HPQTRA08.exe - What is it?
HPQTRA08.exe (Hewlett Packard Tray 08) is the Hewlett Packard Digital Imaging Monitor task. It is installed with the drivers of HP imaging products like PhotoSmart Printers.
It incessantly monitors and indicates the connectivity status with any recognizable HP product.
Simply put, HPQTRA08.exe is an exe (executable) file that contains step-by-step instructions that a computer follows to carry out a function.
HPQTRA08.exe error code is displayed in any of the following formats:
- "Hpqtra08.exe Application Error."
- "Cannot find hpqtra08.exe."
- "Hpqtra08.exe not found."
- "Error starting program: hpqtra08.exe."
- "Hpqtra08.exe is not a valid Win32 application."
- "Hpqtra08.exe failed."
- "Faulting Application Path: hpqtra08.exe."
- "Hpqtra08.exe has encountered a problem and needs to close. We are sorry for the inconvenience."
- "Hpqtra08.exe is not running."
Solution
 Error Causes
Error Causes
Error code HPQTRA08.exe can be triggered for several reasons. However, some of the most common causes include:
- Corrupt Windows registry keys
- Virus infection
- Deleted, damaged, or corrupted HPQTRA08.exe file
- HPQTRA08.exe file conflict
- Corrupt or incomplete installation of Hp Digital Imaging
It is advisable to repair the error code HPQTRA08.exe on your PC immediately. Delays can lead to serious problems especially if the underlying cause of the error is related to registry corruption.
Further Information and Manual Repair
To resolve this error on your PC, you don’t need to hire a professional and pay hundreds of dollars for the repair. Simply try the DIY methods listed below to fix the problem right away.
Method 1 - Download and Install HPQTRA08.exe File
If the error cause is related to deleted, corrupted, or damaged HPQTRA08.exe file, then the best way to fix the problem is to install the HPQTRA08.exe file on your PC.
However, first, make sure the site you select to download the file from is reliable and trusted.
By downloading from an unreliable website you can expose your PC to potential malicious programs and risk your data security.
Method 2 - Remove all Viruses
Sometimes viruses and malware tend to disguise in the form of exe files such as the HPQTRA08.exe file.
In such a situation scan your entire PC for viruses and malware using a powerful antivirus. Remove all the malicious programs found to fix the issue.
Method 3 - Clean and Repair the Registry
The registry saves all PC-related activities and information including both important and obsolete files such as cookies, bad registry entries, invalid keys, internet history, and junk files.
If these files are not removed from the registry frequently, these accumulate in the registry and corrupt thereby triggering error codes. Error code HPQTRA08.exe is generated when the corrupt Windows registry keys are associated with the HPQTRA08.exe file.
To resolve, clean the registry and repair it. Although this can be done manually it can be time-consuming and tricky especially if you are not technically sound, therefore it is advisable to download Restoro.
Click here to download Restoro and resolve error HPQTRA08.exe.
Method 4 - Locate and Install the Driver
As was pointed out, you might need to reinstall the printer driver again. Using
DriverFIX, you’ll be able to automatically update your computer system and install the drivers your computer needs to operate smoothly.

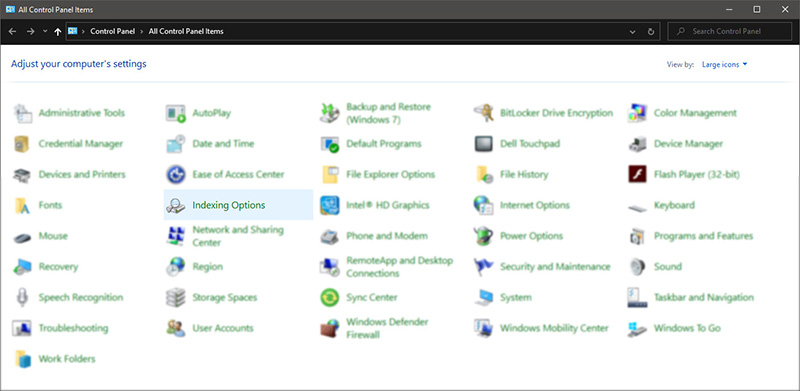
 Once you are in the control panel, switch your view to large icons and locate Indexing options.
Once you are in the control panel, switch your view to large icons and locate Indexing options.
 Inside indexing options, click on advanced.
Inside indexing options, click on advanced.
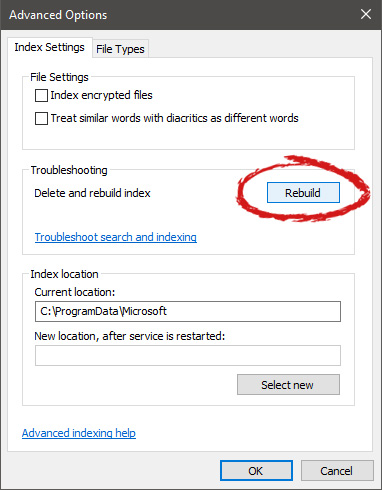
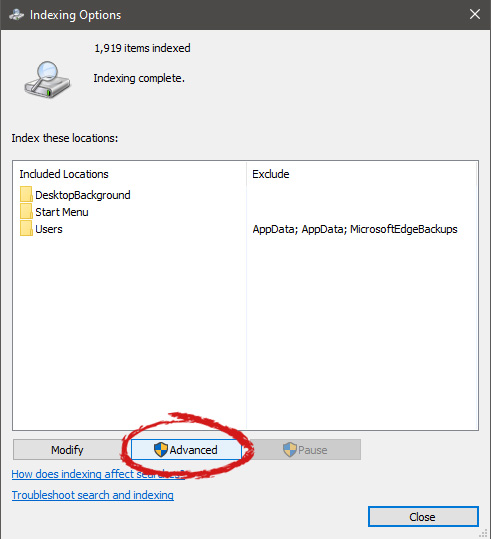 In advanced options click on the rebuild and confirm.
In advanced options click on the rebuild and confirm.
 Leave your computer to finish and your searches should be working fine now.
Leave your computer to finish and your searches should be working fine now.  Storage management Page update
Storage management Page update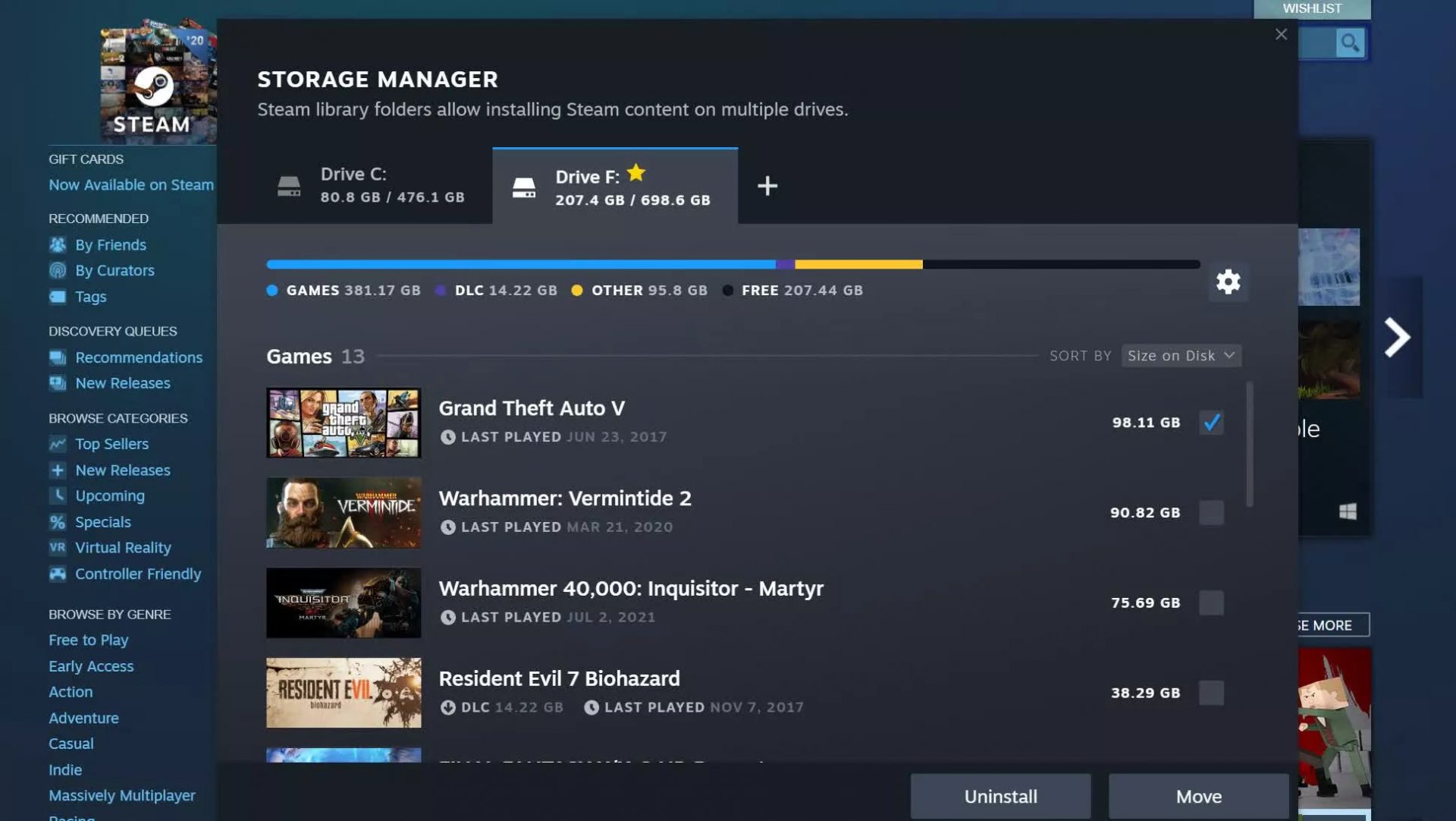 Another thing with the Steam store management page is the ability to move installation files from one location to another. Let’s say that you have two or more hard disk drivers in your machine and that you have SSD that you use for running stuff since it is fast and larger and slower one for storage. Now you can easily and quickly move one installation from one to another in order to take advantage of your faster SSD for quicker LOAD game times without making a new installation.
Another thing with the Steam store management page is the ability to move installation files from one location to another. Let’s say that you have two or more hard disk drivers in your machine and that you have SSD that you use for running stuff since it is fast and larger and slower one for storage. Now you can easily and quickly move one installation from one to another in order to take advantage of your faster SSD for quicker LOAD game times without making a new installation.
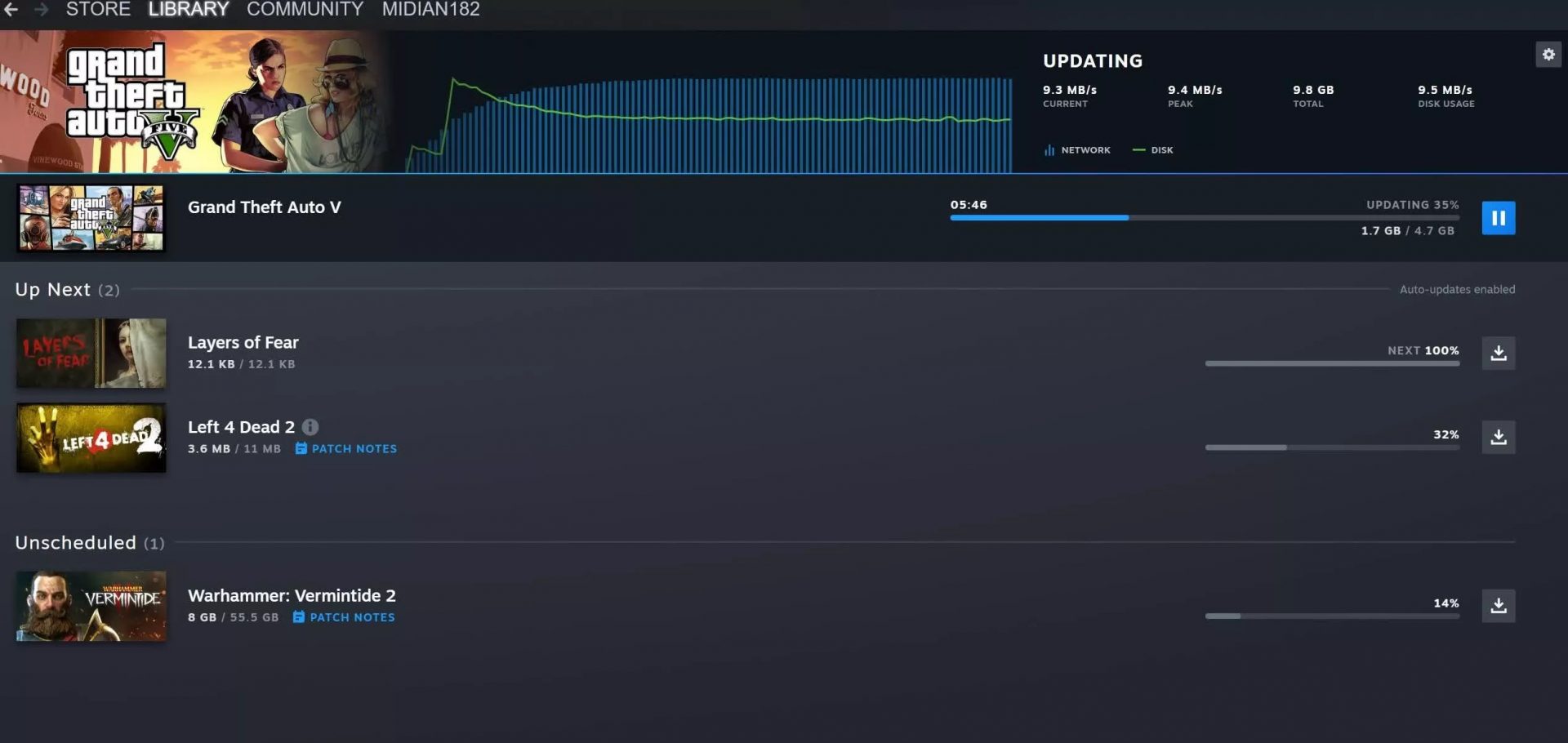 Also, you can now drag and drop items in the download bracket to reorder download orders or place them as active downloads to start downloading right away.
Also, you can now drag and drop items in the download bracket to reorder download orders or place them as active downloads to start downloading right away. 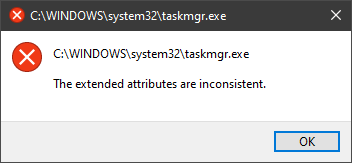 In this guide, we will show you common ways in fixing Extended Attributes are inconsistent errors inside your Windows that are easy to do and less time-consuming than complete reinstallation of the system.
In this guide, we will show you common ways in fixing Extended Attributes are inconsistent errors inside your Windows that are easy to do and less time-consuming than complete reinstallation of the system.

