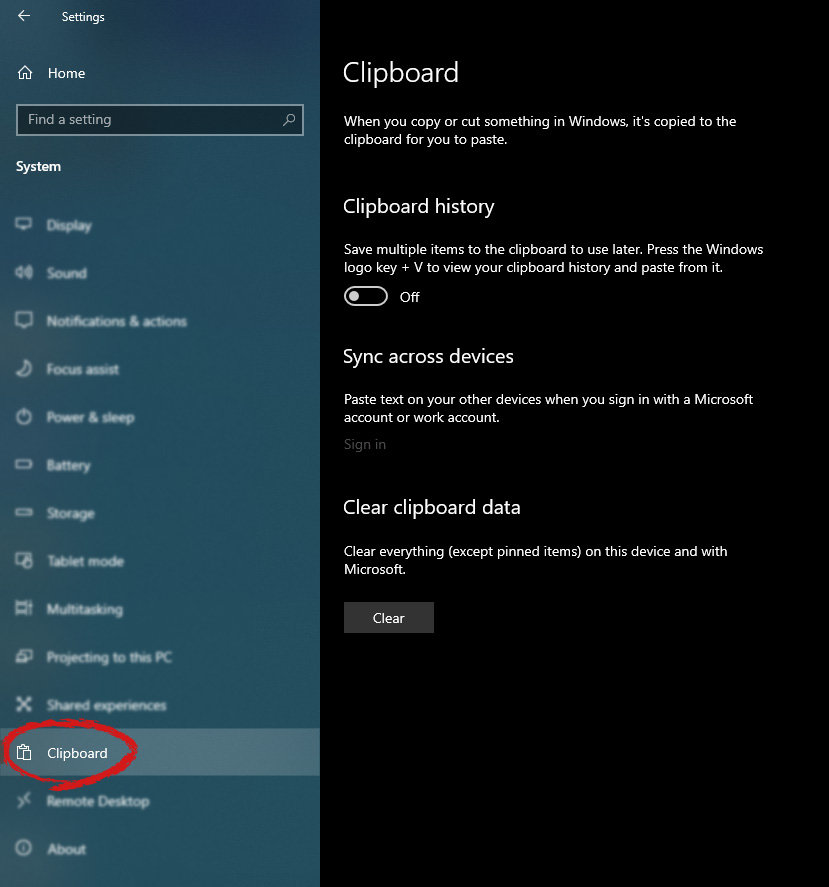
 in system dialog click on the clipboard and on the right screen turn ON CLipboard history.
in system dialog click on the clipboard and on the right screen turn ON CLipboard history.