Free Download Manager is a software program developed by FreeDownloadManager.ORG. According to the publisher:
This software downloads files and converts videos. Its features include integration with all browsers, support of downloads from RapidShare, BitTorrent support, adjusting traffic usage, resuming broken downloads, and adds BitTorrent support, flash video download, upload manager, portable mode, and remote control.
During setup, the program creates a startup registration point in Windows in order to automatically start when any user boots the PC. It adds a browser extension to help it cache files you are downloading over your browser. The software is designed to connect to the internet and adds a Windows Firewall exception in order to do so without being interfered with. It also hooks up to start automatically and cache every download even if it's turned off.
This software comes bundled with video converters that some anti-virus programs marked as malware and therefore it is considered a potentially unwanted program.
About Potentially Unwanted Applications
If you’ve ever downloaded freeware or shareware, odds are high that your computer can get installed with a bunch of unwanted programs. These unwanted applications, officially known as Potentially Unwanted Programs (PUPs), often come bundled with other software and install themselves on user’s computers without their knowledge. They might not look like computer viruses to some individuals, but they can create huge annoyances and lead to serious difficulties for users.
It’s clear by its name – unwanted programs – but did not really constitute “malware” in the traditional sense. What makes a PUP different from malware is the fact that when you download one, you’re doing it with your approval – even though in most cases unconsciously and unwillingly. Nevertheless, there is no doubt that PUPs continue to be bad news for PC users as they can be incredibly detrimental to your computer in several ways.
How does unwanted software affect you?
Unwanted programs come in various forms. Usually, they could be found in adware bundlers that are known to use aggressive and deceptive advertising. The majority of bundlers install multiple adware applications from a number of companies, each of which has its own EULA policy. Safebytes Anti-Malware entirely eliminates this threat and safeguards your PC against PUP or adware infection. They will also come in the form of web browser extension add-ons and toolbars. Not just they needlessly fill up space on your computer screen, toolbars could also manipulate search results, keep an eye on your web browsing activities, decrease your internet browser’s efficiency, and slow down your net connection to a crawl.
Potentially unwanted programs utilize aggressive distribution methods to get in your computer. They will often include things like information gathering code that will collect and send your private information to other companies. Due to this unwanted program, your application may freeze, your security protections may get turned off that can leave your computer susceptible, your system could get damaged, and this list goes on and on.
Tips to prevent PUPs
• Always read the license agreement and privacy statement. Don’t agree unless you understand exactly what you are acknowledging.
• Always choose “Custom” or “Advanced” installation and don’t blindly click the Next button, which will allow you to uncheck any foistware software programs you do not want.
• Install an ad blocker/pop-up blocker; Add anti-malware products such as Safebytes Anti-Malware. These applications could establish a wall between the computer and cybercriminals.
• Be alert if you install freeware, open-source programs, or shareware. Nowadays ‘freeware’ is not really freeware – but ‘crapware’ bundling nonsense.
• Always download software from trusted sources like official websites instead of untrustworthy sharing space. Avoid file-hosting sites wherever possible.
Can't Install Safebytes Anti-malware due to the presence of Malware? Do This!
Malware could cause plenty of damage to your PC. Some malware types modify browser settings by including a proxy server or change the PC’s DNS configurations. In these cases, you’ll be unable to visit certain or all of the internet sites, and thus not able to download or install the required security software to remove the infection. If you are reading this article, you may have got infected by malware that stops you from installing a computer security program such as Safebytes Anti-Malware. There are some fixes you can attempt to get around with this obstacle.
Get rid of viruses in Safe Mode
In the event the malware is set to load at Windows startup, then booting in safe mode should avoid it. Only minimal required programs and services are loaded whenever you boot your PC in Safe Mode. To launch your Windows XP, Vista, or 7 computers in Safe Mode with Networking, do as instructed below.
1) Tap the F8 key continuously as soon as your PC boots, however, before the large Windows logo appears. This would conjure up the Advanced Boot Options menu.
2) Choose Safe Mode with Networking using arrow keys and hit Enter.
3) Once you get into this mode, you should have an internet connection once again. Now, use your browser normally and navigate to https://safebytes.com/products/anti-malware/ to download and install Safebytes Anti-Malware.
4) Following installation, run a complete scan and let the software program remove the threats it discovers.
Obtain the anti-malware program using an alternate browser
Web-based viruses could be environment-specific, targeting a particular web browser or attacking particular versions of the web browser. In case you suspect that your Internet Explorer has been hijacked by a computer virus or otherwise compromised by online hackers, the most effective thing to do would be to switch to a different browser like Chrome, Firefox, or Safari to download your chosen computer security program – Safebytes Anti-Malware.
Run antivirus from your pen drive
Here’s yet another solution which is creating a portable USB antivirus software package that can scan your computer for malicious software without the need for installation. Try these simple steps to clear up your infected computer by using a portable antivirus.
1) On a virus-free PC, download and install Safebytes Anti-Malware.
2) Put the pen drive into the clean PC.
3) Double click on the downloaded file to open the installation wizard.
4) Choose the drive letter of the flash drive as the location when the wizard asks you where you want to install the antivirus. Follow the directions to finish the installation process.
5) Unplug the pen drive. Now you can utilize this portable anti-virus on the affected computer system.
6) Run the Safebytes Anti-malware directly from the USB drive by double-clicking the icon.
7) Click on “Scan Now” to run a scan on the infected computer for malware.
Features and Benefits of SafeBytes Anti-Malware
If you are looking to purchase anti-malware for your computer system, there are numerous brands and applications for you to consider. A few of them do a good job in getting rid of malware threats while some will ruin your PC by themselves. You must choose a product that has gained a good reputation and detects not only viruses but other kinds of malware too. Among few good programs, SafeBytes Anti-Malware is the strongly recommended software for the security-conscious user.
SafeBytes anti-malware is a very effective and easy-to-use protection tool that is created for users of all levels of IT literacy. Once you’ve got installed this software program, SafeBytes superior protection system will make sure that no viruses or malware can seep through your computer.
SafeBytes anti-malware provides an array of advanced features that sets it aside from all others. The following are some of the good ones:
World-class AntiMalware Protection: Safebytes is made on the very best virus engine in the industry. These engines can detect and remove threats even during the early stages of a malware outbreak.
Real-time Active Protection: SafeBytes provides complete and real-time security for your personal machine. It will monitor your personal computer for suspicious activity at all times and shields your PC from unauthorized access.
Fast Multi-threaded Scanning: Safebytes Anti-Malware, using its advanced scanning engine, provides super-fast scanning that can immediately target any active online threat.
Safe Web Browsing: Through its unique safety rating, SafeBytes notifies you whether a website is safe or not to access it. This will ensure that you’re always certain of your safety when browsing the online world.
Lowest Memory/CPU Usage: This software is lightweight and will work silently in the background, and that does not have an effect on your PC efficiency.
24/7 Live Expert Support: You can obtain high levels of support round the clock if you’re using their paid software.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove FreeDownloadManager without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by FreeDownloadManager
Files:
C:WINDOWSsystem32netmsg.dll
C:DocumentsUserLocalTempfdminst.exe
C:DocumentsUserLocalTempis-FJKMF.tmpfdminst.tmp
C:WINDOWSsystem32msctfime.ime
C:DocumentsUserLocalTempis-FN3E3.tmp_isetup_shfoldr.dll
C:WINDOWSsystem32shfolder.dll
C:DocumentsUserLocalTempis-FN3E3.tmpfdminno.dll
C:DocumentsUserLocalTempis-FN3E3.tmpnsProcessW_modified.dll
C:WINDOWSsystem32shell32.dll
C:Documents and SettingsUserStart Menudesktop.ini
C:Documents and SettingsUserStart MenuProgramsdesktop.ini
C:WINDOWSRegistrationR000000000007.clb
C:WINDOWSwin.ini
Registry:
HKEY_CURRENT_USERSoftwareCodeGearLocales
HKEY_LOCAL_MACHINESoftwareCodeGearLocales
HKEY_CURRENT_USERSoftwareBorlandLocales
HKEY_CURRENT_USERSoftwareBorlandDelphiLocales
HKEY_LOCAL_MACHINESoftwareMicrosoftWindows NTCurrentVersionIMM
HKEY_USERSS-1-5-21-1547161642-507921405-839522115-1004SoftwareMicrosoftWindows NTCurrentVersionAppCompatFlagsLayers
HKEY_CURRENT_USERSOFTWAREMicrosoftCTF
HKEY_LOCAL_MACHINESoftwareMicrosoftCTFSystemShared
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionFontSubstitutes
HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersion
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersion
HKEY_CURRENT_USERSoftwareFreeDownloadManager.ORGFree Download Manager 5
HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionPoliciesExplorer
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionPoliciesExplorer
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionShellCompatibilityObjects20D04FE0-3AEA-1069-A2D8-08002B30309D
HKEY_CLASSES_ROOTHKEY_LOCAL_MACHINESoftwareClassesCLSID20D04FE0-3AEA-1069-A2D8-08002B30309DInProcServer32
HKEY_CLASSES_ROOTDriveshellexFolderExtensions
HKEY_CLASSES_ROOTDriveshellexFolderExtensionsfbeb8a05-beee-4442-804e-409d6c4515e9
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorerUser Shell Folders
HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionExplorerUser Shell Folders
HKEY_LOCAL_MACHINESystemCurrentControlSetControlSession Manager
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorerShell Folders
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorerMountPoints2CPCVolume
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorerMountPoints2CPCVolume475c7950-e3d2-11e0-8d7a-806d6172696f
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorerMountPoints2CPCVolume475c7952-e3d2-11e0-8d7a-806d6172696f
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorerMountPoints2475c7952-e3d2-11e0-8d7a-806d6172696f
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorerMountPoints2475c7950-e3d2-11e0-8d7a-806d6172696f
HKEY_CLASSES_ROOTDirectory
HKEY_CLASSES_ROOTDirectoryCurVer
HKEY_CLASSES_ROOTDirectory
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorer
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorer
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionPoliciesSystem
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorerAdvanced
HKEY_CLASSES_ROOTDirectoryShellExIconHandler
HKEY_CLASSES_ROOTDirectoryClsid
HKEY_CLASSES_ROOTFolder
HKEY_CLASSES_ROOTFolderClsid
HKEY_CURRENT_USERSoftwareMicrosoftwindowsCurrentVersionExplorerAutoComplete
HKEY_LOCAL_MACHINESoftwareMicrosoftwindowsCurrentVersionExplorerAutoComplete
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionExplorerAutoComplete
HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionExplorerAutoComplete
HKEY_LOCAL_MACHINESoftwareMicrosoftCOM3
HKEY_USERSS-1-5-21-1547161642-507921405-839522115-1004_Classes
HKEY_LOCAL_MACHINESoftwareClassesREGISTRYUSER
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062TreatAs
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062InprocServer32
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062InprocServerX86
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062LocalServer32
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062InprocHandler32
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062InprocHandlerX86
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062LocalServer
HKEY_CLASSES_ROOTHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062
HKEY_CLASSES_ROOTHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2765-6A77-11D0-A535-00C04FD7D062TreatAs
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383TreatAs
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383InprocServer32
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383InprocServerX86
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383LocalServer32
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383InprocHandler32
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383InprocHandlerX86
HKEY_LOCAL_MACHINESoftwareClassesHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383LocalServer
HKEY_CLASSES_ROOTHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383
HKEY_CLASSES_ROOTHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383TreatAs
HKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062
HKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062TreatAs
HKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062
HKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062InprocServer32
HKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062InprocServerX86
HKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062LocalServer32
HKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062InprocHandler32
HKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062InprocHandlerX86
HKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062LocalServer
HKEY_CLASSES_ROOTHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062
HKEY_CLASSES_ROOTHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062TreatAs
HKEY_CLASSES_ROOTHKEY_LOCAL_MACHINESoftwareClassesCLSID3C036F1-A186-11D0-824A-00AA005B4383InProcServer32
HKEY_CLASSES_ROOTHKEY_LOCAL_MACHINESoftwareClassesCLSID0BB2763-6A77-11D0-A535-00C04FD7D062InProcServer32
HKEY_CURRENT_USERsoftwareMicrosoftWindowsCurrentVersionExplorerAdvanced
HKEY_LOCAL_MACHINEsoftwareMicrosoftWindowsCurrentVersionExplorerAdvanced
HKEY_LOCAL_MACHINESoftwareMicrosoftWindows NTCurrentVersionFontSubstitutes
HKEY_USERSS-1-5-21-1547161642-507921405-839522115-1004
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionLanguagePackSurrogateFallback
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionUninstallFree Download Manager_is1
HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionUninstallFree Download Manager_is1
HKEY_CURRENT_USERSoftwareFreeDownloadManager.ORGFree Download ManagerSettingsCommunity
HKEY_CURRENT_USERSoftwareFreeDownloadManager.ORGFree Download ManagerSettingsNetworkBittorrent
HKEY_CURRENT_USERKeyboard LayoutToggle
HKEY_CURRENT_USERSOFTWAREMicrosoftCTFLangBarAddIn
HKEY_LOCAL_MACHINESOFTWAREMicrosoftCTFLangBarAddIn


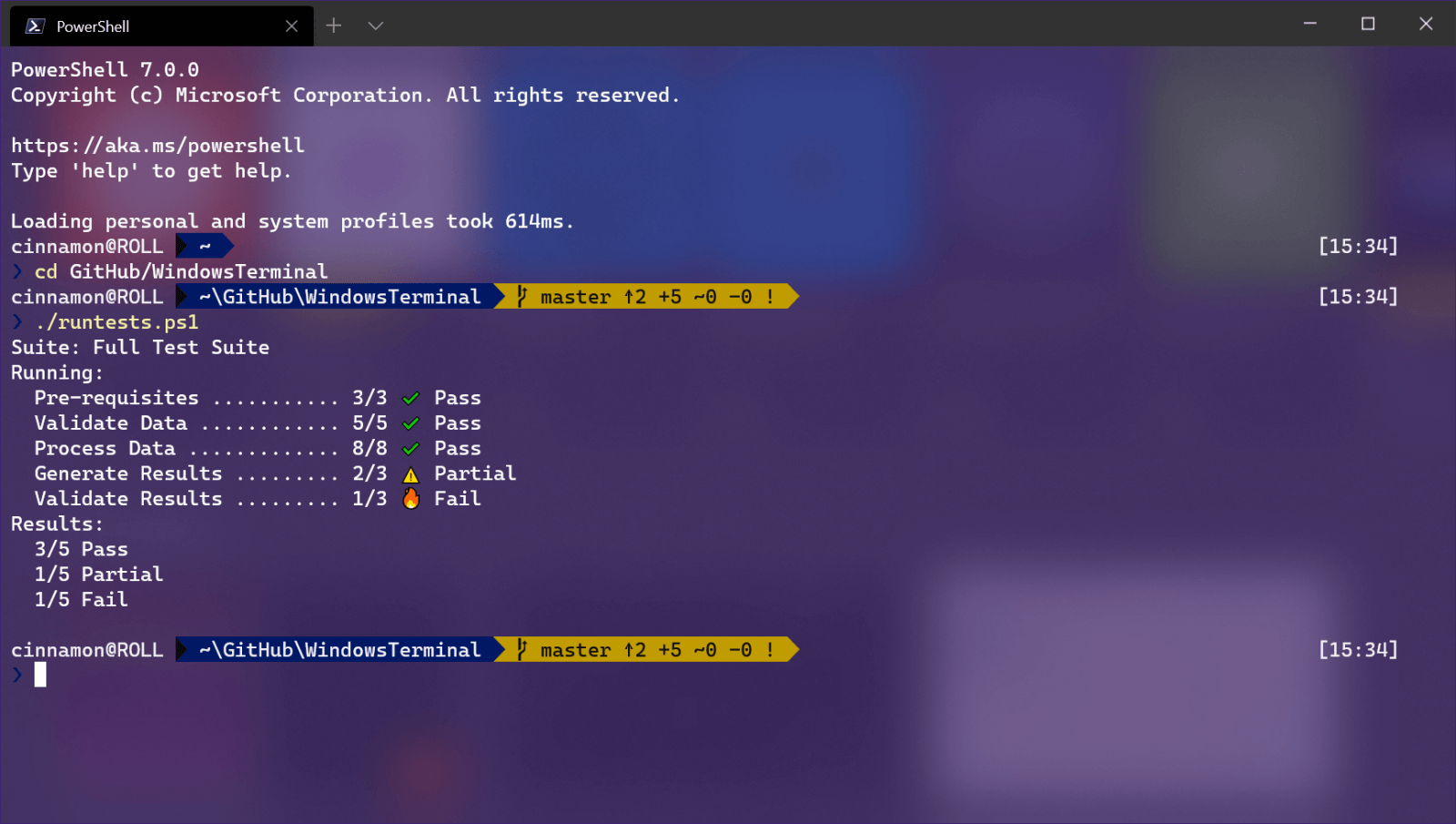 Windows Terminal is a new free Microsoft terminal sort of application. When you open either Power Shell or Command Prompt in Windows they will be opened in different windows, and if you want several of each you will have several windows of each on your screen.
Windows Terminal fixes this by opening each of the Instances of Command Prompt and Power Shell as separate tabs inside itself making it much easier to manage multiple instances of named applications.
You can also run both Power Shell and Command prompt tabs in the same Windows Terminal. Luckily running command prompt and power shell in different tabs is not the only thing you can do. Windows Terminal lets you choose your own theme, it has emoji support, GPU rendering, split panes, and many more customizable options.
Windows 11 will have Terminal as the default command-line environment for opening Power Shell or Command prompt, even Windows Subsystem for Linux (WSL)
Windows Terminal is a new free Microsoft terminal sort of application. When you open either Power Shell or Command Prompt in Windows they will be opened in different windows, and if you want several of each you will have several windows of each on your screen.
Windows Terminal fixes this by opening each of the Instances of Command Prompt and Power Shell as separate tabs inside itself making it much easier to manage multiple instances of named applications.
You can also run both Power Shell and Command prompt tabs in the same Windows Terminal. Luckily running command prompt and power shell in different tabs is not the only thing you can do. Windows Terminal lets you choose your own theme, it has emoji support, GPU rendering, split panes, and many more customizable options.
Windows 11 will have Terminal as the default command-line environment for opening Power Shell or Command prompt, even Windows Subsystem for Linux (WSL)
