Wondering if upgrading to Windows 11 will boost your gaming experience? We can’t give you a straightforward answer, sadly. But we can take you through the tweaks you can expect if you have all the right requirements and help you make a final decision.
Is Windows 11 good for gaming?
Essentially, the answer to this question is yes. Microsoft has definitely added a bunch of enhancements and features to its latest OS to give gamers the best possible experience. However, you have to keep in mind that this may not work out smoothly for every single user.
Whether you’ll be able to fully take advantage of the Windows 11 gaming features really depends on your setup. As expected, Windows 11 has more demanding system requirements than its predecessor.

So, unless your hardware can run the new OS comfortably, you might not be able to make the most of all these gaming perks. In that case, we recommend you first upgrade your hardware and then make the switch. Be prepared to be a little surprised by a few other interesting changes in comparison to Windows 10, though!
For some of the new gaming features to work, it’ll also be necessary for you to have an NVMe SSD and an HDR-compatible monitor. So let’s take a look at 4 big improvements you can expect if your setup is compatible.
Gaming enhancements on Windows 11
1. Enjoy faster loading speed with DirectStorage
For this powerful feature to work, you need a compatible graphics card and, as stated before, an NVMe SSD. It’s also important for your GPU to support the DirectX 12 graphics API at least. And since we’re on that subject, you’ll be happy to know that Windows 11 has also introduced a new version of the API called DirectX 12 Ultimate.
Now, what does DirectStorage do? It’s a new feature designed to make full use of the speedy storage of NVMe SSDs. It also transfers game data directly onto the graphics card, lightening the load on your CPU. Normally the CPU would have to decompress the data first, but DirectStorage helps bypass this. That’s how loading times are reduced and games run more smoothly.
2. Fully immerse yourself through Game Mode
Windows 11’s Game Mode is certainly a welcomed addition. When you turn on Game Mode, usage of background apps that aren’t essential to your game is reduced. This results in the game you’re running becoming a priority process. This way, it uses your hardware and system resources to the max. Ultimately, the Game Mode means less lag and higher frame rates so you can play undisturbed and fully enjoy your gaming session.
3. Vibrant visual experience thanks to AutoHDR
For this one you’ll absolutely need an HDR-compatible monitor. Basically, HDR (High Dynamic Range) means a wider range of contrasts and colors that can be displayed on a monitor.
Windows 10 has an HDR feature, but you have to turn it on and off manually (“Use HDR”). Plus, users have reported that, if left on, it results in an unappealing appearance of content other than movies and games.
Windows 11 fixes that problem with its AutoHDR feature. Toggling it results in the system automatically adjusting the color contrast, balance and brightness based on what you’re currently looking at. For gamers, this means vivid imagery in every single game, resulting in a supreme visual experience. You can check out Microsoft’s own video showcasing the power of AutoHDR.
Aside from AutoHDR, another way Windows 11 improves the visual aspect is through its support for refresh rates of up to 360Hz.
4. Xbox Game Pass & Game Bar
It’s no secret that Microsoft wants to integrate Windows and Xbox. We’ve seen some attempts with Windows 10, but they’re pretty wonky compared to the new OS.
Windows 11’s built-in Xbox Game Bar enables quite a few options all gamers desire. You can take screenshots and videos of your game and send them, for starters. Furthermore, you can use it to see audio settings and monitor your PC’s performance without having to leave the game or open the Task Manager.
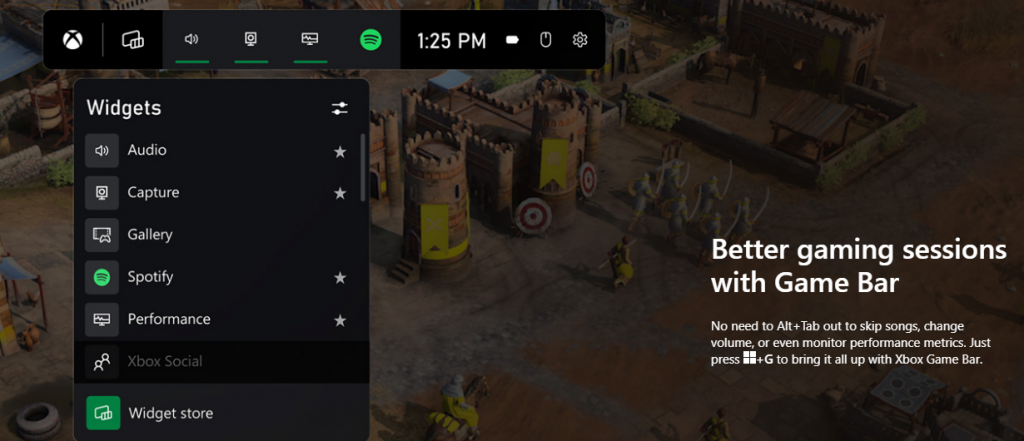
Widgets are also a really cool part of the Game Bar. You can choose from a wide variety of widgets, such as Xbox Achievements, Spotify, Gallery, Xbox Social and more.
Moreover, the Xbox Game Pass has been streamlined on Windows 11. Game Pass is a subscription service that unlocks hundreds of awesome games and supports cloud streaming. Do keep in mind that the games are only unlocked for a certain period of time, as the selection rotates once in a while.
What can you do for a better gaming experience?
Windows 11 does offer tweaks that require zero input from you. However, there are a few things you can do manually to get even more out of your new OS while gaming.
- Turn off enhanced pointer precision. Most games enhance precision by default, so having this feature on might interfere with that.
- Make sure to select your high performance graphics card for each game. Go to Settings > Gaming > Game Mode and tap ‘Graphics’ from the ‘Related settings’ menu. Find the game you want to adjust, click on ‘Options’ and choose your high performance graphics card to be the default setting. While there, you can also turn on ‘Hardware-accelerated GPU scheduling’ at the top.
- Disable unnecessary apps and programs. As long as they aren’t essential to running your game, they might take up valuable system resources, so disable them to make space for your gaming requirements.
- Check for pending updates and install them. It’s well-known that out-of-date software causes bugs, latency and crashes. The same goes for your GPU drivers.
- Use the High-performance power plan (Control Panel > Power Options > Additional plans) to maximize the use of resources for the best possible performance.
Summary
Windows 11 has done quite a bit for avid gamers. We hope your setup is compatible with all these new features and you can experience these enhancements ASAP!


 Microsoft wants to escalate the situation from Australia to the EU, what a surprise.
Hello all and welcome to another news article, this time we are focusing on Microsoft pushing the EU to accept law proposition from Australia.
For all of you who are not familiar with the given situation let me quickly explain. The feud began when the Australian government proposed a new law that targeted Facebook and Google specifically. The government said that it believed that both of the tech giants were using content from news outlets without paying.
Have you ever seen the little news snippets that Google or Facebook sometimes show its users to keep them up to date? These are lifted directly from news websites, and the Australian government claimed that this practice meant that people didn't bother visiting the news website. This then staved news websites of revenue.
As such, the government put forward a new law that would mean Google and Facebook would have to pay the source website for every time they displayed a news snippet. Facebook responded by removing its Australian news coverage in light of the law.
Google, however, put up a fight. It argued that its snippets encouraged people to click on it to read more, thus driving more traffic to the news website. It also said that such a law would be too expensive to maintain in the long run.
As such, Google threatened to remove itself from Australia if the law passed. This was likely a scare tactic, as 95 percent of Australian web users use Google; however, it actually opened the door for its rival, Microsoft.
Microsoft saw how it could push its own search engine BING to replace google. It of course went and reached the Australian government to assure them that BING is more than capable to fulfill its needs and fully abide by the proposed law.
Now Microsoft knows that if this law passes it could see a similar situation happening in Europe and it is pushing it. US News reported on how Microsoft plans to encourage EU countries to adopt this new law too. The company has teamed up with the European Publishers Council and News Media Europe to make the following statement:
Publishers might not have the economic strength to negotiate fair and balanced agreements with these gatekeeper tech companies, who might otherwise threaten to walk away from negotiations or exit markets entirely
Microsoft wants to escalate the situation from Australia to the EU, what a surprise.
Hello all and welcome to another news article, this time we are focusing on Microsoft pushing the EU to accept law proposition from Australia.
For all of you who are not familiar with the given situation let me quickly explain. The feud began when the Australian government proposed a new law that targeted Facebook and Google specifically. The government said that it believed that both of the tech giants were using content from news outlets without paying.
Have you ever seen the little news snippets that Google or Facebook sometimes show its users to keep them up to date? These are lifted directly from news websites, and the Australian government claimed that this practice meant that people didn't bother visiting the news website. This then staved news websites of revenue.
As such, the government put forward a new law that would mean Google and Facebook would have to pay the source website for every time they displayed a news snippet. Facebook responded by removing its Australian news coverage in light of the law.
Google, however, put up a fight. It argued that its snippets encouraged people to click on it to read more, thus driving more traffic to the news website. It also said that such a law would be too expensive to maintain in the long run.
As such, Google threatened to remove itself from Australia if the law passed. This was likely a scare tactic, as 95 percent of Australian web users use Google; however, it actually opened the door for its rival, Microsoft.
Microsoft saw how it could push its own search engine BING to replace google. It of course went and reached the Australian government to assure them that BING is more than capable to fulfill its needs and fully abide by the proposed law.
Now Microsoft knows that if this law passes it could see a similar situation happening in Europe and it is pushing it. US News reported on how Microsoft plans to encourage EU countries to adopt this new law too. The company has teamed up with the European Publishers Council and News Media Europe to make the following statement:
Publishers might not have the economic strength to negotiate fair and balanced agreements with these gatekeeper tech companies, who might otherwise threaten to walk away from negotiations or exit markets entirely 