Modem Error 633 error is a dial-up error that usually occurs when using a USB modem with a Windows computer. The Modem Error 633 error message is displayed as the following:
“Error 633: The Modem is already in use or not configured properly.”
 Error Causes
Error CausesThis error can be triggered due to several reasons such as:
If you experience the Modem Error 633 on your PC, you don’t have to panic. Though this error does not pose any major threats like data loss, it may hamper your ability to use the internet therefore it is advisable to resolve the error.
Repairing the Modem Error 633 is quite easy. There are a number of ways to fix this error. So, let’s get started:
If the error occurs because the modem is not properly configured, then this solution is possibly the best way to resolve this error. Here’s what you need to do:

 One of the first things that everyone saw when Microsoft has unveiled Windows 11 is its Start menu. Funny enough this is what has caused most of the divide among users, some find it interesting, and some do not like it. Truth is, it is different, and it is centered in the middle instead of the lower left part of the screen.
It has been confirmed however that the Start menu can be moved to any part of the screen so if you want, you could place it on the lower left as it has always been.
Live tiles do not longer exist in the Start menu, instead, we have styled simple icons.
One of the first things that everyone saw when Microsoft has unveiled Windows 11 is its Start menu. Funny enough this is what has caused most of the divide among users, some find it interesting, and some do not like it. Truth is, it is different, and it is centered in the middle instead of the lower left part of the screen.
It has been confirmed however that the Start menu can be moved to any part of the screen so if you want, you could place it on the lower left as it has always been.
Live tiles do not longer exist in the Start menu, instead, we have styled simple icons.
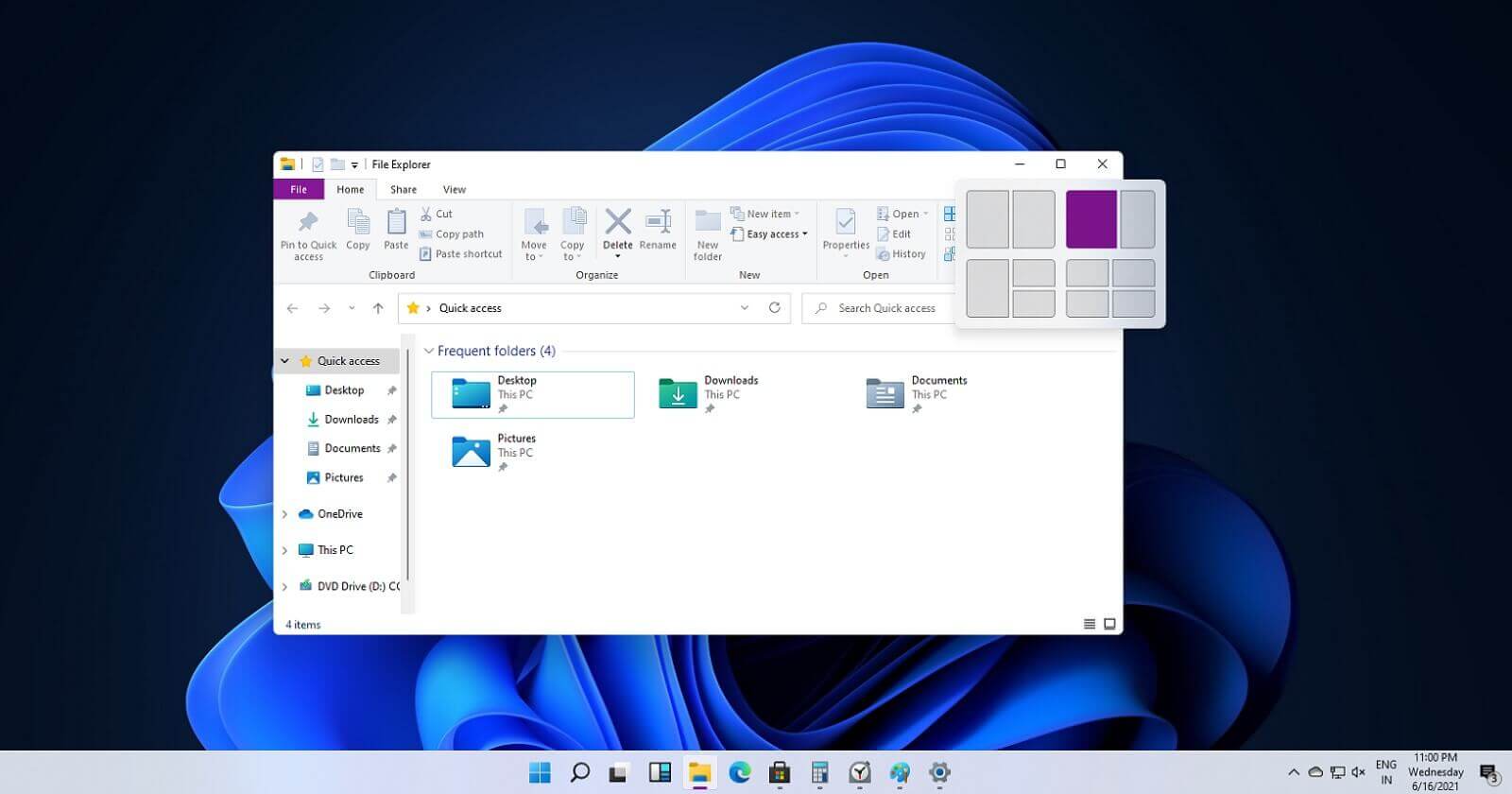 If you have used the cascade option in previous Windows versions then it is most likely that you will like the new Snap controls.
You can quickly snap windows side by side, or arrange them in sections on your desktop just by hovering over maximize button on the title bar.
If you have used the cascade option in previous Windows versions then it is most likely that you will like the new Snap controls.
You can quickly snap windows side by side, or arrange them in sections on your desktop just by hovering over maximize button on the title bar.
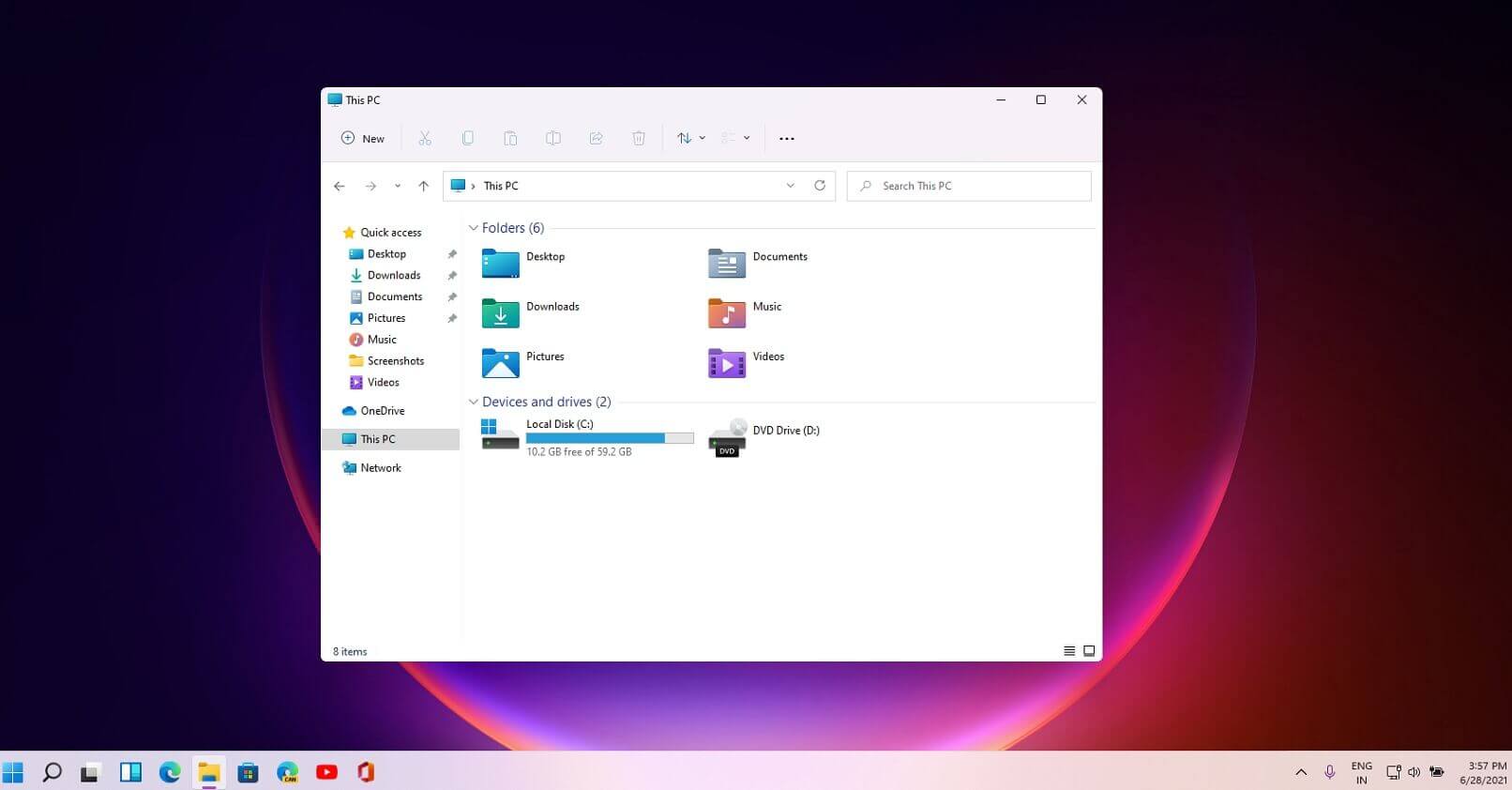 File explorer has gone through some visual and design changes, the ribbon on top has been completely removed and replaced with a header-like feature with a slick and clean design.
The header contains a nice organized and designed single row of icons like cut, paste, copy, rename, delete, and new folder icons.
File explorer has gone through some visual and design changes, the ribbon on top has been completely removed and replaced with a header-like feature with a slick and clean design.
The header contains a nice organized and designed single row of icons like cut, paste, copy, rename, delete, and new folder icons.
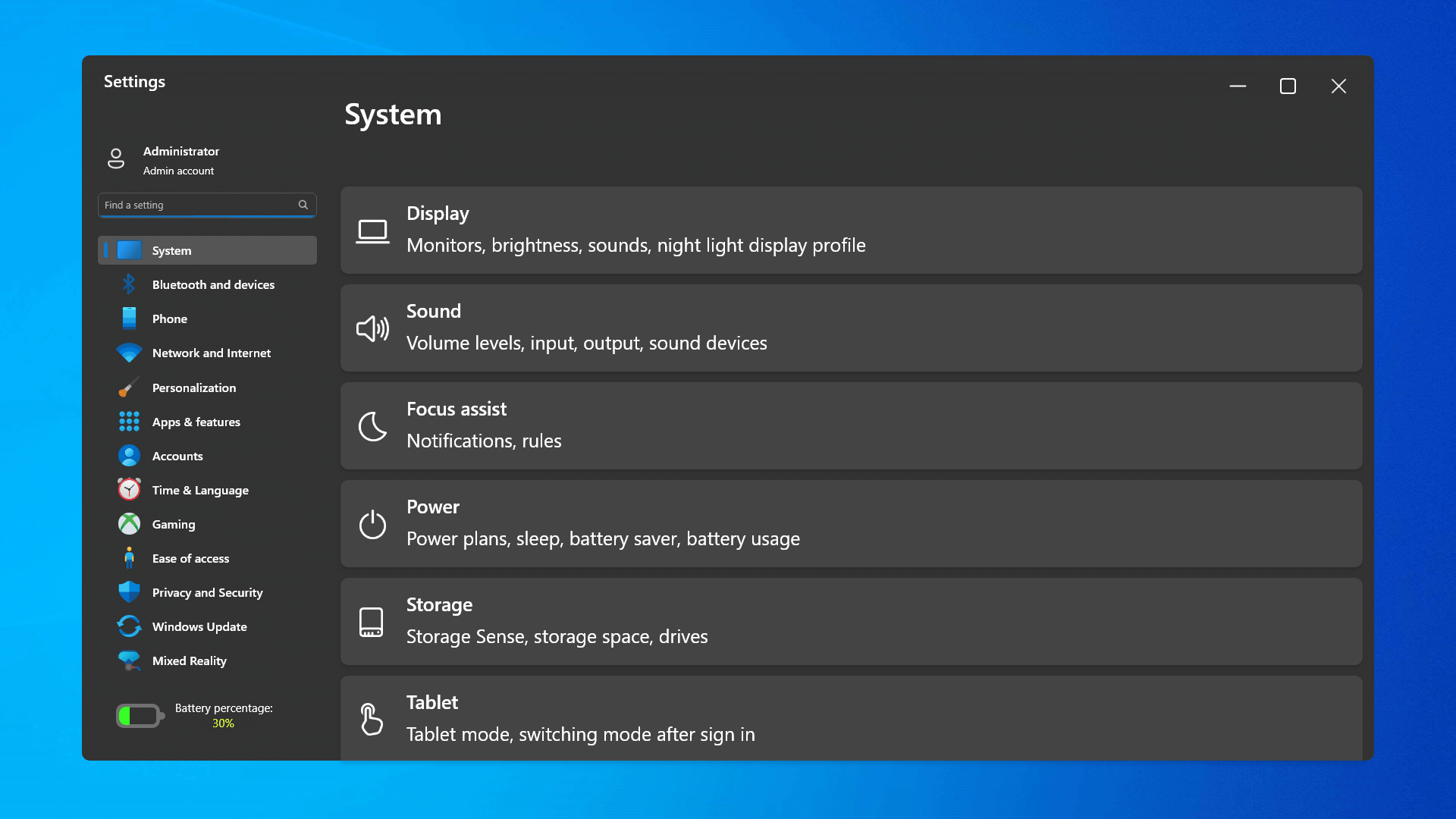 The settings app also has gone through visual and design changes. It has a new design that is very visually appealing and navigation has been simplified and more organized. Finding the right and desired setting is much faster and clearer now.
The settings app also has gone through visual and design changes. It has a new design that is very visually appealing and navigation has been simplified and more organized. Finding the right and desired setting is much faster and clearer now.
 Yes, widgets are back but not like you remember them.
Instead of being all-time present at your desktop like once they used to be, now there is a button on the taskbar which brings the widget bar up that contains desired widgets. This way they are easily accessible and do not clutter desktops.
So far we have weather, news, calendar, and stocks widget but we will see how development on these goes. I expect to have community-made widgets like in old days for all of our needs.
Yes, widgets are back but not like you remember them.
Instead of being all-time present at your desktop like once they used to be, now there is a button on the taskbar which brings the widget bar up that contains desired widgets. This way they are easily accessible and do not clutter desktops.
So far we have weather, news, calendar, and stocks widget but we will see how development on these goes. I expect to have community-made widgets like in old days for all of our needs.
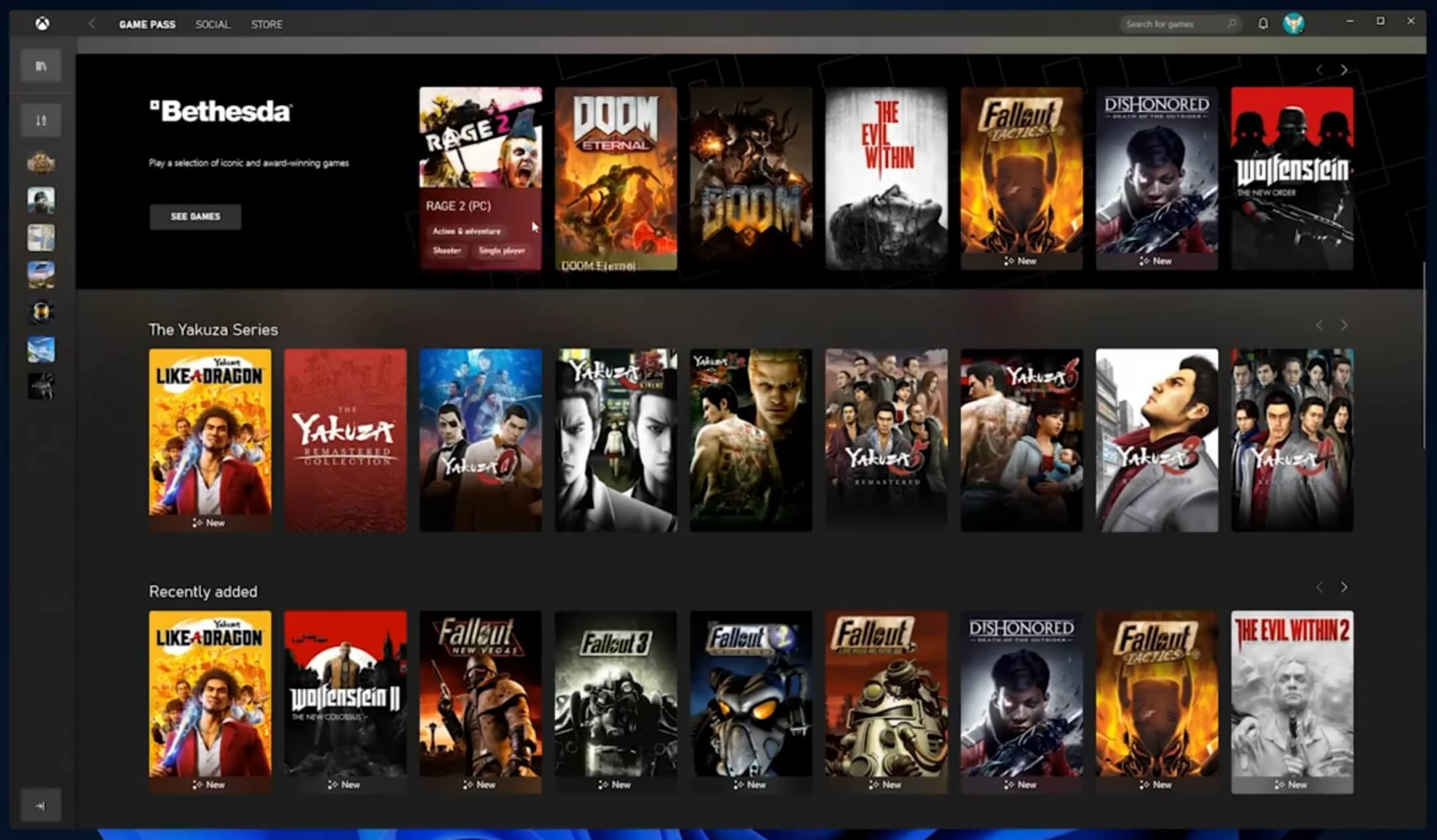 The new Xbox app is now integrated into Windows 11, offering quick access to Xbox Game Pass games, the social parts of the Xbox network, and the Xbox store.
The new Xbox app is now integrated into Windows 11, offering quick access to Xbox Game Pass games, the social parts of the Xbox network, and the Xbox store.
 As widely known by now Windows 11 will require you to have a TPM 2.0 module capable CPU in order to install it.
This system requirement has caused a lot of controversies but essentially it seems that MS's goal is to protect your personal data by using this module.
The upside of course is that your data will be protected much more than in previous Windows versions, the downside, of course, will be that you will need newer hardware to run OS on it.
and that is essentially it, keep on tuned on more Windows 11 information and overall articles tied to PC and technology here at errortools.com
As widely known by now Windows 11 will require you to have a TPM 2.0 module capable CPU in order to install it.
This system requirement has caused a lot of controversies but essentially it seems that MS's goal is to protect your personal data by using this module.
The upside of course is that your data will be protected much more than in previous Windows versions, the downside, of course, will be that you will need newer hardware to run OS on it.
and that is essentially it, keep on tuned on more Windows 11 information and overall articles tied to PC and technology here at errortools.com Stop 0X00000050 (parameter1, 0, parameter3, parameter4) PAGE_FAULT_IN_NONPAGED_AREA”
 Error Causes
Error Causes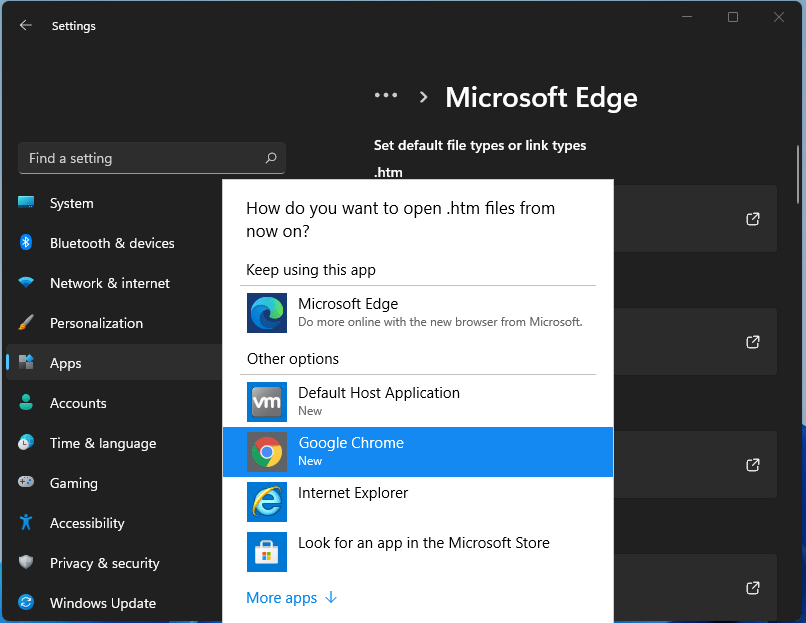 For anyone who is not aware, when Windows 11 was released if you wanted to switch to another browser you had to go into the settings app and choose the default browser for different types of file extensions like HTML, HTM, PDF for opening on the web, etc. Of course, this was completely unnecessary and it was not well received by users. So after some time, Microsoft backpedaled to standard one click, choose your default browser solution that existed in the previous version of Windows OS.
Altho sometimes Microsoft knows how to irritate its users base, it is good to know that they can also listen and fix things that are required.
For anyone who is not aware, when Windows 11 was released if you wanted to switch to another browser you had to go into the settings app and choose the default browser for different types of file extensions like HTML, HTM, PDF for opening on the web, etc. Of course, this was completely unnecessary and it was not well received by users. So after some time, Microsoft backpedaled to standard one click, choose your default browser solution that existed in the previous version of Windows OS.
Altho sometimes Microsoft knows how to irritate its users base, it is good to know that they can also listen and fix things that are required.