Nectar Toolbar is a Browser addon for Internet Explorer developed by AIMIA Coalition Loyalty. This addon changed your default search provider to Yahoo UK. While installed, you might see additional unwanted ads and sponsored links injected in the search results.
From the Author: We all search the web every day for information from handy how-to’s, must know news about shopping. So wouldn’t it be great if you could collect extra Nectar points just for doing something you do already? Like to shop online? Nectar Search will also tell you when you’re on a shopping website (like Argos, Debenhams, Next, Play.com, and Apple) where you can collect points too.
Several anti-virus scanners have marked this addon as a Browser Hijacker and are therefore not recommended to keep on your computer.
About Browser Hijackers
Browser hijacking means a malicious program code has power over and modified the settings of your browser, without your permission. Browser hijackers could do more than just changing home pages. In general, hijackers are developed for the benefit of online hackers often through income generation that comes from forced ad mouse clicks and website visits. Nonetheless, it isn’t that harmless. Your web safety is compromised and it is also really annoying. In a much worst case, your browser could be hijacked to download malicious software that will do a great deal of damage to your computer.
Key symptoms that your browser has been hijacked
When your browser is hi-jacked, the following can happen: you notice unauthorized changes to your internet browser’s homepage; you observe new unwanted favorites or bookmarks added, usually directed to advertisement-filled or porn websites; the default browser configurations have been changed and/or your default web engine is altered; unwanted new toolbars are added to your internet browser; you might notice numerous pop-up adverts on your computer screen; your browser has instability issues or exhibits frequent errors; You can’t access particular websites, especially anti-malware websites.
Exactly how they invade computers
A browser hijacker can be installed on your computer or laptop when you go to an infected site, click on an e-mail attachment, or download something from a file-sharing site. Many internet browser hijackings originate from add-on programs, i.e., browser helper objects (BHO), toolbars, or plug-ins added to browsers to provide them additional features. Other times you might have accidentally accepted a browser hijacker as part of a software bundle (generally freeware or shareware). Popular examples of browser hijackers include CoolWebSearch, Conduit, OneWebSearch, Coupon Server, RocketTab, Delta Search, Searchult.com, and Snap.do.
Browser hijacking can bring about serious privacy problems and even identity theft, affect your web browsing experience by taking control over outgoing traffic, drastically slows down your computer or laptop by depleting lots of resources, and lead to system instability also.
Browser hijacker removal methods
Some browser hijacking can be easily stopped by identifying and eliminating the corresponding malware software from your control panel. However, most hijackers are quite tenacious and require specialized applications to get rid of them. Moreover, browser hijackers could modify the Windows registry so it can be extremely tough to fix manually, particularly when you are not a tech-savvy person.
Browser hijackers can be effectively removed by installing and running an anti-malware application on the affected computer. To get rid of any browser hijacker out of your computer, you could download this particular top-notch malware removal application – SafeBytes Anti-Malware. Together with anti-malware, a PC optimizer software, similar to Total System Care, could help you correct Windows registry errors, remove unwanted toolbars, secure your internet privacy, and stabilize programs installed on your computer.
Find Out How To Install Safebytes Anti-Malware On An Infected Computer system
All malware is bad and the consequences of the damage will vary based on the specific type of malicious software. Certain malware goes to great lengths to stop you from downloading or installing anything on your computer system, particularly anti-virus programs. If you are reading this, you probably have infected by a virus that stops you from installing a security program like Safebytes Anti-Malware. Follow the instructions below to remove malware through alternative methods.
Install in Safe Mode with Networking
Safe Mode is a unique, simplified version of Windows where just essential services are loaded to counteract malware and other problematic programs from loading. In case the malicious software is set to load immediately when the PC boots, switching to this mode could prevent it from doing so. To boot into Safe Mode, hit “F8” key on the keyboard right before Windows logo screen appears; Or right after normal Windows boot up, run MSCONFIG, look over Safe Boot under Boot tab, and then click Apply. Once you are in Safe Mode, you can try to install your anti-malware application without the hindrance of the malware. After installation, run the malware scanner to eliminate standard infections.
Download the anti-malware program in a different internet browser
Some malware only targets particular internet browsers. If this is your case, employ another browser as it might circumvent the computer virus. In case you suspect that your Internet Explorer happens to be hijacked by a computer virus or otherwise compromised by online hackers, the most effective course of action is to switch over to a different web browser such as Mozilla Firefox, Google Chrome, or Apple Safari to download your favorite security application – Safebytes Anti-Malware.
Make a bootable USB anti-virus drive
Another solution is to save and run an anti-malware software program entirely from a Thumb drive. To run antivirus from a thumb drive, follow these simple steps:
1) On a clean computer, install Safebytes Anti-Malware.
2) Plug the USB drive into the clean computer.
3) Double-click the Setup icon of the anti-malware software to run the Installation Wizard.
4) Select the drive letter of the pen drive as the location when the wizard asks you where you would like to install the anti-virus. Follow the onscreen instructions to finish the installation.
5) Now, insert the USB drive into the corrupted PC.
6) Run the Safebytes Anti-malware directly from the pen drive by double-clicking the icon.
7) Simply click “Scan Now” to run a complete scan on the affected computer for malware.
SafeBytes Anti-Malware Features
To protect your laptop or computer from various internet-based threats, it’s important to install anti-malware software on your personal computer. However, with countless numbers antimalware companies out there, these days it is hard to decide which one you should buy for your laptop. Some of them do a great job in eliminating malware threats while some will damage your PC by themselves. You must be careful not to pick the wrong product, especially if you buy a paid application. On the list of strongly recommended software by industry leaders is SafeBytes Anti-Malware, the most dependable program for Microsoft Windows.
SafeBytes anti-malware is a trustworthy tool that not only secures your PC permanently but is also quite user-friendly for people of all skill levels. Once you’ve got installed this application, SafeByte's sophisticated protection system will ensure that no viruses or malware can seep through your PC.
SafeBytes anti-malware provides an array of enhanced features that sets it aside from all others. Some of them are listed as below:
Real-Time Protection: SafeBytes gives you round-the-clock protection for your PC limiting malware intrusions in real-time. This utility will constantly monitor your computer for suspicious activity and updates itself continuously to keep abreast of the constantly changing threat landscape.
Most effective AntiMalware Protection: Built on a greatly acclaimed anti-virus engine, this malware removal application can find and get rid of numerous stubborn malware threats such as browser hijackers, potentially unwanted programs, and ransomware that other common anti-virus applications will miss.
Website Filtering: Safebytes allots all websites a unique safety score that helps you to have an idea of whether the webpage you’re just about to visit is safe to browse or known to be a phishing site.
Fast Multi-threaded Scanning: Safebytes Anti-Malware, with its advanced scanning engine, offers extremely fast scanning which can promptly target any active online threat.
Low CPU/Memory Usage: SafeBytes is well known for its low influence on processing power and great detection rate of various threats. It operates silently and efficiently in the background so you’re free to utilize your PC at full power all of the time.
24/7 Customer Service: For any technical concerns or product assistance, you could get 24/7 professional assistance through chat and email.
Put simply, SafeBytes has created a meaningful anti-malware solution that is aimed to protect you against all manner of malware. You now may understand that this particular software does more than just scan and eliminate threats from your PC. So if you’re searching for the absolute best malware removal application out there, and when you don’t mind shelling out a few bucks for it, opt for SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
To eliminate Nectar Toolbar manually, go to the Add or Remove programs list in the Windows Control Panel and choose the program you want to remove. For browser extensions, go to your web browser’s Addon/Extension manager and select the add-on you want to remove or disable. You’ll probably also want to reset your internet browser to its default settings.
Finally, check your hard disk for all of the following and clean your computer registry manually to get rid of leftover application entries after uninstallation. But bear in mind, this can be a tough task and only computer professionals can perform safely. In addition, certain malicious programs have the capability to defend against its removal. Completing this task in Safe Mode is suggested.
Files:
C:\Program Files (x86)\Nectar Toolbar
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\AimiaPoints.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\AimiaPointsAct.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\AimiaToolbar.css
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\ArrowDown.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\ArrowRight.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\ArrowUp.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\arrow_refresh.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\background.html
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\background.js
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\basis.xml
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\BrowserTweak.css
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\btn-background-grey.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\CanCollect.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\CanCollectAct.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\closeIcon.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\cog.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\Collecting.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\CollectingAct.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\computer_delete.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\eShopsMenu.html
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\eShopsMenu.js
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\help.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\HelpMenu.html
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\HelpMenu.js
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\icon-128.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\icon-16.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\icon-48.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\icons.bmp
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\icons.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\ie7vista.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\ie7xp.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\ie8bg.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\IE8GuardWorkaround.exe
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\info.txt
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\InstIcon.ico
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\jquery-1.7.2.min.js
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\jquery.placeholder.min.js
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\JSON.js
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\main.js
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\menu.js
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\nectar-icon-32×32.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\PIE.htc
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\PIE.js
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\SearchHist.html
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\SearchHist.js
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\search_glass.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\separator.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\separator_arrows.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\TbCommonUtils.dll
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\tbcore3.dll
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\TbHelper2.exe
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\tbhelperU.dll
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\uninstall.exe
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\UninstIcon.ico
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\update.exe
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\version.txt
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\Yahoo.ico
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\yahoo.png
C:\Program Files (x86)\Nectar Toolbar\tbunsg7A.tmp\your_logo.png
Registry:
HKEY_CURRENT_USER\Software376694984709702142491016734454
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run 13376694984709702142491016734454


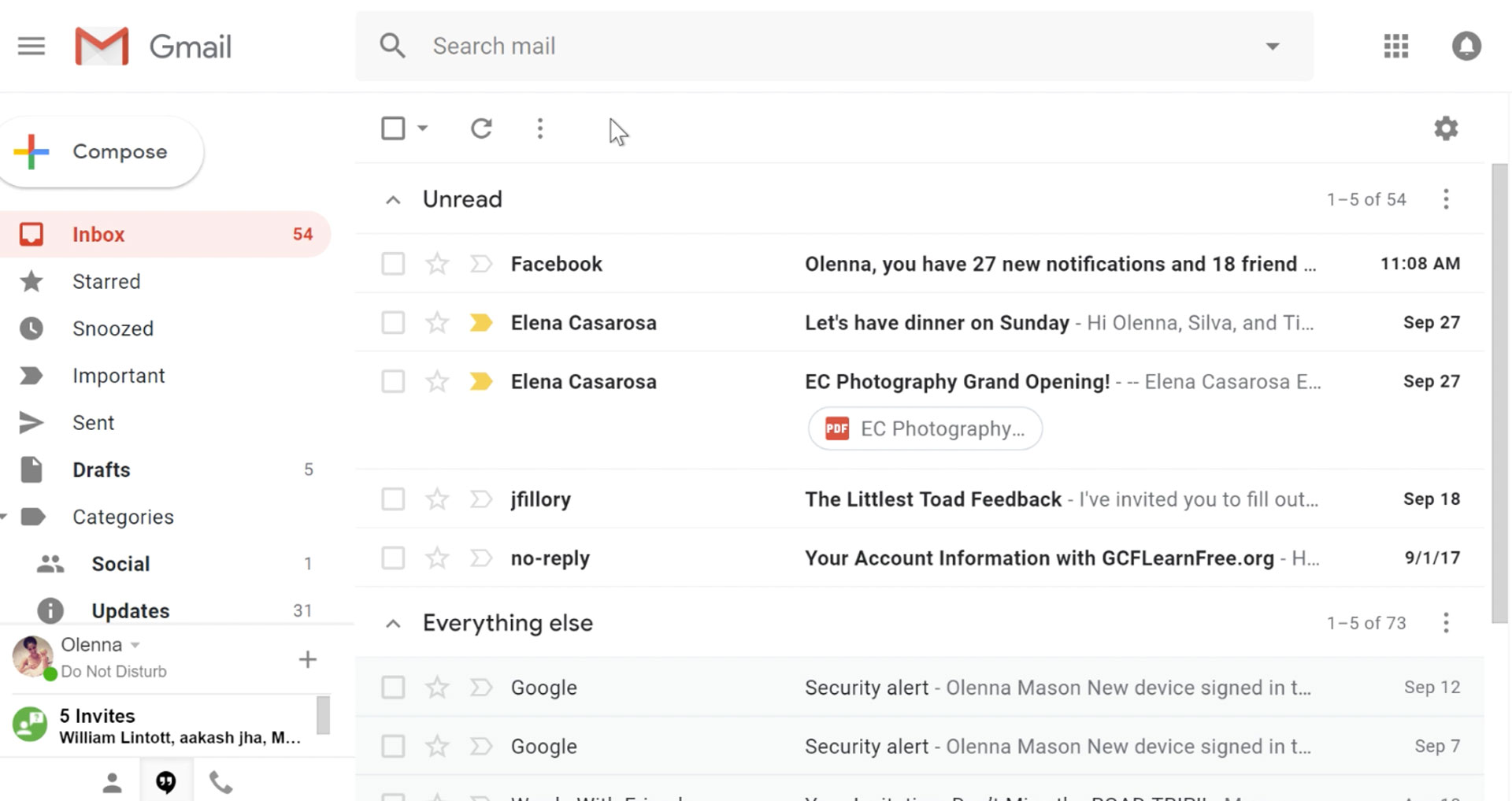 It would be very difficult to even start a free eMail list without mentioning Google's Gmail. Introduced all the way back in 2004 as an invite-only service it became over time the most popular email platform largely due to the fact Google is offering free eMail accounts.
There are a lot of good things to be said about Gmail itself, most of the area is clutter-free and the largest space is reserved for eMail itself letting users focus on what is important. WEB client itself means that you do not need to have any application installed on your device, altho via Google chrome, you can use Gmail offline offering you flexibility if needed.
The ability to connect and manage other accounts like Outlook, Yahoo, etc is just making Gmail even more attractive, and the snooze feature is a really neat little detail that will pause eMail notifications if you need to focus on other things.
Lack of organizing messages into folders is a little confusing since Gmail offers its own unique label system but sometimes I need to have old reliable save eMail to folder.
All in all, Gmail is a great service and it offers a great eMail on the go experience.
It would be very difficult to even start a free eMail list without mentioning Google's Gmail. Introduced all the way back in 2004 as an invite-only service it became over time the most popular email platform largely due to the fact Google is offering free eMail accounts.
There are a lot of good things to be said about Gmail itself, most of the area is clutter-free and the largest space is reserved for eMail itself letting users focus on what is important. WEB client itself means that you do not need to have any application installed on your device, altho via Google chrome, you can use Gmail offline offering you flexibility if needed.
The ability to connect and manage other accounts like Outlook, Yahoo, etc is just making Gmail even more attractive, and the snooze feature is a really neat little detail that will pause eMail notifications if you need to focus on other things.
Lack of organizing messages into folders is a little confusing since Gmail offers its own unique label system but sometimes I need to have old reliable save eMail to folder.
All in all, Gmail is a great service and it offers a great eMail on the go experience.
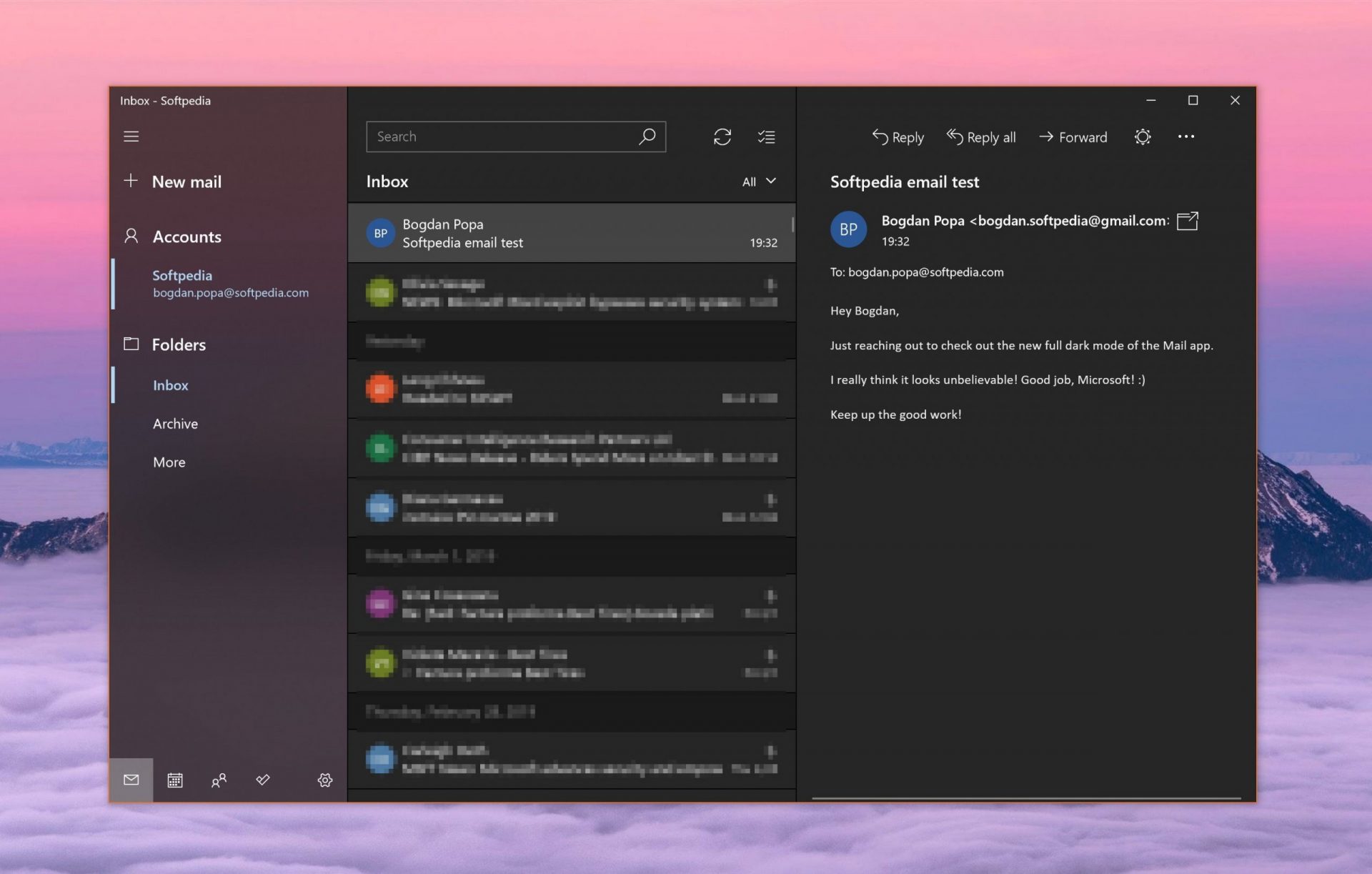 Free Windows eMail client simply called Mail is what was once outlook express. Mail itself has the ability to work with other popular accounts like Google Gmail account, Yahoo, iCloud etc. How it comes with Windows OS and it integrates very well with Microsoft Calendar, this eMail client is for many the first choice.
On the negative side, I might say this is a strip-down version of Outlook which is paid solution so some features are missing if we would compare the two.
Overall, a simple and nice eMail client worth your time, especially if you are on the Windows platform.
Free Windows eMail client simply called Mail is what was once outlook express. Mail itself has the ability to work with other popular accounts like Google Gmail account, Yahoo, iCloud etc. How it comes with Windows OS and it integrates very well with Microsoft Calendar, this eMail client is for many the first choice.
On the negative side, I might say this is a strip-down version of Outlook which is paid solution so some features are missing if we would compare the two.
Overall, a simple and nice eMail client worth your time, especially if you are on the Windows platform.
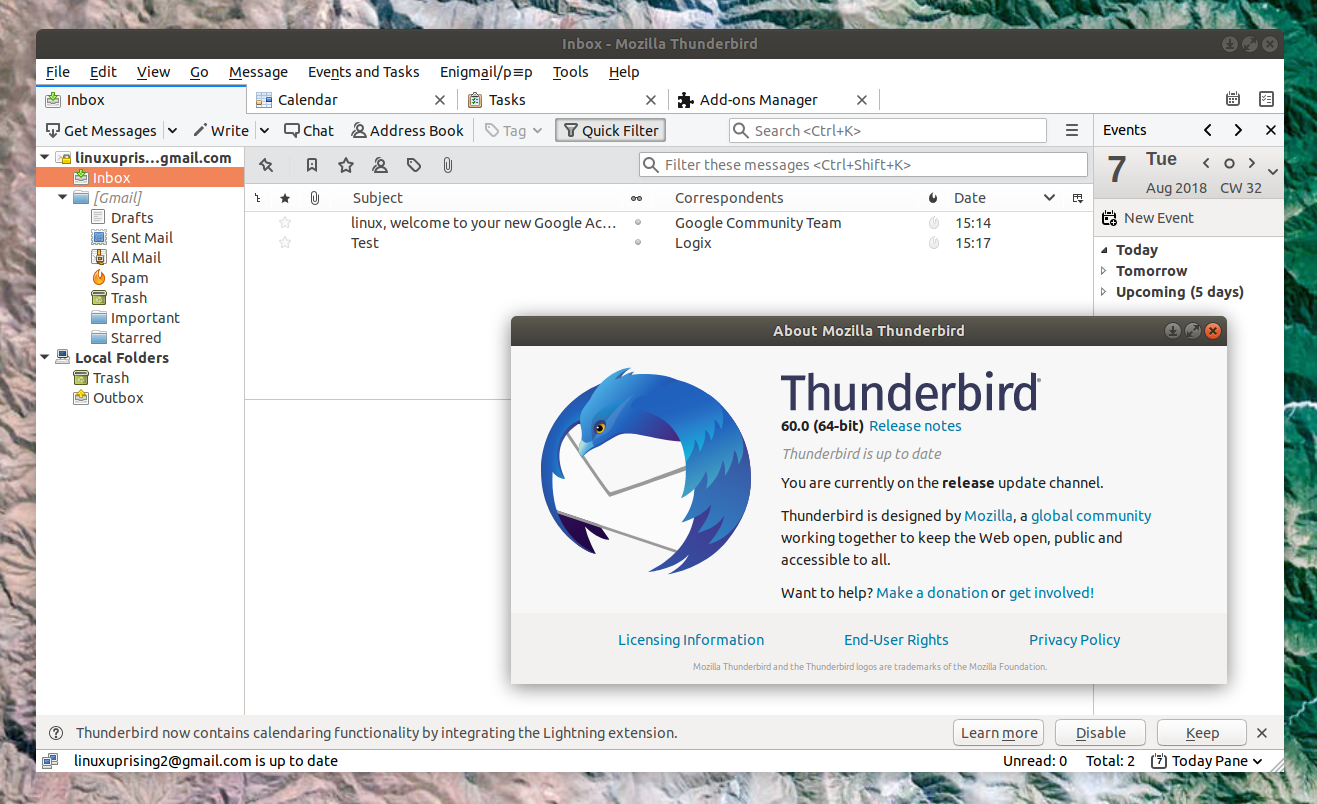 Great eMail client matching in functions against paid and premium solutions of big tech companies. Fueled with plenty of customization options and reskinning ones this eMail client offers a lot for its free price tag.
It is also fueled by Mozilla community focusing on privacy and security. It can work with any mail service and it is lightweight with a clean look, altho the look itself can be heavily customized.
The bad side is that client itself relies on email services to provide cloud-based emails, so if you are receiving your email via a service that does not have a cloud-based service in itself all of your received emails will be locked to the computer where you have received them. Also customizing it can be sometimes a little too technical for the average computer user.
All in all, Thunderbird is one great eMail client and it would be a shame not to use it because of its technical side, if you need a reliable and secure eMail client on a single machine, look no further than Thunderbird.
Great eMail client matching in functions against paid and premium solutions of big tech companies. Fueled with plenty of customization options and reskinning ones this eMail client offers a lot for its free price tag.
It is also fueled by Mozilla community focusing on privacy and security. It can work with any mail service and it is lightweight with a clean look, altho the look itself can be heavily customized.
The bad side is that client itself relies on email services to provide cloud-based emails, so if you are receiving your email via a service that does not have a cloud-based service in itself all of your received emails will be locked to the computer where you have received them. Also customizing it can be sometimes a little too technical for the average computer user.
All in all, Thunderbird is one great eMail client and it would be a shame not to use it because of its technical side, if you need a reliable and secure eMail client on a single machine, look no further than Thunderbird.
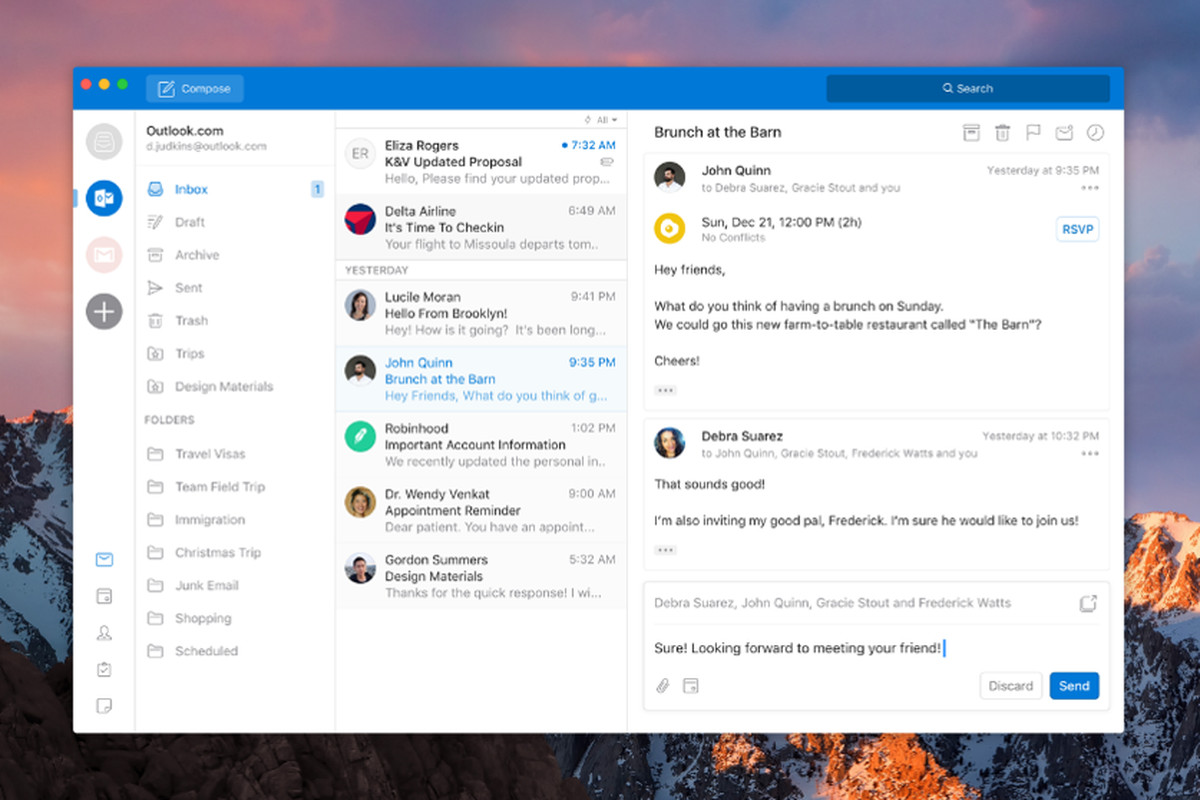 Outlook comes as a part of the Microsoft Office suite and as one of the oldest eMail clients, it is still widely popular and adopted through many users and businesses. It has tight integration with all Microsoft services and full integration with Calendar making it one of the if not the best eMail client out there.
Outlook also has a free online service completely free for personal use as well.
The downside is that you can not get it as a separate product if you want a business version other than as a part of the Office suite.
The final verdict would be that this is perhaps the best eMail client out but the big downside is that there is no desktop version outside the Office suite.
Outlook comes as a part of the Microsoft Office suite and as one of the oldest eMail clients, it is still widely popular and adopted through many users and businesses. It has tight integration with all Microsoft services and full integration with Calendar making it one of the if not the best eMail client out there.
Outlook also has a free online service completely free for personal use as well.
The downside is that you can not get it as a separate product if you want a business version other than as a part of the Office suite.
The final verdict would be that this is perhaps the best eMail client out but the big downside is that there is no desktop version outside the Office suite.
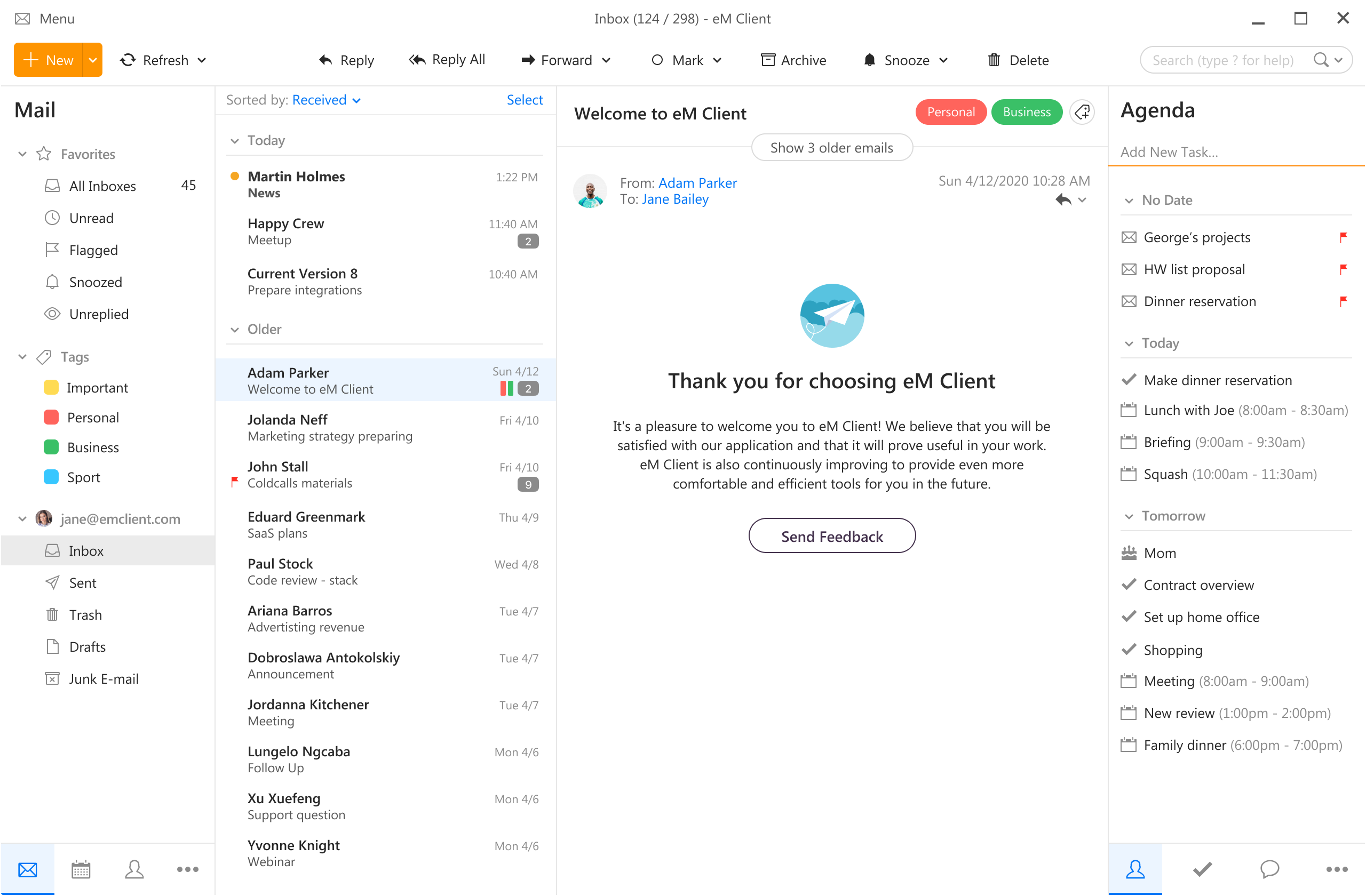 eM Client offers a wide array of features, including a calendar, contacts, and chat. Support is provided for all the major email services including Gmail, Yahoo, iCloud, and Outlook.com. The latest version also offers PGP encryption, live backup, basic image editing capabilities, and auto-replies for Gmail.
Its automatic system makes it very easy to get emails from other services since there is no manual setting, all that is needed is to type in your email and eM Client will do everything else automatically.
A one-time purchase is not pricy and it could offer some features that some free clients are missing. Go check it out with a free trial and see if it is for you.
eM Client offers a wide array of features, including a calendar, contacts, and chat. Support is provided for all the major email services including Gmail, Yahoo, iCloud, and Outlook.com. The latest version also offers PGP encryption, live backup, basic image editing capabilities, and auto-replies for Gmail.
Its automatic system makes it very easy to get emails from other services since there is no manual setting, all that is needed is to type in your email and eM Client will do everything else automatically.
A one-time purchase is not pricy and it could offer some features that some free clients are missing. Go check it out with a free trial and see if it is for you.
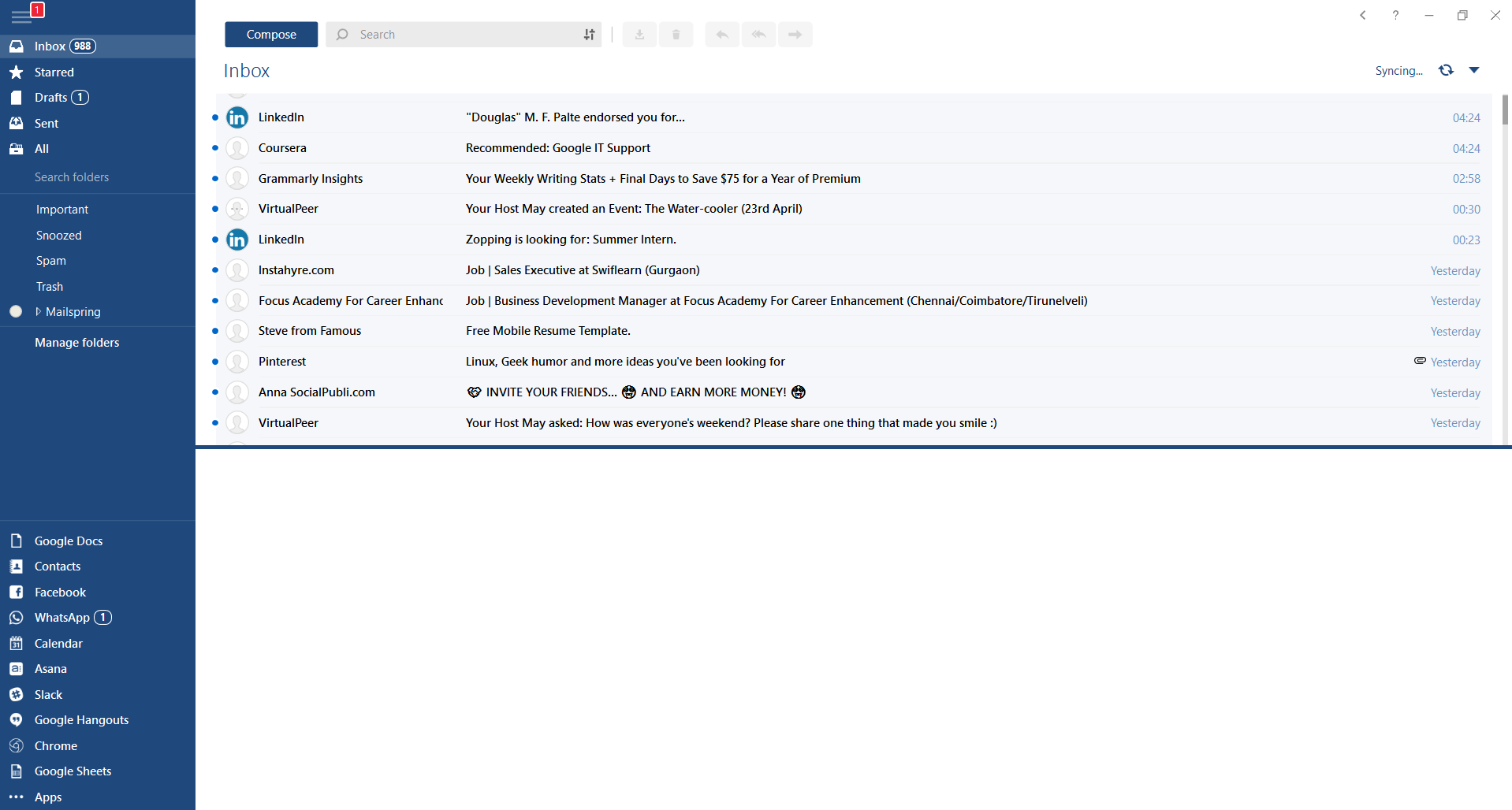 This eMail client's main focus is the simplicity of use with visual appeal while tackling multiple eMail accounts. It has many built-in apps along with a customizable interface. Unlike some more Microsoft-centric email clients, Mailbird Business supports a diverse range of integrated apps, including WhatsApp, Google Docs, Google Calendar, Facebook, Twitter, Dropbox, and Slack, all making for a better-streamlined workflow.
The downside of this client is the yearly subscription plan. I think people, in general, want to get away from software subscription plans so I will include this as a downside but bear in mind it is downside just in terms of a business plan not in the client itself.
This eMail client's main focus is the simplicity of use with visual appeal while tackling multiple eMail accounts. It has many built-in apps along with a customizable interface. Unlike some more Microsoft-centric email clients, Mailbird Business supports a diverse range of integrated apps, including WhatsApp, Google Docs, Google Calendar, Facebook, Twitter, Dropbox, and Slack, all making for a better-streamlined workflow.
The downside of this client is the yearly subscription plan. I think people, in general, want to get away from software subscription plans so I will include this as a downside but bear in mind it is downside just in terms of a business plan not in the client itself.
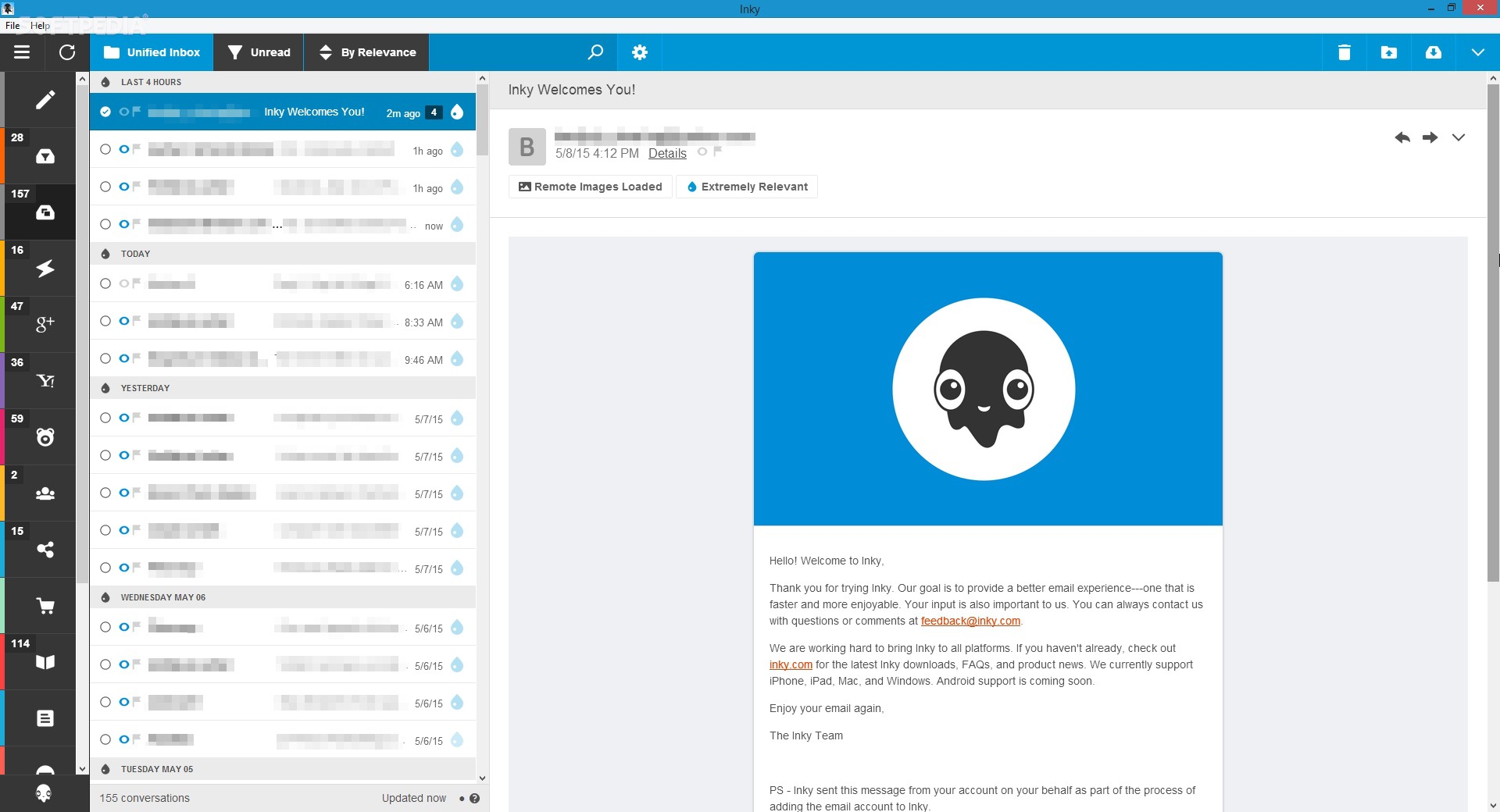 Inky is eMail client if you are looking for security. It uses AI along with machine learning in order to block all types of phishing attacks that can get through to other clients. The proprietary machine learning technology can literally read an email to determine if it has phishing content, and then is able to quarantine the email or deliver it with the malicious links disabled. It also takes things a step further and offers an analytics dashboard, which allows an administrator to see patterns of attacks based on dates, or targeted users.
The downside is that client itself is so much focused on security that sometimes some nonsecurity features get overlooked and provide a poor experience but if you need a good and greatly secured eMail client Inky is one to check out.
Inky is eMail client if you are looking for security. It uses AI along with machine learning in order to block all types of phishing attacks that can get through to other clients. The proprietary machine learning technology can literally read an email to determine if it has phishing content, and then is able to quarantine the email or deliver it with the malicious links disabled. It also takes things a step further and offers an analytics dashboard, which allows an administrator to see patterns of attacks based on dates, or targeted users.
The downside is that client itself is so much focused on security that sometimes some nonsecurity features get overlooked and provide a poor experience but if you need a good and greatly secured eMail client Inky is one to check out. 
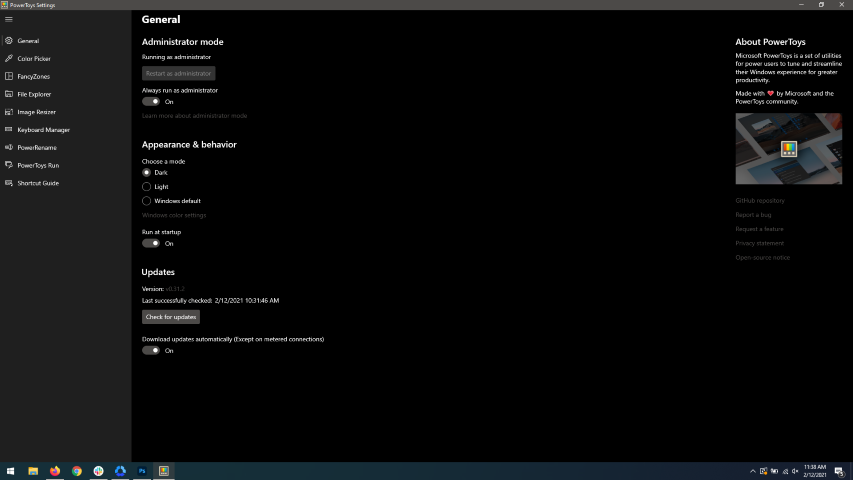 When opened you will be greeted with general settings window. These are settings for power toys themselves, Here you can check for updates, change the looks of power toys, run it on system startup and run them as administrator. Set them up so they best suit your needs.
When opened you will be greeted with general settings window. These are settings for power toys themselves, Here you can check for updates, change the looks of power toys, run it on system startup and run them as administrator. Set them up so they best suit your needs.
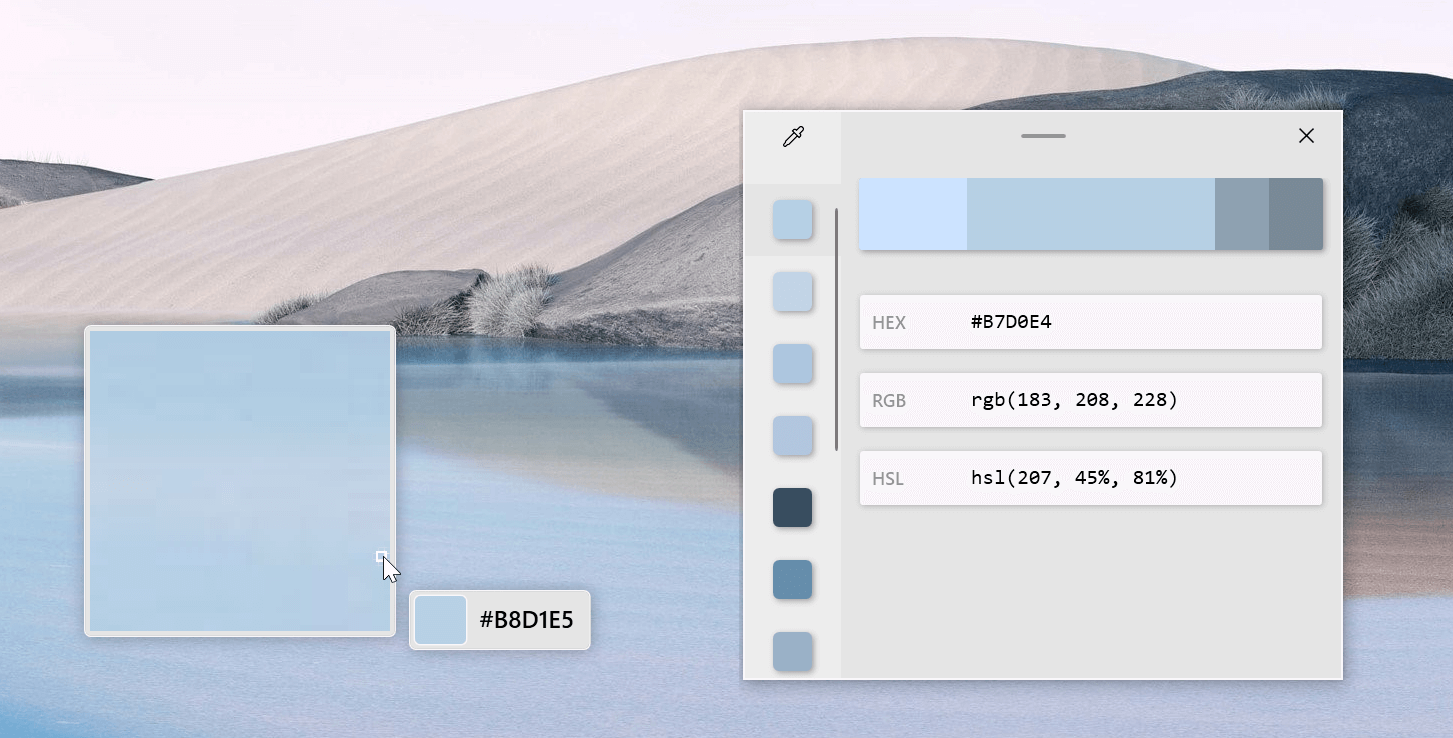 The color picker will let you as the name suggests pick colors, it will sample colors from running applications and windows, snap their values, and place them in the clipboard. A useful application if you are working as a graphic designer, want to create some cool word document, or just want to compare the difference between colors.
After the Color Picker is activated, hover your mouse cursor over the color you would like to copy and left-click the mouse button to select a color. If you want to see the area around your cursor in more detail, scroll up to zoom in. The copied color will be stored in your clipboard in the format that is configured in the settings (HEX by default). The editor lets you see the history of picked colors (up to 20) and copy their representation in any predefined string format. You can configure what color formats are visible in the editor, along with the order that they appear. This configuration can be found in PowerToys settings. The editor also allows you to fine-tune any picked color or get a new similar color. Editor previews different shades of currently selected color - 2 lighter and 2 darker ones. Clicking on any of those alternative color shades will add the selection to the history of picked colors (appears on the top of the colors history list). Color in the middle represents your currently selected color from the history of the colors. By clicking on it, the fine-tuning configuration control will appear, which will let you change the HUE or RGB values of the current color. Pressing OK will add newly configured color into the history of the colors.
The color picker will let you as the name suggests pick colors, it will sample colors from running applications and windows, snap their values, and place them in the clipboard. A useful application if you are working as a graphic designer, want to create some cool word document, or just want to compare the difference between colors.
After the Color Picker is activated, hover your mouse cursor over the color you would like to copy and left-click the mouse button to select a color. If you want to see the area around your cursor in more detail, scroll up to zoom in. The copied color will be stored in your clipboard in the format that is configured in the settings (HEX by default). The editor lets you see the history of picked colors (up to 20) and copy their representation in any predefined string format. You can configure what color formats are visible in the editor, along with the order that they appear. This configuration can be found in PowerToys settings. The editor also allows you to fine-tune any picked color or get a new similar color. Editor previews different shades of currently selected color - 2 lighter and 2 darker ones. Clicking on any of those alternative color shades will add the selection to the history of picked colors (appears on the top of the colors history list). Color in the middle represents your currently selected color from the history of the colors. By clicking on it, the fine-tuning configuration control will appear, which will let you change the HUE or RGB values of the current color. Pressing OK will add newly configured color into the history of the colors.
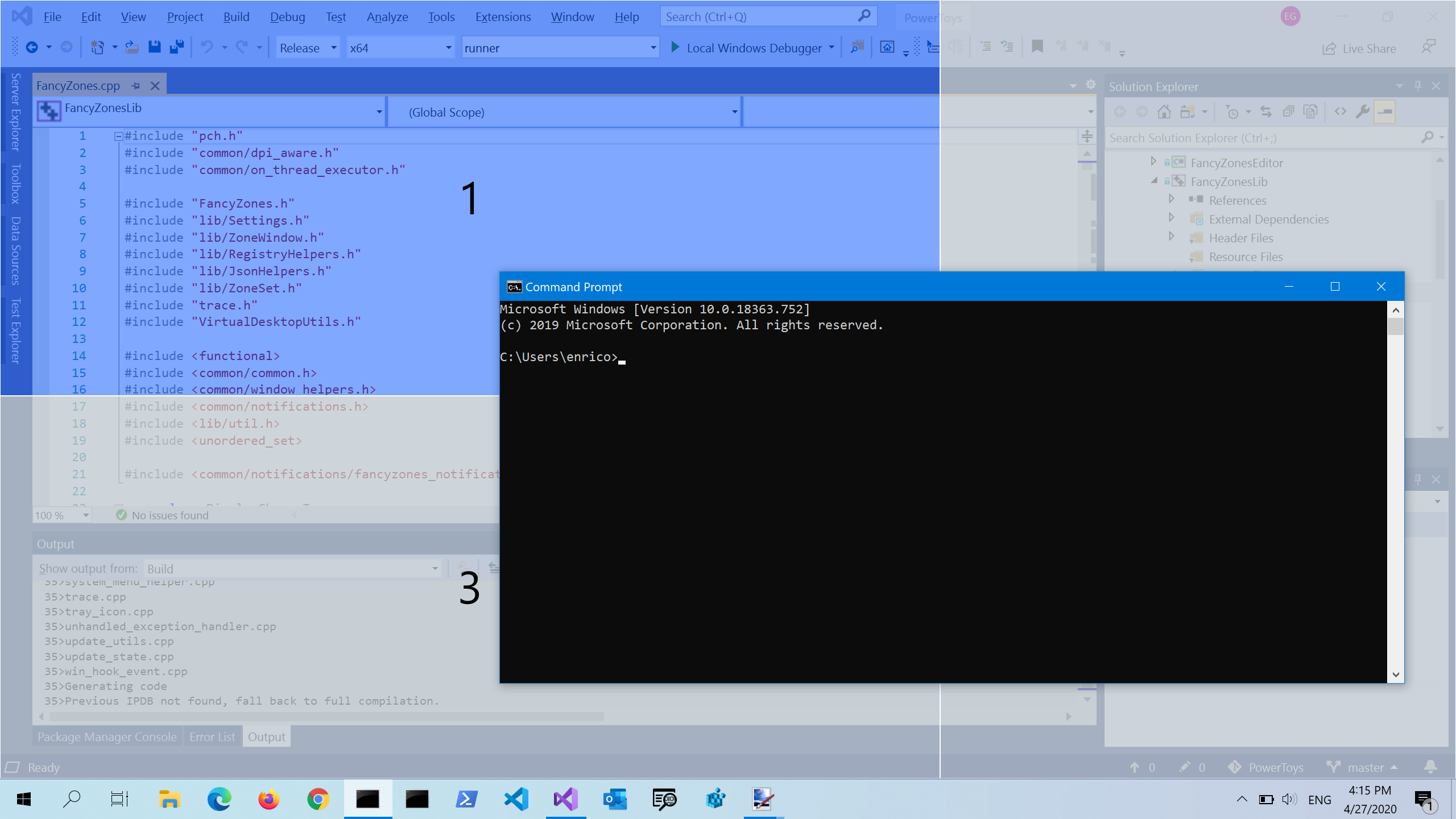 FancyZones is a window manager utility for arranging and snapping windows into efficient layouts to improve the speed of your workflow and restore layouts quickly. FancyZones allows the user to define a set of window locations for a desktop that are drag targets for windows. When the user drags a window into a zone, the window is resized and repositioned to fill that zone. When first launched, the zones editor presents a list of layouts that can be adjusted by how many windows are on the monitor. Choosing a layout shows a preview of that layout on the monitor. The selected layout is applied automatically.
FancyZones is a window manager utility for arranging and snapping windows into efficient layouts to improve the speed of your workflow and restore layouts quickly. FancyZones allows the user to define a set of window locations for a desktop that are drag targets for windows. When the user drags a window into a zone, the window is resized and repositioned to fill that zone. When first launched, the zones editor presents a list of layouts that can be adjusted by how many windows are on the monitor. Choosing a layout shows a preview of that layout on the monitor. The selected layout is applied automatically.
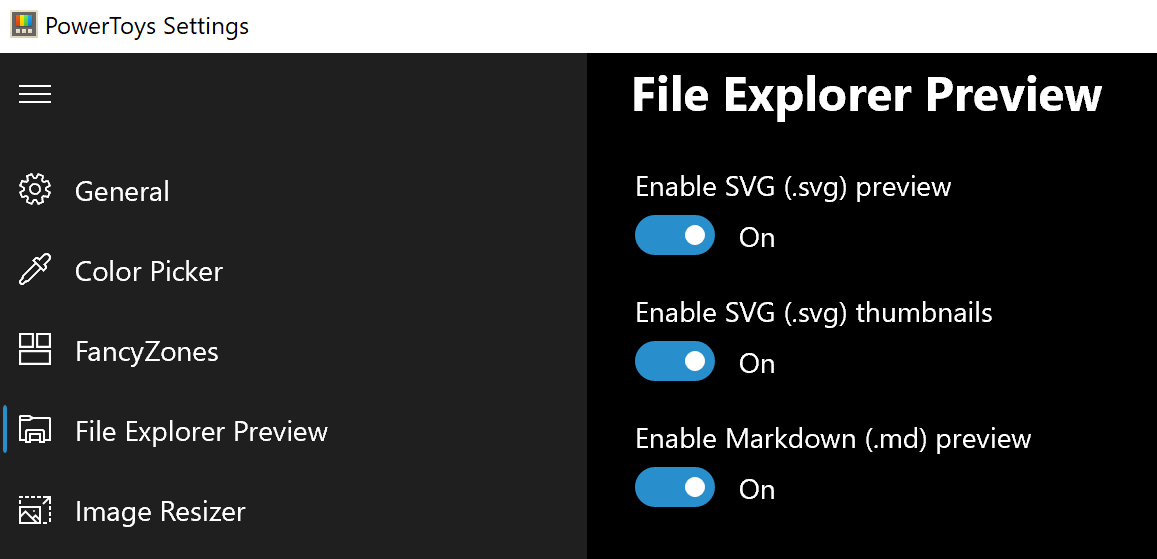 Only 3 options here but maybe some are important to you. This extension lets you enable SVG file preview in File Explorer, enable Markdown preview, and enable SVG thumbnails. Turn on each one you might need.
Only 3 options here but maybe some are important to you. This extension lets you enable SVG file preview in File Explorer, enable Markdown preview, and enable SVG thumbnails. Turn on each one you might need.
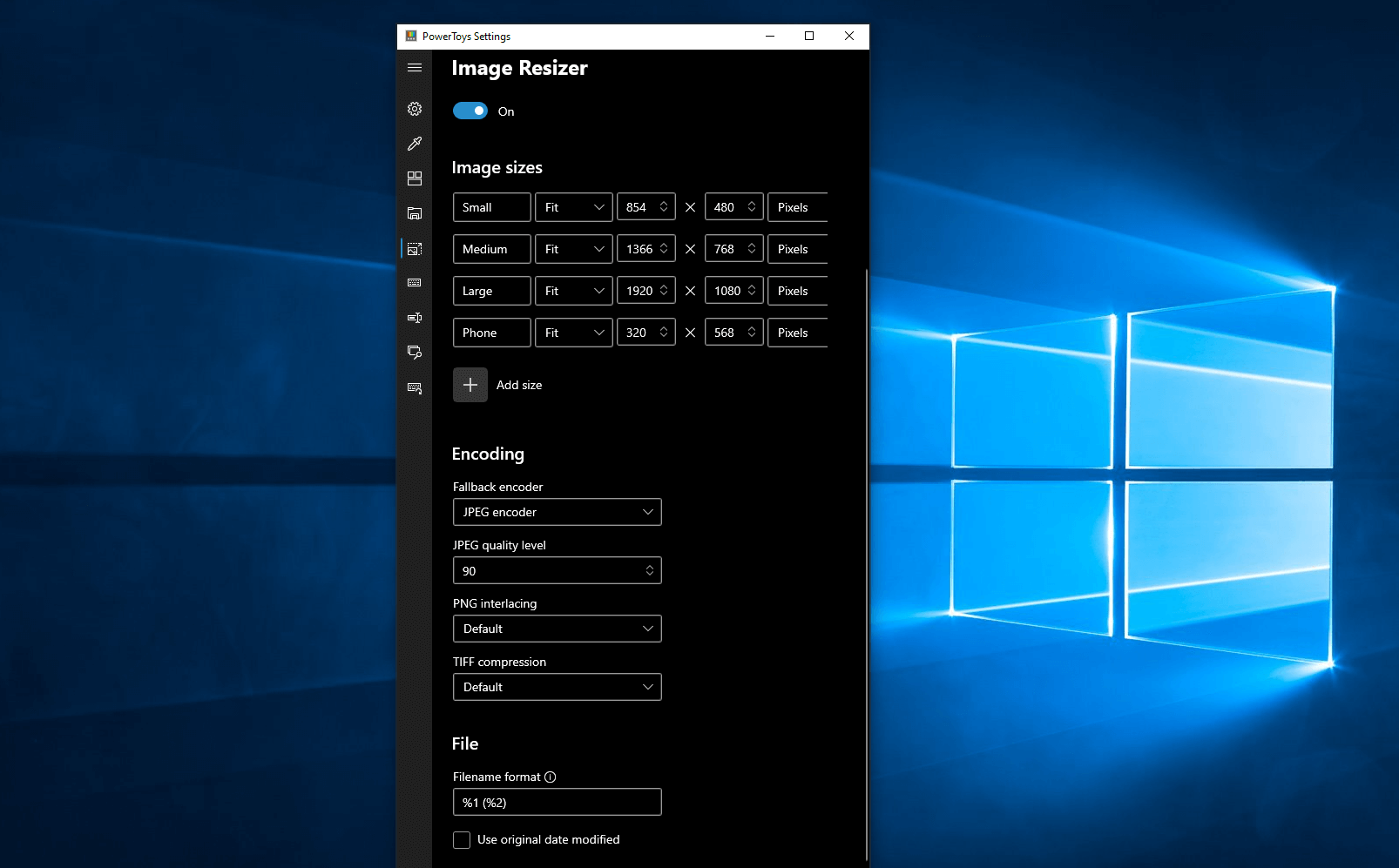 Image Resizer is a Windows shell extension for bulk image-resizing. After installing PowerToys, right-click on one or more selected image files in File Explorer, and then select Resize pictures from the menu. You can specify your own sizes if you want, you can resize when dragging files, you can overwrite files or make new copies of new sizes, and many more options. A very useful tool I am sure plenty of users can use since this eliminates the need for pictures or any other image application for common resizing tasks.
Image Resizer is a Windows shell extension for bulk image-resizing. After installing PowerToys, right-click on one or more selected image files in File Explorer, and then select Resize pictures from the menu. You can specify your own sizes if you want, you can resize when dragging files, you can overwrite files or make new copies of new sizes, and many more options. A very useful tool I am sure plenty of users can use since this eliminates the need for pictures or any other image application for common resizing tasks.
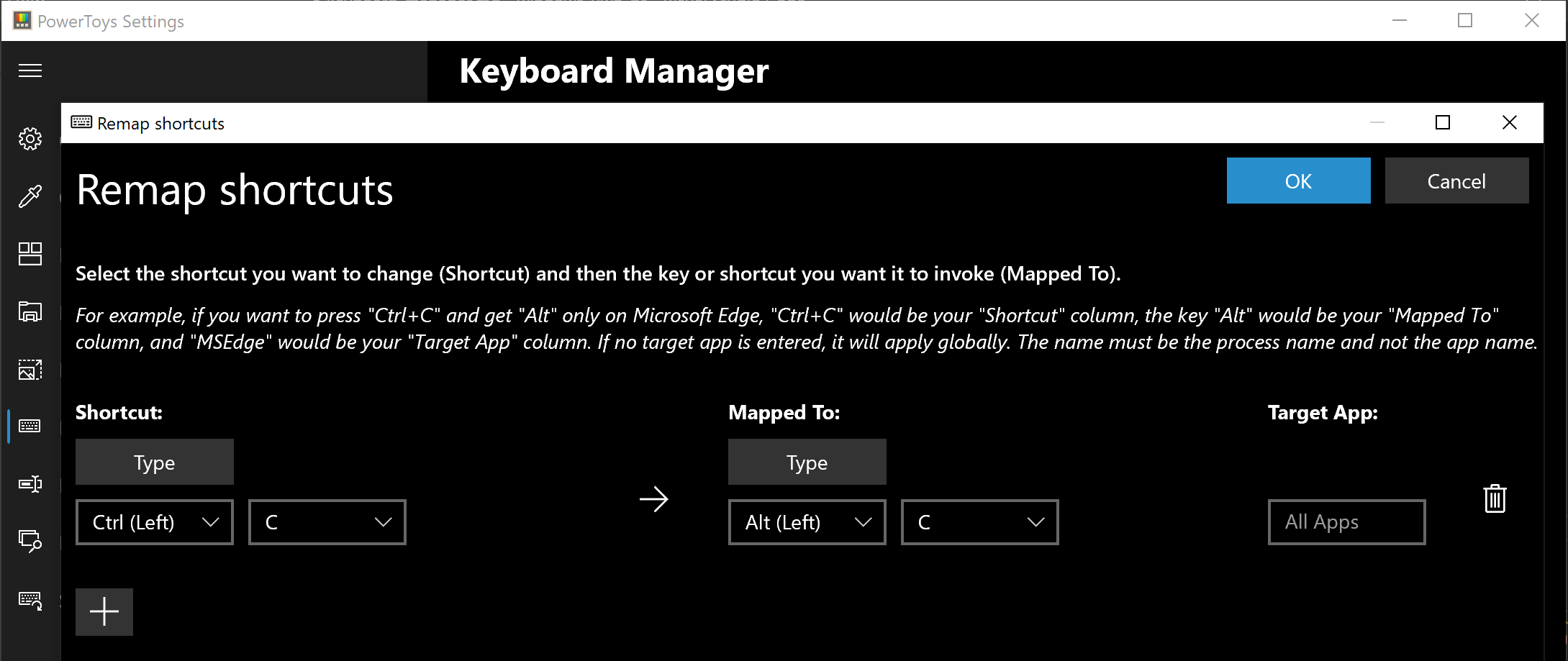 The PowerToys Keyboard Manager enables you to redefine keys on your keyboard. For example, you can exchange the letter A for the letter D on your keyboard. When you select the A key, a D will display. You can also exchange shortcut key combinations. For example, the shortcut key, Ctrl+C, will copy the text in Microsoft Word. With the PowerToys Keyboard Manager utility, you can exchange that shortcut for ⊞ Win+C). Now, ⊞ Win+C) will copy text. If you do not specify a targeted application in PowerToys Keyboard Manager, the shortcut exchange will be applied globally across Windows. PowerToys Keyboard Manager must be enabled (with PowerToys running in the background) for remapped keys and shortcuts to be applied. If PowerToys is not running, key remapping will no longer be applied.
The PowerToys Keyboard Manager enables you to redefine keys on your keyboard. For example, you can exchange the letter A for the letter D on your keyboard. When you select the A key, a D will display. You can also exchange shortcut key combinations. For example, the shortcut key, Ctrl+C, will copy the text in Microsoft Word. With the PowerToys Keyboard Manager utility, you can exchange that shortcut for ⊞ Win+C). Now, ⊞ Win+C) will copy text. If you do not specify a targeted application in PowerToys Keyboard Manager, the shortcut exchange will be applied globally across Windows. PowerToys Keyboard Manager must be enabled (with PowerToys running in the background) for remapped keys and shortcuts to be applied. If PowerToys is not running, key remapping will no longer be applied.
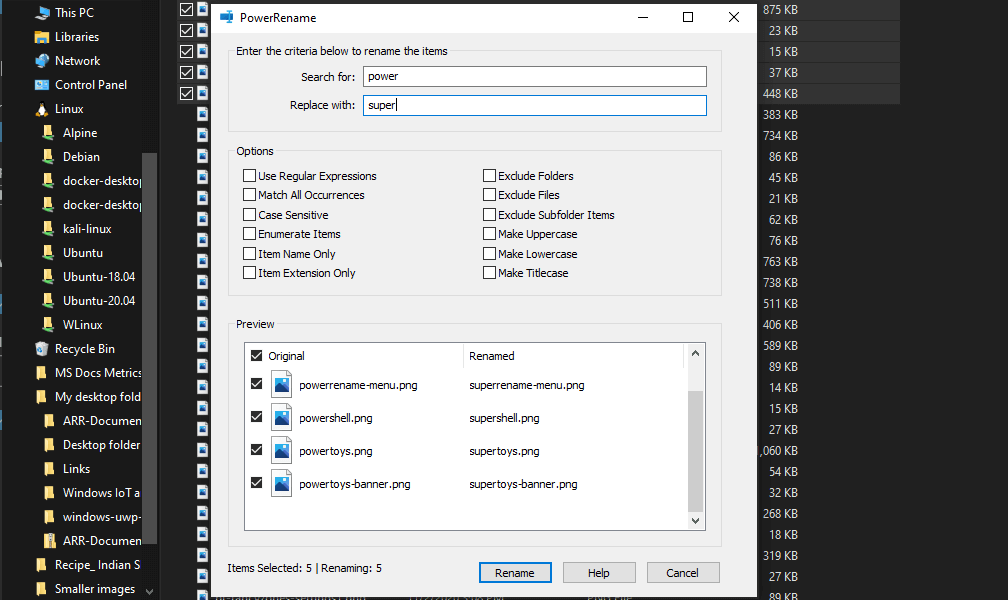 PowerRename is a bulk renaming tool that enables you to:
PowerRename is a bulk renaming tool that enables you to:
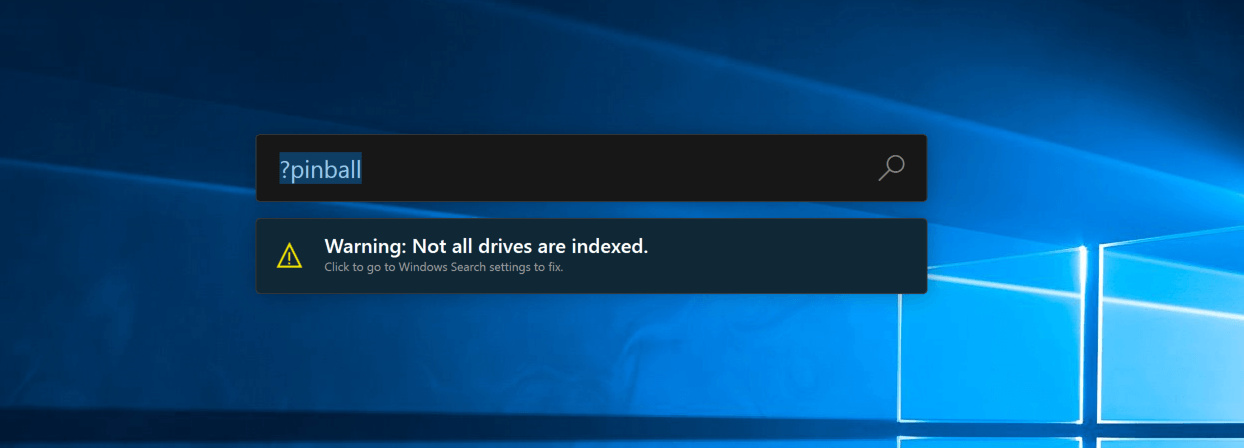 PowerToys Run is a quick launcher for power users that contains some additional features without sacrificing performance.
PowerToys Run features include:
PowerToys Run is a quick launcher for power users that contains some additional features without sacrificing performance.
PowerToys Run features include:
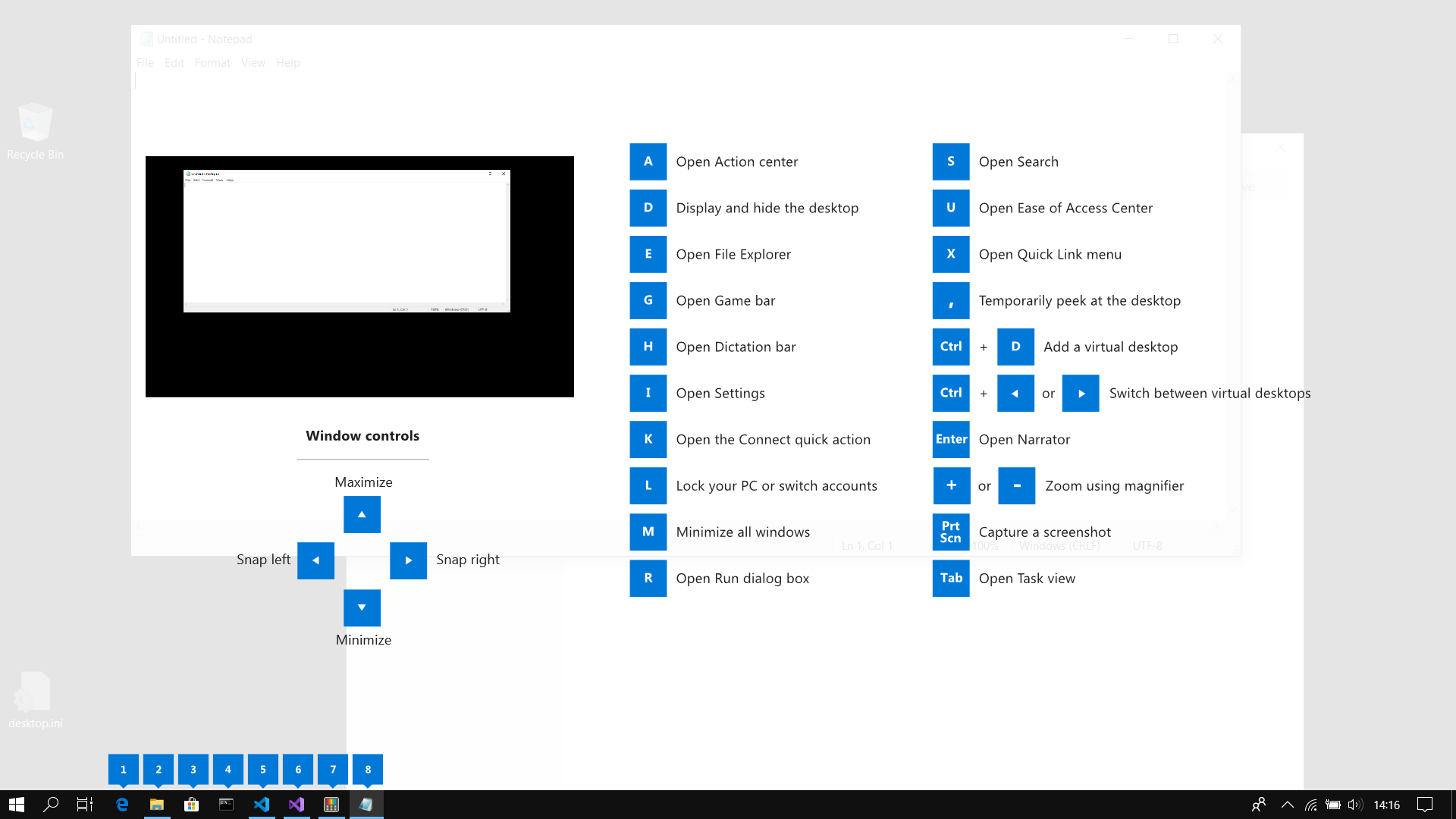 This guide uses PowerToys to display common keyboard shortcuts that use the Windows ⊞ key. Windows key keyboard shortcuts can be used while the guide is being shown and the result of those shortcuts (active window moved, arrow shortcut behavior changes, etc) will be displayed in the guide. Releasing the Windows ⊞ key will make the overlay disappear. Tapping the Windows ⊞ key will display the Windows Start menu.
Hey, you made it till the end, thank you for reading and I hope to see you soon.
This guide uses PowerToys to display common keyboard shortcuts that use the Windows ⊞ key. Windows key keyboard shortcuts can be used while the guide is being shown and the result of those shortcuts (active window moved, arrow shortcut behavior changes, etc) will be displayed in the guide. Releasing the Windows ⊞ key will make the overlay disappear. Tapping the Windows ⊞ key will display the Windows Start menu.
Hey, you made it till the end, thank you for reading and I hope to see you soon. 