Error Code 0x802400d - What is it?
The Error Code 0x802400d most often occurs when users attempt to use the Windows Update tool on their computers to move from one version of the software to another. In some cases, this error is more likely to appear on your computer during the process if you have not performed regular updates to the software as they have been available.
Common symptoms include:
- Inability to finish the download of the necessary update to Windows 10
- Incomplete installation of the desired Windows 10 update
While it can take additional time to deal with the issues that cause Error Code 0x802400d to appear on your computer, there are several steps that you can take to address the problem. These are fairly simple to perform and do not require advanced knowledge of the system to employ.
Solution
 Error Causes
Error Causes
The most basic cause for Error Code 0x802400d is that there is a file or a process that is causing the update process to hiccup. In many cases, this error appears when a user attempts to begin the process of updating their computer if they have several stacked updates to perform. Computers that are several updates behind where they should be will display this error more often than computers that are kept on a schedule of recommended updates.
Further Information and Manual Repair
While there are multiple reasons why the Error Code 0x802400d may appear on your computer during the Windows Update process, there are several methods that can be used to attempt to resolve the problem on your own. These are generally easy to do and do not require advanced techniques. However, if you do not feel comfortable addressing the issue on your own, contact a qualified Windows repair technician.
Here are some of the best methods that users can employ to resolve Error Code 0x802400d:
Method 1: Run the System Update Readiness Tool
There are a number of different processes, files, and settings that could cause Error Code 0x802400d to appear on your computer during the Windows 10 Update process. For this reason, the most efficient way to determine what the culprit is for your specific issue is to download and use the System Update Readiness function.
This tool is available directly from Windows. Although there are other tools available on the Internet that claim to be able to fix the problem, these can contain viruses and malware, so be cautious if you decide to employ these instead. There are also several versions of the tool on the Windows website, so be sure to download the version that matches the operating system and version of your computer.
Once you have downloaded the Readiness tool from the Windows website, allow it to run a scan on your system. At a minimum, this process will take about fifteen minutes to complete. Although you will see a progress bar at the bottom of the window, it does not always update effectively. Some users have reported that the update appears to stop when it is two-thirds complete. Continue to let the scan run if this happens, rather than canceling it out. Even if the progress bar doesn’t update, the scan is still running.
Method 2: Remove New Software and Re-Attempt the Update Process
If you have recently installed new software on your machine, it can sometimes cause problems with the update process. The best way to resolve this issue is to remove or uninstall the software, run the update process again, and then reinstall the software once the Windows system has been successfully updated.
If the above methods are not successful in resolving Error Code 0x802400d from your machine and you are still unable to complete the Windows 10 Update process or if you are not confident in your ability to complete these steps successfully on your own, get in touch with a qualified computer repair technician who is familiar with the issues surrounding Windows 10 in particular. Microsoft offers certifications for Windows repair technicians, so look for a professional who has the experience, skills, and knowledge necessary to adequately address Error Code 0x802400d on your machine.
If you wish to always have at your disposal a utility tool to fix these Windows 10 and other related issues when they do arise, download and install a powerful automated tool.

 You can it here:
You can it here:  What exactly is GitHub?
What exactly is GitHub?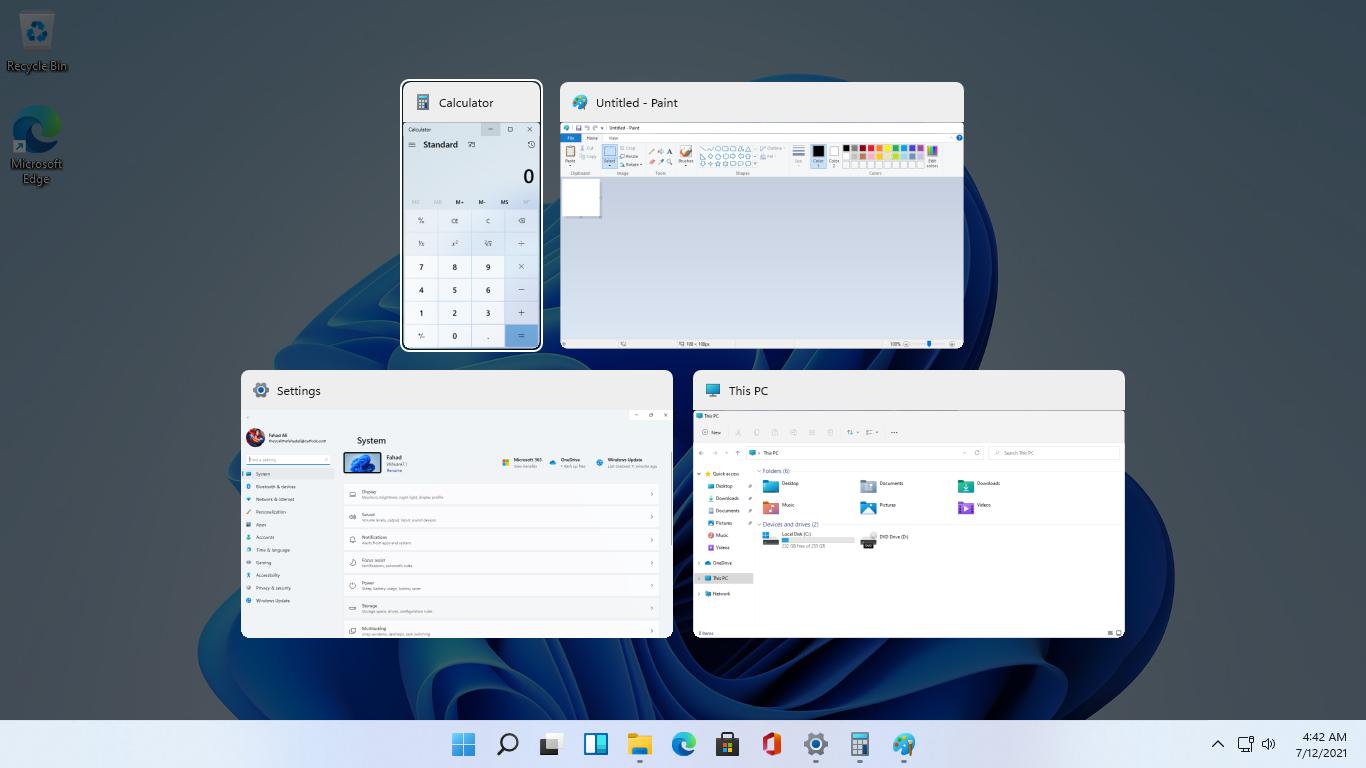 As in previous Windows 10, inside Windows 11 also when you press the ALT + TAB key combination you will get a preview of all running applications along with all Browser tabs so you can go through them and pick the one you want to switch to.
Alto, I personally am a big fan of alt-tabbing, I must admit that I am not a big fan of having multiple browsers tabs on screen when I do press key combo. Luckily there is a very easy way to turn this feature off.
Turning browsers tabs thumbnails off
As in previous Windows 10, inside Windows 11 also when you press the ALT + TAB key combination you will get a preview of all running applications along with all Browser tabs so you can go through them and pick the one you want to switch to.
Alto, I personally am a big fan of alt-tabbing, I must admit that I am not a big fan of having multiple browsers tabs on screen when I do press key combo. Luckily there is a very easy way to turn this feature off.
Turning browsers tabs thumbnails off
