Wondering if upgrading to Windows 11 will boost your gaming experience? We can’t give you a straightforward answer, sadly. But we can take you through the tweaks you can expect if you have all the right requirements and help you make a final decision.
Is Windows 11 good for gaming?
Essentially, the answer to this question is yes. Microsoft has definitely added a bunch of enhancements and features to its latest OS to give gamers the best possible experience. However, you have to keep in mind that this may not work out smoothly for every single user.
Whether you’ll be able to fully take advantage of the Windows 11 gaming features really depends on your setup. As expected, Windows 11 has more demanding system requirements than its predecessor.

So, unless your hardware can run the new OS comfortably, you might not be able to make the most of all these gaming perks. In that case, we recommend you first upgrade your hardware and then make the switch. Be prepared to be a little surprised by a few other interesting changes in comparison to Windows 10, though!
For some of the new gaming features to work, it’ll also be necessary for you to have an NVMe SSD and an HDR-compatible monitor. So let’s take a look at 4 big improvements you can expect if your setup is compatible.
Gaming enhancements on Windows 11
1. Enjoy faster loading speed with DirectStorage
For this powerful feature to work, you need a compatible graphics card and, as stated before, an NVMe SSD. It’s also important for your GPU to support the DirectX 12 graphics API at least. And since we’re on that subject, you’ll be happy to know that Windows 11 has also introduced a new version of the API called DirectX 12 Ultimate.
Now, what does DirectStorage do? It’s a new feature designed to make full use of the speedy storage of NVMe SSDs. It also transfers game data directly onto the graphics card, lightening the load on your CPU. Normally the CPU would have to decompress the data first, but DirectStorage helps bypass this. That’s how loading times are reduced and games run more smoothly.
2. Fully immerse yourself through Game Mode
Windows 11’s Game Mode is certainly a welcomed addition. When you turn on Game Mode, usage of background apps that aren’t essential to your game is reduced. This results in the game you’re running becoming a priority process. This way, it uses your hardware and system resources to the max. Ultimately, the Game Mode means less lag and higher frame rates so you can play undisturbed and fully enjoy your gaming session.
3. Vibrant visual experience thanks to AutoHDR
For this one you’ll absolutely need an HDR-compatible monitor. Basically, HDR (High Dynamic Range) means a wider range of contrasts and colors that can be displayed on a monitor.
Windows 10 has an HDR feature, but you have to turn it on and off manually (“Use HDR”). Plus, users have reported that, if left on, it results in an unappealing appearance of content other than movies and games.
Windows 11 fixes that problem with its AutoHDR feature. Toggling it results in the system automatically adjusting the color contrast, balance and brightness based on what you’re currently looking at. For gamers, this means vivid imagery in every single game, resulting in a supreme visual experience. You can check out Microsoft’s own video showcasing the power of AutoHDR.
Aside from AutoHDR, another way Windows 11 improves the visual aspect is through its support for refresh rates of up to 360Hz.
4. Xbox Game Pass & Game Bar
It’s no secret that Microsoft wants to integrate Windows and Xbox. We’ve seen some attempts with Windows 10, but they’re pretty wonky compared to the new OS.
Windows 11’s built-in Xbox Game Bar enables quite a few options all gamers desire. You can take screenshots and videos of your game and send them, for starters. Furthermore, you can use it to see audio settings and monitor your PC’s performance without having to leave the game or open the Task Manager.
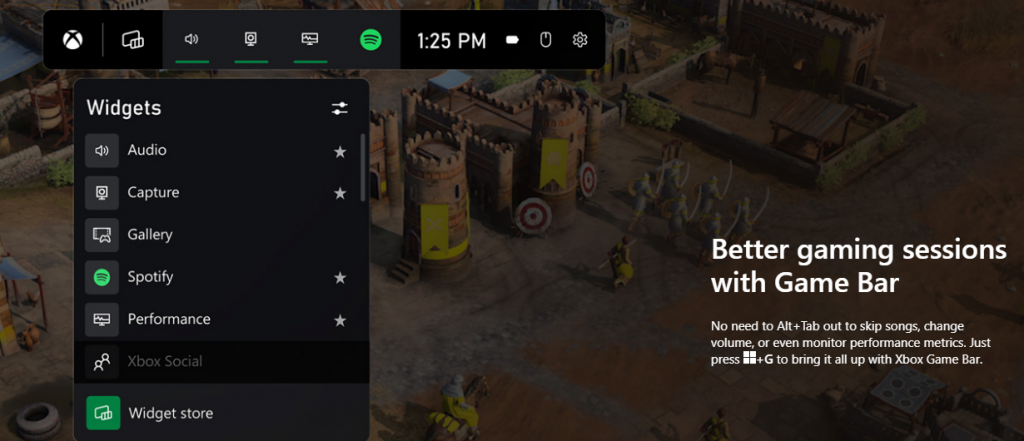
Widgets are also a really cool part of the Game Bar. You can choose from a wide variety of widgets, such as Xbox Achievements, Spotify, Gallery, Xbox Social and more.
Moreover, the Xbox Game Pass has been streamlined on Windows 11. Game Pass is a subscription service that unlocks hundreds of awesome games and supports cloud streaming. Do keep in mind that the games are only unlocked for a certain period of time, as the selection rotates once in a while.
What can you do for a better gaming experience?
Windows 11 does offer tweaks that require zero input from you. However, there are a few things you can do manually to get even more out of your new OS while gaming.
- Turn off enhanced pointer precision. Most games enhance precision by default, so having this feature on might interfere with that.
- Make sure to select your high performance graphics card for each game. Go to Settings > Gaming > Game Mode and tap ‘Graphics’ from the ‘Related settings’ menu. Find the game you want to adjust, click on ‘Options’ and choose your high performance graphics card to be the default setting. While there, you can also turn on ‘Hardware-accelerated GPU scheduling’ at the top.
- Disable unnecessary apps and programs. As long as they aren’t essential to running your game, they might take up valuable system resources, so disable them to make space for your gaming requirements.
- Check for pending updates and install them. It’s well-known that out-of-date software causes bugs, latency and crashes. The same goes for your GPU drivers.
- Use the High-performance power plan (Control Panel > Power Options > Additional plans) to maximize the use of resources for the best possible performance.
Summary
Windows 11 has done quite a bit for avid gamers. We hope your setup is compatible with all these new features and you can experience these enhancements ASAP!

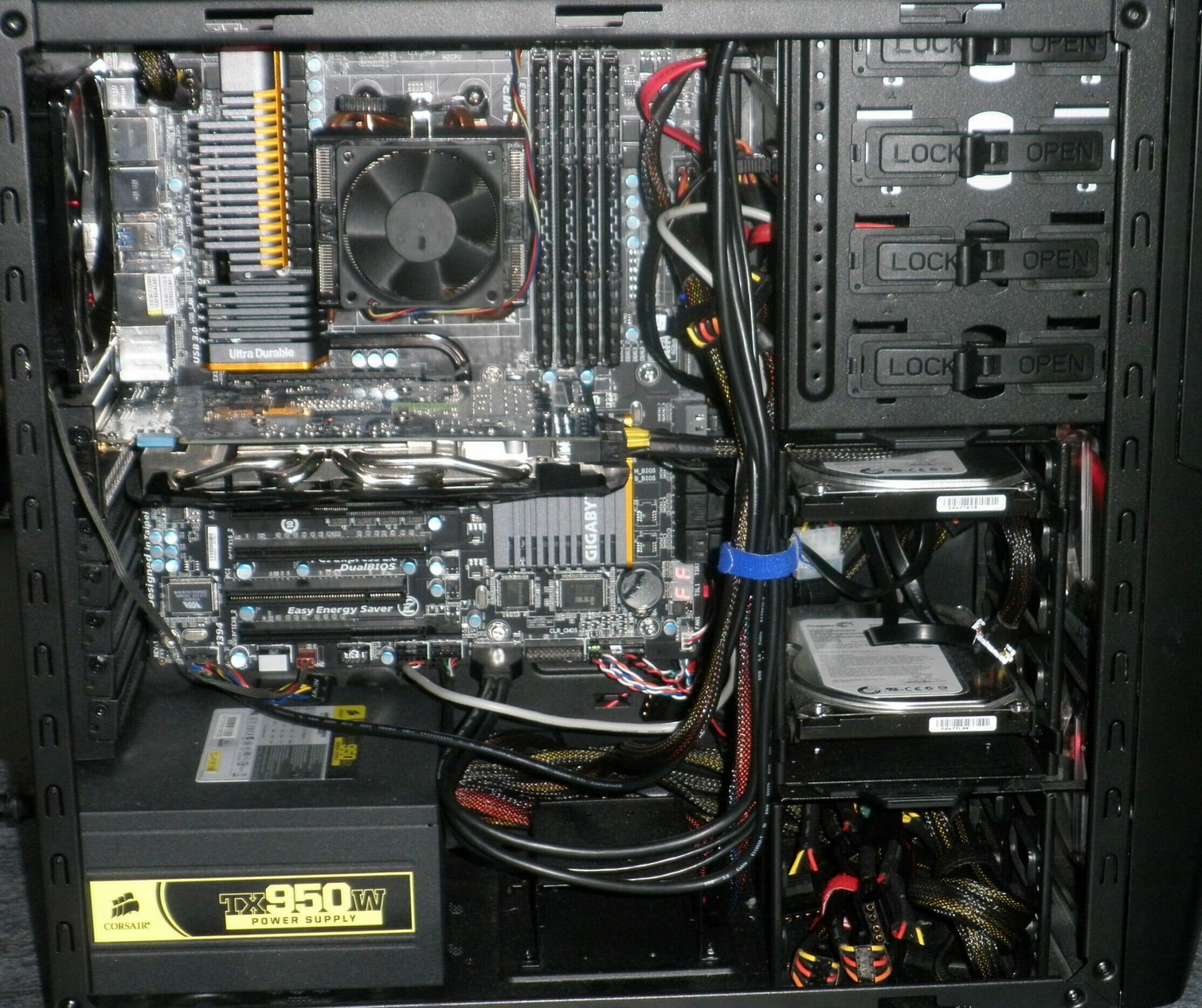
 Keeping your PC clean is not rocket science and you can do it with things you already and probably have in your house. One thing that I would recommend tho to purchase is antistatic gloves since they could prevent any kind of electrostatic discharges thus protecting your electric components.
If you have the option to disconnect your PC and get it outdoors, I would highly recommend this approach since all the dust will be dusted outside and not in the room where your computer is. If you can not it is still ok, but since some portion of dust will be set in the room, you might need to dust your room after cleaning your computer.
Keeping your PC clean is not rocket science and you can do it with things you already and probably have in your house. One thing that I would recommend tho to purchase is antistatic gloves since they could prevent any kind of electrostatic discharges thus protecting your electric components.
If you have the option to disconnect your PC and get it outdoors, I would highly recommend this approach since all the dust will be dusted outside and not in the room where your computer is. If you can not it is still ok, but since some portion of dust will be set in the room, you might need to dust your room after cleaning your computer.
 Removing options all together
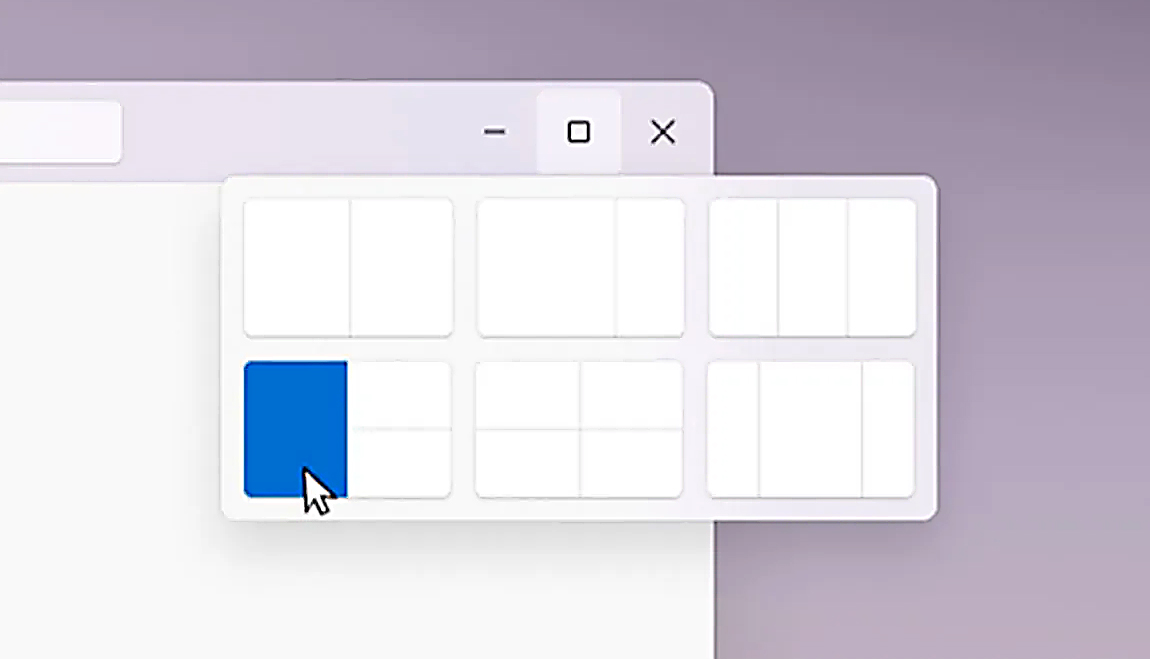
Removing options all together Microsoft just released Windows 11 ISo file, based on the latest Insider Preview Build 22000.132. Inside build, you can try all-new features like clock updated app, snip tool, and everything releases so far via various patches. You can also use Windows 11 ISO file to do a clean install on your computer, but if you go with this option all of your existing files will be deleted.
Microsoft says it added the ability to name your PC during the setup experience. You’ll also get to experience the Get Started app that’s designed to help you get going on your new Windows 11 PC (even if it’s not actually a new one).
Microsoft just released Windows 11 ISo file, based on the latest Insider Preview Build 22000.132. Inside build, you can try all-new features like clock updated app, snip tool, and everything releases so far via various patches. You can also use Windows 11 ISO file to do a clean install on your computer, but if you go with this option all of your existing files will be deleted.
Microsoft says it added the ability to name your PC during the setup experience. You’ll also get to experience the Get Started app that’s designed to help you get going on your new Windows 11 PC (even if it’s not actually a new one).


