AVFoundationCF.dll is a type of Dynamic Link Library file.
This DLL file is associated with AVFoundationCF and is developed by Apple Computer Inc. for Windows PC. This file functions similarly to any other DLL files. It comprises of small programs. This DLL file is typically needed to load and start the Apple iTunes utility.
The inability to call this file or the files to load triggers the AVFoundationCF.dll error message on your system.
The error message can be displayed in either of the formats on your PC:
“The program can’t start because AVFoundationCF.dll is missing from your computer. Try reinstalling the program to fix this problem.”
"This application failed to start because avfoundationcf.dll was not found.”
"Cannot find %COMMONFILES%AppleApple Application Supportavfoundationcf.dll."
"Cannot start AVFoundationCF. A required component is missing: avfoundationcf.dll.”
“Avfoundationcf.dll Access Violation."
"Cannot register avfoundationcf.dll."
Solution
 Error Causes
Error Causes
AVFoundationCF.dll error can occur due to numerous reasons. However, the most common reasons for this error code include:
- Viral infection
- Corrupt or invalid registry entries
- Apple Computer Inc. hardware failure such as bad hard drive
- Missing or deleted Avfoundationcf.dll file
It is recommended to resolve the error as soon as you experience it virtually because if the error code is related to viral infection on your system, it can expose your PC to privacy errors and data security risk.
And if the error is triggered by registry issues, it can lead to serious threats like system crash, failure, and data loss.
Therefore, the AVFoundationCF.dll error not only hampers your ability to access and start
Apple iTunes program but it also puts your PC at serious risk.
Further Information and Manual Repair
To fix the error AVFoundationCF.dll on your PC, here are some of the best and easy to do solutions that you can try:
Check your Recycle Bin
Since dll files are shared files, there is a possibility that this file accidentally got deleted when you were uninstalling some other program on your system. If you experience missing AVFoundationCF dll file error message after performing any program on your PC, then chances are that it got deleted and maybe in your recycle bin.
So, first, check your recycle bin and search for the dll file. If you find it, restore it to fix the error.
Update Device Driver
To resolve the issue, try performing a driver update.
This can be done by downloading the latest drivers from the hardware manufacturer’s website. Now open Device Manager from the Control Panel and locate the hardware device that you want to update the driver for.
Once you find the hardware you are updating the driver for, right-click on the hardware icon and choose properties. In the properties windows, click the driver tab. Now click the update driver button. To activate changes, restart your PC.
To automatically update your computer's drivers when necessary,
download and install DriverFIX.
Try Re-installing Apple iTunes Program
To do this, simply go to the control panel, select programs and then uninstall a program and then select iTunes. Uninstall it and then repeat the same program and install the Apple iTunes program again on your PC by downloading the program from Apple’s official website.
Scan for Viruses
If the error still persists, then it is advisable to scan your PC for viruses. This can be easily done by running a powerful antivirus on your PC. However, please note anti-viruses are notorious for slowing down PC performance. So, may have to compromise on the
speed of your system.
Clean and Repair the Registry
If the error is caused by invalid and corrupt registry entries and damaged Avfoundationcf dll file, then the best way to resolve is to download a powerful registry cleaner.
We advise you to install Restoro on your PC. This is an advanced and a multi-functional PC Fixer integrated with multiple powerful utilities including a high functional registry cleaner, an antivirus and a system optimizer.
The registry cleaning utility scans all the registry issues and removes all errors triggered by the registry immediately.
It cleans the registry by wiping out all the unnecessary, obsolete and redundant files including invalid entries and bad registry keys. Furthermore, it also fixes the damaged and corrupt dll files including Avfoundationcf dll file. Thereby resolving the error right away.
Furthermore, the antivirus deployed in this software scans for all types of malicious codes like viruses, Trojans, spyware, and malware and removes them. To ensure you don’t compromise on your PC performance, it is deployed with a system optimizer utility that boosts the speed of your computer dramatically.
This tool is bug free, has a user-friendly interface and compatible with all Windows versions.
Click here to download Restoro and resolve Avfoundationcf.dll error on your PC today!
 Once it opens, click on Device Manager to open it,
If you have a driver device error inside Windows, you should see it immediately when entering the Device Manager, it will have a yellow exclamation mark beside it. Right-click on it and choose update driver.
Once it opens, click on Device Manager to open it,
If you have a driver device error inside Windows, you should see it immediately when entering the Device Manager, it will have a yellow exclamation mark beside it. Right-click on it and choose update driver.
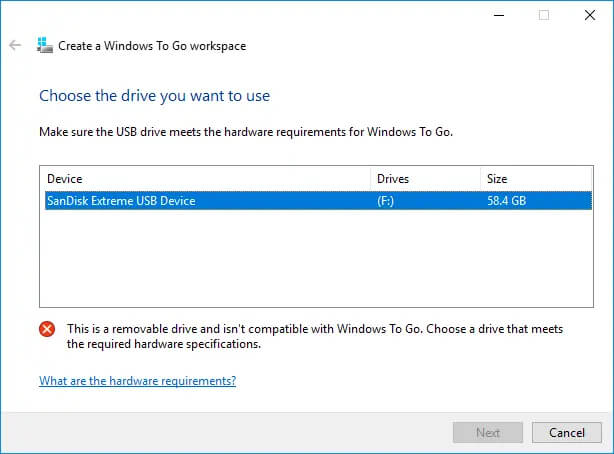 Many Linux users if not all of them can run their distros from a USB drive but did you know you can run Windows 10 from a USB drive as well?
Microsoft has introduced all the way back to Windows 8 one feature called Windows To Go and it kept it in Windows 8.1 and in Windows 10 as well.
This feature is intended as a convenient way for workers to carry their corporate environments with them, but having your own copy of Windows on a thumb drive could be handy for backup purposes, too, or if you frequently use public machines that lack your preferences/applications or that have a restricted OS.
Many Linux users if not all of them can run their distros from a USB drive but did you know you can run Windows 10 from a USB drive as well?
Microsoft has introduced all the way back to Windows 8 one feature called Windows To Go and it kept it in Windows 8.1 and in Windows 10 as well.
This feature is intended as a convenient way for workers to carry their corporate environments with them, but having your own copy of Windows on a thumb drive could be handy for backup purposes, too, or if you frequently use public machines that lack your preferences/applications or that have a restricted OS.


