Not a Valid Win32 Application Error - What is it?
Not a Valid Win32 Application error code that indicates either the file or the program you are attempting to run missing or corrupt. And because of this error, Windows is unable to open your desired file or run the program successfully.
Error Causes
The ‘Not a Valid Win32 Application’ is triggered due to multiple reasons such as:
- Unsuccessful program installation due to damaged disc/CD
- Corrupted or incompatible file
- The hard drive is loaded with bad and invalid entries
- Malware invasion or viral infection
When you come across this error code on your PC, it is advisable to resolve it as it will cause you a great deal of inconvenience hampering program and file accessibility.
Furthermore, if the error code occurs due to malware or viruses, then it can lead to severe data security threats and privacy issues.
Further Information and Manual Repair
To resolve the Not a Valid Win32 Application error on your PC, you don’t need to be a technical expert or hire a professional. Though this error might be crucial it is easy to fix.
Here are some of the many methods that you can try to resolve this error code on your PC:
- Check for File Compatibility
If you downloaded a file that is not compatible with your Windows version then you will come across this error. In this case, it is advisable to download the file version that is compatible and can run easily on the Windows version installed on your system.
Nonetheless, if the file is compatible but still doesn’t run on your PC, then it’s possible that the file became corrupt during the download.
Try downloading the file again.
You may also come across the Not a valid Win32 application error code if the program installation from the CD is unsuccessful.
This happens when the CD is dirty or it is scratched. The program does not copy properly onto the computer from the damaged CD. So, if the CD is scratched and dirty, buy a new CD and try installing the program again.
- Verify the Program You Want to Run is Still on the Computer
If you are running the program from a shortcut, then verify that the program is still installed on your PC. This error may occur if the program is no longer installed on the computer.
If you find the program is not installed on your system, then reinstall and try running the program again.
Make sure the program or the file you are attempting to run on your system does not contain the same name as the long filename directory it is saved in. For example, running a file named ‘program’ in the ‘program files’ directory can cause errors in some Windows versions.
If this is the issue, then try installing the program in a different directory.
If the hard drive is bad or corrupted, it can also generate the not a valid Win32 application. And because of this error files and programs fail to execute successfully as not all data can be read from the hard drive.
To repair this issue first you need to run defrag and ScanDisk Microsoft built-in tools. These tools check for errors on the hard drive.
If the error code occurs due to a viral infection or malware attack on your system, then you must download an antivirus, scan, and remove such malicious software. However, antivirus may slow down the speed of your PC.
So, to resolve speed issues and boost the performance of your system, you may have to download a system optimizer.
 Since this requires registry tweak, please follow given solution step by step
Since this requires registry tweak, please follow given solution step by step

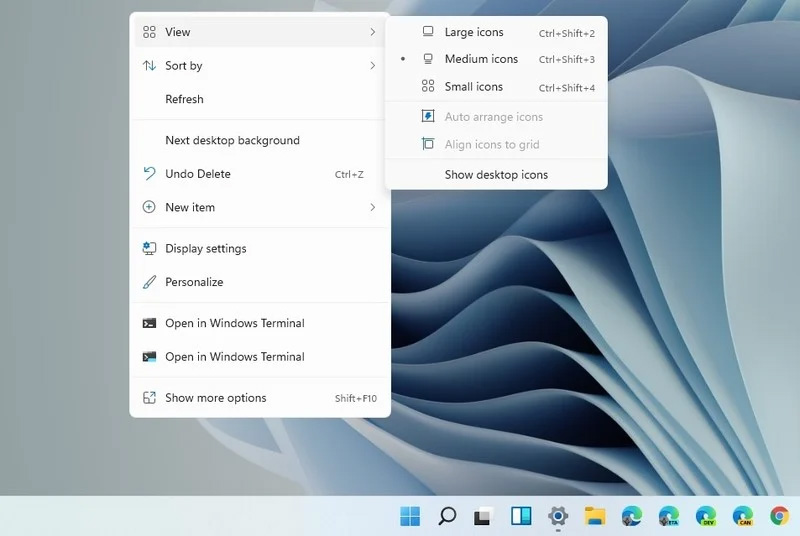
 Microsoft has released Windows 11 as a public beta release for all the people that are not willing to be in the insider program.
Beta release as of this moment is identical to Insider Preview build 22000.100. and updates will not roll so fast as in insider preview and it is marked as unstable release, same as insider build.
I would not install Windows 11 beta on the main PC since some drivers still have issues and may lead to some blue screens.
Be aware that the beta build will have all Windows 11 system requirements including TPM 2.0. This is a big difference from insider build which can be installed on systems lacking official requirements.
So basically if you have a spare PC that could run Windows 11 install it so you can see what it brings and feel it so you can make a decision will upgrade once it is released later this year.
Microsoft has released Windows 11 as a public beta release for all the people that are not willing to be in the insider program.
Beta release as of this moment is identical to Insider Preview build 22000.100. and updates will not roll so fast as in insider preview and it is marked as unstable release, same as insider build.
I would not install Windows 11 beta on the main PC since some drivers still have issues and may lead to some blue screens.
Be aware that the beta build will have all Windows 11 system requirements including TPM 2.0. This is a big difference from insider build which can be installed on systems lacking official requirements.
So basically if you have a spare PC that could run Windows 11 install it so you can see what it brings and feel it so you can make a decision will upgrade once it is released later this year. 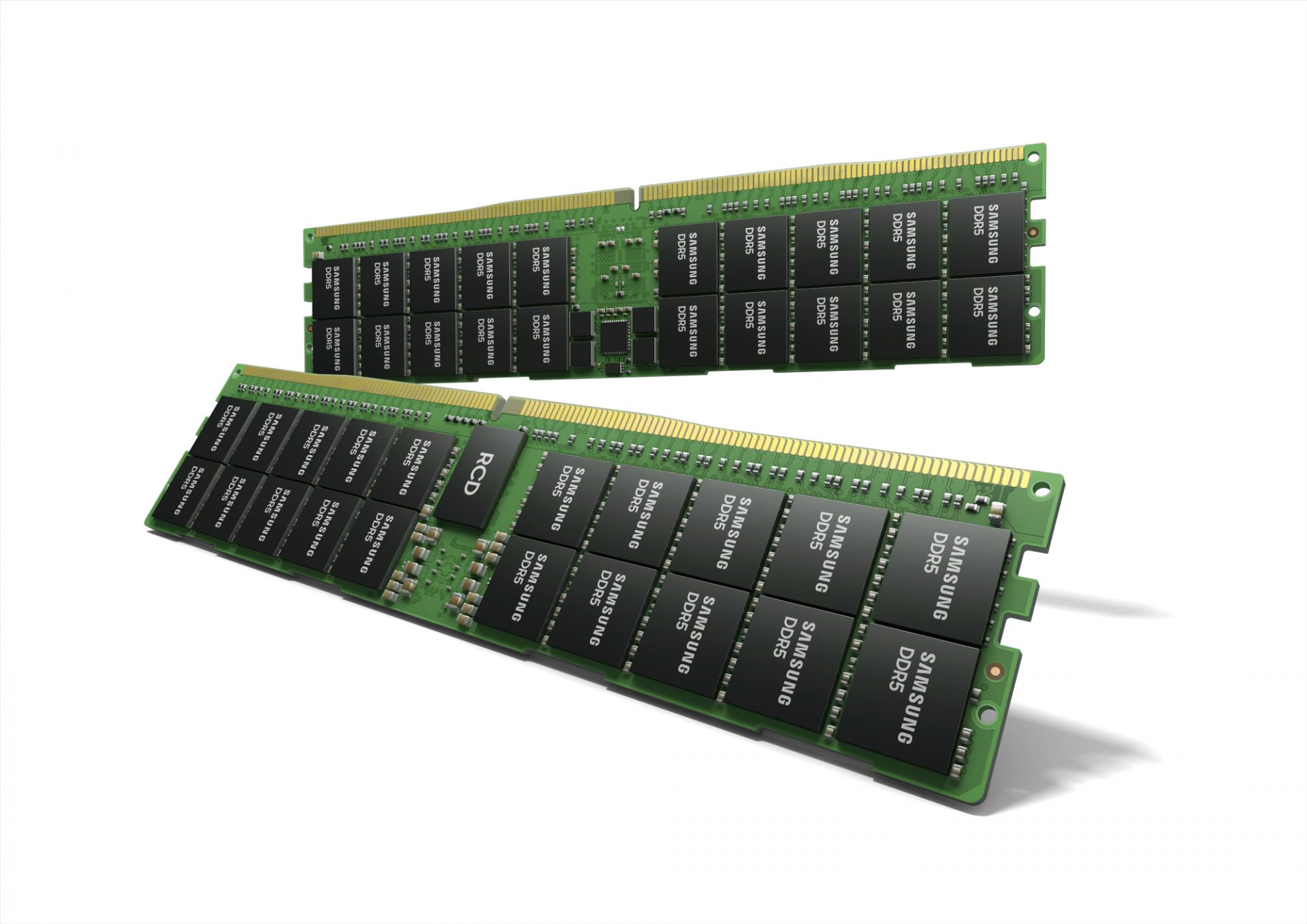 Next-generation of RAM, DDR5 supposed to hit shelves around late summer or fall in 2021if everything goes as planned.
Its goal is to increase speed and efficiency, wants to pack more memory in a single stick, and have better power management.
Next-generation of RAM, DDR5 supposed to hit shelves around late summer or fall in 2021if everything goes as planned.
Its goal is to increase speed and efficiency, wants to pack more memory in a single stick, and have better power management.


