As you know, the Graphics Card in a computer is one of the important components in an operating system as they are responsible for rendering various objects in your computer. However, there are cases when the performance of this rendering can degrade and your computer can trigger a VIDEO_SCHEDULER_INTERNAL_ERROR Blue Screen of Death error instead.
The VIDEO_SCHEDULER_INTERNAL_ERROR bug check has a value of 0x00000119 which means that the video scheduler has detected a fatal violation in your computer. Before you troubleshoot the problem, you might want to perform System Restore first as it might help you fix the Stop error. To perform System Restore, refer to these steps:
If the VIDEO_SCHEDULER_INTERNAL_ERROR BSOD error is still not fixed after System Restore, then follow the given options below to further troubleshoot the problem.
You might also want to check the physical status of your Graphics card and you can do this by disconnecting the Graphics card or any other external device connected to your computer. Once you’ve removed the external device, check it for any damages. If there’s none, connect it back to your computer and check if the VIDEO_SCHEDULER_INTERNAL_ERROR Blue Screen error is fixed or not.
If you have recently installed some hardware or drivers, you might want to disable or remove them since external devices are proven to be one of the factors that trigger Blue Screen errors like VIDEO_SCHEDULER_INTERNAL_ERROR. All you have to do is physically disconnect any external devices that are connected to your computer and then check if it fixes the BSOD error or not.
Since the VIDEO_SCHEDULER_INTERNAL_ERROR Blue Screen error has something to do with Graphics card drivers, you can either roll back, update or disable them depending on your preference in order to resolve the error.
Note: You also have the option to go directly to the website of your graphics card manufacturers like NVIDIA, Intel, or AMD and go to the section called Drivers then check if there’s a new available update – if there is, download and install it.
You can also uninstall any faulty drivers via Device Manager. How? Refer to these steps:
As you know, the Blue Screen troubleshooter is a built-in tool in Windows 10 that helps users in fixing BSOD errors like the VIDEO_SCHEDULER_INTERNAL_ERROR error. It can be found in the Settings Troubleshooters page. To use it, refer to these steps:

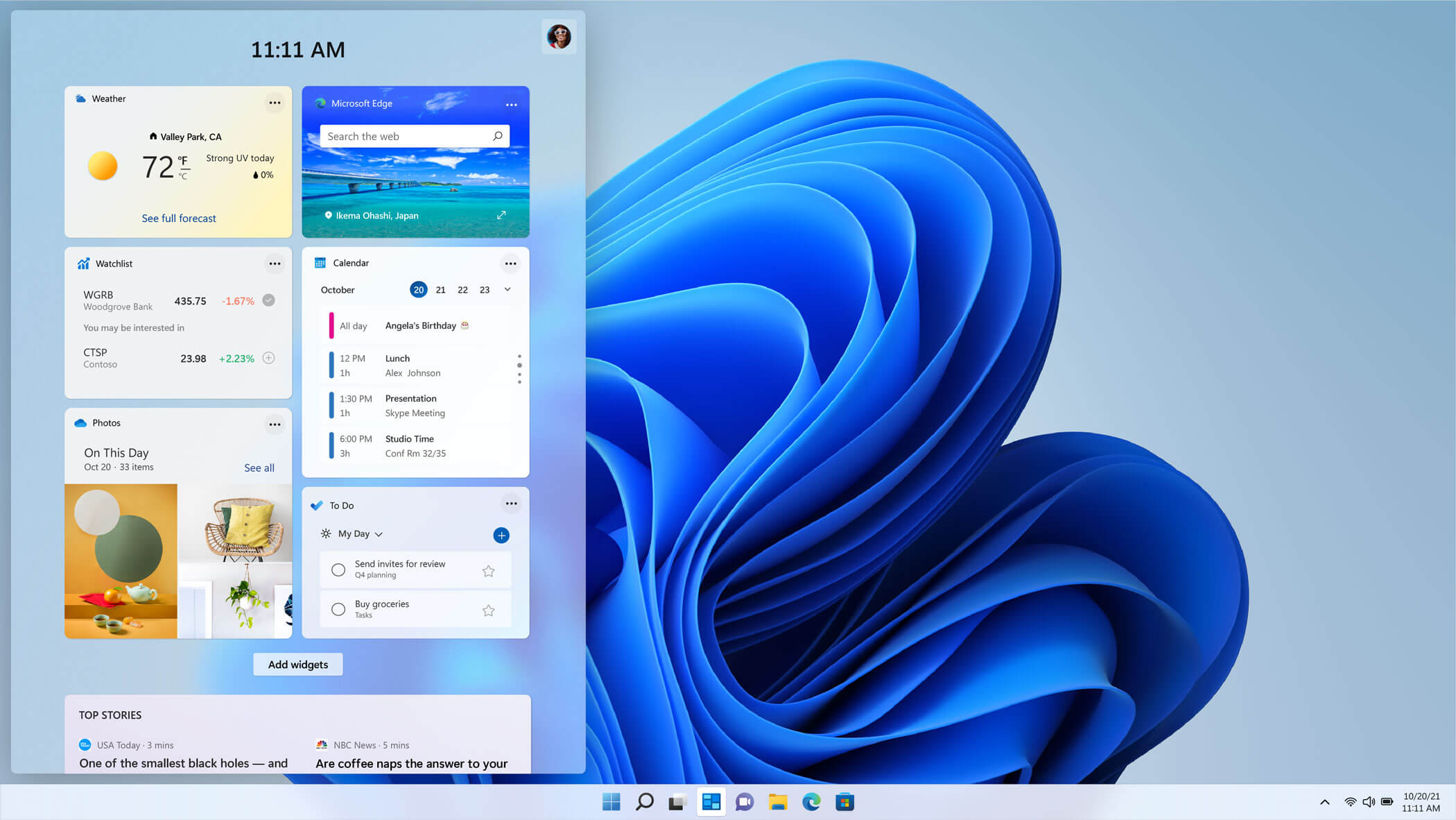 The new widget's menu inside Windows 11 is generally met with a positive attitude but there are still users which prefer not to have it. Luckily for them, Microsoft included a very easy way to turn the widgets menu on or off. Follow this easy guide to see how.
Right-click on the widget button in the taskbar and click on Hide from Taskbar and that’s it
Alternatively, you can also turn it off via the setting app.
Go to the settings app and navigate to Personalization > Taskbar > Taskbar Items and flipping the switch beside Widgets to Off.
Please note that both methods will only hide the button to toggle widgets menu, at the current state there is no really a way to actually turn it off, only hide it and make it not available to bring it up.
The new widget's menu inside Windows 11 is generally met with a positive attitude but there are still users which prefer not to have it. Luckily for them, Microsoft included a very easy way to turn the widgets menu on or off. Follow this easy guide to see how.
Right-click on the widget button in the taskbar and click on Hide from Taskbar and that’s it
Alternatively, you can also turn it off via the setting app.
Go to the settings app and navigate to Personalization > Taskbar > Taskbar Items and flipping the switch beside Widgets to Off.
Please note that both methods will only hide the button to toggle widgets menu, at the current state there is no really a way to actually turn it off, only hide it and make it not available to bring it up.  Error Causes
Error CausesError 17: Spotify has encountered a problem and needs to close. We are sorry for the inconvenience. Spotify could not be started (Error code 17)Some of the symptoms of this error code are program crash, slow Windows performance, and periodic system freeze.
 Error Causes
Error CausesStarted as an internal network and has slowly expanded since 1960 internet has taken over the world. In the beginning, it was a means of information change but in the modern age you can run applications and virtual machines over the internet, you can stream video and audio, and you can communicate in real-time with someone on the other side of Earth.
With the internet growing so fast in such a small amount of time it is only logical and wise to take a step back and take a good look at what it offers now, what are great things about it and what are some of the worst.

There are a lot of advantages of the internet, first and foremost is information. Internet was made as an information exchange service and even today you can find a lot of various information about various topics that interest you. A site like Wikipedia is a completely free online encyclopedia and a lot of news companies have their own internet sites where you can find free information and news.
On the other hand, there are also websites like udemy, edx, Coursera, and many others that will offer you the education, some for free, some for money but you can get a glimpse and part of university quality education for just a fraction of price.
Sites like Amazon have used the internet and launched themselves as today's multi-billion companies. In today's world, there is not a single thing you can not buy online. Many sites today are going from the large online marketplace where you can find everything to small niche specialized ones. Also every major brand in the world today has its own online store.
Other shops will offer you music, movies, games, etc. Services like steam, xbox pass, sony pass etc, will let you buy games online, other music, movies, and many more.
Days, when you had to buy movies in order to watch them at home, are gone, thanks to the internet we have plenty of streaming services for movies and tv shows as well as ones for music. If you do not want to spend money on actually purchasing things then a good idea is to have a streaming plan set up when you want it.
Communication is a great thing and since the dawn of mankind people have been talking and sharing with each other, the internet has made it possible to send mail electronically and instantly and modern chat communication is everywhere. We can not just talk with our friends and family that can be on the other side of the world, we can also talk in real-time with the sales representative, with technical service, or attend online classes with a group of people.
Saving your pictures in this digital media age on the hard drive can be risky but thanks to modern technologies you can save most of your precious files on cloud servers for safekeeping. From pictures to documents and even other files that you need and want to save. There are some of them that will offer you a free amount and some basic free plans as well.
We could not talk about the bad side of the internet if we do not mention its greatest threat. Bad sites, infected software, phishing emails, and many more malicious threats. Problem is that these kinds of tricks and attacks have become more and more sophisticated and harder to detect and avoid.
Pornography is bad, having it freely available to children is even worse. Sadly the only way to regulate this is on a computer-by-computer basis by turning on parent control on each one. There are many studies that go into detail about why this is bad, sadly currently there are no effective ways to isolate this content.
When we say there is no privacy we do not mean by using social media and not setting your privacy settings altho that also fits in this point, what we are talking about is data mining of your habits and things you do. It is well known that today lot of websites are using some form of AI recommender system in order to tailor your internet experience to suit your needs better. Most of these AI systems are trained by mining your data and analyzing your habits.
If you have 2 google accounts there is a high probability chance that for the same query you will get different results, depending on your so far browsing habits. The same goes for other services as well.
There are some great things in dark and deep WEB-like sites with true news and information. Even some legit libraries where you can find and download rare books. Sadly as goes with the internet dark and deep WEB also has its well, dark sides, from disturbing content to shops that sell stolen items to straight stealing your money by parading as legit shops but only to steal your money.
We all try to find someone that is perfectly matched with us but using the online dating site has many proven bad effects on psychology. It also devaluates interaction between people and can lower self-esteem.
Since the internet has become wildly available and popular on various devices like tablets and mobile phones more and more people are spending an unhealthy amount of time on it. Harvesting the benefits of the internet is great but find some time for other people as well.
22H2 update for Windows 11 will arrive later this year and although Microsoft is not releasing anything big there will be some interesting improvements and fixes. We take a look at some that caught our attention.

One of the most interesting upcoming features is enhanced phishing protection. Microsoft Defender SmartScreen will be upgraded to alert users when they try to store passwords in plain text files and also if they accidentally type in a Microsoft account password on phishing sites.
"These enhancements will make Windows the world's first operating system with phishing safeguards built directly into the platform and shipped out of the box to help users stay productive and secure without having to learn to be their own IT department,"
Microsoft
Finally, Windows File explorer is getting tabs that will allow much easier management of folders and files inside it.
It is confirmed that Microsoft is also working on a new 'HOME' sidebar that should be modern in design and in features including OneDrive so you can find everything in one place.
Pinning of favorite files was also mentioned so you can easily pin favorites for quick access.
Windows 11 has brought back widgets in a new way and from all the feedback users are loving them. Currently, you have a widget sidebar on the left part of the screen where you have your chosen store widgets but from the Microsoft teaser, we will have soon the option to have them in full screen.
If you are using a widget for reading news, blogs, etc. this feature will be very good since you will be able to use your whole screen for information and not just a part of it.
Another new feature is 'suggested actions' which is going to be particularly useful in apps like Microsoft Teams. With this new feature, you can highlight a date in a Teams message and Windows will suggest actions.
For example, if you highlight a date, you'll see a recommendation to create an event in Microsoft Calendar for that day.
"Error Code 0x80070057: The parameter is wrong"When this problem happens, you will end up struggling to move private documents from one person to another.
 Error Causes
Error Causes"An Internal Error has occurred. Incorrect parameters".If this happens to you, realize that you are dealing with malfunction code 0x80070057. This error occurs mostly when you are trying to build a full backup of your Windows 7 OS.
 Error Causes
Error Causes