What is Desk365?
Desk 365 is a program developed by 337 Technology Limited and is classified as a potentially unwanted application by a number of Antiviruses. While not technically malware, for many users it is unwanted as it is often distributed as a bundle with other downloads. It allows a fast way to access your shortcuts and applications. Upon installation this program will insert itself into the system registry, adding startup strings to allow it to automatically start every time your system is restarted.
The software adds a scheduled windows task to allow it to reopen itself even when closed. The applications also access the internet and add firewall rules to your system, that allow it to access anything without restrictions.
The main executable file for this application is Dock365.exe. It is possible to delete this file preventing the application to run, but its monitoring services and registry entities remain hidden inside your computer.
The software sends browsing information back to its ad servers, displaying custom ads and sponsored products instead of the usual search results. And the app itself pins itself to the start menu and cannot be removed.
About Potentially Unwanted Applications
Have you ever discovered an unwanted program on your PC that you didn’t consciously download and never gave authorization to be installed? Potentially Unwanted Programs (PUP), also referred to as Potentially Unwanted Applications (PUA), are applications that you never wanted in the first place and often come bundled with freeware. Once installed, the majority of these applications can be difficult to eliminate and become much more of an annoyance rather than a necessity.
PUPs did not actually constitute pure “malware” in the strict sense of the definition. What normally makes a PUP different from malicious software is that whenever you download one, you’re doing it with your consent – though in many instances unconsciously and unwillingly. A PUP may not be regarded as malicious or unsafe yet still, it’s a common cause of clunky OS’s; some PUPs are a lot more aggressive by intentionally slowing down your computer or laptop.
Exactly how do unwanted programs look like?
Potentially Unwanted Programs can be found in different forms and varieties, but in the majority of cases, these are typically adware programs that exhibit irritating pop-up adverts and advertisements on websites you check out. They even come in the form of browser extension toolbars and add-ons. Not only they needlessly take up space on your screen, but toolbars can also manipulate search engine results, keep an eye on your surfing activities, decrease your internet browser’s efficiency, and slow down your internet connection to a crawl.
PUPs load up a dangerous bite if left unchecked. They could include keyloggers, dialers, and other program built into them which could track you or send your sensitive information to third parties. Typically, such software will disable security protections and configuration settings to take control over your computer or laptop, leaving that PC vulnerable to online hackers and data fraud. At a minimum, PUPs slow your computer down with every added program.
Tips on how to prevent PUPs
• Read the fine print so that the end-user license agreement (EULA) you are accepting is only for the software you primarily intend to download.
• Choose the “custom” install whenever installing an application. Especially, look closely at those small boxes which have been checked as default, where you may ‘agree’ to receive promotions or install software bundlers.
• Use an anti-PUP program. Security applications such as Safebytes Anti-Malware gives the very best real-time protection against PUPs and also other malware.
• Be alert if you download and install freeware, open-source programs, or shareware. Nowadays ‘freeware’ isn’t actually freeware – but “crapware” bundling nonsense.
• Always download software from trustworthy sources like official websites rather than untrustworthy sharing space. Avoid file-hosting sites where/when possible.
What To Do If You Cannot Download Safebytes Anti-Malware?
Every malware is detrimental and the level of the damage can vary greatly according to the type of infection. Some malware is designed to restrict or prevent things that you wish to do on your PC. It may well not permit you to download anything from the web or prevent you from accessing some or all internet sites, in particular the antivirus sites. If you are reading this, chances are you’re stuck with a virus infection that is preventing you to download or install Safebytes Anti-Malware software on your computer system. There are a few fixes you could try to get around with this particular problem.
Download the software in Safe Mode with Networking
The Windows-based PC comes with a special mode known as “Safe Mode” in which just the minimum required programs and services are loaded. If the malicious software is set to load immediately when PC boots, shifting into this mode may well prevent it from doing so. To get into Safe Mode or Safe Mode with Networking, press the F8 key while the system is starting up or run MSCONFIG and look for the “Safe Boot” options in the “Boot” tab. After you restart the PC into Safe Mode with Networking, you can download, install, and update the anti-malware program from there. At this point, you could run the anti-virus scan to eliminate viruses and malware without any hindrance from another malicious application.
Switch over to an alternate web browser
Some malware mainly targets specific internet browsers. If this sounds like your situation, use another internet browser as it might circumvent the malware. If you are not able to download the anti-virus software using Internet Explorer, it means the virus could be targeting IE’s vulnerabilities. Here, you need to switch to a different internet browser such as Chrome or Firefox to download Safebytes Anti-malware software.
Install and run anti-virus from your flash drive
Another option would be to create a portable anti-malware program on your USB stick. To run antivirus from a thumb drive, follow these simple steps:
1) Make use of another virus-free computer to download Safebytes Anti-Malware.
2) Plug in the pen drive to a USB port on the uninfected computer.
3) Double-click the Setup icon of the antivirus software package to run the Installation Wizard.
4) When asked, choose the location of the USB drive as the place in which you want to put the software files. Follow activation instructions.
5) Now, insert the USB drive into the infected PC.
6) Run the Safebytes Anti-malware directly from the flash drive by double-clicking the icon.
7) Run Full System Scan to detect and clean-up up all kinds of malware.
If all the above approaches fail to help you in downloading the anti-malware, then you’ve no alternative but to reinstall the computer’s operating system to wipe out all the data, including the malicious programs which are obstructing the anti-malware installation. If you are already our customer, technical help for Malware Removal is just a phone call away. Call 1-844-377-4107 to speak to our expert technicians and get assistance remotely.
Let's Talk About SafeBytes Anti-Malware!
To help protect your computer from many different internet-based threats, it’s very important to install anti-malware software on your personal computer. But with so many antimalware companies out there, nowadays it’s tough to decide which one you should obtain for your PC. A few are good ones, some are decent, and some are merely fake anti-malware programs that will harm your PC themselves! You need to be very careful not to pick the wrong product, especially if you buy a paid program. On the list of the highly recommended tools by industry experts is SafeBytes Anti-Malware, well-known security software for Windows computers.
Safebytes is among the well-established computer solutions firms, which offer this comprehensive anti-malware software program. Using its outstanding protection system, this utility will quickly detect and eliminate the majority of the security threats, including viruses, adware, browser hijackers, ransomware, PUPs, and trojans.
SafeBytes anti-malware offers an array of advanced features which sets it apart from all others. Listed below are some of the highlighted features included in the tool.
Real-time Threat Response: SafeBytes delivers complete and real-time security for your PC. It will inspect your computer for suspicious activity continuously and shields your personal computer from unauthorized access.
Optimum AntiMalware Protection: This deep-cleaning anti-malware software goes much deeper than most antivirus tools to clean your computer. Its critically acclaimed virus engine finds and disables hard-to-remove malware that conceals deep within your computer.
Web Filtering: SafeBytes gives an instant safety rating about the web pages you’re about to visit, automatically blocking harmful sites and ensuring that you are certain of your online safety while browsing the net.
Light-weight: This software program is not “heavy” on your computer’s resources, so you will not notice any performance issues when SafeBytes is working in the background.
24/7 Online Support: You can obtain high levels of support round the clock if you’re using their paid version.
Overall, SafeBytes Anti-Malware is a solid program since it has plenty of features and can identify and remove any potential threats. You can rest assured that your computer will be protected in real-time once you put this tool to use. For optimum protection and the best bang for your buck, you can’t get better than SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove Desk365 without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by Desk365
Files:
File $APPDATACheckRun22find.exe.
File $APPDATADesk 365accelerate.
File $APPDATADesk 365desk_bkg_list.xml.
File $APPDATADesk 365desk_list.xml.
File $APPDATADesk 365desk_settings.ini.
File $APPDATADesk 365firstrun.
File $APPDATADesk 365process_mgr.xml.
File $APPDATADesk 365promote.xml.
File $APPDATAeDownloadfindhpnt_v2.exe.
File $APPDATAMicrosoftInternet ExplorerQuick Launchfind.lnk.
File $COMMONPROGRAMSDesk 365Desk 365.lnk.
File $COMMONPROGRAMSDesk 365eUninstall.lnk.
File $DESKTOPfind.lnk.
File $LOCALAPPDATAGoogleChromeUser DataDefaultExtensionsnewtab.crx.
File $LOCALSETTINGSTempV9Zip_003Desk365.exe.
File $PROGRAMFILESDesk 365desk_bkg_list.xml.
File $PROGRAMFILESDesk 365desk_list.xml.
File $PROGRAMFILESDesk 365desk_settings.ini.
File $PROGRAMFILESDesk 365desk365.exe.
File $PROGRAMFILESDesk 365deskSvc.exe.
File $PROGRAMFILESDesk 365ebase.dll.
File $PROGRAMFILESDesk 365edeskcmn.dll.
File $PROGRAMFILESDesk 365eDhelper.exe.
File $PROGRAMFILESDesk 365eDhelper64.exe.
File $PROGRAMFILESDesk 365edis.dll.
File $PROGRAMFILESDesk 365edis64.dll.
File $PROGRAMFILESDesk 365ElexDbg.dll.
File $PROGRAMFILESDesk 365eUninstall.exe.
File $PROGRAMFILESDesk 365libpng.dll.
File $PROGRAMFILESDesk 365main.
File $PROGRAMFILESDesk 365ouilibnl.dll.
File $PROGRAMFILESDesk 365process_mgr.xml.
File $PROGRAMFILESDesk 365promote.xml.
File $PROGRAMFILESDesk 365recent.xml.
File $PROGRAMFILESDesk 365sqlite3.dll.
File $PROGRAMFILESDesk 365svc.conf.
File $PROGRAMFILESDesk 365TrayDownloader.exe.
File $PROGRAMFILESDesk 365zlib1.dll.
File $PROGRAMFILESMozilla Firefoxsearchpluginsfind.xml.
File $SENDTODesk 365.lnk.
Directory $APPDATADesk 365.
Directory $APPDATAeDownload.
Directory $COMMONPROGRAMFILES7.
Directory $COMMONPROGRAMSDesk 365.
Directory $LOCALSETTINGSTempDesk365.
Directory $LOCALSETTINGSTempV9Zip_003.
Directory $PROGRAMFILESDesk 365.
Registry:
Key 33BB0A4E-99AF-4226-BDF6-49120163DE86 at HKEY_CURRENT_USERSoftwareMicrosoftInternet ExplorerSearchScopes.
Key deskSvc at HKEY_LOCAL_MACHINESOFTWARE.
Key desksvc at HKEY_LOCAL_MACHINESYSTEMControlSet001Services.
Key desksvc at HKEY_LOCAL_MACHINESYSTEMControlSet001ServicesEventlogApplication.
Key desksvc at HKEY_LOCAL_MACHINESYSTEMCurrentControlSetServices.
Key desksvc at HKEY_LOCAL_MACHINESYSTEMCurrentControlSetServicesEventlogApplication.
Key findSoftware at HKEY_LOCAL_MACHINESOFTWARE.
Key ijblflkdjdopkpdgllkmlbgcffjbnfda at HKEY_LOCAL_MACHINESOFTWAREGoogleChromeExtensions.
Key lnkguard at HKEY_CURRENT_USERSoftware.
Key V9 at HKEY_LOCAL_MACHINESOFTWARE.
 Error Causes
Error Causes
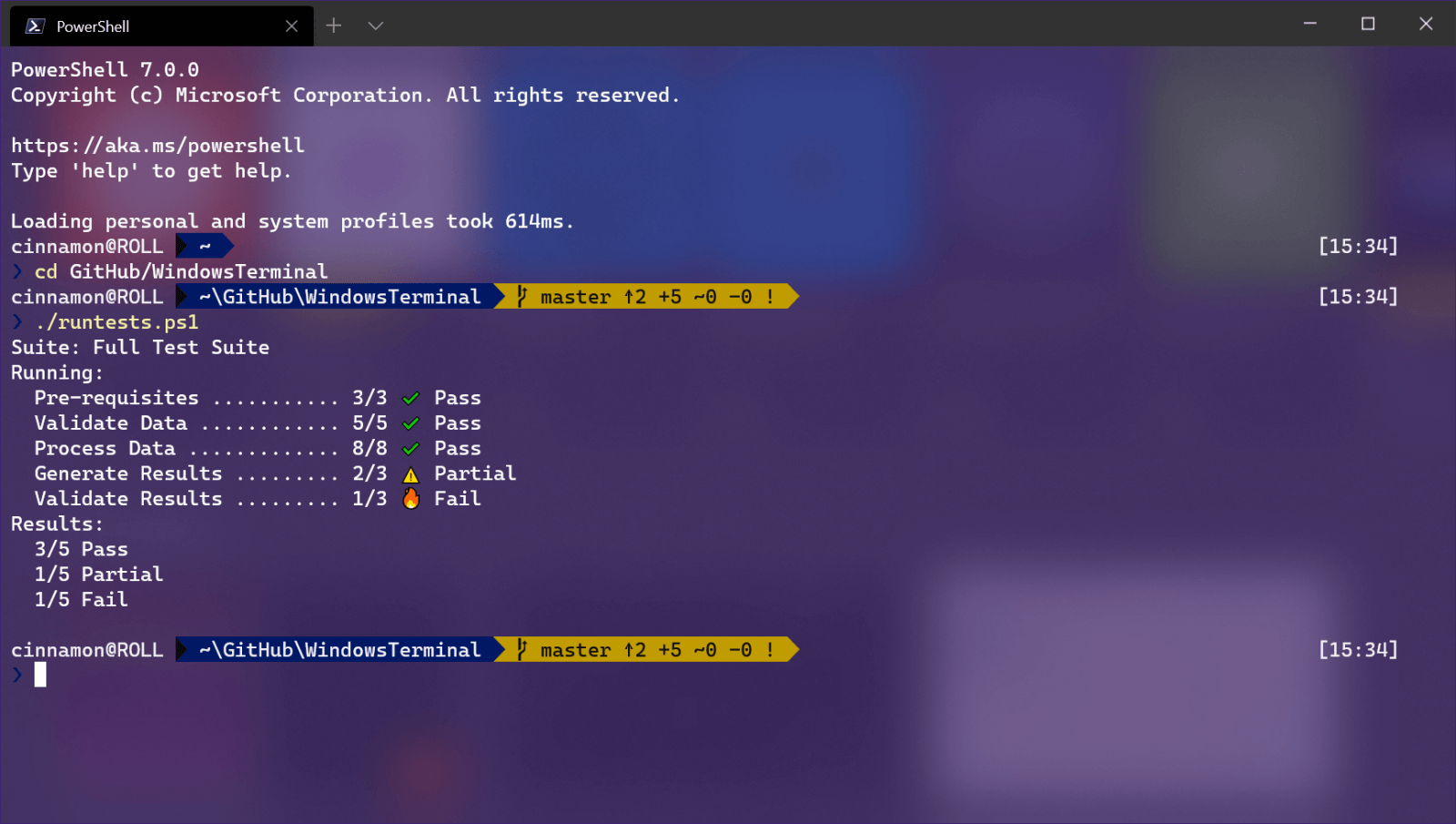 Windows Terminal is a new free Microsoft terminal sort of application. When you open either Power Shell or Command Prompt in Windows they will be opened in different windows, and if you want several of each you will have several windows of each on your screen.
Windows Terminal fixes this by opening each of the Instances of Command Prompt and Power Shell as separate tabs inside itself making it much easier to manage multiple instances of named applications.
You can also run both Power Shell and Command prompt tabs in the same Windows Terminal. Luckily running command prompt and power shell in different tabs is not the only thing you can do. Windows Terminal lets you choose your own theme, it has emoji support, GPU rendering, split panes, and many more customizable options.
Windows 11 will have Terminal as the default command-line environment for opening Power Shell or Command prompt, even Windows Subsystem for Linux (WSL)
Windows Terminal is a new free Microsoft terminal sort of application. When you open either Power Shell or Command Prompt in Windows they will be opened in different windows, and if you want several of each you will have several windows of each on your screen.
Windows Terminal fixes this by opening each of the Instances of Command Prompt and Power Shell as separate tabs inside itself making it much easier to manage multiple instances of named applications.
You can also run both Power Shell and Command prompt tabs in the same Windows Terminal. Luckily running command prompt and power shell in different tabs is not the only thing you can do. Windows Terminal lets you choose your own theme, it has emoji support, GPU rendering, split panes, and many more customizable options.
Windows 11 will have Terminal as the default command-line environment for opening Power Shell or Command prompt, even Windows Subsystem for Linux (WSL)
