Some Windows 7 or Windows 8/8.1 users are having a hard time upgrading to Windows 10 as they are being prompted for a product key. By default, the Windows 10 operating system does not require a product key and users should not be prompted for one, given you upgraded your computer from an activated Windows 7 or Windows 8/8.1 license or from the Windows 10 Preview build. However, there are some users encountering this problem and there are several reasons for this.
 Error Causes
Error CausesThere are a few reasons why some users are being prompted for a product key when upgrading to Windows 10:
Before you can fix this problem, you need to know why you’re being prompted for a product key. Some things you should know about Windows 10 product key activation are the following:
Now, if ever you’re prompted for a product key when you’re upgrading to Windows 10, you can apply the following methods:
If you’ve been prompted for a product key upon upgrading to Windows 10, you should click on the “Do this later” option. Wait for a few days then Windows 10 will get activated automatically.
One of the reasons Windows users are being prompted for a product key when upgrading to Windows 10 is that they have downloaded a wrong edition of Windows 10 and do not correspond with your current system.
NOTE: Users of Windows 7 Enterprise, Windows 8.0 Enterprise, and Windows 8.1 Enterprise are not eligible for the free upgrade offer.
If your Windows 7 or Windows 8/8.1 is not genuine or activated, you will get prompted for a product key. You need to make sure first your current system is activated.
Another thing you can try doing is to run the system file checker utility to scan if there are any broken operating system files. In doing so, you’ll be able to detect problems that might be preventing the product activation of your Windows 10 upgrade.
If in case you’ve exhausted all your resources and you are still being prompted for a product key when upgrading to Windows 10, you can try contacting the Microsoft Activation Center for further details. Check here for the appropriate telephone numbers to contact.
If you still experience the error after doing the methods above, you might want to try a powerful and trusted automated tool to fix the job.

Administrators can download updates from the Microsoft Download Center or the Windows Update Catalog to deploy to multiple computers If you are running Windows Server Update Services (WSUS) 3.0, System Center Essentials (SCE), or System Center Configuration Manager (SCCM) you can import updates directly into these applications. Security updates, critical updates, service packs, update rollups, definition updates, and critical drivers can be configured to synchronize with your server automatically. You can still import these updates into your application by using Microsoft Update Catalog; however, depending on how you configure WSUS, SCE, and SCCM, you may not need to import the updates.
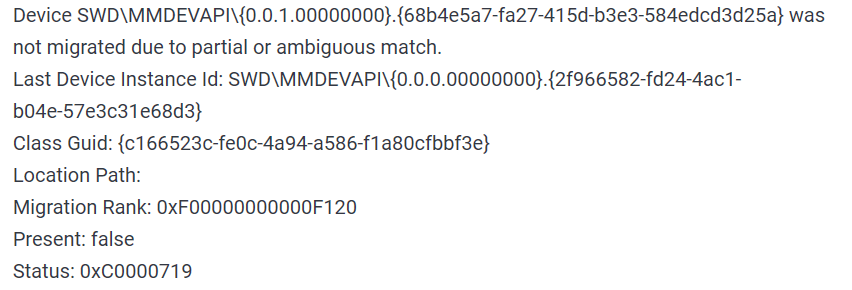 The first thing that would pop into my mind is that I have lost tons of work and that something in my hardware has gone very wrong and it is dead. Luckily that is not the case and this error means that due to Windows update drivers were not properly transferred due to some compatibility issues, maybe it was a corrupt update file, etc. Of course, the reason could be hardware malfunction as well, but if everything was working fine before the update, it is a software issue, and I must say it is a common one and fixable. Please keep reading this guide in order to fix the Device not migrated error.
The first thing that would pop into my mind is that I have lost tons of work and that something in my hardware has gone very wrong and it is dead. Luckily that is not the case and this error means that due to Windows update drivers were not properly transferred due to some compatibility issues, maybe it was a corrupt update file, etc. Of course, the reason could be hardware malfunction as well, but if everything was working fine before the update, it is a software issue, and I must say it is a common one and fixable. Please keep reading this guide in order to fix the Device not migrated error.
 Find device inside device manager, right-click on it, and choose properties. Go to the events tab and make sure that the device has migration issues.
Find device inside device manager, right-click on it, and choose properties. Go to the events tab and make sure that the device has migration issues.
 You have now 3 options for updating the driver, you can do it manually, automatically, or with the driver installer. We will cover all 3 options so you choose which one best suits you.
OPTION 1: Manually.
Close the Properties tab, go to the device manufacturer website and download the latest driver, if there are no drivers there, the only executable installer for the device skip this step and try the other 2. After you have downloaded the driver package from the website, right-click on the device and choose update driver.
You have now 3 options for updating the driver, you can do it manually, automatically, or with the driver installer. We will cover all 3 options so you choose which one best suits you.
OPTION 1: Manually.
Close the Properties tab, go to the device manufacturer website and download the latest driver, if there are no drivers there, the only executable installer for the device skip this step and try the other 2. After you have downloaded the driver package from the website, right-click on the device and choose update driver.
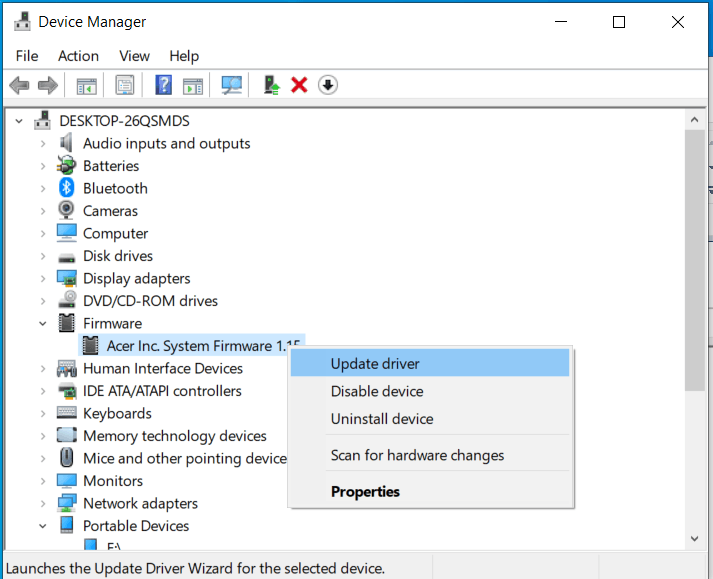 Now navigate to the folder where you have downloaded your driver package and update the driver. Reboot your system.
OPTION 2: Automatic update.
Close the Properties tab, right-click on the device and choose to uninstall.
Now navigate to the folder where you have downloaded your driver package and update the driver. Reboot your system.
OPTION 2: Automatic update.
Close the Properties tab, right-click on the device and choose to uninstall.
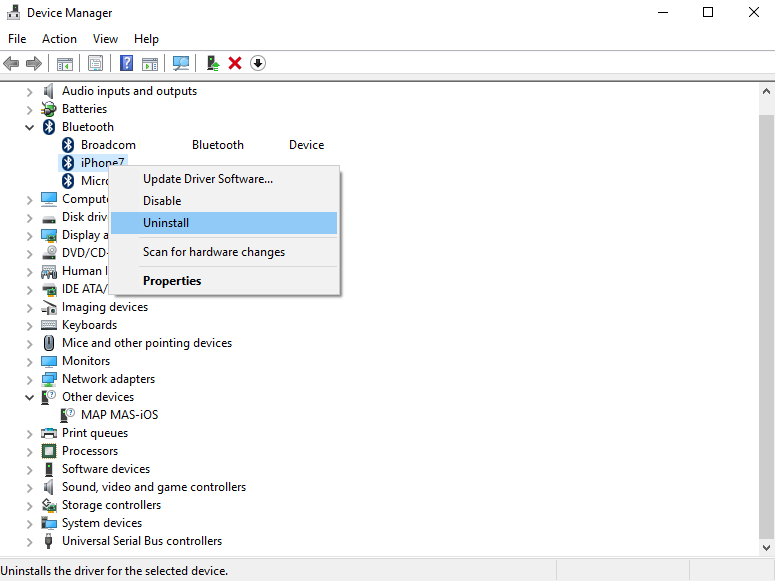 Once the device is uninstalled, restart your system, and Windows will automatically search and install the latest driver for the device.
OPTION 3: Via driver installer.
If you have downloaded .EXE or executable driver installer from device manufacturers web site try installing it, if the installation fails, try using compatibility mode for the installer. Navigate where the installer is located, right-click on it, and choose properties. Go to compatibility TAB and try installing it with administrator privileges in Windows 8 mode.
Once the device is uninstalled, restart your system, and Windows will automatically search and install the latest driver for the device.
OPTION 3: Via driver installer.
If you have downloaded .EXE or executable driver installer from device manufacturers web site try installing it, if the installation fails, try using compatibility mode for the installer. Navigate where the installer is located, right-click on it, and choose properties. Go to compatibility TAB and try installing it with administrator privileges in Windows 8 mode.
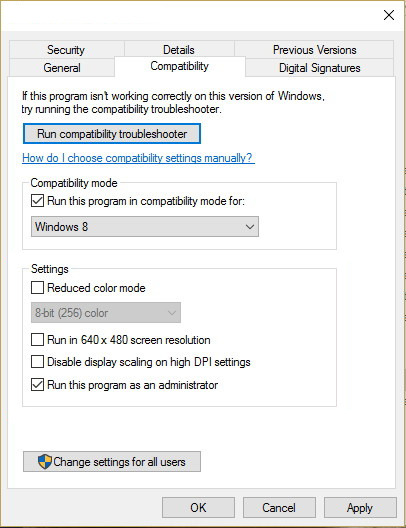 Reboot your system after this step.
This should solve the issues, however, if the issue still persists, follow the next steps.
Reboot your system after this step.
This should solve the issues, however, if the issue still persists, follow the next steps. In the command prompt type in: sfc /scannow and press ENTER.
In the command prompt type in: sfc /scannow and press ENTER.
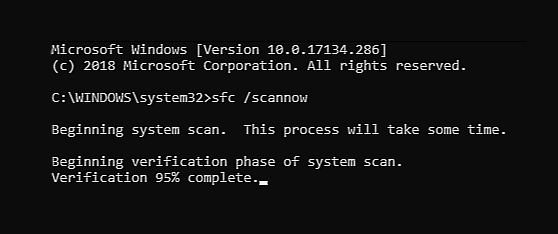 The scanning process and repair of files will take around 15 min. Leave it to finish completely, do not restart, work on the computer or shut it down while the process is active, and only after it is finished reboot your system.
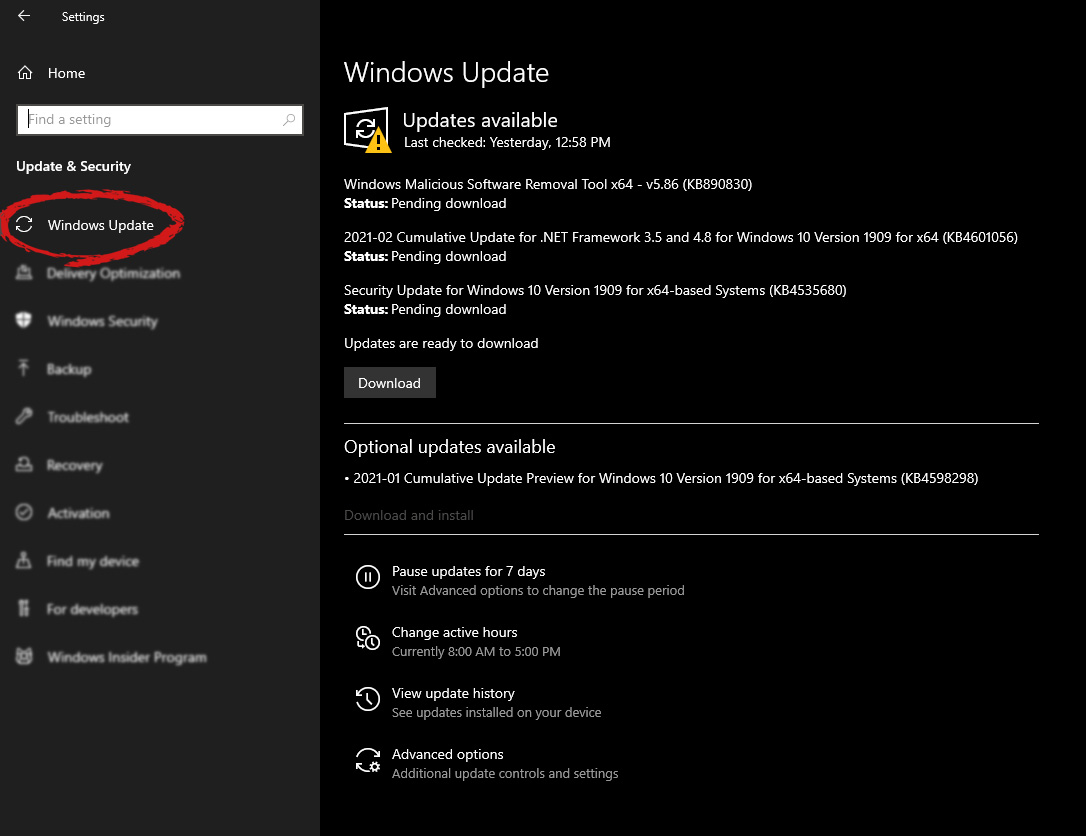
The scanning process and repair of files will take around 15 min. Leave it to finish completely, do not restart, work on the computer or shut it down while the process is active, and only after it is finished reboot your system.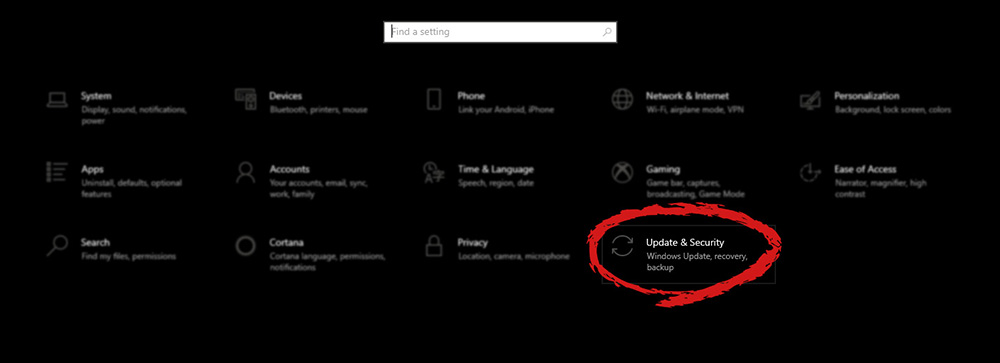 Go to the Windows update tab and click on DOWNLOAD or click on check for updates for the latest Windows fix.
Go to the Windows update tab and click on DOWNLOAD or click on check for updates for the latest Windows fix.
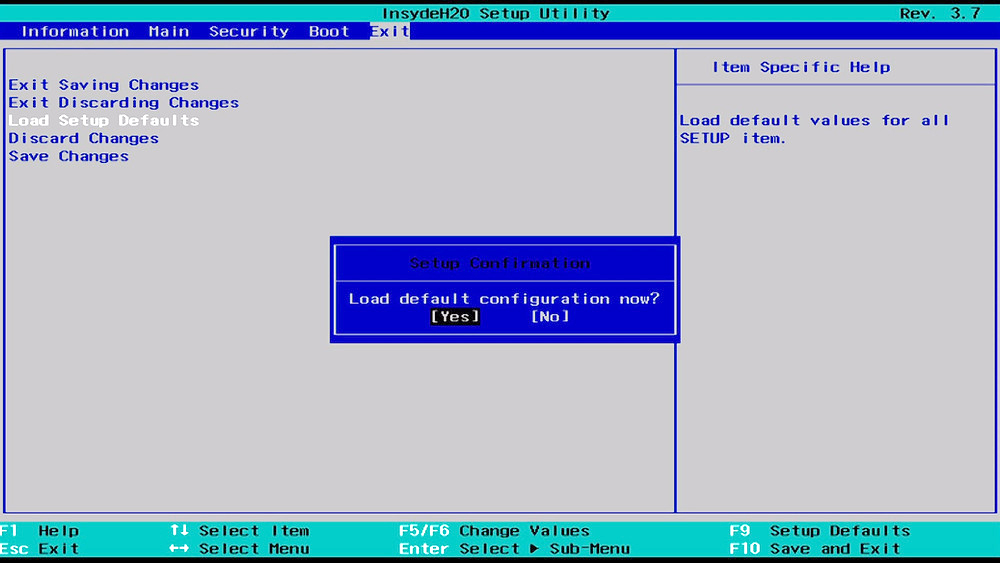
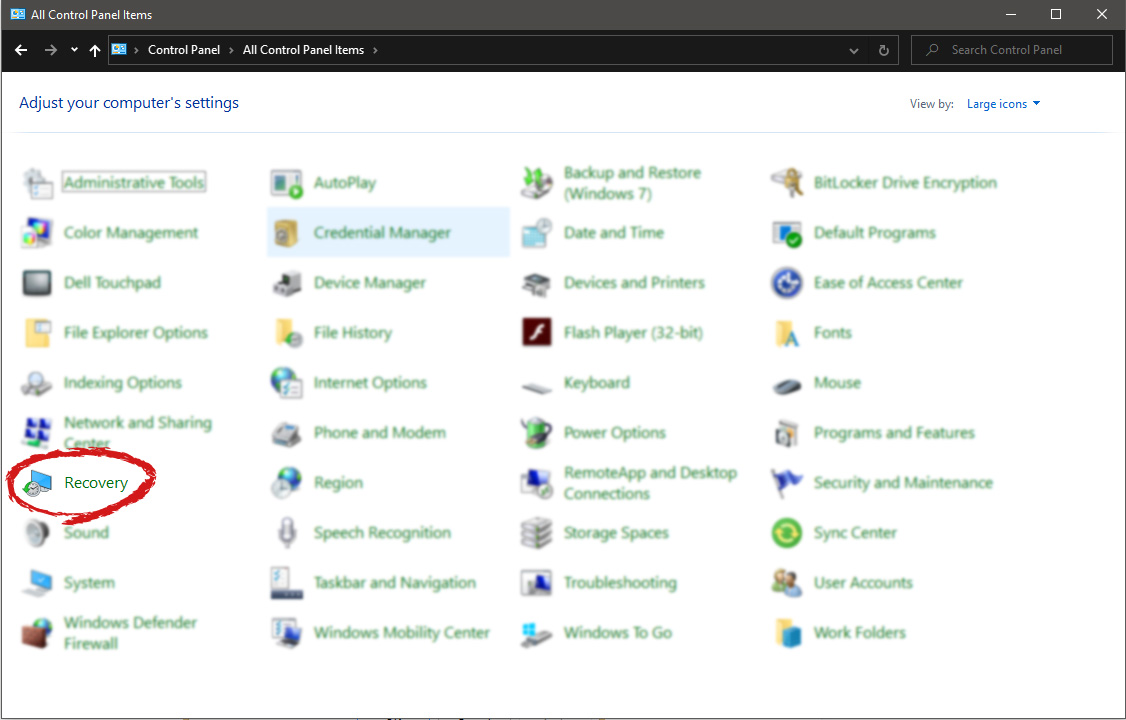
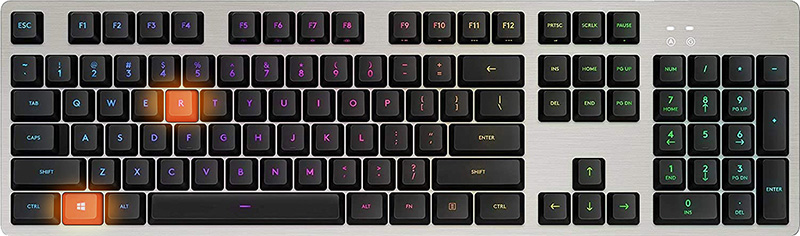 In the run dialog, type control panel and press enter to enter control panel, locate recovery and click on it.
In the run dialog, type control panel and press enter to enter control panel, locate recovery and click on it.
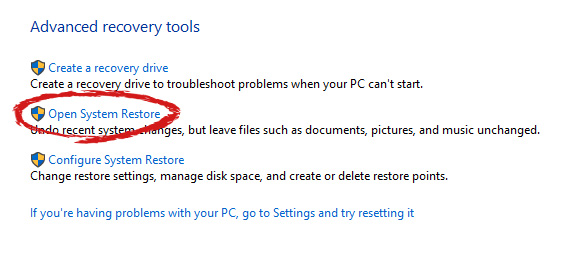
 Inside the recovery screen click on Open System Restore.
Inside the recovery screen click on Open System Restore.
 Choose a date when everything was working in order, the best bet is the date before Windows update and roll it back.
Choose a date when everything was working in order, the best bet is the date before Windows update and roll it back.
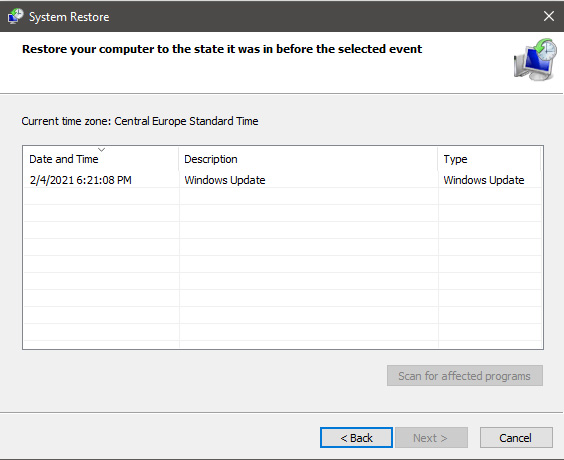 Click on date, and then on next.
Click on date, and then on next.Error Code 0x800703e3 is an error that arises on Windows 10, as well as on many of the past versions of the Windows operating system, dating back to Windows 7. It is an error that is associated with a number of different causes, and therefore, there are many different ways to attempt to resolve the error.
Common symptoms include:
In most cases, users experience Error Code 0x800703e3 when they attempt to install new software or upgrade their programs and operating systems on their Windows machine. Error Code 0x800703e3 is fairly simple to fix and many of the methods used do not require advanced computer skills or knowledge. However, if you have any difficulty in implementing the steps below on your device, it is recommended that you contact a qualified computer repair technician to assist you.
 Error Causes
Error CausesAs there are many different things that can cause Error Code 0x800703e3 to appear on your Windows device, there are many methods that you can use to attempt to resolve the error. While many of these are easy to complete for basic users, some of the methods below require familiarity with advanced computing techniques. If you have trouble using the methods below, contact a qualified Windows repair technician.
Here are the top ways to resolve Error Code 0x800703e3:
The best place to start in resolving Error Code 0x800703e3 is to open up your settings for your drivers and check to see if any updates are necessary. After updating your drivers, it is important to restart your computer to allow any changes to take effect.
Secondarily, you can also run the Windows Registry Repair tool to see if there are any system files in your library that can be fixed, removed, or added automatically by the repair wizard. Again, it is important that you restart your computer after the tool has finished its scan and repair process to ensure that all necessary changes become fully active and recognized by the system.
If it has been a while since you last updated your software and operating system, open up the settings for your system updates. Always restart your computer after a system update has been completed to allow the necessary changes to take effect.
Remember that it is important to regularly update both your Windows operating system and your programs to ensure that there is not a backlog of updates to be completed. This can help to keep your computer in optimum health and eliminate future errors during installations and standard operation of your computer.
In some cases, the best way to address Error Code 0x800703e3 is to reinstall the Windows operating system on your machine. If the core issue of the error is that there is a missing or damaged system file, this is the best way to address the problem quickly and efficiently. Before you attempt to reinstall the Windows operating on your machine, make sure that all of your programs and information have been backed up in a secure manner so that you can restore these items after the installation is complete.
If you just began to experience the error after installing a new program, try removing the new program from your machine using the “uninstall” process, then restart your computer.
If you have any difficulty in completing the above methods on your own or if the problem has not been fully resolved using these methods, get in touch with a certified Windows technician who can help you to fix the issues at hand and get your computer up and running again.
Recently Meta has gone viral that it is working on an AI video-making algorithm named Make a Video. AI will like in picture making AI take text input and produce a video from it.
Now, a new player enters the AI video battlefield, its name is GOOGLE!

The Google research project Imagen Video is also text to video generator similar to Meta's Make a Video with one little difference. unlike Meta's offering which includes only sign-up, Google is withholding access for now under the veil of safeguarding issues.
Google has been in the Ai space before with their Imagen, a DALL-E style generator capable of photorealistic picture generation based on text prompts. The new Google tool works in a similar way but with better functions. Ai can generate a diverse range of high-fidelity videos across different aesthetic styles and with a deep understanding of 3D models thus creating high-definition, 24-frames-per-second videos.
"With the help of progressive distillation, Imagen Video can generate high-quality videos using just eight diffusion steps per sub-model. This speeds up video generation time substantially, by a factor of ~18x,”
Jonathan Ho, author of the research paper
Despite filtering for “undesirable content”, the team admits “there is a risk that Imagen has encoded harmful stereotypes and representations”. So, until the AI - and its users - can be trusted, Google refuses to release Imagen Video without additional safeguards in place.
“Windows could not search for updates, Code 0x800F0922 Windows Update encountered an unknown error” Or: “Windows failed to install the update with error 0x800F0922”This issue might be caused by two possible reasons such as:
RegClean Pro is a program developed by Systweak Inc. RegClean Pro cleans such invalid registry errors using its advanced scan engine. It not only fixes invalid registry entries, it also defragments the registry, keeping it streamlined for smoother system performance.
RegClean Pro defines auto-start registry entities that allow the program to run each time the system is restarted, it also adds various Scheduled tasks in Windows Task Manager in order to launch the application at various times. This application has been found bundled up with various other potentially unwanted applications, also several anti-virus programs have detected this application for optional removal.
chkdsk /r /f
 Error Causes
Error Causes