If when trying to start Autodesk applications you receive a Network license not available error then please keep on reading, this guide is for you:
Solutions for the error:
Verify that the Autodesk License Server is setup with the correct license file.
To set up a license server for Windows, perform the following:
- Download and install the Network License Manager for Windows:
- Open LMTools and access the System Settings tab. Make a note of the "hostname" and "ethernet address" of the license server.
- Generate a Network License File in Autodesk Account.
- On the Service/License tab, select Configuration Using Services and LMTOOLS ignores license file path environment variables.
- On the Config Services tab, enter a name for the new service in the Service Name field.
- Fill the following fields, using the Browse buttons:
- Path to the lmgrd.exe - Navigate to this file: C:\Autodesk\Network License Manager.
- Path to the License file - Navigate to the new Autodesk.lic file, typically placed in: C:\Autodesk\Network License Manager\Licenses.
- Path to the Debug Log file: C:\Autodesk\Network License Manager.
- If no file is present, create a TXT file in Notepad and rename it “Debug.log.”
- Make sure the "Start Server at Power Up" and the "Use Services" boxes are checked. Then click Save Services.
- On the Start/Stop/Reread tab, click Start Server.
- On the Server Status tab, click Perform Status Enquiry.
- Licenses should display as active.
How to set up the Autodesk Network License Manager on a Mac.
Note: The Autodesk License Server Manager (version 11.16.2.0) is supported only on the following Mac operating systems:
- Apple macOS High Sierra 10.13
- Apple macOS Sierra 10.12
- Apple Mac OS X El Capitan 10.11
- Download Autodesk Network License Manager version 11.16.2.0 for Mac
- Download the nlm11.16.2.0_ipv4_ipv6_mac_universal.tar.gz file to the Desktop.
- To install the Autodesk Network License Manager:
- Double click on nlm11.16.2.0_ipv4_ipv6_mac_universal.tar.gz to unpack the installer package.
- After unpacking nlm11.16.2.0_ipv4_ipv6_mac_universal.pkg, will be /Downloads/adlm/FLEXnet folder.
- Double click on nlm11.16.2.0_ipv4_ipv6_mac_universal.pkg to start installation and follow the installation wizard.
- The license server will be installed in /usr/local/flexnetserver/ directory.
- Change permissions for /usr/local/flexnetserver/ directory to 777
- Open Terminal (located in /Applications/Utilities/Terminal) and enter the following command:
sudo chmod -R 777 /usr/local/flexnetserver
- Note: Administrator password may be asked. While typing no characters are shown, just type out the password and hit return key.
- Note: To start the license server only with elevated permissions (using sudo command), change permissions to 755 instead of 777.
- Create /usr/local/flexnetserver/licenses directory for network license file location
sudo mkdir /usr/local/flexnetserver/licenses
- Find the license server Host Name and Host ID.
- Generate the Network License File in the Autodesk Account
- Once the license file is generated, make sure it has a .lic extension (e.g. adsk_license.lic) and is in a plain text format and place it in /usr/local/flexnetserver/licenses directory
Note: In this article we will refer to adsk_license.lic as network license file name. Feel free to change the actual name of the license file, but make sure to reflect the new name when using the commands below.
- Create a debug.log file in the /usr/local/flexnetserver/ directory using the following command:
- To start the Network License Server use the following command:
/usr/local/flexnetserver/lmgrd -c /usr/local/flexnetserver/licenses/adsk_license.lic -l /usr/local/flexnetserver/debug.log
Note: If folder permissions for /usr/local/flexnetserver/ are set to 775, then use sudo command to start the server. For example:
sudo /usr/local/flexnetserver/lmgrd -c /usr/local/flexnetserver/licenses/adsk_license.lic -l /usr/local/flexnetserver/debug.log
- To obtain license server status enquiry:
/usr/local/flexnetserver/lmutil lmstat -a -c /usr/local/flexnetserver/licenses/adsk_license.lic
- To stop the license server:
/usr/local/flexnetserver/lmutil lmdown -q -force
- Alternatively, run ps command to obtain process ids for lmgrd and adskflex and then kill those processes:
ps -ax | grep lmgrd
ps -ax | grep adskflex
kill -9
- (provide process ids obtained by previous commands individually)
How to set up the Autodesk Network License Manager on Linux.
Note: The Autodesk License Manager (11.16.2.0) is supported only on the following Linux distros:
- Red Hat® Enterprise Linux® 7
- Red Hat Enterprise Linux 6
- SUSE Linux Enterprise 12
- SUSE Linux Enterprise 11
To configure the license manager use the following steps:
- Download Autodesk Network License Manager v. 11.16.2 for Linux from this link
- Download the nlm11.16.2.0_ipv4_ipv6_linux64.tar.gz file to your desktop.
- To install the Autodesk Network License Manager run following command as root.
- tar –zxvf nlm11.16.2.0_ipv4_ipv6_linux64.tar.gz
- rpm -vhi nlm11.16.2.0_ipv4_ipv6_linux64.rpm
- The license server will be installed in /opt/flexnetserver/ directory.
- Find the license server Host Name and Host ID
- To obtain the license server system hostid run the following command
/opt/flexnetserver/lmutil lmhostid
From the command output note the hostid in quotes, if the system has two active NIC cards, select the first MAC address.
lmutil - Copyright (c) 1989-2018 Flexera. All Rights Reserved.
The FlexNet host ID of this machine is "000c297949e0"
- To obtain the license server system hostname run the following command
/opt/flexnetserver/lmutil lmhostid hostname
From the command output note the hostname of the license server.
mutil - Copyright (c) 1989-2018 Flexera. All Rights Reserved.
The FlexNet host ID of this machine is "HOSTNAME=Centos7.localdomain"
- Generate your Network License File in Autodesk Account
- Once the license file is generated, make sure it has .lic extension (e.g. adsk_license.lic) and place it in /opt/flexnetserver/licenses directory. If the directory doesn't exits, create it with this command: sudo mkdir /opt/flexnetserver/licenses
Note: in this article we will refer by adsk_license.lic your network license file name.
- To start the Network License Server
- /opt/flexnetserver/lmgrd -c /opt/flexnetserver/licenses/adsk_license.lic -l /opt/flexnetserver/server_log.log
- To obtain license server status enquiry
- /opt/flexnetserver/lmutil lmstat -a -c /opt/flexnetserver/licenses/adsk_license.lic
- To stop your license server service
- /opt/flexnetserver/lmutil lmdown -q -force
- alternatively you can also run ps command to obtain process ids for lmgrd and adskflex and then kill those processes
- ps -aw | grep lmgrd
- ps -aw | grep adskflex
- kill -9 (provide process ids obtained by previous commands individually)
- To start the license server automatically after the system reboot
- Open /etc/rc.d/rc.local script as root and enter license server start up command in it.
touch /var/lock/subsys/local
/opt/flexnetserver/lmgrd -c /opt/flexnetserver/licenses/adsk_license.lic -l /opt/flexnetserver/server_log.logNote: To ensure that the script will be executed during boot, run following command as root.
chmod +x /etc/rc.d/rc.local
- Make sure that all necessary ports are open:
- lmgrd.exe needs ports 27000 to 27009.
- adskflex.exe needs port 2080.
Note: Errors may occur if the network license file is corrupt or in the case of a combined network license it has incorrectly combined licenses. To learn more about combining licenses, see Combining License Files for Multiple Autodesk Products. Use the
License File Parser to verify that the license contains the appropriate products and
FLEXnet feature codes and does not display an error
Verify that TCP ports (2080, 27000-27009) used by Autodesk Network License Manager are not blocked by Firewall.
The FLEXlm® based version uses the following incoming ports:
- TCP ports 2080 (for the adskflex vendor daemon)
- TCP ports 27000 to 27009 (for the lmgrd master daemon, which uses the first open port in the range)
Note: If these port addresses are restricted by a router or firewall software, users on the remote side of the router will not have access to licenses controlled by the Network License Manager.
Verify that the client computer is configured with the correct license server name or IP.
Windows:
Clear license server information from the system registry.
- Type regedit in the Windows Search box and hit Enter key.
- Select the following registry key
- [HKEY_CURRENT_USER\SOFTWARE\FLEXlm License Manager]
- As the key is selected, in right panel ADSKFLEX_LICENSE_FILE will be visible.
- Right click on the key and delete it.
Specify the license server in ADSKFLEX_LICENSE_FILE system variable
- Go to Start > Control Panel > System and Security > System.
- Select Advanced system settings.
- On the System Properties dialog, click Environment Variables.
- Under System Variables, click New.
- Enter ADSKFLEX_LICENSE_FILE for the variable name and 2080@SERVER_NAME _OR _IP for the variable value.
Note: the license server information most often is recorded in LICPATH.lic file and can be verified there too. ADSKFLEX_LICENSE_FILE system variable supersedes LICPATH.lic. Thus, setting the system variable is preferable when this error is seen.
If the license server is on a VPN or a remote network set the FLEXLM_TIMEOUT environment variable:
- Go to Start > Control Panel > System and Security > System.
- Select Advanced system settings.
- On the System Properties dialog, click Environment Variables.
- Under System Variables, click New.
- Enter FLEXLM_TIMEOUT for the variable name and 5000000 for the variable value.
- Click OK to save the setting.
Note: if needed the variable value can be increased to 10000000.
Mac/Linux:
Specify the Autodesk Network License server information in $HOME/.flexlmrc file.
Use a text editor to create a flexlmrc.txt file and save it in Plain text format (In TextEdit on Mac: Format - Make Plain Text) on desktop.
The file content should look like this, except with the name or IP address of the license server.
- ADSKFLEX_LICENSE_FILE=@SERVER_NAME _OR _IP
If the license server is on the same machine as the Autodesk software, use localhost as the license server name. Thus, the content of flexlmrc file could look like this:
- ADSKFLEX_LICENSE_FILE=@localhost
Note: On firewall restricted network or when accessing the license server via VPN, need to include TCP port/s (usually 27000 or 2080) into Autodesk License Server service as follows: ADSKFLEX_LICENSE_FILE=2080@SERVER_NAME _OR _IP
Once flexlmrc file is created move it to user's $HOME folder as follows:
- Open a Terminal window
- Type open ~ (Mac) or nautilus ~ (Linux) to open $HOME folder
- Drag and drop flexlmrc.txt file from Desktop to the home folder.
- To make the file a configuration file, rename it to .flexlmrc (please note . [DOT] in front of the file name) by running the following command:
- mv flexlmrc.txt .flexlmrc (Mac)
- mv flexlmrc .flexlmrc (Linux)
Verify that the license server information registered with the product is correct (versions 2020 and later only)
In versions 2020 and later, the license server information is registered with the AdskLicensing service running locally on the workstation. When changing to a new license server, the old server information may still be registered with
AdskLicensing and result in the error above, if this is not appropriately updated.
See the below steps to solve this:
- Click the Start menu and type cmd.
- Right-click on the Command prompt and choose "Run As Administrator."
- In the Command prompt, run the following command, followed by ENTER:
"C:\Program Files (x86)\Common Files\Autodesk Shared\AdskLicensing\Current\helper\AdskLicensingInstHelper.exe" change -pk PRODKEY -pv VER.0.0.F -lm "" -ls "" -lt""
Note:
- Replace PRODKEY with the product key correspondent to your product(s). See Look Up Product Keys for the full list.
- Replace VER with the version you are using. E.g. 2020 for AutoCAD 2020.
- Repeat this step for each software you need to reset.
- Open Registry Editor (Start > type regedit > ENTER).
- Navigate to HKEY_CURRENT_USER\Software\FLEXlm License Manager.
- On the right-side, verify of the ADSKFLEX_LICENSE_FILE key exists. If yes, remove it (right-click > Delete).
- Run the software again.
- Select Multi-user in the Let's Get Started screen.
- Follow the steps to connect to your license server.


 Hacker group recently came up with claims that they have stolen data from 100 million T-Mobile customers. T-Mobile has responded with confirmation it has been compromised and that over 40 million records were stolen, among them are not just present customers, but anyone who has applied for T-Mobile service as well as past accounts.
Hacker group recently came up with claims that they have stolen data from 100 million T-Mobile customers. T-Mobile has responded with confirmation it has been compromised and that over 40 million records were stolen, among them are not just present customers, but anyone who has applied for T-Mobile service as well as past accounts.
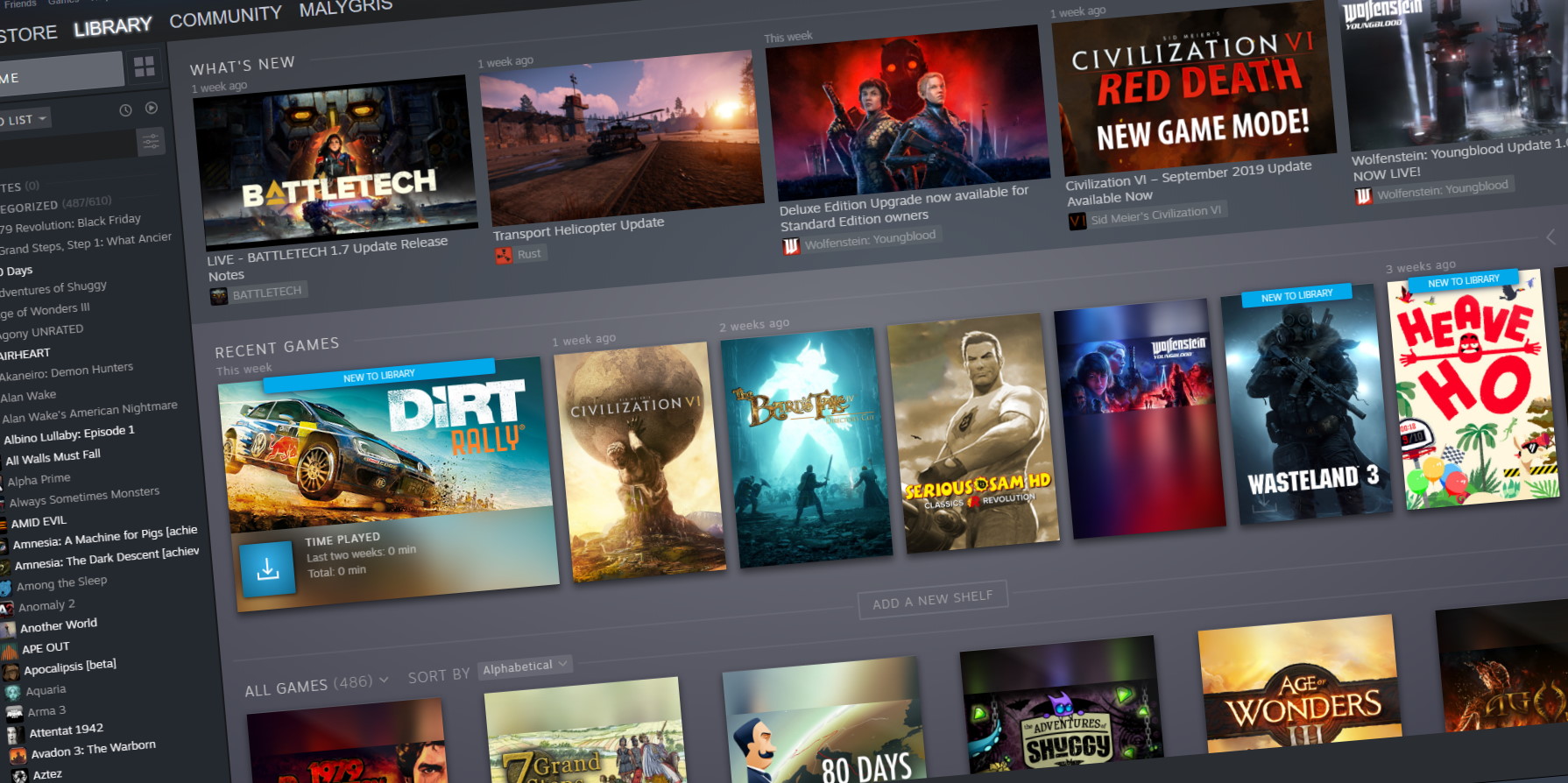 Well, you can and it is not complicated as well. Follow this easy guide to see how can you get someone’s account up and running with some of your games.
Well, you can and it is not complicated as well. Follow this easy guide to see how can you get someone’s account up and running with some of your games.
