EhRecvr.exe Error Code - What is it?
EhRecvr.exe is an executable file located in a subfolder of C:\Windows (usually C:\WINDOWS). An executable file is denoted by the filename extension .exe.
You should only run executable files from the publisher you trust because .exe files are prone to errors. Executable files can potentially change your computer settings and harm your computer. These files can easily get corrupted.
Similarly, when the EhRecvr.exe fails to run on the computer and gets corrupt, you experience an EhRecvr.exe error on your system. This error code may pop up while playing games on the PC or using any other program.
EhRecvr.exe error may be displayed in any one of the following formats:
- “ehRecvr.exe cannot be found."
- “There was a problem starting [path]ehRecvr.exe. The specified module could not be found."
- "Runtime Error. ehRecvr.exe pure virtual function call."
- "This program can't start because ehRecvr.exe is missing from your computer."
- "Unable to launch the software located at path: [path]ehRecvr.exe"
- "This application requires the file ehRecvr.exe, which was not found on this system."
- "ehRecvr.exe is missing."
- "Access Violation File [path]ehRecvr.exe"
Solution
 Error Causes
Error Causes
There are plenty of reasons why this error may occur these include:
- EhRecvr.exe file is mistakenly deleted
- EhRecvr.exe file is corrupted and damaged
- Viral/Malware infection
- Bad registry entries
- Outdated drivers
Though this error code is not fatal but nonetheless it is advisable to fix it immediately because EhRecvr.exe error not just hampers your ability to run and access different programs on your system but it also triggers issues like viral infection and registry problems which if not resolved can put your big at greater risk like system failure, freeze, and crash.
Further Information and Manual Repair
To resolve the EhRecvr.exe error on your system, you don’t have to hire a professional and spend hundreds of dollars in repair. Here are the best and easy DIY methods that you can try to fix this error.
To work around these methods you don’t need to be a technical whiz.
Let’s get started:
Method 1 - Restore EhRecvr.exe from Recycle Bin
In the case of EhRecvr.exe file deletion, it is advisable to
check the recycle bin. Search through the bin for the file. If you find it, then simply restore it, if not then if you have access to the internet, then download it from a trusted website.
Method 2 - Reinstall the Associated Software That Uses EhRecvr.exe File
If you receive this error when you want to use certain software on your PC, then try reinstalling that software again on your PC.
This will be very helpful to obtain the EhRecvr.exe file that is not provided by Microsoft. To re-install, first, uninstall the program. Go to Add/Program in the control panel and find the program and then uninstall it.
Once uninstalled, simply follow the same steps but this time round install the software. This will hopefully help resolve the EhRecvr.exe error code.
Method 3 - Update Drivers for Hardware Devices
Sometimes the error may pop up due to outdated drivers. If this is the cause then the best way to resolve the issue would be to update the driver. Use the wizard within the Device Manager to update the outdated drivers.
Method 4 - Scan for Viruses
Viruses and malware can disguise as executable files. These usually enter your PC through downloads from unreliable websites and phishing emails. In such an event, it is recommended to install a powerful antivirus. Scan your entire PC and remove all viruses to repair the issue.
Method 5 - Clean and Repair the Registry
Another method is to clean and repair the registry. If you don’t clean the registry regularly it may get accumulated with obsolete files and get corrupt. This may generate EhRecvr.exe error codes.
To resolve, simply download Restoro. This is a user-friendly PC Fixer with a powerful registry cleaner. It scans for all registry errors, wipes out all the invalid entries and obsolete files and repairs corrupted DLL and .exe files in minutes.
Click here to download Restoro and resolve the EhRecvr.exe error now!



 The first thing that would pop into my mind is that I have lost tons of work and that something in my hardware has gone very wrong and it is dead. Luckily that is not the case and this error means that due to Windows update drivers were not properly transferred due to some compatibility issues, maybe it was a corrupt update file, etc. Of course, the reason could be hardware malfunction as well, but if everything was working fine before the update, it is a software issue, and I must say it is a common one and fixable. Please keep reading this guide in order to fix the Device not migrated error.
The first thing that would pop into my mind is that I have lost tons of work and that something in my hardware has gone very wrong and it is dead. Luckily that is not the case and this error means that due to Windows update drivers were not properly transferred due to some compatibility issues, maybe it was a corrupt update file, etc. Of course, the reason could be hardware malfunction as well, but if everything was working fine before the update, it is a software issue, and I must say it is a common one and fixable. Please keep reading this guide in order to fix the Device not migrated error.
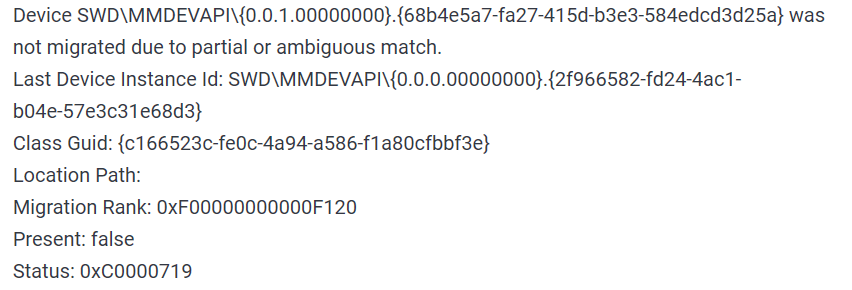
 Find device inside device manager, right-click on it, and choose properties. Go to the events tab and make sure that the device has migration issues.
Find device inside device manager, right-click on it, and choose properties. Go to the events tab and make sure that the device has migration issues.
 You have now 3 options for updating the driver, you can do it manually, automatically, or with the driver installer. We will cover all 3 options so you choose which one best suits you.
OPTION 1: Manually.
Close the Properties tab, go to the device manufacturer website and download the latest driver, if there are no drivers there, the only executable installer for the device skip this step and try the other 2. After you have downloaded the driver package from the website, right-click on the device and choose update driver.
You have now 3 options for updating the driver, you can do it manually, automatically, or with the driver installer. We will cover all 3 options so you choose which one best suits you.
OPTION 1: Manually.
Close the Properties tab, go to the device manufacturer website and download the latest driver, if there are no drivers there, the only executable installer for the device skip this step and try the other 2. After you have downloaded the driver package from the website, right-click on the device and choose update driver.
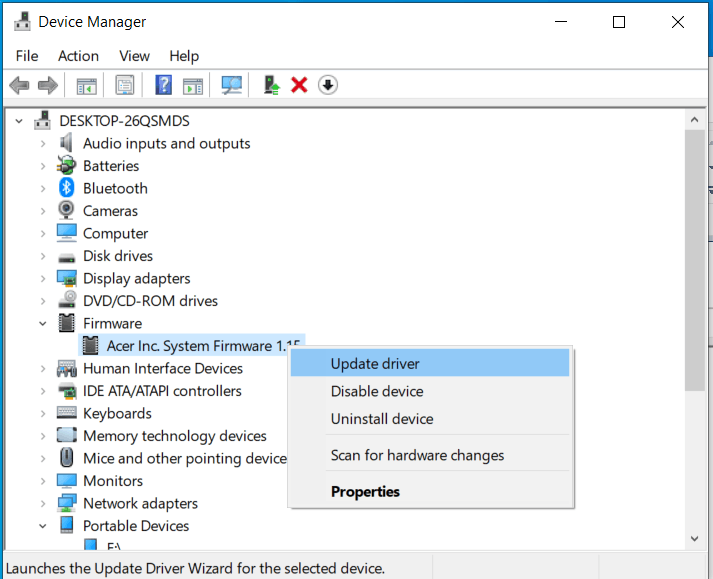 Now navigate to the folder where you have downloaded your driver package and update the driver. Reboot your system.
OPTION 2: Automatic update.
Close the Properties tab, right-click on the device and choose to uninstall.
Now navigate to the folder where you have downloaded your driver package and update the driver. Reboot your system.
OPTION 2: Automatic update.
Close the Properties tab, right-click on the device and choose to uninstall.
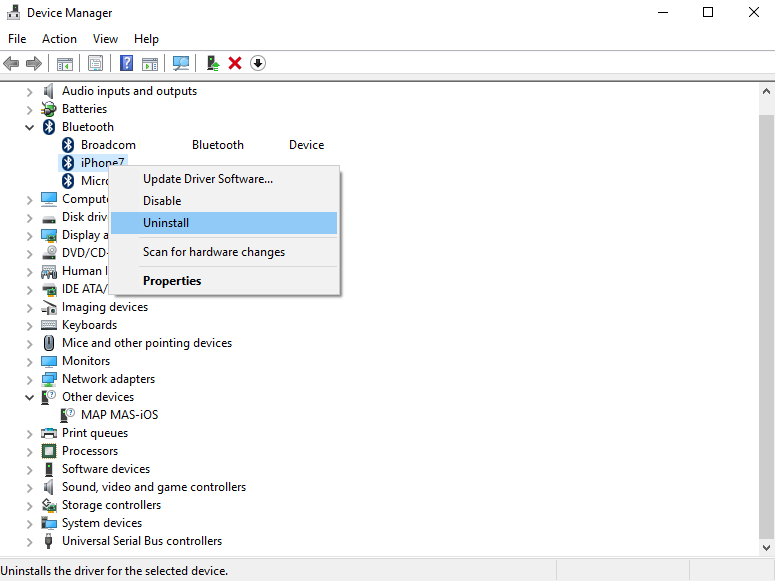 Once the device is uninstalled, restart your system, and Windows will automatically search and install the latest driver for the device.
OPTION 3: Via driver installer.
If you have downloaded .EXE or executable driver installer from device manufacturers web site try installing it, if the installation fails, try using compatibility mode for the installer. Navigate where the installer is located, right-click on it, and choose properties. Go to compatibility TAB and try installing it with administrator privileges in Windows 8 mode.
Once the device is uninstalled, restart your system, and Windows will automatically search and install the latest driver for the device.
OPTION 3: Via driver installer.
If you have downloaded .EXE or executable driver installer from device manufacturers web site try installing it, if the installation fails, try using compatibility mode for the installer. Navigate where the installer is located, right-click on it, and choose properties. Go to compatibility TAB and try installing it with administrator privileges in Windows 8 mode.
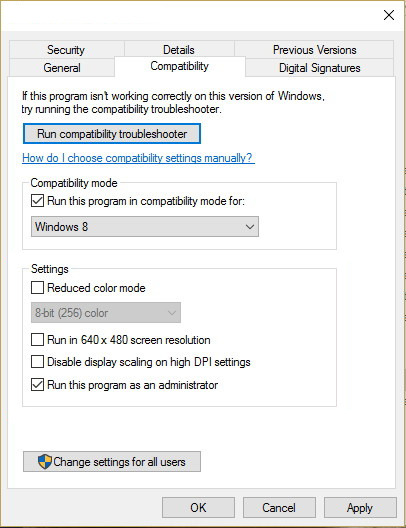 Reboot your system after this step.
This should solve the issues, however, if the issue still persists, follow the next steps.
Reboot your system after this step.
This should solve the issues, however, if the issue still persists, follow the next steps.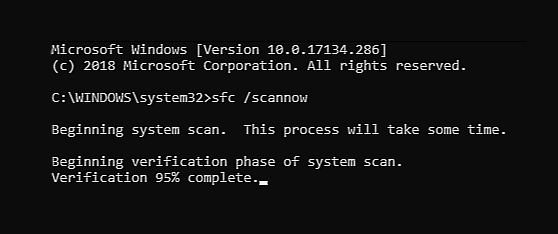 The scanning process and repair of files will take around 15 min. Leave it to finish completely, do not restart, work on the computer or shut it down while the process is active, and only after it is finished reboot your system.
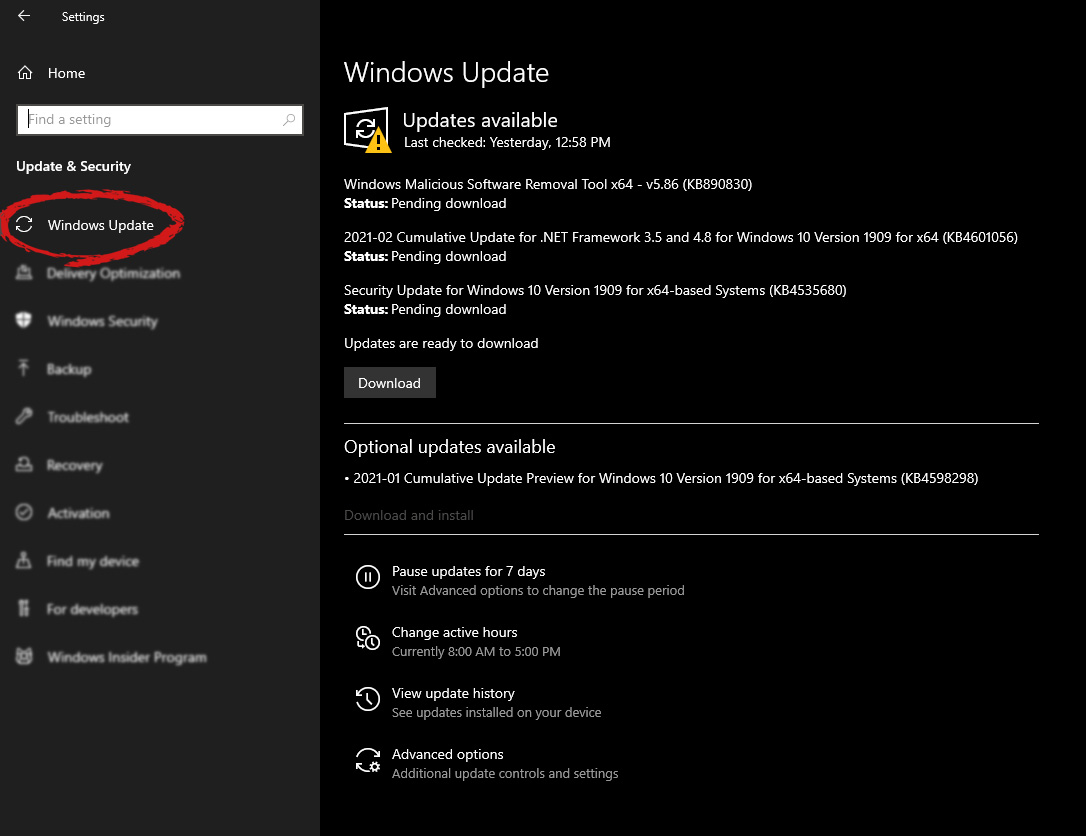
The scanning process and repair of files will take around 15 min. Leave it to finish completely, do not restart, work on the computer or shut it down while the process is active, and only after it is finished reboot your system.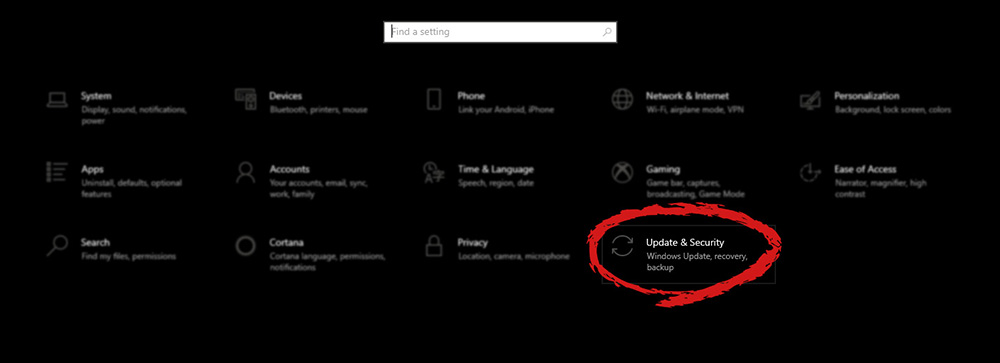 Go to the Windows update tab and click on DOWNLOAD or click on check for updates for the latest Windows fix.
Go to the Windows update tab and click on DOWNLOAD or click on check for updates for the latest Windows fix.
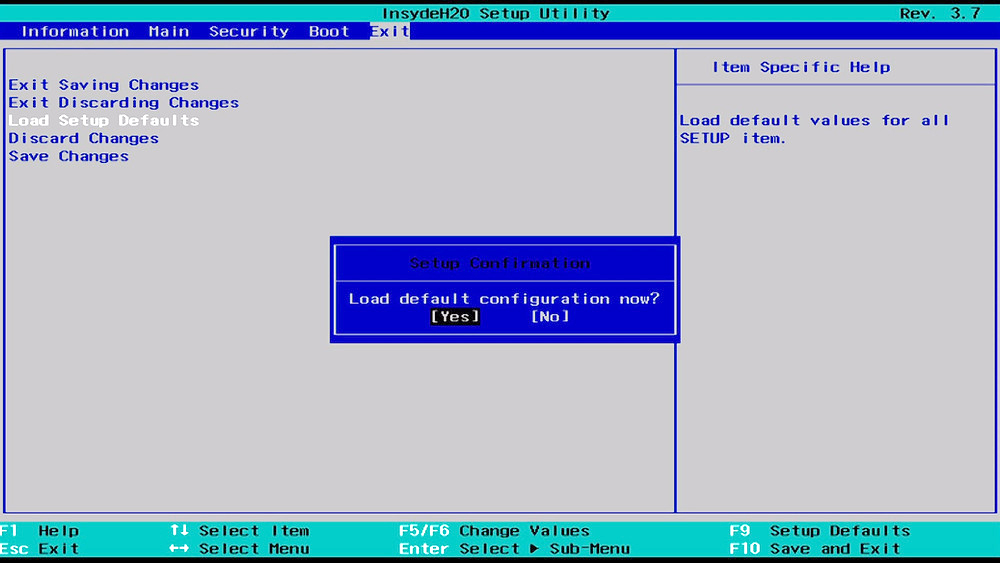
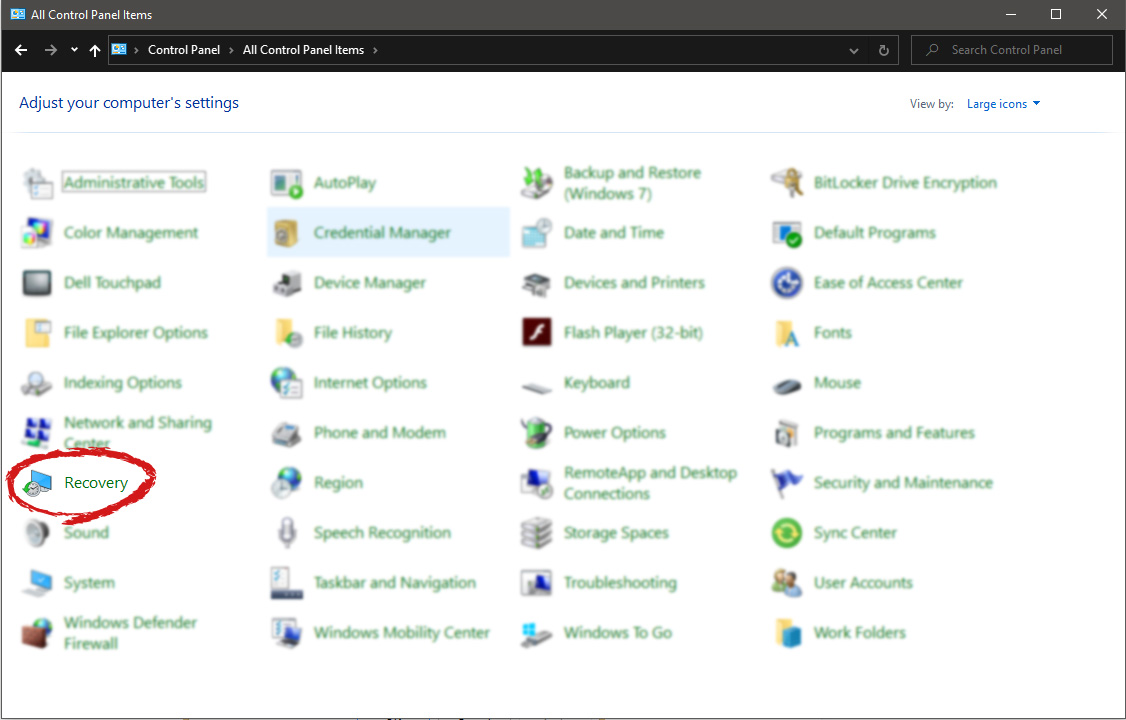
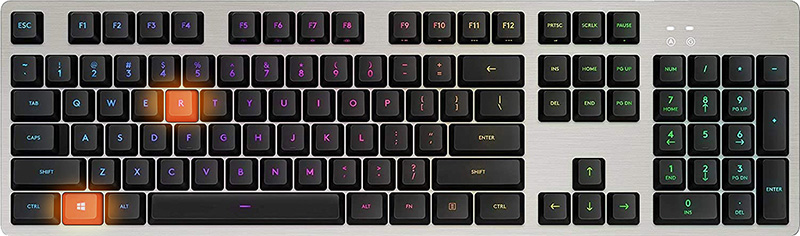 In the run dialog, type control panel and press enter to enter control panel, locate recovery and click on it.
In the run dialog, type control panel and press enter to enter control panel, locate recovery and click on it.
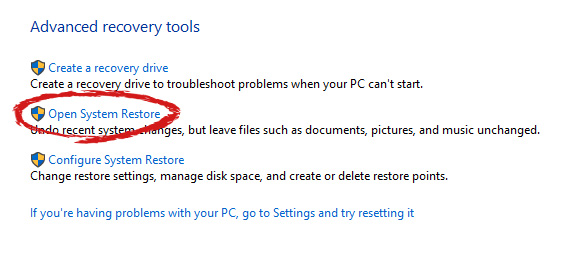
 Inside the recovery screen click on Open System Restore.
Inside the recovery screen click on Open System Restore.
 Choose a date when everything was working in order, the best bet is the date before Windows update and roll it back.
Choose a date when everything was working in order, the best bet is the date before Windows update and roll it back.
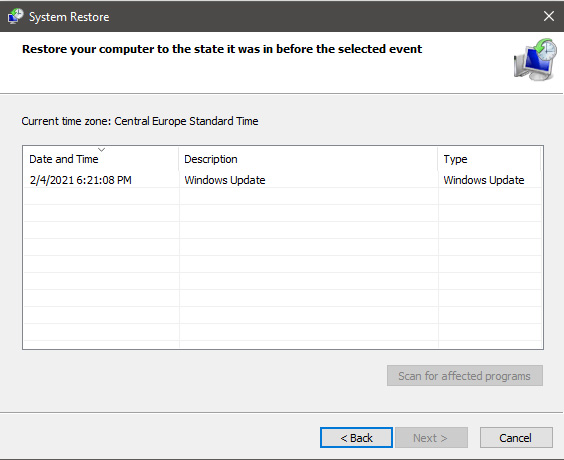 Click on date, and then on next.
Click on date, and then on next.