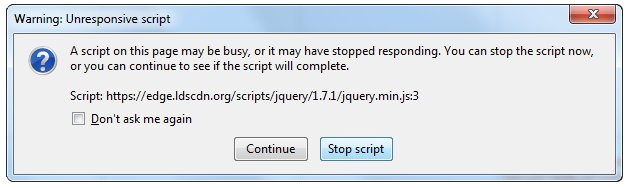
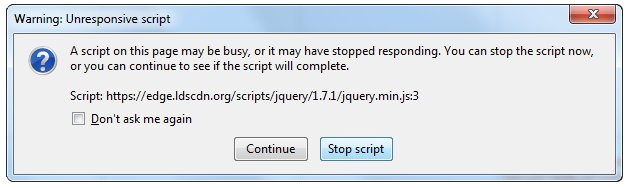
This Unresponsive Script problem information is most frequent on Firefox, which is among the top browsers worldwide.
Firefox might show you these errors with the information, "Warning: Unresponsive Script". It is going to subsequently inform you that software to the web page you're trying to open is unresponsive, or has quit reacting.
This means that the script has ceased functioning and may freeze or hang Firefox if not immediately resolved. You can easily solve this problem.
Solution
 Error Causes
Error Causes
Before you can fix this error, you need to understand its primary cause.
The biggest risk is that if left unchecked, Unresponsive Scripts will hang your browser and to an extension of your computer thus limiting your productivity. You may have to uninstall and re-install Firefox if the problem persists.
Listed here are several of the very most typical reasons for unresponsive script:
- Programming Errors
- Interference by other Softwares
- Using an older outdated version of the program.
Further Information and Manual Repair
Most times, you have to do very little to fix this problem. Furthermore, a lot of the remedies supplied here do not require the assistance of a qualified professional technician. You can easily perform them and completely solve the error.
-
If you wish to stop the error, keep your browser and add-ons up to date.
It's easy to update your browser and any add-ons therein. In most cases it's free. By upgrading your browser and add-ons frequently, you are effectively eliminating the risk of Unresponsive Script occurring and interfering with your work.
-
 Check for a poorly functioning background process
Check for a poorly functioning background process
The sorts of background procedures that might result in the Unresponsive Software error include Javascript code, media plugin, and browser extension.
You can stop the script from running while using Firefox thus eliminating the Unresponsive script error.
Shutting the dialog box is just another easy way of eliminating the unresponsive script error information. Firefox offers you two choices in case of this malfunction. Either "Continue" or "Stop Script". Whatever alternative you pick, you can be certain the dialog box shuts, thus allowing you to continue browsing.
 The final solution. Contact Firefox about these errors on your browser. Oftentimes, these errors occur when you attempt to visit particular websites. Mark the offending websites' URLs and include them in your communications with Firefox.
The final solution. Contact Firefox about these errors on your browser. Oftentimes, these errors occur when you attempt to visit particular websites. Mark the offending websites' URLs and include them in your communications with Firefox.
Sometimes you can also contact the website owner yourself and request them to check their website's code.
Following are additional measures you can take to resolve the Unresponsive Script error.
- Waiting longer for the error to resolve itself automatically
- Blocking the offending script
- Yanking the guilty add-ons
- Disabling the hardware acceleration tool.
With one of these few steps, you won't have to worry about the Unresponsive Script error, can continue enjoying your browsing activities on Firefox.

 Check for a poorly functioning background process
Check for a poorly functioning background process The final solution. Contact Firefox about these errors on your browser. Oftentimes, these errors occur when you attempt to visit particular websites. Mark the offending websites' URLs and include them in your communications with Firefox.
The final solution. Contact Firefox about these errors on your browser. Oftentimes, these errors occur when you attempt to visit particular websites. Mark the offending websites' URLs and include them in your communications with Firefox.
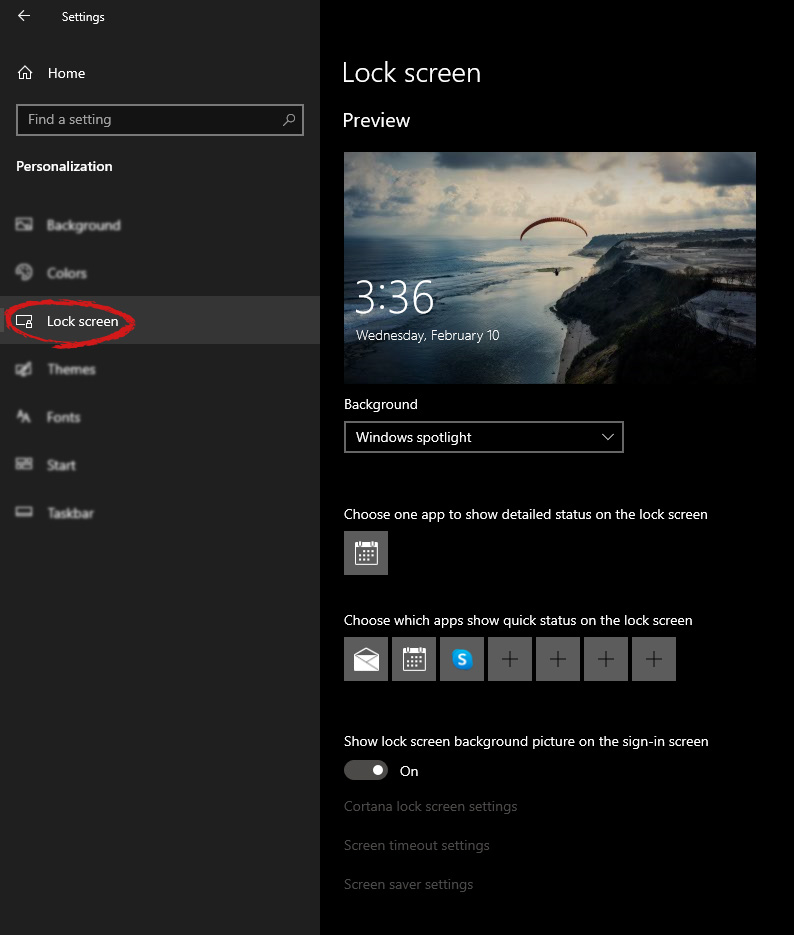
 Inside personalization, click on the Lock Screen tab.
Inside personalization, click on the Lock Screen tab.
 On the right screen, under the picture, you will find Windows spotlight, click on it to bring a drop-down menu up.
On the right screen, under the picture, you will find Windows spotlight, click on it to bring a drop-down menu up.
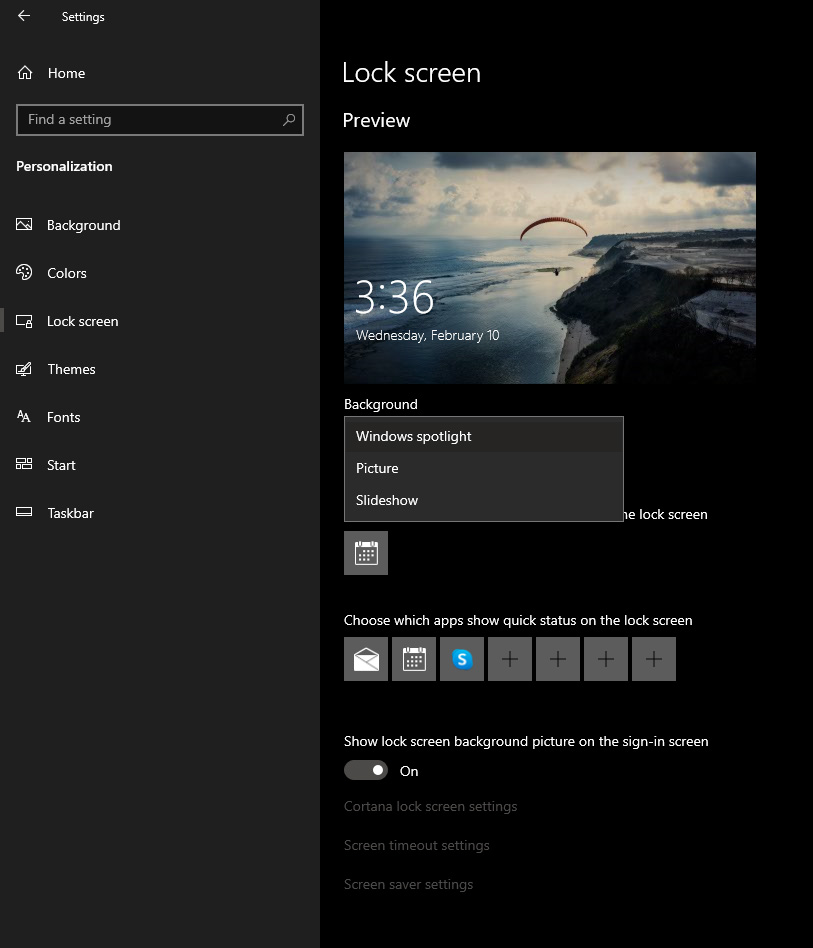 Your choice is presented as a single picture for background or slideshow, a series of pictures that are going to be looped in a given time interval.
If you would like just a single picture for your background, choose that and click on it.
Your choice is presented as a single picture for background or slideshow, a series of pictures that are going to be looped in a given time interval.
If you would like just a single picture for your background, choose that and click on it.
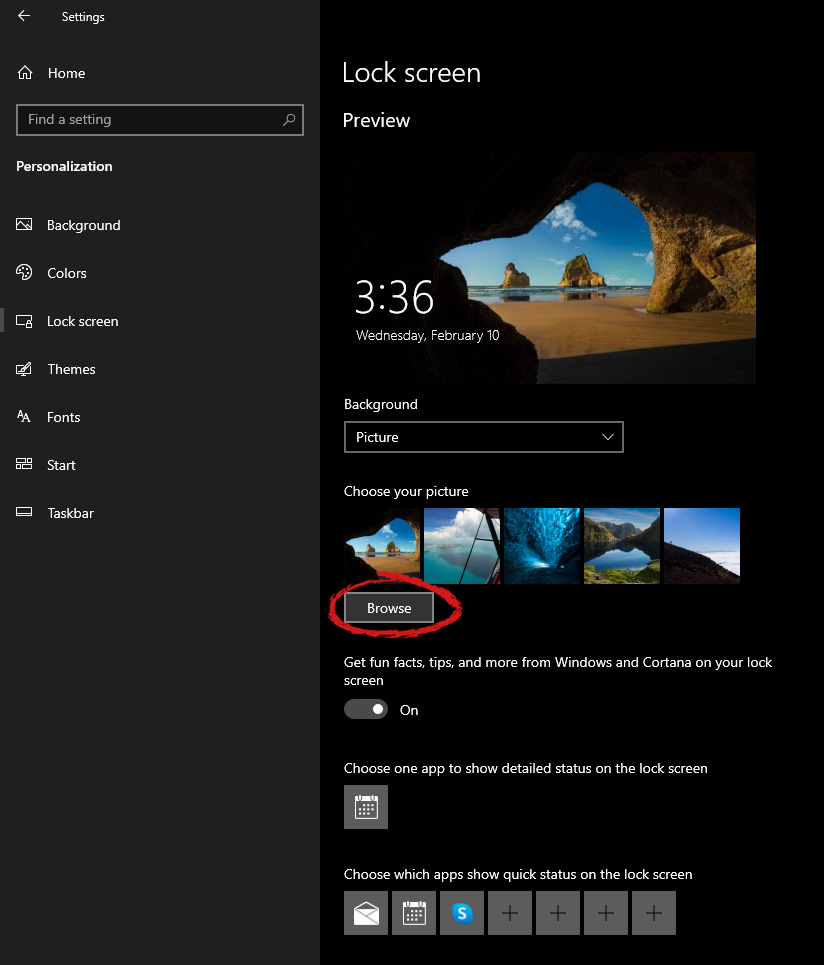 Once you are in choose picture dialog, click on the browse button and navigate to the picture on your storage which you would like to have as a background.
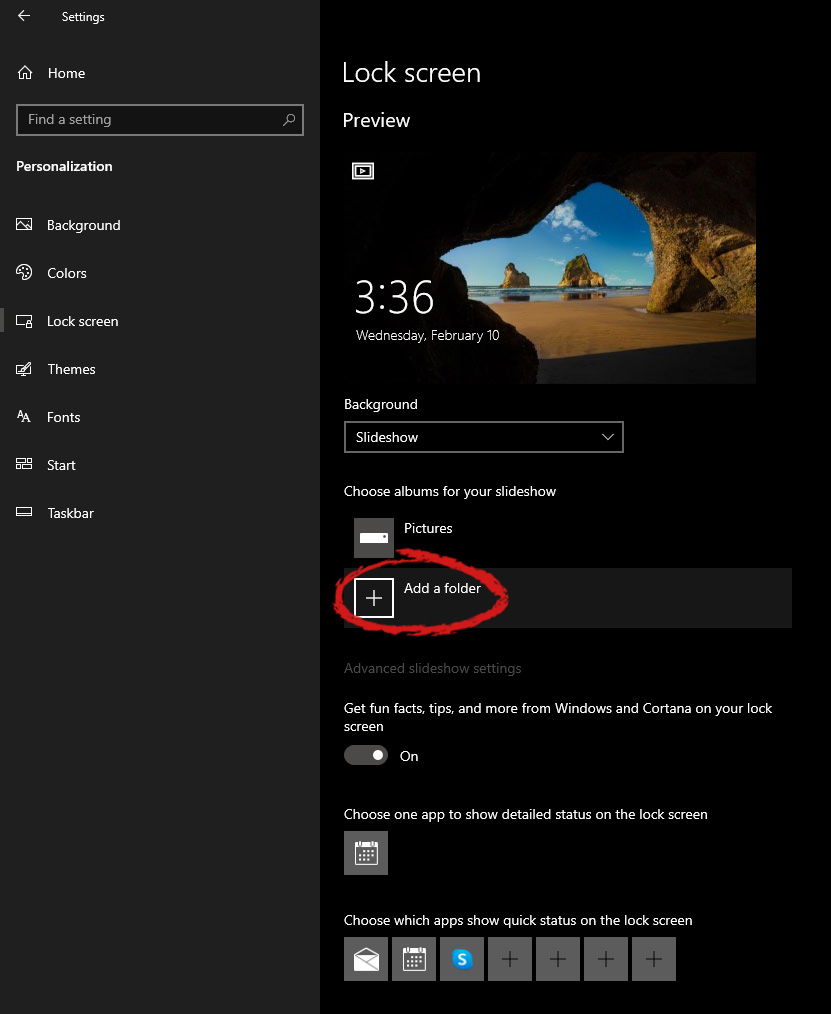
If however, you fancy slideshow as your lock screen background, click on the background drop-down menu and choose the slideshow. Next, click on add a folder and navigate to a folder where you have pictures that you would like to have as a slideshow for your Windows lock screen.
Once you are in choose picture dialog, click on the browse button and navigate to the picture on your storage which you would like to have as a background.
If however, you fancy slideshow as your lock screen background, click on the background drop-down menu and choose the slideshow. Next, click on add a folder and navigate to a folder where you have pictures that you would like to have as a slideshow for your Windows lock screen.
 If we are to believe news from Intel, new series of processors based on Alder Lake architecture are about to be released somewhere in October. Alder Lake is the 12th Generation Core of Intel processors and it is meant to have all advantages of the current CPU structure.
I9 is aimed to pack a punch against its competitors with technology including eight high-performance Golden Cove cores (P-cores) with Hyper-Threading and eight energy-efficient Goldmont (E-cores) equipped with a 30MB L3 cache and operating at high clock speeds.
During the benchmark test, the new CPU outperformed all of Intel’s previous Rocket Lake structure processors which is logically expected but the big surprise came from results that indicate better performance than Apple’s new M1 processor even in single-threaded performance which is supposed to be best in that field.
Another surprise was really beating AMD Ryzen 9 in each field. If we take into account that i9 has 16 cores in total and can process 24 threads against Ryzen 9 with 16 Cores and 32 threads this is an impressive feature.
Now truth to be told Alder lake has massive L3 cache and microarchitectural advantages and consumes much more power but the results of performance are high. Also, note that this early CPU is not really a mass production one and maybe some things will still change but early results are very satisfactory.
We will see what will price tag be since in this age of shortage and competition that will also play a big role in its overall success. Speaking of competition I eagerly await AMD’s response to this, in any way it seems that the CPU market is for some turbulence which is always a good thing for the final customer and I welcome it.
If we are to believe news from Intel, new series of processors based on Alder Lake architecture are about to be released somewhere in October. Alder Lake is the 12th Generation Core of Intel processors and it is meant to have all advantages of the current CPU structure.
I9 is aimed to pack a punch against its competitors with technology including eight high-performance Golden Cove cores (P-cores) with Hyper-Threading and eight energy-efficient Goldmont (E-cores) equipped with a 30MB L3 cache and operating at high clock speeds.
During the benchmark test, the new CPU outperformed all of Intel’s previous Rocket Lake structure processors which is logically expected but the big surprise came from results that indicate better performance than Apple’s new M1 processor even in single-threaded performance which is supposed to be best in that field.
Another surprise was really beating AMD Ryzen 9 in each field. If we take into account that i9 has 16 cores in total and can process 24 threads against Ryzen 9 with 16 Cores and 32 threads this is an impressive feature.
Now truth to be told Alder lake has massive L3 cache and microarchitectural advantages and consumes much more power but the results of performance are high. Also, note that this early CPU is not really a mass production one and maybe some things will still change but early results are very satisfactory.
We will see what will price tag be since in this age of shortage and competition that will also play a big role in its overall success. Speaking of competition I eagerly await AMD’s response to this, in any way it seems that the CPU market is for some turbulence which is always a good thing for the final customer and I welcome it. 