If you find it hard to update Google Chrome to its latest version and each time you try to do so it keeps on failing, worry not for this post will guide you in fixing a list of Google Chrome Update errors. Even though there are a lot of error codes around Chrome, these are only caused by issues with the update.
Here are some of the errors you can encounter when updating Google Chrome:
- Update failed: You can encounter this error when the Updates are disabled by the administrator.
- Update failed with
- Error 3 or 11: When Chrome’s inbuilt updater fails to find the Update server to download the latest version.
- Error 4 or 10: This happens while checking for updates with the message “Update check failed to start”
- Error 7 or 12: This occurs when the download fails while checking for updates.
- Windows OS version is not supported.
- Google Chrome may not be able to keep itself updated.
- Any other errors that mention that “Update failed”
Since these aforementioned error codes are related to “Update Failure”, then they have common solutions and here they are:
Option 1 – Restart your computer
You need to restart your computer first and then try updating Chrome again. There are times when it’s only a temporary issue that can be fixed by simply restarting your computer.
Option 2 – Try checking antivirus programs, firewall, and parental control settings
If you have antivirus programs, a firewall installed in your computer, as well as parental controls, then any of these could be blocking you to download anything, including the update for Chrome. This is why you have to double-check and make sure that software updates aren’t being blocked by these programs. On the other hand, you can also try running the Network Troubleshooter as it can help you resolve any DNS or connectivity issues. To use it, follow the steps below.
- Open the Search bar on your computer and type in “troubleshoot” to open the Troubleshoot settings.
- Next, scroll down and select the “Network Adapter” option from the right pane.
- Then click on the Run Troubleshooter” button.
- After that, your computer will check for any possible errors and will pinpoint the root cause of the problem if possible.
Option 3 – Try to remove Proxy
Removing the Proxy might also help you in fixing the Chrome Update errors. Here’s how you can do it:
- Tap the Win + R keys to open the Run dialog box.
- Then type “inetcpl.cpl” in the field and hit Enter to pull up the Internet Properties.
- After that, go to the Connections tab and select the LAN settings.
- From there. Uncheck the “Use a Proxy Server” option for your LAN and then make sure that the “Automatically detect settings” option is checked.
- Now click the OK and the Apply buttons.
- Restart your PC.
Note: If you are using a third-party proxy service, you have to disable it.
Option 4 – Try to reset Winsock, TCP/IP & Flush DNS cache
Resetting Winsock, TCP/IP, and flushing DNS might help in resolving the Chrome Update errors just follow these steps:
- Right-click on the Start button and click on Command Prompt (administrator) so you can pull up an elevated Command Prompt.
- After that, execute each one of the commands listed below. And after you typed in one after the other, you have to hit Enter.
- netsh winsock reset – type in this command to reset Winsock
- netsh int ip reset resettcpip.txt – type in this command to reset TCP/IP
- ipconfig /flushdns – type in this command to flush the DNS cache
- Next, restart your PC and check if the problem’s fixed.
Option 5 – Try to run the Chrome Cleanup tool
You might want to run Google Chrome’s built-in Malware Scanner & Cleanup tool as it could also help in getting rid of any unwanted ads, pop-ups, and even malware, as well as unusual startup pages, toolbars, and anything else that might overtake the network and could affect the performance of the browser.
Option 6 – Get rid of any conflicting browser extensions
- Open Chrome and press Alt + F keys.
- Go to More tools and click Extensions to look for any suspicious browser extensions or toolbars.
- Click the Recycle bin and select Remove.
- Restart Chrome and press Alt + F keys again.
- Proceed to On Startup and mark Open a specific page or set of pages.
- To check if the browser hijacker is still active, click Set pages, if it is active, overwrite the URL.
Option 7 – Reset Google Chrome
Resetting Chrome can also help you get rid of the error. Resetting Chrome will restore its default settings, disabling all the extensions, add-ons, and themes. Aside from that, the content settings will be reset as well and the cookies, cache, and site data will also be deleted. To reset Chrome, here’s what you have to do:
- Open Google Chrome, then tap the Alt + F keys.
- After that, click on Settings.
- Next, scroll down until you see the Advanced option, once you see it, click on it.
- After clicking the Advanced option, go to the “Restore and clean up option and click on the “Restore settings to their original defaults” option to reset Google Chrome.
- Now restart Google Chrome.


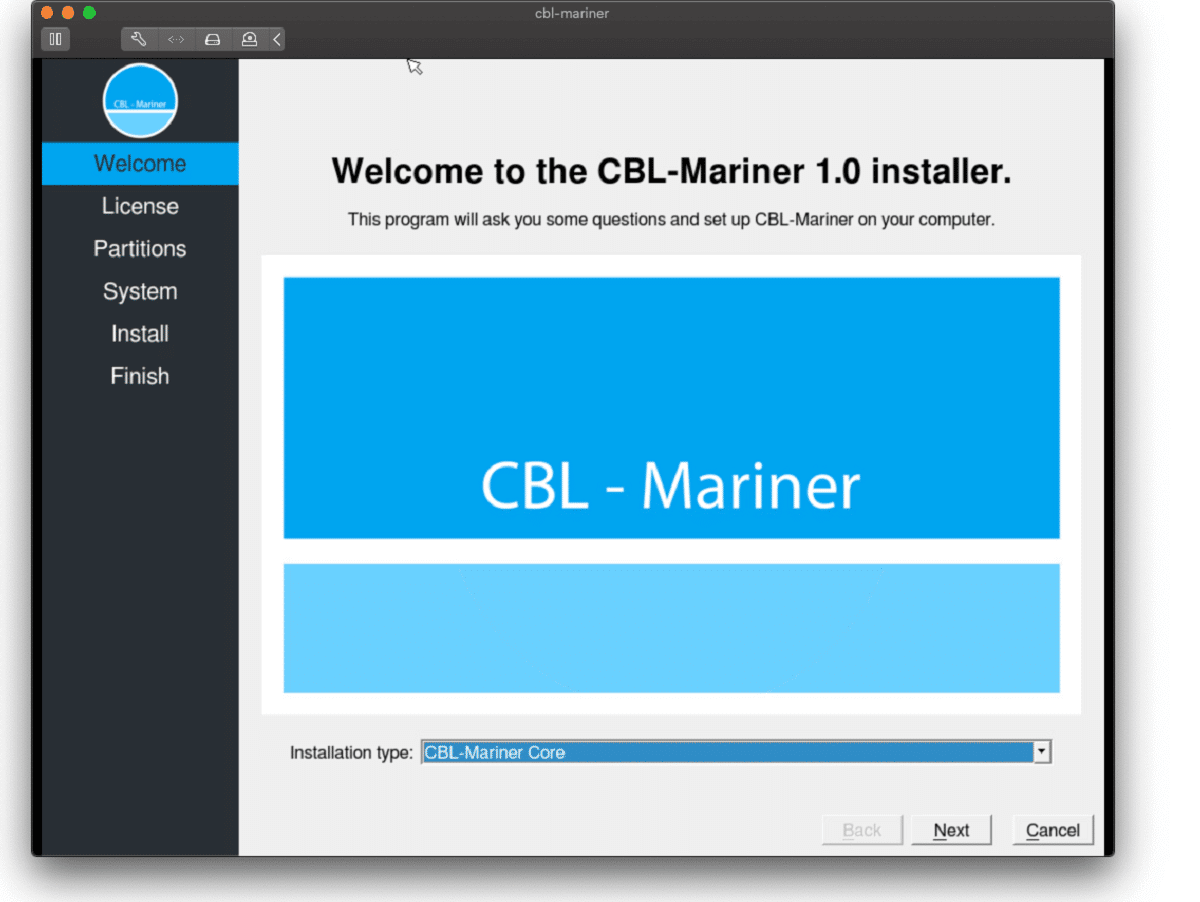 Well if anyone told me just a few years ago that I will see the day when Microsoft releases a new OS based on Linux I would be very amused, but that day has come. Mariner is the newest OS out of nowhere.
Microsoft’s new Linux Distro, dubbed Common Base Linux (CBL)-Mariner, isn’t the type of distro you’d want to install directly on any old machine. It’s primarily meant for cloud infrastructure and edge products. Specifically Microsoft’s Cloud and Edge products.
But if you are curious, it’s possible to run. Juan Manuel Rey, a Microsoft Senior Program Manager for Azure VMware, recently published a guide to ISO CBL-Mariner image. With that, you can easily get it up and running. And you can build CBL-Mariner on an Ubuntu 18.04 desktop. So you can try it out since it is free.
You can get it from here:
Well if anyone told me just a few years ago that I will see the day when Microsoft releases a new OS based on Linux I would be very amused, but that day has come. Mariner is the newest OS out of nowhere.
Microsoft’s new Linux Distro, dubbed Common Base Linux (CBL)-Mariner, isn’t the type of distro you’d want to install directly on any old machine. It’s primarily meant for cloud infrastructure and edge products. Specifically Microsoft’s Cloud and Edge products.
But if you are curious, it’s possible to run. Juan Manuel Rey, a Microsoft Senior Program Manager for Azure VMware, recently published a guide to ISO CBL-Mariner image. With that, you can easily get it up and running. And you can build CBL-Mariner on an Ubuntu 18.04 desktop. So you can try it out since it is free.
You can get it from here:  The console itself is coming in cylindrical shape powered by Intel CPU and ASUS GPU of the unknown chipset. It has Seagate Baraccuda 1TB SSD and it is VR-ready. The console will have raytracing and will be 4K ready.
The console itself is coming in cylindrical shape powered by Intel CPU and ASUS GPU of the unknown chipset. It has Seagate Baraccuda 1TB SSD and it is VR-ready. The console will have raytracing and will be 4K ready.