Error Code 0x800703e3, What is it?
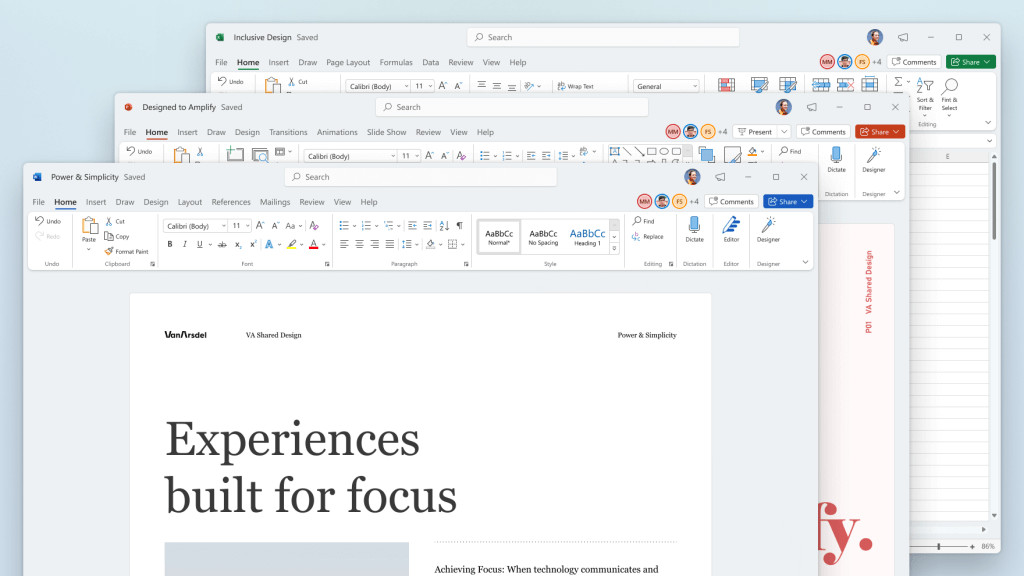
Error Code 0x800703e3 is an error that arises on Windows 10, as well as on many of the past versions of the Windows operating system, dating back to Windows 7. It is an error that is associated with a number of different causes, and therefore, there are many different ways to attempt to resolve the error.
Common symptoms include:
- Programs running slowly or locking up
- Computer freezing or going to a blue screen
- Report of an error message
In most cases, users experience Error Code 0x800703e3 when they attempt to install new software or upgrade their programs and operating systems on their Windows machine. Error Code 0x800703e3 is fairly simple to fix and many of the methods used do not require advanced computer skills or knowledge. However, if you have any difficulty in implementing the steps below on your device, it is recommended that you contact a qualified computer repair technician to assist you.
Solution
 Error Causes
Error Causes
There are a number of different causes for Error Code 0x800703e3. The most common ones that Windows users experience are:
- Incomplete installations interfering with system files
- Outdated operating system or programs
- Updates left unfinished for long periods of time
- Manual cancellation of the installation process
- Malware or viruses
- Corrupted files in the operating system
- Redundancy in the installations of a program on the device
Further Information and Manual Repair
As there are many different things that can cause Error Code 0x800703e3 to appear on your Windows device, there are many methods that you can use to attempt to resolve the error. While many of these are easy to complete for basic users, some of the methods below require familiarity with advanced computing techniques. If you have trouble using the methods below, contact a qualified Windows repair technician.
Here are the top ways to resolve Error Code 0x800703e3:
Method One: Update Your Device Drivers and Registries
The best place to start in resolving Error Code 0x800703e3 is to open up your settings for your drivers and check to see if any updates are necessary. After updating your drivers, it is important to restart your computer to allow any changes to take effect.
Secondarily, you can also run the Windows Registry Repair tool to see if there are any system files in your library that can be fixed, removed, or added automatically by the repair wizard. Again, it is important that you restart your computer after the tool has finished its scan and repair process to ensure that all necessary changes become fully active and recognized by the system.
Method Two: Check for System and Program Updates
If it has been a while since you last updated your software and operating system, open up the settings for your system updates. Always restart your computer after a system update has been completed to allow the necessary changes to take effect.
Remember that it is important to regularly update both your Windows operating system and your programs to ensure that there is not a backlog of updates to be completed. This can help to keep your computer in optimum health and eliminate future errors during installations and standard operation of your computer.
Method Three: Restore Your System
In some cases, the best way to address Error Code 0x800703e3 is to reinstall the Windows operating system on your machine. If the core issue of the error is that there is a missing or damaged system file, this is the best way to address the problem quickly and efficiently. Before you attempt to reinstall the Windows operating on your machine, make sure that all of your programs and information have been backed up in a secure manner so that you can restore these items after the installation is complete.
Method Four: Remove Recently Added Programs
If you just began to experience the error after installing a new program, try removing the new program from your machine using the “uninstall” process, then restart your computer.
If you have any difficulty in completing the above methods on your own or if the problem has not been fully resolved using these methods, get in touch with a certified Windows technician who can help you to fix the issues at hand and get your computer up and running again.

 How to switch
How to switch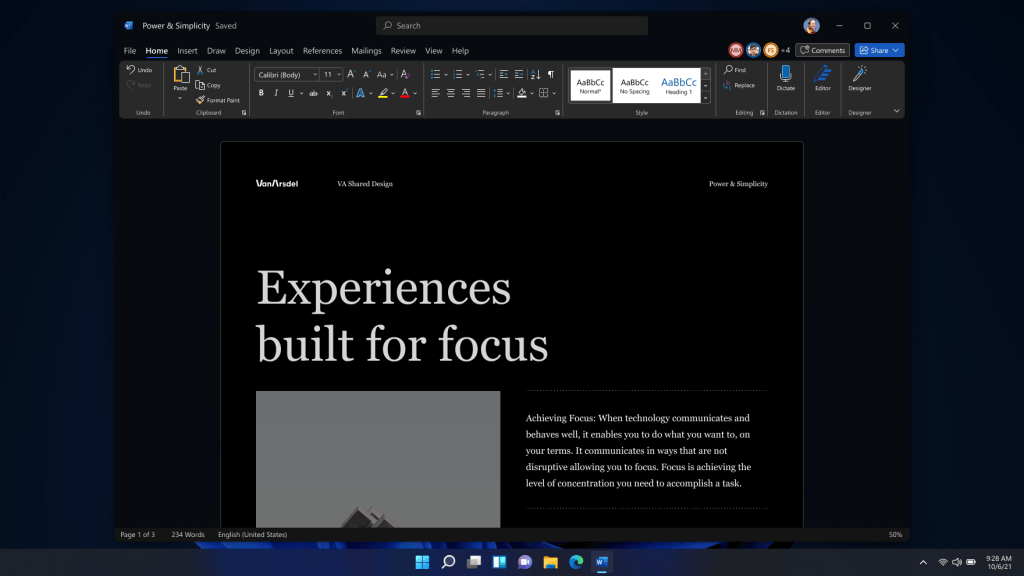 Conclusion
Conclusion
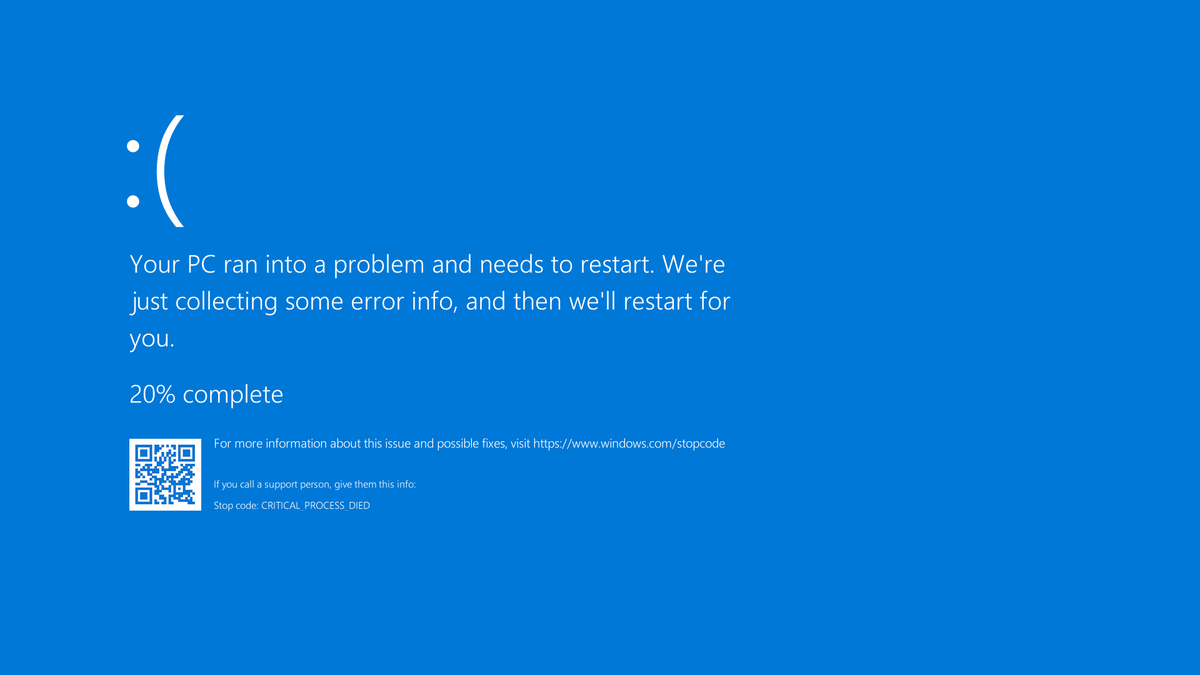 A stop error or exception error commonly called the blue screen of death (BSoD) or blue screen, is an error screen displayed on Windows computers following a fatal system error. It indicates a system crash, in which the operating system has reached a condition where it can no longer operate safely. This is caused by many different problems, such as a general hardware failure or a crucial process terminating unexpectedly.
A stop error or exception error commonly called the blue screen of death (BSoD) or blue screen, is an error screen displayed on Windows computers following a fatal system error. It indicates a system crash, in which the operating system has reached a condition where it can no longer operate safely. This is caused by many different problems, such as a general hardware failure or a crucial process terminating unexpectedly.
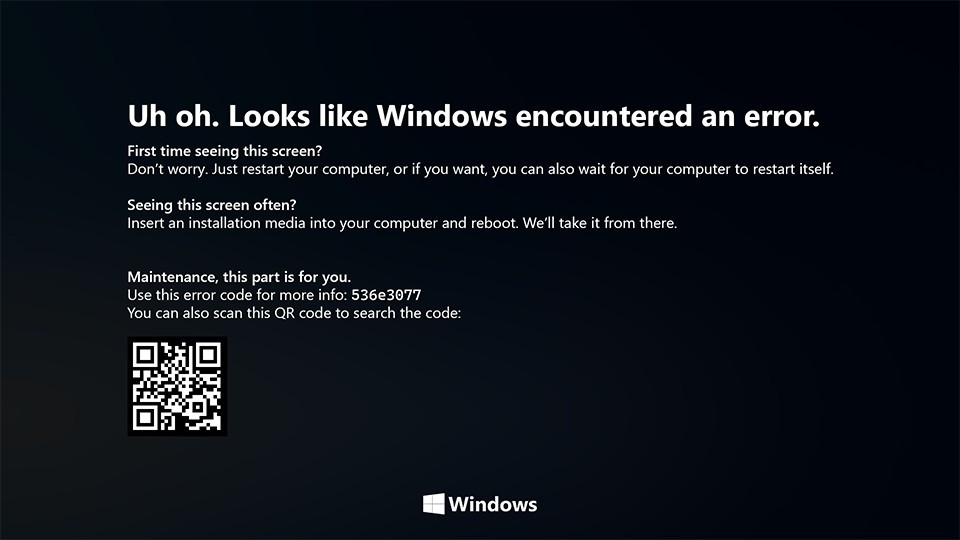 On Windows 10 systems, a Black Screen of Death can be caused by an unfinished Windows Update.
On Windows 10 systems, a Black Screen of Death can be caused by an unfinished Windows Update.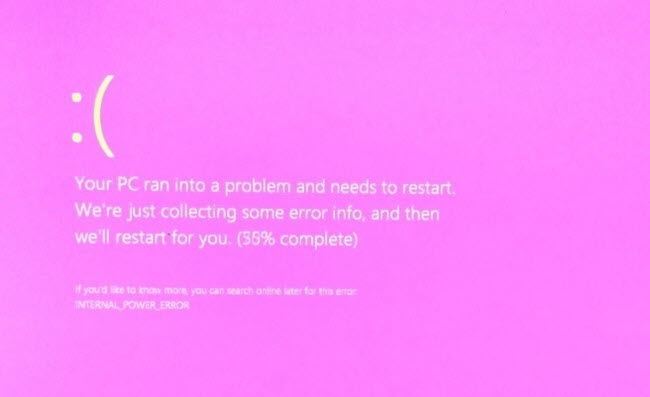 It is a diagnostic screen with a white type on a pink background. Pink Screen is mainly seen when the VMkernel of an ESX/ESXi host experiences a critical error, becomes inoperative, and terminates any virtual machines that are running. It is not fatal and generally considered more of a developer testing issue. When encountered, it can be fixed quickly by following the simple action of pressing and holding your computer’s power button to shut down the device.
It is a diagnostic screen with a white type on a pink background. Pink Screen is mainly seen when the VMkernel of an ESX/ESXi host experiences a critical error, becomes inoperative, and terminates any virtual machines that are running. It is not fatal and generally considered more of a developer testing issue. When encountered, it can be fixed quickly by following the simple action of pressing and holding your computer’s power button to shut down the device.
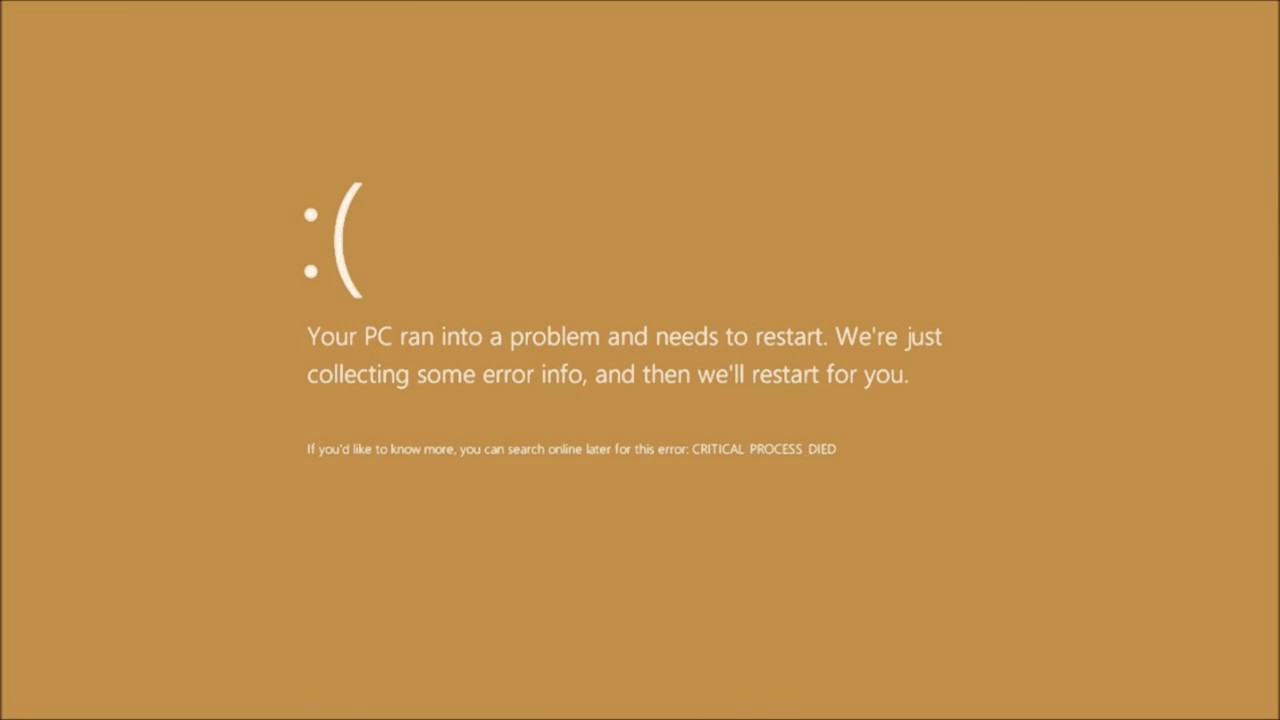 The Microsoft Windows 10 Operating System Brown Screen of Death is an on-screen fatal error notification with bug check codes which is seen when a computer crashes due to graphics hardware or software-related problems (failing graphics drivers).
The Microsoft Windows 10 Operating System Brown Screen of Death is an on-screen fatal error notification with bug check codes which is seen when a computer crashes due to graphics hardware or software-related problems (failing graphics drivers).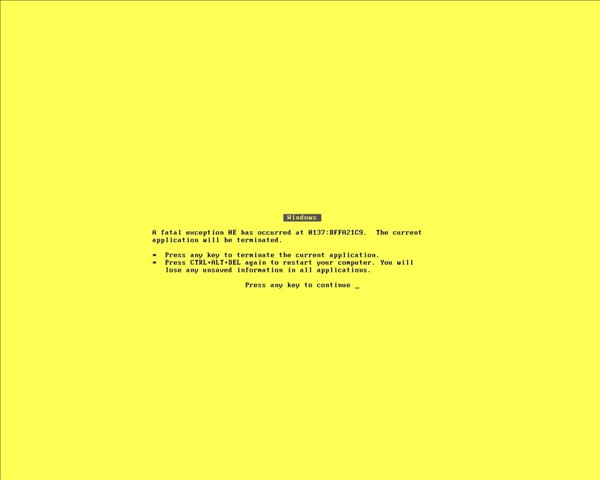 It affects the functioning of a browser, particularly Mozilla Firefox. The Yellow Screen of Death makes the appearance with a weird buzzing sound in the background when the XML parser refuses to process an XML document causing a parsing error and a weird buzzing sound. The issue persists unless the computer is manually rebooted.
It affects the functioning of a browser, particularly Mozilla Firefox. The Yellow Screen of Death makes the appearance with a weird buzzing sound in the background when the XML parser refuses to process an XML document causing a parsing error and a weird buzzing sound. The issue persists unless the computer is manually rebooted.
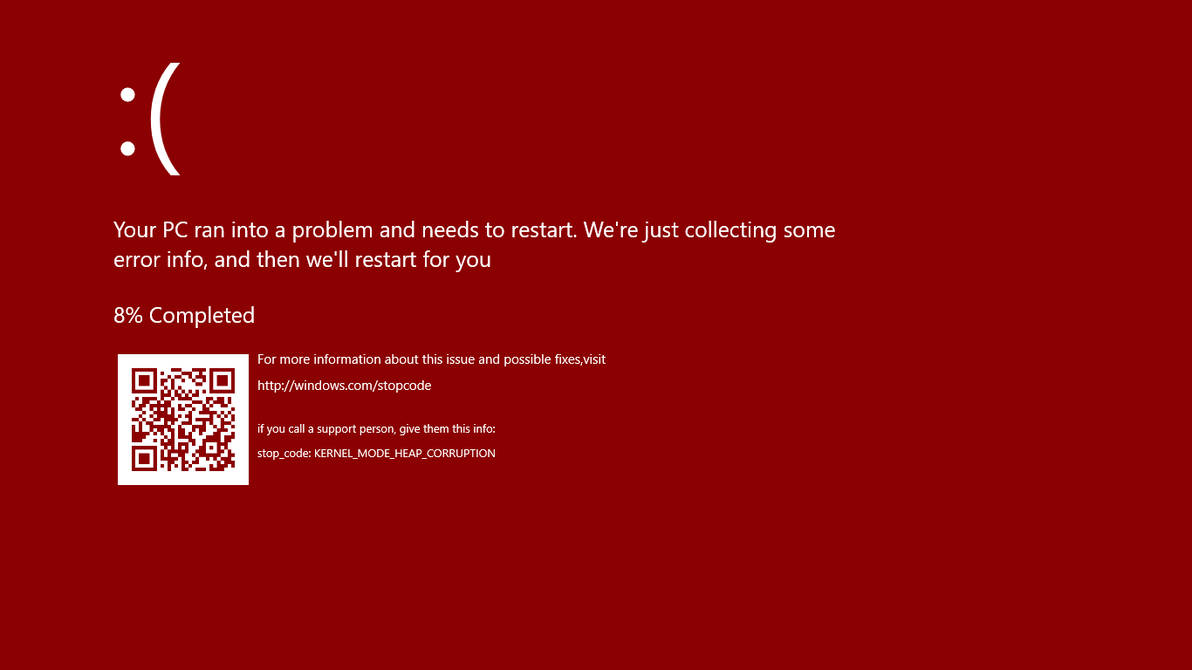 Commonly the Windows 10 red screen is caused due to the hardware error, particularly if you overclock your Windows PC/laptop. Despite this, sometimes the red screen of death is also caused by outdated or incompatible drivers or due to BIOS issues.
Commonly the Windows 10 red screen is caused due to the hardware error, particularly if you overclock your Windows PC/laptop. Despite this, sometimes the red screen of death is also caused by outdated or incompatible drivers or due to BIOS issues.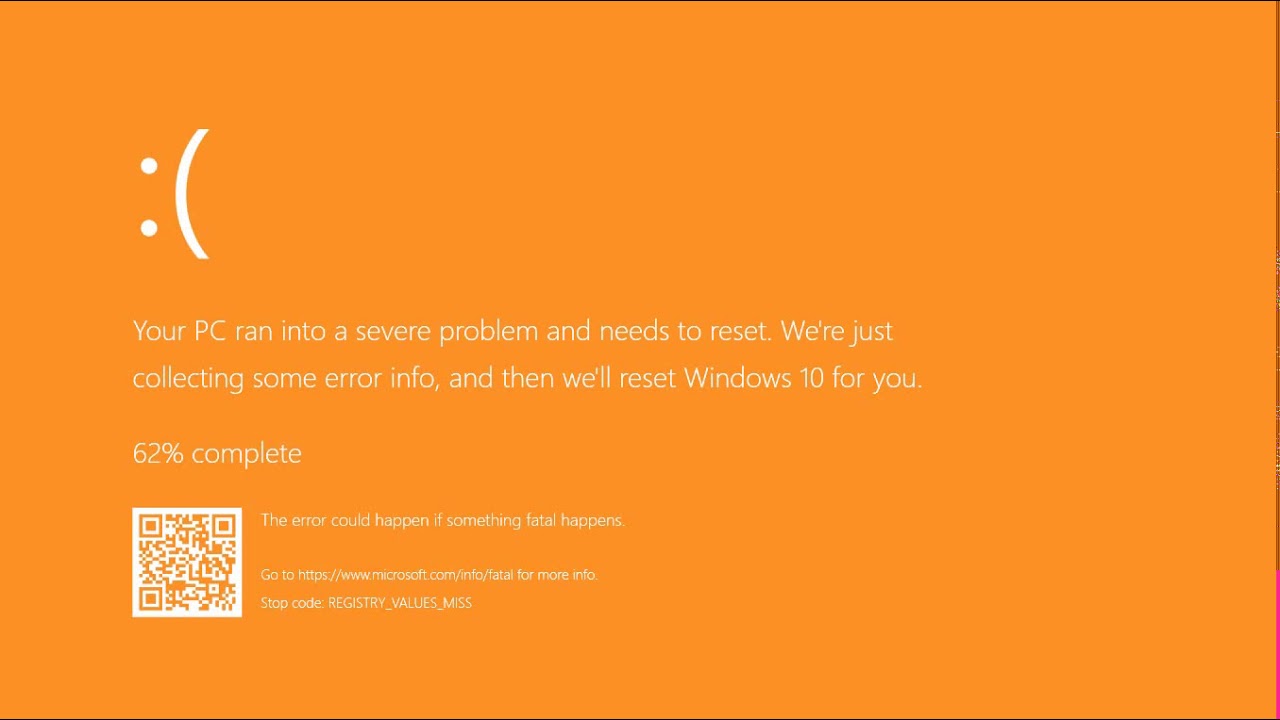 The Orange Screen of Death on Windows occurs due to fatal hardware errors. Multiple reasons have been reported for the Orange Screen of Death. Some had this issue when watching a YouTube video, some were not able to boot into Windows. It can even occur when waking up from Sleep.
The Orange Screen of Death on Windows occurs due to fatal hardware errors. Multiple reasons have been reported for the Orange Screen of Death. Some had this issue when watching a YouTube video, some were not able to boot into Windows. It can even occur when waking up from Sleep.
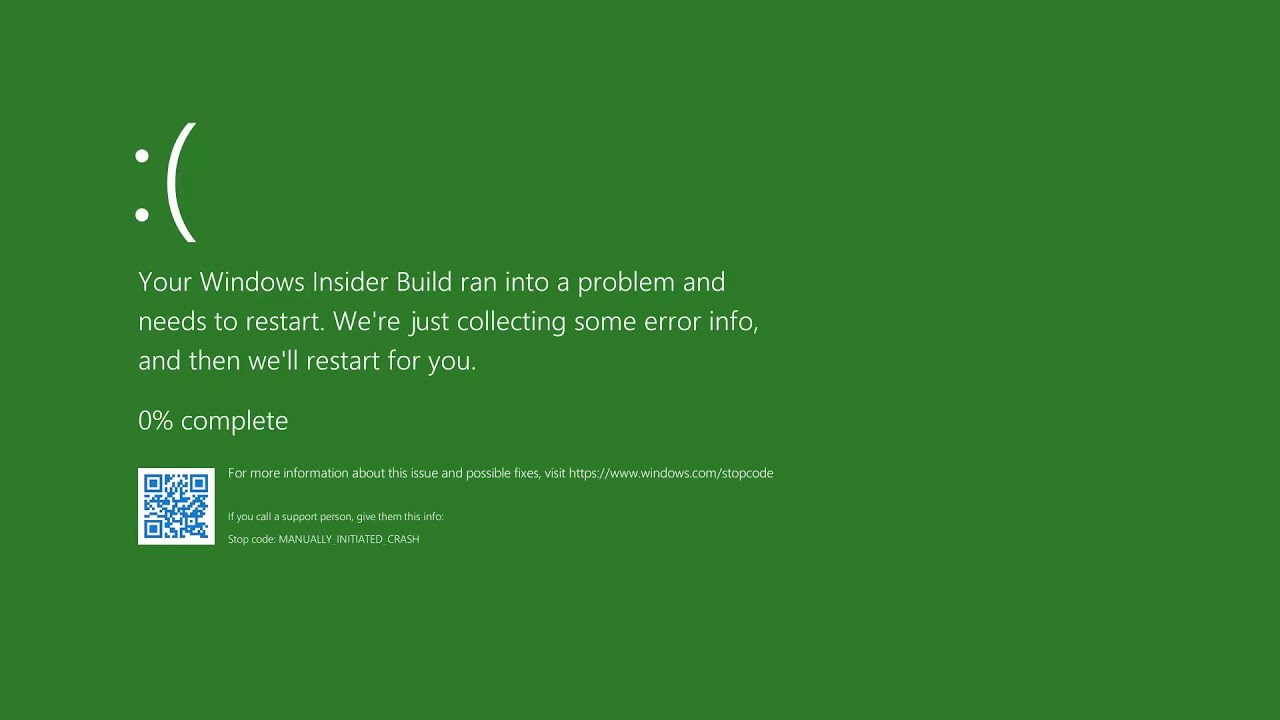 The green screen of death only appears when you're running an Insider Preview version of Windows 10. It's the same as the blue screen of death, and it will show the same error messages. ... If you see a green screen of death (GSOD) on your PC, that's a sign you're using an Insider Preview build of Windows 10.
The green screen of death only appears when you're running an Insider Preview version of Windows 10. It's the same as the blue screen of death, and it will show the same error messages. ... If you see a green screen of death (GSOD) on your PC, that's a sign you're using an Insider Preview build of Windows 10.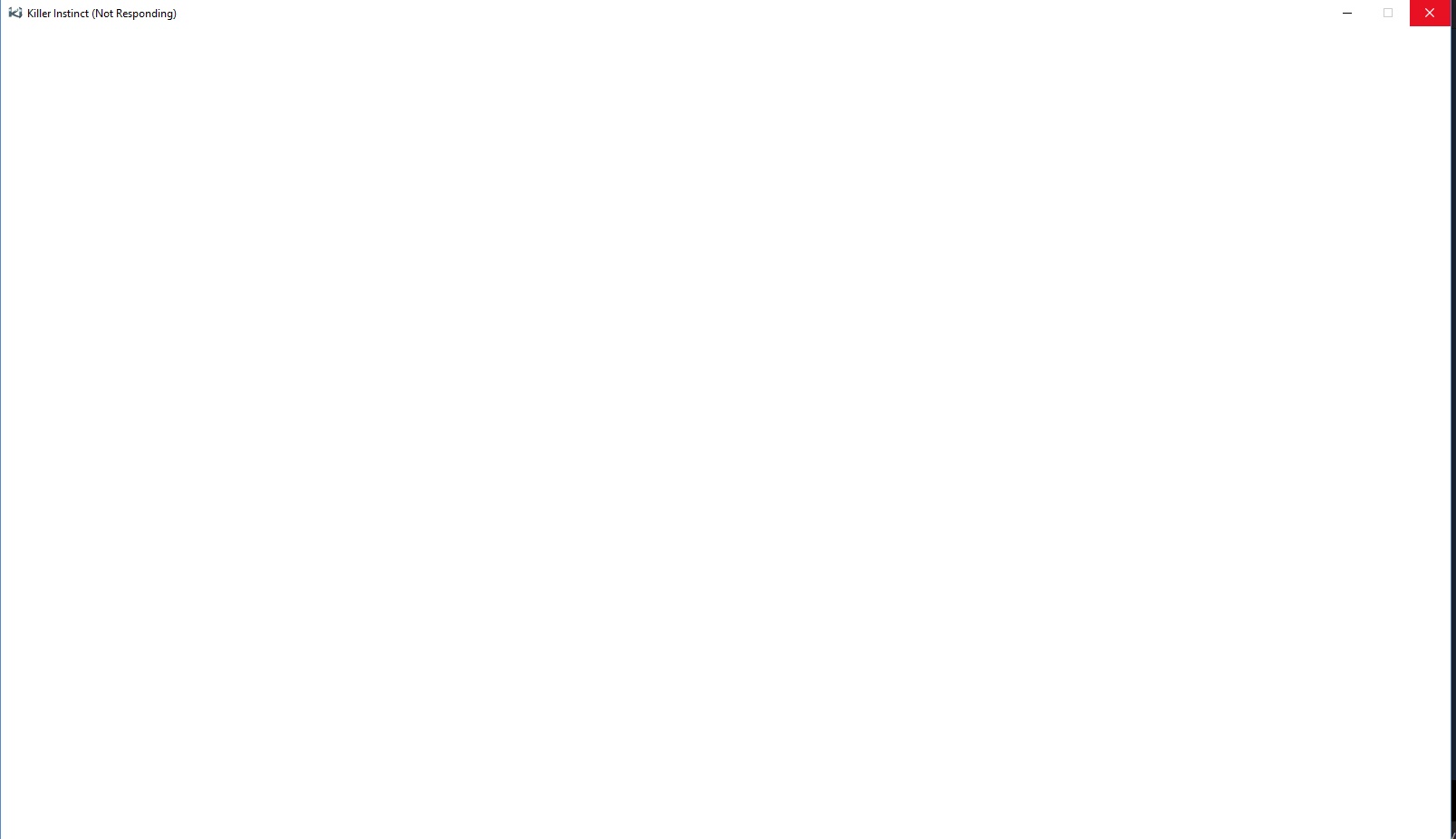 The White Screen on Windows is also an error where the screen of the computer just turns white and freezes. There can be several things that can cause the white screen to appear on the Windows laptop monitor. But the main issue could be because of malfunctioning of the graphics hardware.
The White Screen on Windows is also an error where the screen of the computer just turns white and freezes. There can be several things that can cause the white screen to appear on the Windows laptop monitor. But the main issue could be because of malfunctioning of the graphics hardware. 