What is Search.schooldozer.com? And how does it function?
Search.schooldozer.com is a browser extension that functions as a search engine. It is developed and maintained by “Schooldozer”. It claims to improve users’ browsing experience by providing them with improved search results. However, it does not really do the things it claims to do. In fact, they’re quite the opposite ones – instead of improving the browsing experience, it makes users’ browsing experience unsafe and full of sponsored content. This is in contrast to what it states in its Privacy Policy:
“Install applications the easy way and without the hassle, using the Schooldozer downloader. The Schooldozer platform stems from years of experience with installing applications, resulting in a highly optimized process, yielding faster downloads, better user experience, and more successful installations.”
In addition, once installed Search.schooldozer.com is installed, it will change the default settings of a browser such as the default search engine, homepage, and new tab page. This is why security experts regard this browser extension as a browser hijacker and a potentially unwanted program. The modification of the browser's settings allows it to control users’ browsing by redirecting them to sponsored sites as well as deliver sponsored content from its affiliated sites in order to gain profit via pay-per-click marketing. And if you think that the ads it displays are harmless, think again for some of these ads can redirect you to suspicious websites that might contain harmful content. What’s more is that this browser hijacker can also keep track and monitor all your browsing activities in order to obtain your browsing data like search queries, what sites you always visit, browsing history, browser type, OS version, and so on. The information collected is then used and may even be shared with its affiliated third parties to deliver more customized and personalized advertisements.
How is Search.schooldozer.com distributed over the web?
Like a typical browser hijacker, Search.schooldozer.com is distributed using the software bundling method where several unknown and unwanted programs are bundled in a software package. Thus when you install any software bundle, make sure to always opt for the Custom or Advanced installation setup rather than the quick setup to avoid installing unwanted programs like Search.schooldozer.com.
To remove Search.schooldozer.com from your computer, follow the removal guide below carefully.
Step 1: Start the removal process by closing all the browsers infected with Search.schooldozer.com. If you’re having a hard time closing them, you can close them using the Task Manager just tap on Ctrl + Shift + Esc.
Step 2: After you open the Task Manager, go to the Processes tab and look for the infected browser’s process and end it.
Step 3: Then close the Task Manager and tap the Win + R keys to open Run and then type in appwiz.cpl to open Programs & Features in Control Panel.
Step 4: From there, look for Search.schooldozer.com or any unfamiliar program that could be related to it under the list of installed programs and once you’ve found it, uninstall it.
Step 5: Edit your Hosts File.
- Tap the Win + R keys to open then type in %WinDir% and then click OK.
- Go to System32/drivers/etc.
- Open the host file using Notepad.
- Delete all the entries that contain Search.schooldozer.com.
- After that, save the changes you’ve made and close the file.
Step 6: Reset all your browsers to default to their default state.
Google Chrome
- Launch Google Chrome, press Alt + F, move to More tools, and click Extensions.
- Look for Search.schooldozer.com or any other unwanted add-ons, click the Recycle Bin button, and choose Remove.
- Restart Google Chrome, then tap Alt + F, and select Settings.
- Navigate to the On Startup section at the bottom.
- Select “Open a specific page or set of pages”.
- Click the More actions button next to the hijacker and click Remove.
Mozilla Firefox
- Open the browser and tap Ctrl + Shift + A to access the Add-ons Manager.
- In the Extensions, menu Remove the unwanted extension.
- Restart the browser and tap keys Alt + T.
- Select Options and then move to the General menu.
- Overwrite the URL in the Home Page section and then restart the browser.
Internet Explorer
- Launch Internet Explorer.
- Tap Alt + T and select Internet options.
- Click the General tab and then overwrite the URL under the homepage section.
- Click OK to save the changes.
Step 7: Hold down Windows + E keys simultaneously to open File Explorer.
Step 8: Navigate to the following directories and look for suspicious files associated to the browser hijacker such as the software bundle it came with and delete it/them.
- %USERPROFILE%Downloads
- %USERPROFILE%Desktop
- %TEMP%
Step 9: Close the File Explorer.
Step 10: Empty the contents of Recycle Bin.


































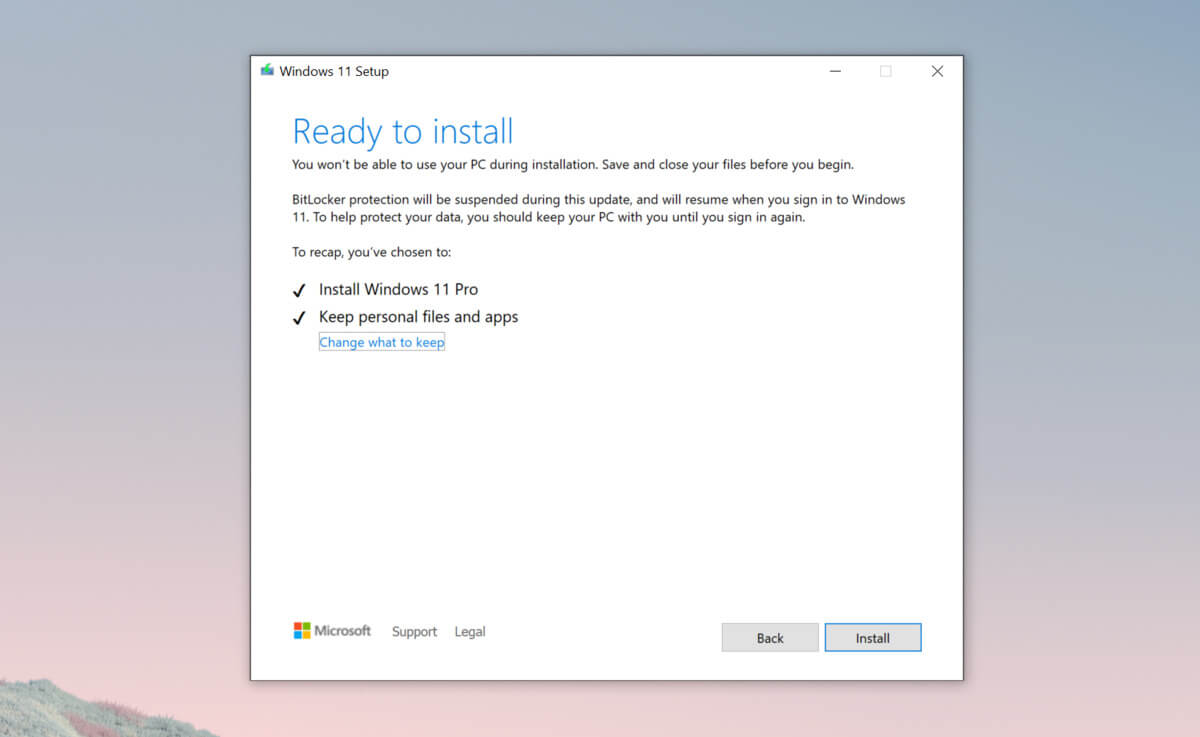 Bypass TPM with changing installation media
Bypass TPM with changing installation media