Premiere Download Manager is a Browser Extension that comes bundled with Premiere Download Manager Potentially unwanted program, and other unwanted applications and extensions. This program was developed by Mindspark Interactive and offers users the ability to download files off the internet through the Download Manager provided. It also changes the home page and defaults the search engine to Myway.com.
This bundle monitors the user’s activity, and while the extension has access to your browsing activity, clicked links, visited pages, etc. the application itself has access to all the files that you downloaded, and have on your computer. This gathered data is later sent back to Mindspark’s servers where it is used to better target ads for users.
While installed, you will run into additional, sponsored links, and even pop-up ads while browsing the internet. Though it is not considered malware, it contains many behaviors disliked by users and is labeled as potentially unwanted. This bundle has been marked as a Browser Hijacker by several anti-virus applications and is therefore recommended to remove from your PC.
About Browser Hijackers
Browser hijacking is actually a form of unwanted software program, commonly a browser add-on or extension, which causes modifications in web browser’s settings. Browser hijacker malware is designed for many different reasons. Often, hijackers will force hits to sites of their preference either to increase web traffic producing higher ad revenue, or to obtain a commission for each and every user visiting there. Although it may seem naive, these tools are made by malicious people who always attempt to take full advantage of you, so that they can earn money from your naivety and distraction. Some browser hijackers are designed to make particular modifications beyond the web browsers, like changing entries in the computer registry and permitting other types of malware to further damage your computer.
Key symptoms that your internet browser has been hijacked
There are numerous symptoms that indicate your web browser is highjacked: the home page of the browser is changed all of a sudden; your browser is constantly being redirected to pornography sites; the default web engine has been changed and the browser security settings have been lowered without your knowledge; you’re getting browser toolbars you have never noticed before; you find lots of pop-up ads on your screen; your browser gets slow, buggy, crashes very often; You can’t access certain sites, in particular anti-virus websites.
Exactly how they get into your computer or laptop
There are several ways your computer or laptop can become infected by a browser hijacker. They generally arrive through spam email, via file-sharing networks, or by a drive-by download. They may also originate from any BHO, extension, toolbar, add-on, or plug-in with malicious purpose. Sometimes you may have mistakenly accepted a browser hijacker as part of an application bundle (usually freeware or shareware).
Browser hijackers could affect the user’s web browsing experience significantly, monitor the websites frequented by users and steal financial information, cause difficulty in connecting to the net, and then finally create stability issues, making applications and computers freeze.
Removing browser hijackers
Certain browser hijacking can be quite easily reversed by finding and removing the corresponding malware application through your control panel. However, many hijackers are extremely tenacious and require specialized applications to eradicate them. Also, browser hijackers might modify the Computer registry therefore it could be very hard to restore all of the values manually, especially when you are not a very tech-savvy person.
Installing and running antivirus applications on the affected system could automatically delete browser hijackers and also other unwanted applications. SafeBytes Anti-Malware discovers all types of hijackers – including Premier Download Manager – and removes every trace efficiently and quickly.
What To Do When You Cannot Install Safebytes Anti-Malware?
All malware is bad and the degree of the damage will differ greatly with regards to the type of malware. Certain malware variants modify internet browser settings by including a proxy server or modify the computer’s DNS configurations. When this happens, you’ll be unable to visit certain or all of the internet sites, and thus unable to download or install the required security software to get rid of the infection. If you are reading this article now, you have probably realized that virus infection is the cause of your blocked internet connectivity. So what to do when you want to download and install an anti-virus program such as Safebytes? There are some options you could try to get around with this particular issue.
Make use of Safe Mode to resolve the issue
In Safe Mode, you may change Windows settings, uninstall or install some applications, and get rid of hard-to-delete viruses and malware. In case the malware is set to load automatically when the computer starts, shifting into this mode could prevent it from doing so. To boot into Safe Mode, hit the “F8” key on the keyboard right before the Windows boot screen comes up; Or right after normal Windows boot up, run MSConfig, check the Safe Boot under the Boot tab, and click Apply. Once you are in Safe Mode, you can try to install your antivirus program without the hindrance of the malware. At this point, you can actually run the anti-malware scan to get rid of viruses and malware without interference from another application.
Switch to some other web browser
Some malware only targets certain internet browsers. If this sounds like your situation, employ another web browser as it can circumvent the computer virus. If you’re not able to download the anti-malware program using Internet Explorer, it means malware is targeting IE’s vulnerabilities. Here, you should switch over to a different internet browser like Chrome or Firefox to download Safebytes software.
Make a bootable USB anti-virus drive
Another option is to create a portable antivirus program onto your USB stick. To run anti-malware using a pen drive, follow these simple steps:
1) Download the anti-malware on a virus-free computer.
2) Plug the pen drive into the uninfected computer.
3) Double click on the downloaded file to run the installation wizard.
4) When asked, choose the location of the pen drive as the place where you want to store the software files. Do as instructed on the computer screen to finish up the installation process.
5) Transfer the USB drive from the clean computer to the infected PC.
6) Double-click the antivirus software EXE file on the USB flash drive.
7) Hit the “Scan Now” button to start the malware scan.
SafeBytes Anti-Malware: Lightweight Malware Protection for Windows PC
In order to protect your PC from many different internet-based threats, it is important to install anti-malware software on your computer system. But with countless numbers of anti-malware companies out there, nowadays it is hard to decide which one you should buy for your personal computer. Some of them are good and some are scamware applications that pretend as legit anti-malware software waiting around to wreak havoc on your computer. You have to be careful not to pick the wrong application, particularly if you buy a premium application. While considering the highly regarded applications, Safebytes AntiMalware is certainly the highly recommended one.
SafeBytes anti-malware is a very effective and user-friendly protection tool that is suitable for end-users of all levels of computer literacy. Through its cutting-edge technology, this software will help you protect your personal computer against infections caused by different types of malware and similar threats, including adware, spyware, trojans, worms, computer viruses, keyloggers, ransomware, and potentially unwanted program (PUPs).
SafeBytes has great features when compared to other anti-malware programs. The following are a few of the great ones:
Active Protection: SafeBytes gives you round-the-clock protection for your personal computer limiting malware intrusions in real-time. It will regularly monitor your pc for hacker activity and also gives users sophisticated firewall protection.
Antimalware Protection: With its advanced and sophisticated algorithm, this malware elimination tool can detect and get rid of the malware threats hiding in your computer system effectively.
High-Speed Malware Scanning Engine: Safebytes AntiMalware, with its enhanced scanning engine, offers extremely fast scanning which can immediately target any active internet threat.
Website Filtering: SafeBytes checks and gives a unique safety ranking to every website you visit and block access to webpages known to be phishing sites, thus protecting you from identity theft, or known to contain malicious software.
Low CPU Usage: SafeBytes gives you complete protection from online threats at a fraction of the CPU load due to its advanced detection engine and algorithms.
24/7 Support: You could get high levels of support around the clock if you’re using their paid version.
SafeBytes will keep your computer safe from the latest malware threats automatically, thus keeping your online experience safe and secure. Once you’ve downloaded and installed SafeBytes Anti-Malware, you will no longer have to bother about malware or other security concerns. So if you’re looking for the best anti-malware subscription for your Windows-based PC, we highly recommend SafeBytes Anti-Malware software.
Technical Details and Manual Removal (Advanced Users)
If you wish to carry out the removal of Premier Download Manager manually instead of employing an automated tool, you may follow these simple steps: Go to the Windows Control Panel, click the “Add or Remove Programs” and there, select the offending program to remove. In cases of suspicious versions of web browser plug-ins, you can easily get rid of it through your web browser’s extension manager. It is also suggested to reset your web browser to its default state to fix corrupt settings.
Lastly, examine your hard drive for all of the following and clean your computer registry manually to remove leftover application entries following an uninstallation. Having said that, editing the registry is usually a difficult task that only experienced computer users and professionals should attempt to fix it. Also, certain malware is capable of replicating itself or preventing its deletion. It is advised that you do the removal process in Safe Mode.
Files:
C:\Program Files\PremierDownloadManager_agEI\Installr.bin\NPagEISb.dl_
C:\Program Files\PremierDownloadManager_agEI\Installr.bin\NPagEISb.dll
C:\Program Files\PremierDownloadManager_agEI\Installr.bin\agEIPlug.dl_
C:\Program Files\PremierDownloadManager_agEI\Installr.bin\agEIPlug.dll
C:\Program Files\PremierDownloadManager_agEI\Installr.bin\agEZSETP.dl_
C:\Program Files\PremierDownloadManager_agEI\Installr.bin\agEZSETP.dll
%PROGRAM FILES%\PREMIERDOWNLOADMANAGER\PDMANAGER_IE.DLL:
%PROGRAM FILES%\PREMIERDOWNLOADMANAGER\PDMANAGER_IE.DLL Malware
%PROGRAM FILES%\PREMIERDOWNLOADMANAGER\PDMANAGER_IE.DLL Dangerous
%PROGRAM FILES%\PREMIERDOWNLOADMANAGER\PDMANAGER_IE.DLL High Risk
%program files%\premierdownloadmanager\pdmanager_ie.dll
%PROGRAM FILES%\PREMIERDOWNLOADMANAGER\PDMANAGER_IE.DLL
%PROGRAM FILES%\PREMIERDOWNLOADMANAGER\PDM.ICO
%PROGRAM FILES%\PREMIERDOWNLOADMANAGER\PDMANAGER.EXE
%PROGRAM FILES%\PREMIERDOWNLOADMANAGER\PDMANAGER_IE.DLL
%PROGRAM FILES%\PREMIERDOWNLOADMANAGER\PDMANAGER_IE.TLB
%PROGRAM FILES%\PREMIERDOWNLOADMANAGER\REGASM.EXE
Registry:
key HKLM\Software\Classes\CLSID\819D045F-E9A2-39E0-B495-D615AD1A9471\InprocServer32.0.0.1\CodeBase: file:///C:/Program Files/PremierDownloadManager/PDManager_ie.DLL
key HKLM\Software\Classes\CLSID\819D045F-E9A2-39E0-B495-D615AD1A9471\InprocServer32\CodeBase: file:///C:/Program Files/PremierDownloadManager/PDManager_ie.DLL
key HKLM\Software\Classes\CLSID\87D1BD5F-0174-4AB2-FFC4-9E3A451F17EB\InprocServer32.0.0.1\CodeBase: file:///C:/Program Files/PremierDownloadManager/PDManager_ie.DLL
key HKLM\Software\Classes\CLSID\87D1BD5F-0174-4AB2-FFC4-9E3A451F17EB\InprocServer32\CodeBase: file:///C:/Program Files/PremierDownloadManager/pdmanager_ie.dll
key HKLM\Software\Classes\Record\EDF1D497-05B5-37F6-AAAC-3EB5E67D4DC2.0.0.1\CodeBase: file:///C:/Program Files/PremierDownloadManager/PDManager_ie.DLL
key HKCU\SOFTWARE\PREMIERDOWNLOADMANAGER\INTERNET EXPLORER: %PROGRAM FILES%\PREMIERDOWNLOADMANAGER\PDMANAGER_IE.DLL

 Intel announced that Pat Gelsinger (CEO) and Dr. Ann Kelleher (technology Department head) will discuss Intel’s process and packaging innovations on an upcoming webcast that will happen on July 26th.
The spokesman will talk and provide a deeper look at the process and packaging roadmaps for Intel. As we know Intel is planning to expand its production capabilities, outsource some of its technologies and offer foundry services to other chip design companies.
The strategy will also include a shift to a 7nm process and Intel’s effort to set itself again as leader of CPU performance by 2024.
There is also a chance that we will hear exact plans for Intel in the next three or four years.
Intel didn't reveal much else about what Gelsinger and Kelleher plan to discuss during the webcast. The event will be streamed on July 26 at 2 pm PT via the
Intel announced that Pat Gelsinger (CEO) and Dr. Ann Kelleher (technology Department head) will discuss Intel’s process and packaging innovations on an upcoming webcast that will happen on July 26th.
The spokesman will talk and provide a deeper look at the process and packaging roadmaps for Intel. As we know Intel is planning to expand its production capabilities, outsource some of its technologies and offer foundry services to other chip design companies.
The strategy will also include a shift to a 7nm process and Intel’s effort to set itself again as leader of CPU performance by 2024.
There is also a chance that we will hear exact plans for Intel in the next three or four years.
Intel didn't reveal much else about what Gelsinger and Kelleher plan to discuss during the webcast. The event will be streamed on July 26 at 2 pm PT via the 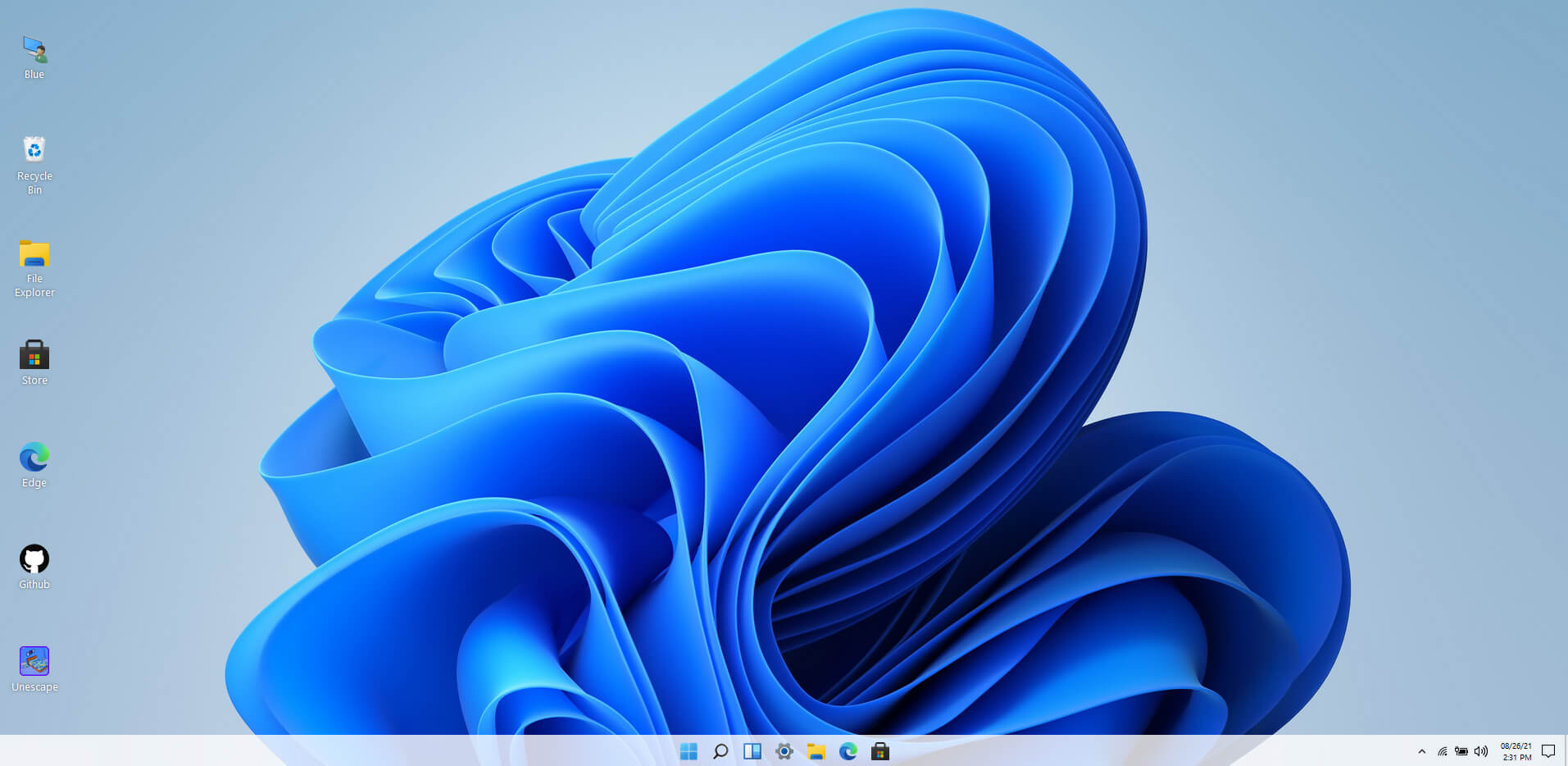 Windows 11 release date is closing in, some people have tried it via insider build, some have decided not to. It has come to our attention that there is a little website made by BlueEdge that offers a virtual Windows 11 desktop.
Opening the Website will put you right inside Windows 11 desktop, now take note that this is not Windows 11, it is a simulation of Microsoft’s newest OS and therefore many things will not work like File Explorer, etc.
One thing you can make sure it is working is UI itself, you can see how you do like the new Taskbar, start menu, widgets, and some other things. You can just pop up on the site and check how you do like the overall new look and feel of Windows 11 UI before installing it or trying it.
We are sure that many more options will come in time but even now you can get a feel of the newest OS.
Windows 11 BlueEdge site:
Windows 11 release date is closing in, some people have tried it via insider build, some have decided not to. It has come to our attention that there is a little website made by BlueEdge that offers a virtual Windows 11 desktop.
Opening the Website will put you right inside Windows 11 desktop, now take note that this is not Windows 11, it is a simulation of Microsoft’s newest OS and therefore many things will not work like File Explorer, etc.
One thing you can make sure it is working is UI itself, you can see how you do like the new Taskbar, start menu, widgets, and some other things. You can just pop up on the site and check how you do like the overall new look and feel of Windows 11 UI before installing it or trying it.
We are sure that many more options will come in time but even now you can get a feel of the newest OS.
Windows 11 BlueEdge site: 
