Free Ride Games is a desktop casual game program and potentially unwanted application. It sets its player to run in startup boot with Windows and installs additional files outside of its designated installation folders. The software reads PC information to display targeted advertising and runs a background process that cannot be shut down even by exiting the FreeRide Player. The player runs in full screen with no visible window controls to exit or minimize, and contains unskippable advertising in its function. While not malicious, the FreeRide Player possesses many traits that as of publication time have caused some AntiVirus programs to designate it as potentially unwanted adware. It has also been associated with adware distribution toolbars such as GameVance.
About Browser Hijackers
Browser hijacking means a malicious code has power over and modified the settings of your browser, without your consent. Browser hijacker malware is created for a variety of reasons. Typically, hijackers will force hits to websites of their preference either to increase web traffic generating higher ad earnings, or to gain a commission for each and every user visiting there. Many people think that such websites are legitimate and harmless but that is incorrect. Nearly every browser hijacker poses an actual threat to your online safety and it is vital to categorize them under privacy risks. When the malware attacks your computer or laptop, it begins to mess things up a whole that slows your system down to a crawl. In the worse case, you will be pushed to deal with serious malware threats as well.
Browser hijacking signs
There are numerous signs that could indicate a browser hijacking:
1. you find unauthorized modifications to your Internet browser’s home-page
2. when you enter a URL, you find yourself regularly directed to some other website than the one you actually intended
3. the default web engine and the default browser settings are modified
4. discover new toolbars that you didn’t add
5. you might find numerous pop-up adverts on your computer screen
6. your internet browser has become unstable or starts running sluggishly
7. you are blocked to access those sites of security solution providers.
How it infects your computer
Browser hijackers could use drive-by downloads or file-sharing websites or even an email attachment to reach a targeted computer. They can also come from any BHO, extension, toolbar, add-on, or plug-in with malicious objectives. Also, certain freeware and shareware can put the hijacker in your computer through the “bundling” technique. An example of some notorious browser hijacker includes Conduit, Anyprotect, Babylon, DefaultTab, SweetPage, Delta Search, and RocketTab, but the names are constantly changing.
Browser hijacking can lead to serious privacy issues and also identity theft, affect your web browsing experience by taking control of outbound traffic, substantially slows down your personal computer by depleting a lot of resources and lead to system instability as well.
How to remove a browser hijacker
Some hijackers could be removed by just uninstalling the related freeware or add-ons through the Add or Remove Programs in the Windows Control Panel. However, most hijackers are difficult to eliminate manually. Regardless of how much you attempt to get rid of it, it might keep returning again and again. Furthermore, manual removals demand in-depth system knowledge and therefore can be an extremely difficult task for beginner computer users.
Can't Install Safebytes Anti-malware due to the presence of Malware? Try This!
Malware can cause all kinds of damage when they invade your system, from stealing your personal details to erasing files on your computer system. Some malware sits in between the computer and your net connection and blocks a few or all internet sites that you really want to check out. It might also prevent you from adding anything on your PC, particularly anti-malware applications. If you are reading this, chances are you’re stuck with a malware infection that is preventing you to download and/or install the Safebytes Anti-Malware program on your system. Even though this sort of problem can be harder to get around, there are a few actions you can take.
Install the anti-virus in Safe Mode
If the virus is set to load automatically when Microsoft Windows starts, entering Safe Mode could block the attempt. Only minimal required applications and services are loaded when you boot your computer or laptop into Safe Mode. To launch your Windows XP, Vista, or 7 PCs in Safe Mode with Networking, please do as instructed below.
1) At power on, hit the F8 key while the Windows splash screen begins to load. This will bring up the Advanced Boot Options menu.
2) Select Safe Mode with Networking with arrow keys and hit ENTER.
3) When you are into this mode, you should have online access once again. Now, get the malware removal application you want by using the browser. To install the software, follow the directions in the setup wizard.
4) Following installation, run a complete scan and let the program delete the threats it discovers.
Download the antivirus program in an alternate browser
Web-based viruses could be environment-specific, aiming for a specific web browser or attacking specific versions of the browser. If you appear to have malware attached to Internet Explorer, then switch over to a different web browser with built-in safety features, such as Firefox or Chrome, to download your favorite antivirus program – Safebytes.
Make a bootable USB antivirus drive
Another option is to save and operate an anti-malware software program entirely from a USB drive. To run anti-malware from a USB drive, follow these simple steps:
1) Download the anti-malware program on a virus-free PC.
2) Plug in the pen drive into the clean computer.
3) Run the setup program by double-clicking the executable file of the downloaded application, which has a .exe file extension.
4) Select flash drive as the location when the wizard asks you exactly where you wish to install the application. Follow the directions to complete the installation process.
5) Remove the flash drive. Now you can use this portable antivirus on the infected computer.
6) Double-click the Safebytes Anti-malware icon on the thumb drive to run the software.
7) Click on the “Scan” button to run a full computer scan and remove viruses automatically.
How SafeBytes Anti-Malware Keep your Machine Virus Free"]If you are planning to buy anti-malware for your desktop, there are numerous brands and applications for you to consider. Some are very good ones, some are decent, while some are merely bogus anti-malware applications that will damage your computer themselves! You have to look for a tool that has gained a strong reputation and detects not just viruses but other types of malware also. Among few good applications, SafeBytes Anti-Malware is the highly recommended program for the security-conscious end user.
SafeBytes anti-malware is really a powerful, highly effective protection tool made to assist end-users of all levels of computer literacy in detecting and removing malicious threats from their PC. After you have installed this tool, SafeBytes sophisticated protection system will make sure that no viruses or malicious software can seep through your PC.
SafeBytes has excellent features when compared to other anti-malware programs. The following are some typical features found in this software:
Active Protection: SafeBytes provides complete and real-time security for your personal machine. It will check your computer system for suspicious activity continuously and its unrivaled firewall protects your PC from unauthorized access by the outside world.
Most effective AntiMalware Protection: Using its enhanced and sophisticated algorithm, this malware removal tool can detect and eliminate the malware threats hiding in your computer system effectively.
Web Protection: SafeBytes checks and gives a unique safety rating to each and every website you visit and block access to webpages considered to be phishing sites, thus safeguarding you from identity theft, or known to contain malicious software.
Faster Scanning: Safebytes Anti-Malware, using its advanced scanning engine, provides extremely fast scanning which can quickly target any active online threat.
Light-weight: This software is lightweight and will work silently in the background, and that does not have an effect on your computer efficiency.
24/7 Online Tech Support: You can get 24/7 technical support to promptly resolve any concern with your security tool.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove FreeRideGames without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by FreeRideGames.
Files:
C:21984fa691bd80870e3e3f15cc83121a5862cef4abf2989844d858b2c64b0f
C:DOCUME1USER1LOCALS1TempSDM143C:21984fa691bd80870e3e3f15cc83121a5862cef4abf2989844d858b2c64b0f
C:DOCUME1USER1LOCALS1TempSDM143%#MANIFEST#%01235B
C:DOCUME1USER1LOCALS1TempSDM143cmhelper.exe
C:DOCUME1USER1LOCALS1TempSDM143ExentCtlInstaller.dll
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1TempSDM143resourceDll.dll
C:WINDOWSRegistrationR000000000007.clb
C:WINDOWSsystem32msxml3r.dll
C:21984fa691bd80870e3e3f15cc83121a5862cef4abf2989844d858b2c64b0f
C:DOCUME1USER1LOCALS1TempSDM143%#MANIFEST#%01235B
C:WINDOWSRegistrationR000000000007.clb
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:WINDOWSsystem32rsaenh.dll
C:Documents and SettingsUSERLocal SettingsTemp_uninsep.bat
C:WINDOWSsystem32shdocvw.dll
C:WINDOWSsystem32stdole2.tlb
c:autoexec.bat
C:DOCUME1USER1LOCALS1TempSDM143%#MANIFEST#%01235B
C:DOCUME1USER1LOCALS1TempSDM143cmhelper.exe
C:DOCUME1USER1LOCALS1TempSDM143ExentCtlInstaller.dll
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1TempSDM143resourceDll.dll
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:DOCUME1USER1LOCALS1TempSDM143SDMLog.log
C:DOCUME1USER1LOCALS1TempSDM143SDM_DB_143.xml
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1Temp_uninsdm.bat
C:DOCUME1USER1LOCALS1Temppft3.tmpIKernel.ex_
C:DOCUME1USER1LOCALS1TempIEC4.tmp
C:Program FilesCommon FilesInstallShieldEngineIntel 32temp.000
C:Program FilesCommon FilesInstallShieldEngineIntel 32IKernel.exe
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1Temp_uninsdm.bat
C:DOCUME1USER1LOCALS1Temppft3.tmpSetup.exe
C:Program FilesCommon FilesInstallShieldEngineIntel 32IKernel.exe -RegServer01235B
C:DOCUME1USER1LOCALS1TempSDM143cmhelper.exe
C:DOCUME1USER1LOCALS1TempSDM143ExentCtlInstaller.dll
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1TempSDM143resourceDll.dll
C:WINDOWSRegistrationR000000000007.clb
C:WINDOWSsystem32msxml3r.dll
C:21984fa691bd80870e3e3f15cc83121a5862cef4abf2989844d858b2c64b0f
C:DOCUME1USER1LOCALS1TempSDM143C:21984fa691bd80870e3e3f15cc83121a5862cef4abf2989844d858b2c64b0f
C:DOCUME1USER1LOCALS1TempSDM143%#MANIFEST#%01235B
C:DOCUME1USER1LOCALS1TempSDM143cmhelper.exe
C:DOCUME1USER1LOCALS1TempSDM143ExentCtlInstaller.dll
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1TempSDM143resourceDll.dll
C:WINDOWSRegistrationR000000000007.clb
C:WINDOWSsystem32msxml3r.dll
C:21984fa691bd80870e3e3f15cc83121a5862cef4abf2989844d858b2c64b0f
C:DOCUME1USER1LOCALS1TempSDM143%#MANIFEST#%01235B
C:WINDOWSRegistrationR000000000007.clb
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:WINDOWSsystem32rsaenh.dll
C:Documents and SettingsUSERLocal SettingsTemp_uninsep.bat
C:WINDOWSsystem32shdocvw.dll
C:WINDOWSsystem32stdole2.tlb
c:autoexec.bat
C:DOCUME1USER1LOCALS1TempSDM143%#MANIFEST#%01235B
C:DOCUME1USER1LOCALS1TempSDM143cmhelper.exe
C:DOCUME1USER1LOCALS1TempSDM143ExentCtlInstaller.dll
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1TempSDM143resourceDll.dll
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:DOCUME1USER1LOCALS1TempSDM143SDMLog.log
C:DOCUME1USER1LOCALS1TempSDM143SDM_DB_143.xml
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1Temp_uninsdm.bat
C:DOCUME1USER1LOCALS1Temppft3.tmpIKernel.ex_
C:DOCUME1USER1LOCALS1TempIEC4.tmp
C:Program FilesCommon FilesInstallShieldEngineIntel 32temp.000
C:Program FilesCommon FilesInstallShieldEngineIntel 32IKernel.exe
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1Temp_uninsdm.bat
C:DOCUME1USER1LOCALS1Temppft3.tmpSetup.exe
C:Program FilesCommon FilesInstallShieldEngineIntel 32IKernel.exe -RegServer01235B
C:WINDOWSRegistrationR000000000007.clb
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:WINDOWSsystem32rsaenh.dll
C:Documents and SettingsUSERLocal SettingsTemp_uninsep.bat
C:WINDOWSsystem32shdocvw.dll
C:WINDOWSsystem32stdole2.tlb
c:autoexec.bat
C:DOCUME1USER1LOCALS1TempSDM143C:21984fa691bd80870e3e3f15cc83121a5862cef4abf2989844d858b2c64b0f
C:DOCUME1USER1LOCALS1TempSDM143%#MANIFEST#%01235B
C:DOCUME1USER1LOCALS1TempSDM143cmhelper.exe
C:DOCUME1USER1LOCALS1TempSDM143ExentCtlInstaller.dll
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1TempSDM143resourceDll.dll
C:WINDOWSRegistrationR000000000007.clb
C:WINDOWSsystem32msxml3r.dll
C:21984fa691bd80870e3e3f15cc83121a5862cef4abf2989844d858b2c64b0f
C:DOCUME1USER1LOCALS1TempSDM143%#MANIFEST#%01235B
C:WINDOWSRegistrationR000000000007.clb
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:WINDOWSsystem32rsaenh.dll
C:Documents and SettingsUSERLocal SettingsTemp_uninsep.bat
C:WINDOWSsystem32shdocvw.dll
C:WINDOWSsystem32stdole2.tlb
c:autoexec.bat
C:DOCUME1USER1LOCALS1TempSDM143%#MANIFEST#%01235B
C:DOCUME1USER1LOCALS1TempSDM143cmhelper.exe
C:DOCUME1USER1LOCALS1TempSDM143ExentCtlInstaller.dll
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1TempSDM143resourceDll.dll
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:DOCUME1USER1LOCALS1TempSDM143SDMLog.log
C:DOCUME1USER1LOCALS1TempSDM143SDM_DB_143.xml
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1Temp_uninsdm.bat
C:DOCUME1USER1LOCALS1Temppft3.tmpIKernel.ex_
C:DOCUME1USER1LOCALS1TempIEC4.tmp
C:Program FilesCommon FilesInstallShieldEngineIntel 32temp.000
C:Program FilesCommon FilesInstallShieldEngineIntel 32IKernel.exe
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1Temp_uninsdm.bat
C:DOCUME1USER1LOCALS1Temppft3.tmpSetup.exe
C:Program FilesCommon FilesInstallShieldEngineIntel 32IKernel.exe -RegServer01235B
C:DOCUME1USER1LOCALS1TempSDM143cmhelper.exe
C:DOCUME1USER1LOCALS1TempSDM143ExentCtlInstaller.dll
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1TempSDM143resourceDll.dll
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:DOCUME1USER1LOCALS1TempSDM143SDMLog.log
C:DOCUME1USER1LOCALS1TempSDM143SDM_DB_143.xml
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1Temp_uninsdm.bat
C:DOCUME1USER1LOCALS1Temppft3.tmpIKernel.ex_
C:DOCUME1USER1LOCALS1TempIEC4.tmp
C:Program FilesCommon FilesInstallShieldEngineIntel 32temp.000
C:Program FilesCommon FilesInstallShieldEngineIntel 32IKernel.exe
C:DOCUME1USER1LOCALS1TempSDM143Free Ride Games.exe
C:DOCUME1USER1LOCALS1Temp_uninsep.bat
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1TempSDM143FreeRideGames.exe
C:DOCUME1USER1LOCALS1Temp_uninsdm.bat
C:DOCUME1USER1LOCALS1Temppft3.tmpSetup.exe
C:Program FilesCommon FilesInstallShieldEngineIntel 32IKernel.exe -RegServer
 Error Causes
Error Causes

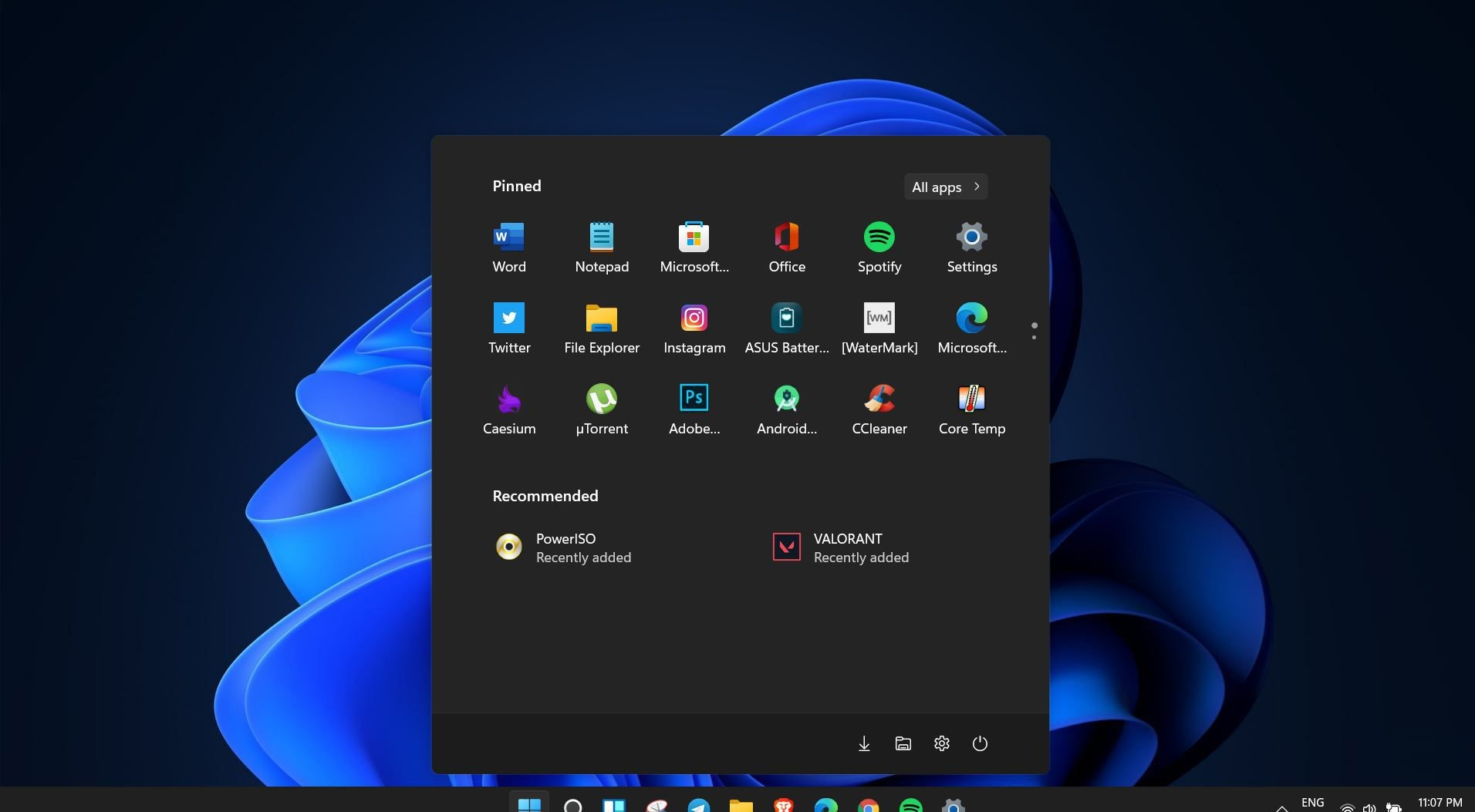 Windows 11 is coming soon, from its typical view and color scheme, Windows 11 will natively support dark mode.
The dark mode is very popular in many applications today, some large companies like Adobe, Autodesk, and many more have already adopted a dark color scheme for their software so it is logical for others to follow and Microsoft is aboard for it.
The dark mode itself has its benefits, for people who work on computer for longer period of time dark mode inside applications will throw less white and blue light on their eyes making workhours easier and pleasant on them.
As a person who does indeed spend a lot of time in front of the screen, I would advise you to switch to dark mode regardless of the time that you spend with a computer, your eyes will be grateful.
Windows 11 is coming soon, from its typical view and color scheme, Windows 11 will natively support dark mode.
The dark mode is very popular in many applications today, some large companies like Adobe, Autodesk, and many more have already adopted a dark color scheme for their software so it is logical for others to follow and Microsoft is aboard for it.
The dark mode itself has its benefits, for people who work on computer for longer period of time dark mode inside applications will throw less white and blue light on their eyes making workhours easier and pleasant on them.
As a person who does indeed spend a lot of time in front of the screen, I would advise you to switch to dark mode regardless of the time that you spend with a computer, your eyes will be grateful.

