Besides Star Trek, Star Wars was one of my favorite movie franchises, as a kid, it was the first movie I have seen in Theatre and over the years I have rewatched and reached each entry in the franchise. It has significantly grown over the years, sometimes for worse, sometimes for better but what it always did is explored and expanded lore, characters and brought stories interesting and original enough.
The Series has always been original and innovative enough with interesting characters and locations and it managed to capture the imagination of many viewers around the globe.
If you or someone else is watching the franchise for the first time it is recommended actually to watch everything how it was released because of some information that is spoiled in prequels that could spoil some interesting revelations later. But if you have already watched everything and would like to follow the story from the beginning to end we are presenting you with the list of all TV series and movies in tar Wars canon in their chronological order so you can enjoy some good character developments and see the whole story unfold how it was meant to be.
In the following list, as told, we are including TV series (both released and currently in production) in the Star Wars canon.
Chronological order of Star Wars franchise:
Star Wars: The Acolyte
Acolyte is upcoming TV series exploring times in the old republic and the rise of the dark side within
Star Wars Episode I: The Phantom Menace
The first movie entry in the franchise introducing some key characters who will go through various adventures yet to come
Star Wars Episode II: Attack of the Clones
Continuation of story and deepening of the plot laid out in the previous movie
Star Wars: The Clone Wars
Animated TV series exploring war in more detail, set in the period between episodes 2 and 3, before series there is clone wars full length animated movie titles simply as Star wars clone wars serving as a pilot to series.
Star Wars Episode III: Revenge of the Sith
Last movie in so-called prequel trilogy finishing some stories and finalizing some character arcs
Star Wars: The Bad Batch
Upcoming animated series Bad batch will focus on few troopers find their way in changing the galaxy
Solo: A Star Wars Story
Story of everyone loved Han Solo character, this origin story will introduce you to some key characters in the later entry of series
Obi-Wan Kenobi
Upcoming series that will focus on everyone's favorite JEDI master Obi-Wan
Star Wars Rebels
Animated series exploring first sparks of forming rebel alliance against dreaded empire
Andor
Upcoming series set five years before the events of Rogue One, the series follows rebel spy Cassian Andor during the formative years of the Rebellion.
Star Wars Rogue One
Full feature movie setting up events for episode 4
Star Wars Episode IV: A New Hope
First Star Wars movie, little outdated today with special effects but with a strong story and introducing some new characters which will become main icons of franchise
Star Wars Episode V: The Empire Strikes Back
Arguably the best movie in the whole series, leaning more to serious note and darker than previous entries. Besides Episode 3 this is the most serious and dark movie of the series.
Star Wars Episode VI: Return of the Jedi
Last movie entry in the so-called original trilogy, finishing some stories and wrapping up one era.
Star Wars The Mandalorian
Set after episode 6 show focuses on a Mandalorian bounty hunter character following his adventures in the galaxy.
The Book of Boba Fett
Upcoming Mandalorian spin-off TV series focusing on Bobba Fet, one of most loved bounty hunter characters in the Star Wars universe
Ahsoka
Star Wars: Ahsoka is an upcoming live-action television limited series exploring the character of Ashoka Tano first seen in Clone Wars
Rangers of the New Republic
Set within the timeline of The Mandalorian, Rangers of the New Republic is a new upcoming live-action series.
Star Wars: Resistance
Animated series exploring resistance against first-order setting up events to be followed in the newest trilogy of movies.
Star Wars Episode VII: The Force Awakens
First full feature movie set in the post-empire era introducing new characters and bringing back some fan favorites.
Star Wars Episode VIII: The Last Jedi
The second movie in the last order trilogy, continuing stories of previously establishes characters
Star Wars Episode IX: The Rise of Skywalker
Last entry in new order trilogy of movies, finishing some open stories and concluding arcs for characters previously introduced in Force Awakens.
That's it, chronological order of canon TV shows and movies of the Star Wars franchise. We are sure there will be more movies and shows in the future and someday we will revisit this list to include them as well. Until then, may the force be with you.
If you would like to
read more helpful
articles and tips about various software and hardware visit
errortools.com daily.
 BigTech platforms Google and Facebook were hit with a series of antitrust lawsuits by the US federal government and states on charges they are operating monopolies and abusing their power.
Below is the status of the cases, as well as government probes of Apple and Amazon in their current states
BigTech platforms Google and Facebook were hit with a series of antitrust lawsuits by the US federal government and states on charges they are operating monopolies and abusing their power.
Below is the status of the cases, as well as government probes of Apple and Amazon in their current states


 One of the first things that everyone saw when Microsoft has unveiled Windows 11 is its Start menu. Funny enough this is what has caused most of the divide among users, some find it interesting, and some do not like it. Truth is, it is different, and it is centered in the middle instead of the lower left part of the screen.
It has been confirmed however that the Start menu can be moved to any part of the screen so if you want, you could place it on the lower left as it has always been.
Live tiles do not longer exist in the Start menu, instead, we have styled simple icons.
One of the first things that everyone saw when Microsoft has unveiled Windows 11 is its Start menu. Funny enough this is what has caused most of the divide among users, some find it interesting, and some do not like it. Truth is, it is different, and it is centered in the middle instead of the lower left part of the screen.
It has been confirmed however that the Start menu can be moved to any part of the screen so if you want, you could place it on the lower left as it has always been.
Live tiles do not longer exist in the Start menu, instead, we have styled simple icons.
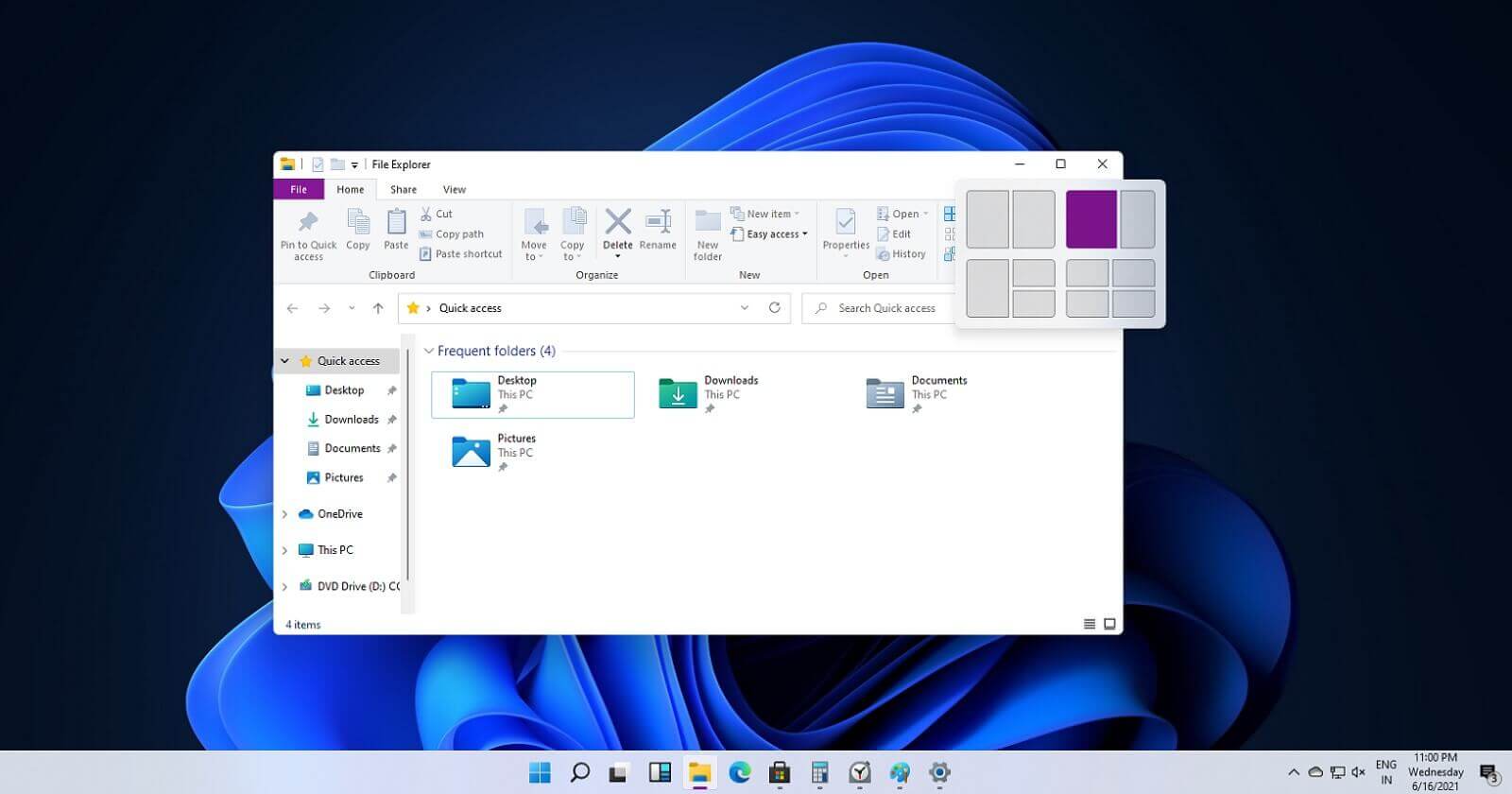 If you have used the cascade option in previous Windows versions then it is most likely that you will like the new Snap controls.
You can quickly snap windows side by side, or arrange them in sections on your desktop just by hovering over maximize button on the title bar.
If you have used the cascade option in previous Windows versions then it is most likely that you will like the new Snap controls.
You can quickly snap windows side by side, or arrange them in sections on your desktop just by hovering over maximize button on the title bar.
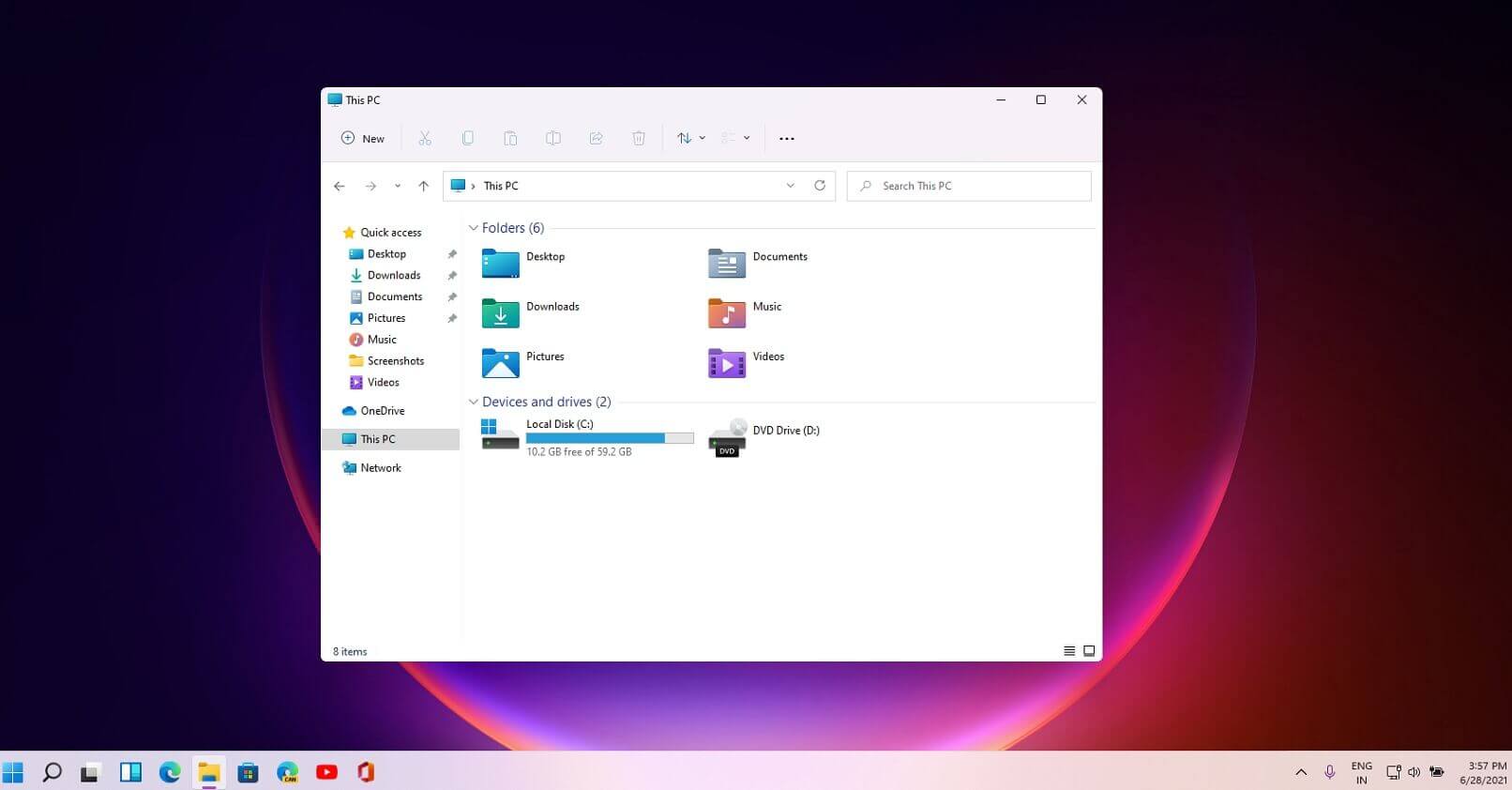 File explorer has gone through some visual and design changes, the ribbon on top has been completely removed and replaced with a header-like feature with a slick and clean design.
The header contains a nice organized and designed single row of icons like cut, paste, copy, rename, delete, and new folder icons.
File explorer has gone through some visual and design changes, the ribbon on top has been completely removed and replaced with a header-like feature with a slick and clean design.
The header contains a nice organized and designed single row of icons like cut, paste, copy, rename, delete, and new folder icons.
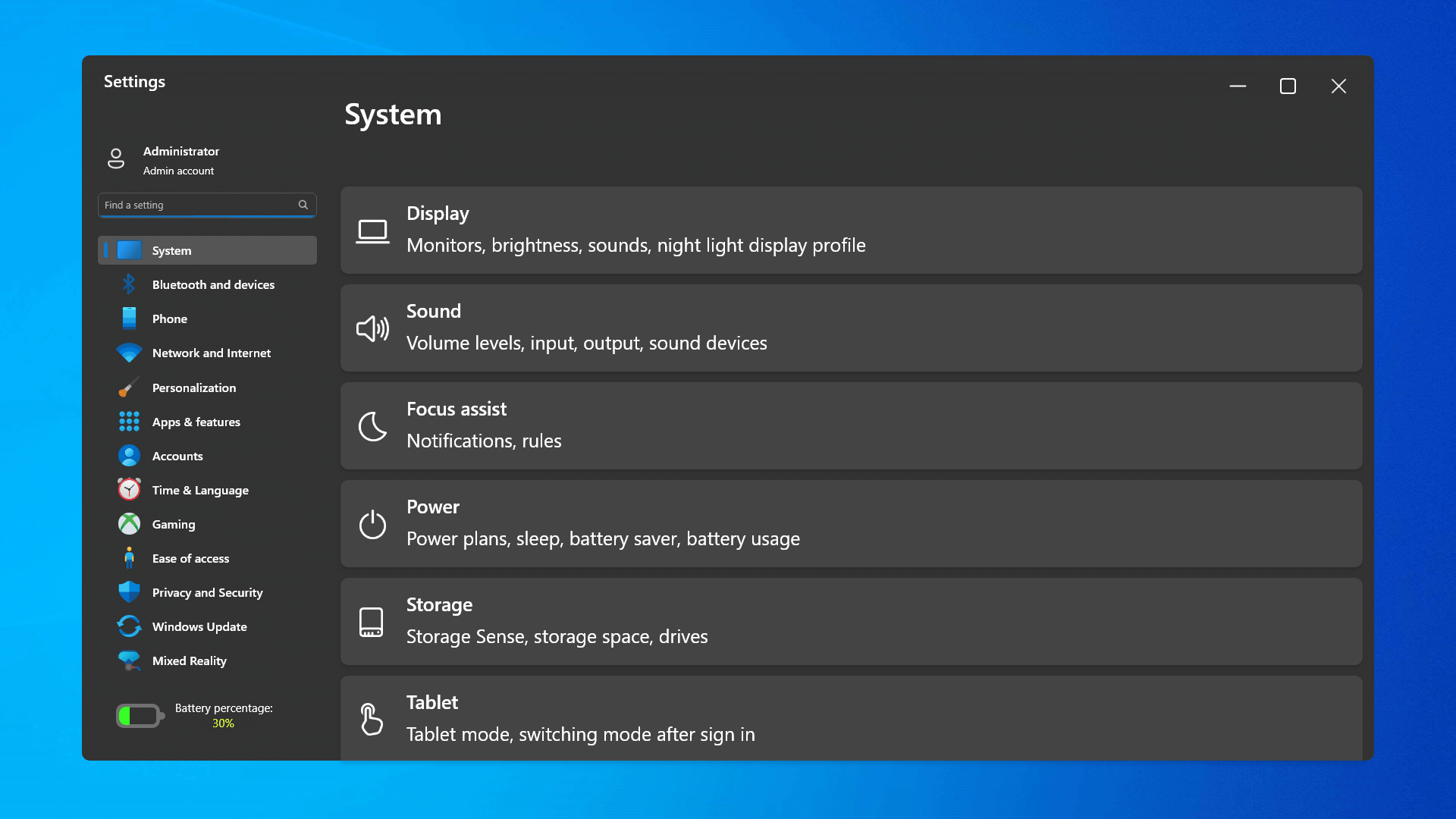 The settings app also has gone through visual and design changes. It has a new design that is very visually appealing and navigation has been simplified and more organized. Finding the right and desired setting is much faster and clearer now.
The settings app also has gone through visual and design changes. It has a new design that is very visually appealing and navigation has been simplified and more organized. Finding the right and desired setting is much faster and clearer now.
 Yes, widgets are back but not like you remember them.
Instead of being all-time present at your desktop like once they used to be, now there is a button on the taskbar which brings the widget bar up that contains desired widgets. This way they are easily accessible and do not clutter desktops.
So far we have weather, news, calendar, and stocks widget but we will see how development on these goes. I expect to have community-made widgets like in old days for all of our needs.
Yes, widgets are back but not like you remember them.
Instead of being all-time present at your desktop like once they used to be, now there is a button on the taskbar which brings the widget bar up that contains desired widgets. This way they are easily accessible and do not clutter desktops.
So far we have weather, news, calendar, and stocks widget but we will see how development on these goes. I expect to have community-made widgets like in old days for all of our needs.
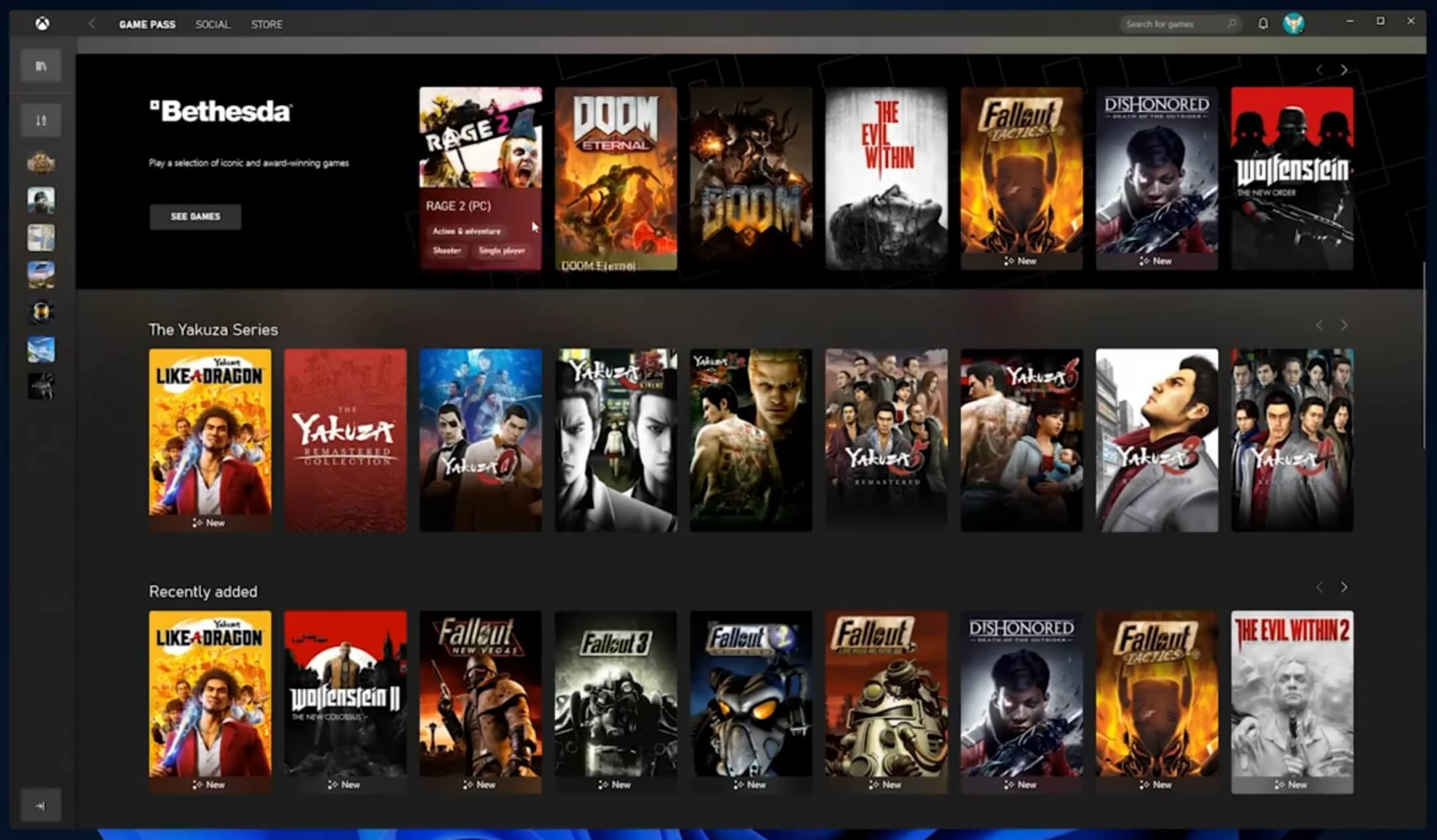 The new Xbox app is now integrated into Windows 11, offering quick access to Xbox Game Pass games, the social parts of the Xbox network, and the Xbox store.
The new Xbox app is now integrated into Windows 11, offering quick access to Xbox Game Pass games, the social parts of the Xbox network, and the Xbox store.
 As widely known by now Windows 11 will require you to have a TPM 2.0 module capable CPU in order to install it.
This system requirement has caused a lot of controversies but essentially it seems that MS's goal is to protect your personal data by using this module.
The upside of course is that your data will be protected much more than in previous Windows versions, the downside, of course, will be that you will need newer hardware to run OS on it.
and that is essentially it, keep on tuned on more Windows 11 information and overall articles tied to PC and technology here at errortools.com
As widely known by now Windows 11 will require you to have a TPM 2.0 module capable CPU in order to install it.
This system requirement has caused a lot of controversies but essentially it seems that MS's goal is to protect your personal data by using this module.
The upside of course is that your data will be protected much more than in previous Windows versions, the downside, of course, will be that you will need newer hardware to run OS on it.
and that is essentially it, keep on tuned on more Windows 11 information and overall articles tied to PC and technology here at errortools.com 