Error 126 - What is it?
Error 126 is a Windows PC error that mostly occurs either during program installation or removal. It is commonly experienced by Vista, XP and Windows 7 users. When the error 126 is generated, it usually terminates the program installation process, immediately.
It is advisable to take corrective error repair measures immediately to ensure that you are easily able to install your desired program and you don’t encounter the error again.
Solution
 Error Causes
Error Causes
There are multiple reasons for the occurrence of the error code 126 including. The reasons are listed below:
- Dll file corruption
- Missing or damaged dll files
- Corrupt and misconfigured system files
- Improper program installation
- Viral infection
- Corrupt registry
- Improper hardware
Further Information and Manual Repair
To resolve the error 126 on your PC, you don’t always have to hire a technician or be a computer programmer yourself. Though this error is critical the good news is that it is very easy to resolve. You can fix the error even if you are not technically sound.
Try the solutions that we have listed below to help you resolve error 126 immediately:
Solution 1: Disable Firewall Protection
Sometimes
Firewall protection may stop you from installing new programs on your PC successfully and this may display the error 126 on your PC. In such a scenario, disable Firewall protection and then try installing the desired program again. See if it works.
Solution 2: Restore Points
Sometimes dll files can go missing due to program removals and you may come across the error 126. To resolve it, restore points.
This will help you restore your PC back to the way it was functioning before you removed a program and will also help you recover the lost and missing dll files.
- This can be done, by clicking the start menu.
- Now go to all programs, then accessories, and then system tools.
- Here you will see the ‘System Restore’ option. Simply click on it.
- This will help you open a new window. Here select the option ‘Restore My Computer to an Earlier Time’ point.
- As you select it, it will show you a list of restore points.
- Choose the latest restore point you see in the list and click ‘Next’ to continue. Now confirm to finish restoration.
- Restart your PC to activate the changes.
Solution 3: Scan for Viruses
The underlying cause for the error could also be related to viruses on your PC. To remove the viruses, you will have to download a powerful antivirus and scan your entire PC.
Please note, anti-viruses are notorious for slowing down system performance, so you might have to compromise on the speed of your PC.
Solution 4: Run a Hardware Diagnostic
To find out which hardware is causing the error message to pop up, you will have to run a hardware diagnostic. For this, simply go to the start menu, type Memory Diagnostic in the search bar.
Now access this tool and click on Diagnose your Memory problems. As you click on it, it will ask you to perform the check by either restarting the PC immediately or on the next restart.
Select the immediate one to get going. The system will carry a scan on the memory and show you the list of problematic errors detected during the scan. To resolve this error then all you have to do is replace the piece of faulty hardware. Nonetheless, if no faulty hardware is detected, this means the error is related to the registry.
Solution 5: Clean and Restore the Registry
The error 126 is also sometimes generated due to poor PC maintenance which leads to registry issues.
The registry basically saves and stores all the data and activities performed on the PC. This also includes junk files, invalid registry entries, bad keys, temporary files, internet history, and cookies.
This accumulates a lot of disk space. If not removed, they damage the registry and corrupt other important files like system and dll files, thereby generating PC-related error codes like error 126.
The best way to resolve this error on your PC in seconds is to download Restoro on your PC. This is an advanced and multi-functional PC repair tool embedded with multiple powerful utilities including an intuitive registry cleaner, an antivirus, and a system optimizer.
The registry cleaning feature detects all registry issues and errors. It wipes out all the unnecessary and obsolete files cluttering the system, fixes the damaged dll files, and restores the registry back to normal.
Simultaneously, the antivirus utility scans for all privacy errors and malicious software infecting your system. This includes malware, adware, spyware, and Trojans.
The system optimizer feature ensures your PC performance does not slow down. It boosts the speed of your PC to its optimum level.
This PC fixer is safe, user-friendly, and efficient. It can be downloaded on any Windows version.
Click here to download Restoro on your system and resolve error 126 right away!
 In order to make a keyboard shortcut for the desired folder know that it is available only when you have a shortcut of the desired folder, it cannot be done on the folder itself, only on its shortcut. Now folder shortcut does not need to reside on desktop, you can place it anywhere you like, but it must be a shortcut.
So the first step is of course to make a shortcut of the folder that you wish to have access via keyboard key combination and place it where you wish.
Once you have done this step, right-click on it and choose properties. Inside properties at the top click on the Shortcut tab and then inside Shortcut Key, press the key combination that you wish to associate with this folder. Confirm with OK and start using fast folder access with your desired key combination.
In order to make a keyboard shortcut for the desired folder know that it is available only when you have a shortcut of the desired folder, it cannot be done on the folder itself, only on its shortcut. Now folder shortcut does not need to reside on desktop, you can place it anywhere you like, but it must be a shortcut.
So the first step is of course to make a shortcut of the folder that you wish to have access via keyboard key combination and place it where you wish.
Once you have done this step, right-click on it and choose properties. Inside properties at the top click on the Shortcut tab and then inside Shortcut Key, press the key combination that you wish to associate with this folder. Confirm with OK and start using fast folder access with your desired key combination. 

 As in most usual online scams, everything starts with a strange email containing threats and other poorly written and composed speech. At the end of the given email, there would be a link claiming that you, of course, need to read it and follow instructions about the threat, if you click the link it will open a web page where you will have an innocent-looking PDF file with more information about the threat itself.
If you click on a seemingly innocent PDF file it will summon Windows 10's AppInstaller.exe tool, kickstarting a download-and-run process that'll put you in a bad place very quickly. From there, you'll have to deal with the dangers of malware BazarBackdoor, including data and credential theft.
This kind of scam is nothing new but the interesting thing here is that it uses App installer and by clicking on a link you are opening and giving permission for a malicious crook to use it. So, stay safe and do not click on any links from unknown emails no matter what.
As in most usual online scams, everything starts with a strange email containing threats and other poorly written and composed speech. At the end of the given email, there would be a link claiming that you, of course, need to read it and follow instructions about the threat, if you click the link it will open a web page where you will have an innocent-looking PDF file with more information about the threat itself.
If you click on a seemingly innocent PDF file it will summon Windows 10's AppInstaller.exe tool, kickstarting a download-and-run process that'll put you in a bad place very quickly. From there, you'll have to deal with the dangers of malware BazarBackdoor, including data and credential theft.
This kind of scam is nothing new but the interesting thing here is that it uses App installer and by clicking on a link you are opening and giving permission for a malicious crook to use it. So, stay safe and do not click on any links from unknown emails no matter what.  Once it opens, click on Device Manager to open it,
Once it opens, click on Device Manager to open it,
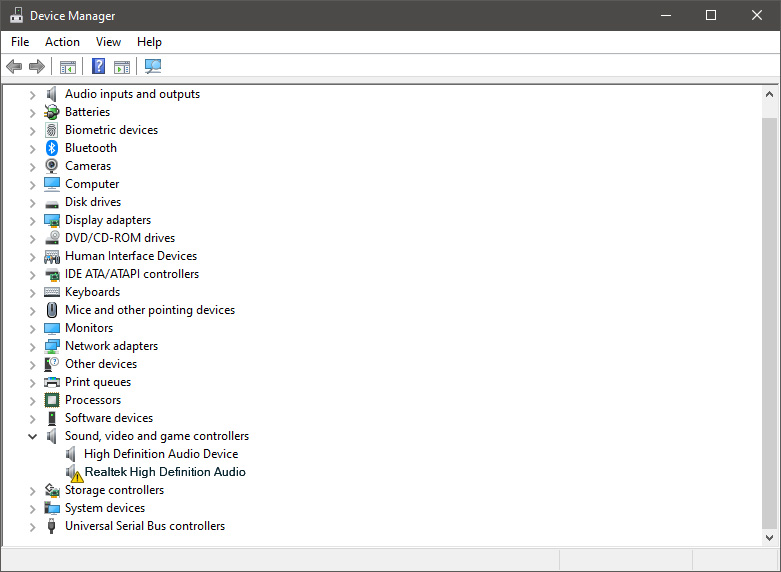 If you have a driver device error inside Windows, you should see it immediately when entering the Device Manager, it will have a yellow exclamation mark beside it. Right-click on it and choose update driver.
If you have a driver device error inside Windows, you should see it immediately when entering the Device Manager, it will have a yellow exclamation mark beside it. Right-click on it and choose update driver.
