PC Performer is a registry cleaner made by PerformerSoft. The purpose of this program is to remove redundant items from the Windows registry. Registry cleaners remove broken links, missing references within the Windows registry. PC performer is designed to automatically optimize your registry and clean it up.
PC Performer adds registry entries for the current user that allow it to run automatically each time the system is rebooted. It adds a scheduled task to Windows Task Scheduler in order to run at various times. The software connects to the internet, therefore it creates a Windows Firewall exception that allows it to connect without interference. Multiple anti-virus programs detected this software as Malware, it typically comes bundled with other software or is distributed through a pay-per-install bundle.
About Potentially Unwanted Applications
People have encountered it – you download and install a piece of free software application, you then see some unwanted applications on your computer or discover a strange toolbar has been added to your browser. You didn’t install them, so how did they turn up? These unwanted programs, technically known as Potentially Unwanted Programs (PUPs), often come bundled along with other software and install themselves on user’s PC without their knowledge. They perhaps might not look like viruses to some individuals, but they can produce major annoyances and bring about serious trouble for users.
The idea of PUP was coined to define this downloadable crapware as something other than malicious software. Much like malware, PUPs create problems when downloaded and placed on your computer, but what makes a PUP different is that you provide consent to download it – the fact is vastly different – the software installation bundle actually tricks you into agreeing to the installation. Still, there isn’t any doubt that PUPs are still bad news for computer users as they can be incredibly damaging to your computer in lots of ways.
What do PUPs look like?
The unwanted software programs after installation display loads of annoying pop-up adverts, create fake alerts, and quite often it even pushes the user to buy the software. Likewise, the majority of free software applications these days come with quite a few unwanted add-ons; in most cases a web browser toolbar or browser modification such as a homepage hijacker. Not only they needlessly use up space on your screen, but toolbars can also manipulate search engine results, watch your browsing activities, decrease your web browser’s performance, and decelerate your net connection to a crawl.
PUPs employ aggressive distribution techniques to get in your computer. Some might include information gathering program code that could collect and send your private information back to third parties. Due to this unwanted program, your application may freeze, your security protections may get disabled that might leave the computer susceptible, your system may get ruined, and the list goes on and on.
Tips on how to prevent ‘crapware’
• Read cautiously before agreeing to the license agreement as it may have a clause about PUPs.
• Usually, when setting up a program you will get two options, ‘Standard Installation (recommended)’ and ‘Custom Installation’. Don’t select ‘Standard’ as PUPs could be installed that way!
• Use good anti-malware software. Try Safebytes Anti-Malware which will find PUPs and handle them as malware by flagging them for removal.
• Be alert when you install freeware, open-source software, or shareware. Avoid downloading browser extensions and programs you are not familiar with.
• Only download applications from the original providers’ sites. Avoid download portals as they use their own download manager to pack additional programs with the initial download.
What you can do if Virus Stops You From Downloading Or Installing Anything?
Malware could potentially cause several kinds of damage to computer systems, networks, and data. Certain malware goes to great lengths to stop you from installing anything on your PC, especially antivirus applications. If you’re reading this right now, you have perhaps recognized that a malware infection is a reason for your blocked web traffic. So what to do if you need to install an antivirus program like Safebytes? There are a few actions you can take to get around this problem.
Eliminate malware in Safe Mode
If the virus is set to load automatically when Microsoft Windows starts, getting into Safe Mode could very well block the attempt. Since just the bare minimum programs and services start-up in safe mode, there are hardly any reasons for issues to happen. The following are the steps you should follow to remove malware in Safemode.
1) At power on/start-up, hit the F8 key in 1-second intervals. This will bring up the Advanced Boot Options menu.
2) Select Safe Mode with Networking using arrow keys and hit ENTER.
3) Once you get into this mode, you should have an internet connection again. Now, obtain the malware removal application you need by using the browser. To install the software, follow the directions in the installation wizard.
4) After installation, do a complete scan and let the software delete the threats it detects.
Switch to an alternate browser
Web-based viruses can be environment-specific, targeting a particular web browser or attacking particular versions of the browser. The best solution to overcome this issue is to opt for a browser that is well known for its security features. Firefox contains built-in Phishing and Malware Protection to keep you safe online.
Install and run anti-virus from a USB drive
To successfully eliminate the malware, you will need to approach the issue of installing an anti-virus program on the infected PC from a different angle. Adopt these measures to employ a USB flash drive to fix your corrupted computer.
1) Use another virus-free computer to download Safebytes Anti-Malware.
2) Insert the pen drive into the clean computer.
3) Double-click the Setup icon of the antivirus program to run the Installation Wizard.
4) When asked, choose the location of the pen drive as the place where you would like to put the software files. Follow the on-screen instructions to complete the installation process.
5) Now, insert the pen drive into the infected computer.
6) Double-click the EXE file to open the Safebytes program right from the flash drive.
7) Click “Scan Now” to run a scan on the infected computer for malware.
Highlights of SafeBytes Anti-Malware
Do you want to install the best anti-malware software program for your computer system? There are various applications in the market that comes in paid and free versions for Microsoft Windows systems. A few of them are great and some are scamware applications that pretend as legit anti-malware software waiting around to wreak havoc on your computer. While looking for anti-malware software, select one which gives dependable, efficient, and full protection against all known computer viruses and malware. On the list of recommended software is SafeBytes Anti-Malware. SafeBytes carries a really good track record of top-quality service, and clients are happy with it.
SafeBytes anti-malware is a highly effective and easy-to-use protection tool that is suitable for users of all levels of computer literacy. With its cutting-edge technology, this application will let you remove multiples types of malware which include viruses, worms, PUPs, trojans, ransomware, adware, and browser hijackers.
SafeBytes anti-malware provides an array of advanced features which sets it apart from all others. Listed here are a few of the great ones:
Anti-Malware Protection: Built on a highly acclaimed anti-virus engine, this malware removal tool is able to detect and remove many obstinate malware threats such as browser hijackers, potentially unwanted programs, and ransomware that other typical anti-virus programs will miss.
Real-time Active Protection: SafeBytes offers an entirely hands-free real-time protection that is set to check, prevent and remove all threats at its first encounter. It’ll check your PC for suspicious activity continuously and shields your PC from unauthorized access.
Faster Scan: SafeBytes’s virus scan engine is one of the quickest and most efficient in the industry. Its targeted scanning seriously increases the catch rate for malware that is embedded in various computer files.
Safe Browsing: Safebytes assigns all sites a unique safety ranking that helps you to have an idea of whether the webpage you’re going to visit is safe to view or known to be a phishing site.
Low CPU Usage: SafeBytes is renowned for its minimal influence on processing power and great detection rate of countless threats. It runs silently and efficiently in the background so you’re free to use your computer at full power all the time.
24/7 Customer Support: SafeBytes provides 24/7 technical support, automatic maintenance, and software upgrades for the best user experience.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove PCPerformer without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by PCPerformer
Files:
File at LOCALAPPDATAPCPerformerSetupPCPerformerSetup.exe.
File at PROGRAMFILESPC PerformerPCPerformer.exe.
File at PROGRAMFILESPC PerformerPSCheckUp.exe.
File at PROGRAMFILESPC PerformerRegistryDefrag.exe.
File at WINDIRTasksPC Performer Daily Check.job.
File at WINDIRTasksPC Performer Scheduled Scan.job.
Registry:
Key PC Performer at HKEY_CURRENT_USERSoftwarePerformerSoft.
Key PC Performer at HKEY_LOCAL_MACHINESOFTWAREPerformerSoft.
Key PCPerformer_is1 at HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionUninstall.

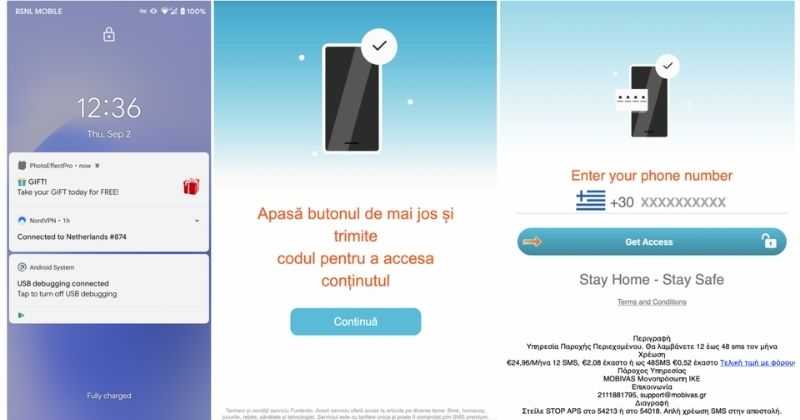 According to Zimperium zLabs, this malware that was recently detected has been doing its scams and attacks even in November of 2020 and has thus far accumulated hundreds of thousands of dollars in its scam.
On the surface it looks very harmless, asking for typical permissions like internet access, calls, and other related needed functions, and then it waits. After few months the real attack happens when users get charged with premium service they never subscribed to in the first place.
According to Zimperium zLabs, this malware that was recently detected has been doing its scams and attacks even in November of 2020 and has thus far accumulated hundreds of thousands of dollars in its scam.
On the surface it looks very harmless, asking for typical permissions like internet access, calls, and other related needed functions, and then it waits. After few months the real attack happens when users get charged with premium service they never subscribed to in the first place.

