If you receive an error message that says, “Entry point not found, The procedure entry point could not be located in the dynamic link library” on your Windows 10 PC, then you will find this post useful for this will provide you some potential fixes to fix the error.
This kind of error can occur if a program fails to locate the DLL library that it needs in order to run. It can also occur if the library is not in the specified directory in the path or if the DLL file has gone missing or has become corrupted.
To fix the “The procedure entry point could not be located in the dynamic link library” error, check out the following options given below.
The first thing you can do to resolve the error is to uninstall the program that throws the error and download its latest version from its official site and then install it again.
If reinstalling the program didn’t work, you can also try running the System File Checker or SFC scan to fix the error. System File Checker is a command utility built into your computer that helps restore corrupted files and missing files. Refer to the following steps to run it:
The command will start a system scan which will take a few whiles before it finishes. Once it’s done, you could get the following results:
Reboot your computer.
The Event Viewer can also help you resolve the error as it contains detailed information about the error that could help you pinpoint its root cause and resolve it.
You may have to re-register the ntdll.dll file using the regsvr32.exe before you can successfully install the program and fix the error. The Regsvr32 tool is a command-line utility that can be used to register and unregister OLE controls like DLL and ActiveX (OCX) controls in the Windows operating system. Follow the steps below to use it.
Note: Replace “[DLL file]” with the name of the DLL file that was pointed out in the error.
It is also possible that the DLL file might be infected with malware or virus which could explain why you’re getting the error. Thus, you have to scan your computer using security programs like Windows Defender.

FreeMaps is a google chrome extension by Mindspark powered by Ask or MyWay. This extension offers users a quick and easy way to find the routes or locations that they desire. While all of this may seem appealing, this extension was classified as a Browser Hijacker by many anti-virus applications and was marked for removal.
When installed FreeMaps will change your home page, new tab and default search engine to MyWay.com, it will monitor your browsing activity and send it back to Mindspark ad servers. This data is later used/sold to better display targeted ads depending on your search queries.
While browsing the internet with this extension active you will see additional pop-up ads, sponsored links, and injected ads displaying throughout your browsing sessions, and even injected into websites that should be ad-free. Due to poor code optimization, these ads can sometimes cover a part of the page, making it unreadable or inaccessible.
“Operation could not be completed (error 0x00000643)”
 Error Causes
Error CausesProblem signature: Problem Event Name: BlueScreen OS Version: 6.0.6002.2.2.0.16.7 Locale ID: 1033When the error occurs, the computer screen turns blue and the user is unable to view or access the program. It is advisable to fix the error right away, virtually because BSoD is a critical PC error, it can pose serious threats to your system.
You don’t need to hire a technician or be a computer whiz to resolve Blue Screen Locale ID1033 error code. Here are some methods that you can try to resolve this error on your PC. These methods are easy to perform and result-driven.
 New Microsoft store
New Microsoft storeC00D1199: Cannot play the file
 Error Causes
Error CausesThis tool is designed to verify the integrity of data stored on the hard drive. In addition to this, it resolves and finds errors that may corrupt and damage stored data on your system and affect your PC’s performance.
This tool is intended to keep your PC’s Windows database clean.
However, this tool has certain limitations. It prevents the hard disk from getting damaged but if it gets damaged and corrupt then this tool is no good. It fails to disk check and repair. As a result, you may come across Chkdsk error pop-ups.
In such an event, it is not advisable to run the malfunctioned Chkdsk utility on your PC as it may damage your system beyond repair making you lose all your valuable data saved on your system.
 Error Causes
Error CausesChkdsk errors are triggered by multiple reasons:
Chkdsk errors may cause PC to freeze and lag and also result in data loss as we discussed above.
To avoid serious damages that the Chkdsk error code can cause to your system, it is advisable to fix it. You can either hire a professional or install Restoro. The latter is not just the best way but also a time and money-saving option. It is fast, user-friendly and you can download it for free thus saving hundreds of dollars that you would be paying for professional services.
Restoro is an advanced PC repair tool embedded with multiple features such as a registry cleaner, anti-virus, system optimizer, and Active X and Class error scanner. It helps resolve practically all types and kinds of PC-related errors including the most notorious ones like the Chkdsk errors.
It has an automated and intuitive interface smoothly integrated with the latest technology that enables this software to scan your entire PC and detect errors in seconds.
With the help of its super functional registry cleaner, Restoro detects errors registry issues triggering Chkdsk errors on your system. It cleans all the unnecessary files like junk files, bad and invalid registry entries, and internet files that are stored in your hard disk and taking a lot of space. It removes the clutter and frees up your disk space and repairs the damaged registry.It boosts the speed of your system and ensures that programs run smoothly on your PC and there are no hang-ups or system freezes.
The privacy error detector functions as a powerful anti-virus. With the help of this feature, Restoro identifies and scans for viruses and malware infecting your system. These are removed right away.
Restoro is 100% safe and efficient. It has a backup feature that enables users to create backup copies. This is carried for safety purposes. In case you lose your data during the repair of the Chkdsk error, you can always recover and restore the lost files without any hassle.
With some registry cleaners and repair tools you may often have to struggle with compatibility issues but not with this PC Fixer.
Restoro is compatible with all Windows versions. It is simple and very easy to use. From beginners, intermediate to experienced, all levels of users can use it with ease. Error Causes
Error Causes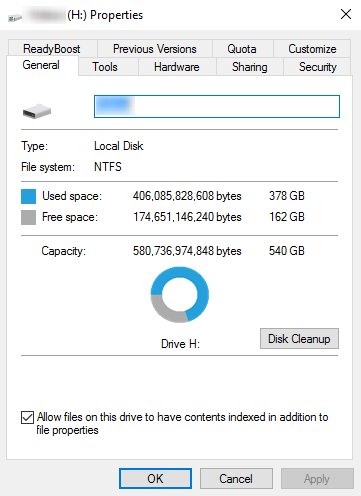 If your disk doesn’t have ample space to accommodate the installation then you should free up some of the space on your disk to make sure the Windows can be installed on it.
You can also reinstall the Windows on another disk that has sufficient space.
If your disk doesn’t have ample space to accommodate the installation then you should free up some of the space on your disk to make sure the Windows can be installed on it.
You can also reinstall the Windows on another disk that has sufficient space.